The following figure shows a linear programming problem where the shaded region represents the polytope of feasible solutions, the colored lines represent constraint functions, and the black lines represent the contours of the objective function. Darker lines of the objective function contour represent larger values. It also shows five different points, all of which lie within the polytope. The linear program attempts to find the maximum value. Which point corresponds to a solution of the linear program? A) 2 (B) 5 D E 20 2 ...
The following figure shows a linear programming problem where the shaded region represents the polytope of feasible solutions, the colored lines represent constraint functions, and the black lines represent the contours of the objective function. Darker lines of the objective function contour represent larger values. It also shows five different points, all of which lie within the polytope. The linear program attempts to find the maximum value. Which point corresponds to a solution of the linear program? A) 2 (B) 5 D E 20 2 ...
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter3: Introduction To Linear Programming
Section: Chapter Questions
Problem 35RP
Related questions
Question
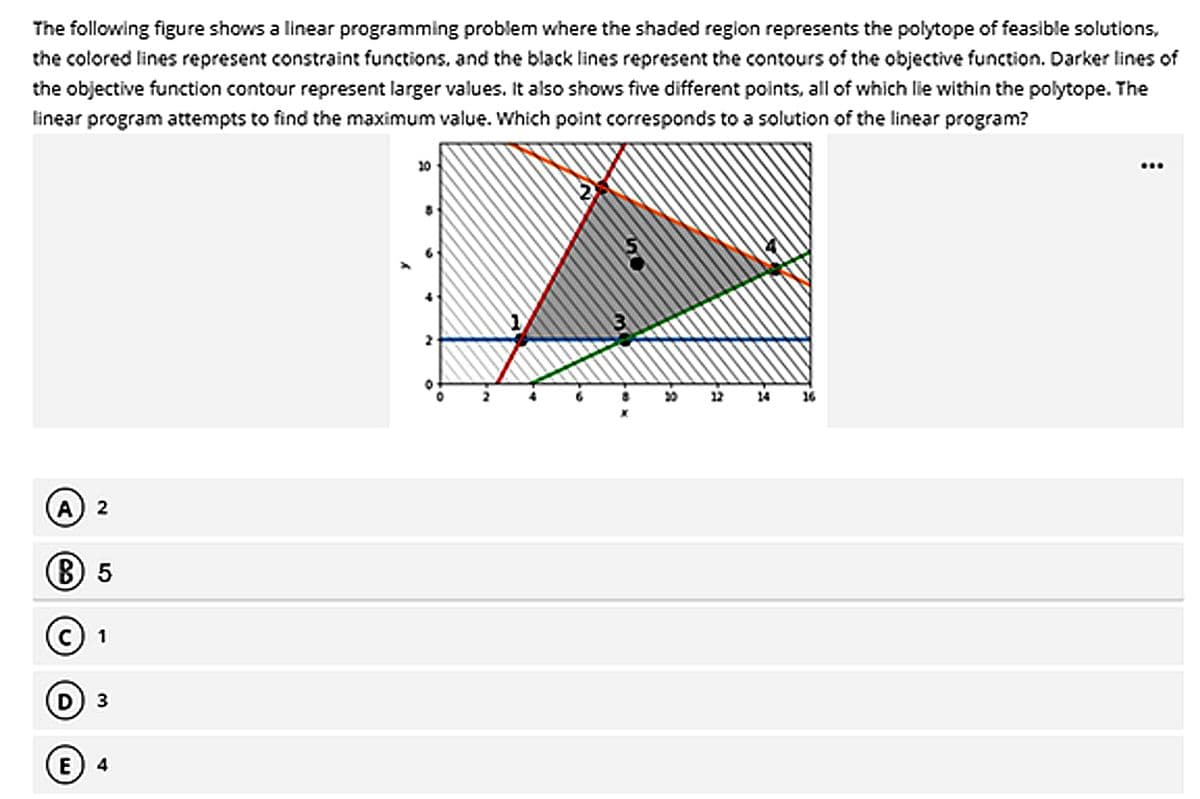
Transcribed Image Text:The following figure shows a linear programming problem where the shaded region represents the polytope of feasible solutions,
the colored lines represent constraint functions, and the black lines represent the contours of the objective function. Darker lines of
the objective function contour represent larger values. It also shows five different points, all of which lie within the polytope. The
linear program attempts to find the maximum value. Which point corresponds to a solution of the linear program?
2
(B) 5
1
3
E 4
20
…..
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole