The function remove of the class arrayListType removes only the first occurrence of an element. Add the function removeAll as an abstract function to the class arrayListType, which would remove all occurrences of a given element. Also, write the definition of the function removeAll in the class unorderedArrayListType and write a program to test this function.
Q: Convert the following expressions to SOP form. Remove any redundant terms. (a) (??′)′(? + ?)(? + ?…
A: SOP stands for Sum of Product.It can be defined in such a way that it is a set of product(AND) terms…
Q: 13. Trace the bubble sort as it sorts the following array into descending order: 10 12 23 34 5
A: Working of Bubble Sort :Start from the beginning of the list.Compare adjacent elements (pairwise)…
Q: lish many subnets on a single switch? If users on one subnet can't connect to users on another…
A: Virtual Local Area Networks (VLANs) play a pivotal role in network segmentation, improving security…
Q: Why is it essential to use a secure key exchange mechanism in encrypted
A: A secure key, in the context of cryptography and encryption, is a piece of information that is used…
Q: A bank client wants to withdraw cash that was sent to them through the cash send service. To…
A: In this case study, a bank customer wants to use an ATM to withdraw money that was transferred to…
Q: Discuss the role of orchestration tools in managing and automating cloud resources.
A: Orchestration tools are software applications that help in automating and managing the deployment,…
Q: It is expected of you to be able to provide your own explanation of System Dynamics. If it is at all…
A: System Dynamics is a mathematical modeling that may be done on a computer to develop strategies and…
Q: differences between Deadlock Avoidance and Deadlock Prevention
A: in the following section we will learn about differences between Deadlock Avoidance and Deadlock…
Q: Which physical key on the keyboard is equivalent to the virtual key symbol for the Left Menus?
A: Which physical key on the keyboard is equivalent to the virtual key symbol for the Left Menus Answer…
Q: the state machine diagram of a single tape deterministic Turing Machine
A: Given :-In the above mentioned question as statement is mentioned as,The language B = {ww^R| w ϵ…
Q: How does the Diffie-Hellman key exchange algorithm work, and why is it significant?
A: The Diffie-Hellman key exchange algorithm is a fundamental cryptographic protocol that enables two…
Q: Why is architecture key? Map a project without and with architecture? Effects on total product.
A: In this question we need to explain why architecture is important or key. Moreover we need to map…
Q: Cloud computing services are available through Microsoft Azure Domain. Amazon Web Services versus.…
A: The evolution of cloud computing has significantly influenced how businesses function and deploy…
Q: As the need and applications for data integration continue to grow, more and more organizations will…
A: The following are the headings for your proposal's table of contents:IntroductionTechnologies and…
Q: In which scenarios would you prefer to use an array over a linked list, and vice versa?
A: In the world of computers, we use special ways to organize information, kind of like arranging items…
Q: What are some signs that the operating system of a laptop has been tampered with, and what are some…
A: Tampering with a laptop's operating system can be a serious security risk. It can allow unauthorized…
Q: Describe the main differences between the transport layer and the network layer.
A: The OSI (Open Systems Interconnection) paradigm is a conceptual framework that standardises how…
Q: Describe the TM that accepts the language, L = {w = {a,b,c}* | w contains equal number of a's, b's…
A: Given :here in the question it is specified that the word or string contains letter a , b and c. It…
Q: 5. Suppose that your implementation of a particular algorithm appears in Java as for (int pass = 1;…
A: In computer science, the term "order" typically refers to the computational complexity or time…
Q: eople like cyber crime, and how
A: For a variety of reasons, people commit crimes online. To execute fraudulent transactions or money…
Q: 8. Assume you have a queue q that has already been populated with data. What does the following code…
A: Here is your solution -
Q: Rather than focusing on efficiency, explain why software engineers choose deep access over shallow…
A: In the context of software engineering and programming,, "deep access" and "shallow access"…
Q: Given symbols and their frequencies of occurrence in some program codes. a) Determine and draw the…
A: The symbols given are +, -, *, /, %, =.These are the frequencies 3, 7, 1, 2, 8 and 9.
Q: Using the exhaustive search approach, what is the maximum value achieved for the following knapsack…
A: Hello studentGreetingsNote: As per our policy guidelines, in case of multiple different questions,…
Q: IT Systems Development and Acquisition Draw an infographic that shows the differences between the…
A: Infographics are a design which represents the objective clearly and easy to understand. and these…
Q: How do Low Power Wide Area Networks (LPWANs) cater to IoT needs?
A: Low Power Wide Area Networks (LPWANs) have emerged as a vital technology to address the connectivity…
Q: How does embedded software development differ from desktop software development?
A: In this passage we delve into the world of embedded and desktop software development.Embedded…
Q: What do you think of going through the OSI layer, its purposes, and the protocols that are used in…
A: Navigating the OSI (Open Systems Interconnection) model involves understanding its layered…
Q: 2. What is the output of the following code ? #include int main() { int i=1;…
A: Step-1: StartStep-2: Declare variable i and assign value 1 Step-3: Print ++i,i++,++iStep-4: Stop
Q: How does SSL/TLS encryption ensure data integrity during transmission?
A: SSL/TLS encryption secures online data transmission. A client requests a secure connection, the…
Q: Reduce this term into normal from, if it exists (show your working):…
A: To reduce the given lambda calculus expression to its normal form, it will follow the usual steps of…
Q: Explain the principle behind the Cyclic Redundancy Check (CRC).
A: Cyclic Redundancy Check, or CRC for short, is a method for detecting errors that is utilized…
Q: (5) Parity Check. Consider a 4-bit long packet that is protected by a single parity bit. Consider…
A: There will be a total of 4+1 = 5 bits in one packet (including the parity bit)<a>Error cannot…
Q: Describe the networking challenges posed by IoT devices
A: An IoT (Internet of Things) device refers to a physical object or machine that is embedded with…
Q: Describe the concept of a Software Defined Network (SDN).
A: Software define network is a approach which is used to increase the efficient of the network by…
Q: Explain how machine learning and Intrusion Detection Systems are being used to increase security of…
A: In recent years, Wireless Sensor Networks (WSNs) have gained significant importance across various…
Q: What is the keyboard's Left Menu virtual key symbol?
A: The keyboard's Left Menu virtual key symbol is an essential element found on computer keyboards,…
Q: Research how the keyboard and mouse input I/O devices function. For each device, write a theory of…
A: A keyboard input device functions through a complex interaction of its physical hardware components,…
Q: What criteria make an app successful?
A: An "app," short for "application," is a software program or software application designed to perform…
Q: What are some of the most important distinctions that can be made between a traditional telephone…
A: Networking of Telephones:Voice communication is made possible via the usage of the telephone…
Q: How does type-checking work with complex datatypes in statically-typed languages versus…
A: The answer is given below step.
Q: Imagine you’ve been hired as an IT consultant for a small business that is expanding its operations…
A: Subnet:A subnet is a smaller network created from a larger network, often used to divide a network…
Q: 12. Construct DFA to accept L = {w E {a,b,c}| w end with either ab, be or ca}
A: We are tasked with constructing a Deterministic Finite Automaton (DFA) that recognizes the language…
Q: Which functions and tasks does the central processing unit perform? What do you think and feel about…
A: The answer is given below step.
Q: What role does a Content Delivery Network (CDN) play in cloud architectures
A: A Content Delivery Network (CDN) serves as a critical component within cloud architectures,…
Q: tages of using simplex m
A: The physical layer specifies the transmission method. Transmission mode refers to how information is…
Q: Explain the significance of port numbers in TCP/IP communication.
A: Port numbers play a crucial role in TCP/IP communication by enabling multiple applications to…
Q: C++ program Given arrays we need to merge all overlapping ranges array to non overlapping array that…
A: Algorithm:I defined the array inside the main function if you want you can take input from the…
Q: Differentiate between public, private, and hybrid cloud models.
A: Cloud computing has revolutionized the way businesses manage and deploy their IT resources. There…
Q: Explain the role of a network bridge in a LAN environment.
A: A network bridge, also known as a "bridge," is a device used in computer networks that operates at…
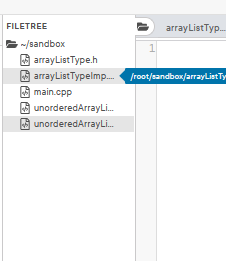
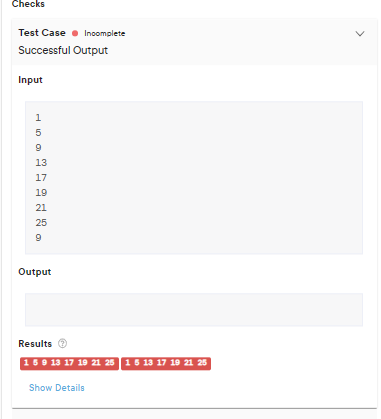
The function remove of the class arrayListType removes only the first occurrence of an element. Add the function removeAll as an abstract function to the class arrayListType, which would remove all occurrences of a given element. Also, write the definition of the function removeAll in the class unorderedArrayListType and write a
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 3 images

- What are the advantages of using a link list instead of an array?public class CustomLinkedList { public static int findMax(IntNode headObj) { /* Type your code here */ } public static void main(String[] args) { IntNode headObj; IntNode currObj; IntNode lastObj; int i; int max; // Create head node headObj = new IntNode(-1); lastObj = headObj; // Add nodes to the list for (i = 0; i < 20; ++i) { currObj = new IntNode(i); lastObj.insertAfter(currObj); lastObj = currObj; } max = findMax(headObj); System.out.println(max); }}java program: University of Bahrain College of Information Technology Department of Computer Science Second Semester, 2020-2021 ITCS214 / ITCS215 / ITCS216 (Data Structures) Assignment 3 Implement generic class ArrayStack as discussed in the lectures having following methods: constructor, push, pop, peek, isEmpty, copy constructor, reallocate (private method). Also add following methods to this class: size: returns number of elements in the stack. contains: Search an element in the stack. If found returns true, else returns false. clear: Deletes all elements of the stack and make it empty stack. Implement generic class ArrayQueue as discussed in the lectures having following methods: constructor, copy constructor, offer, poll, peek, isEmpty, reallocate(private), iterator. Inner class Iter that implements interface Iterator having methods: constructor, hasNext, next. Also add following methods to the ArrayQueue class: size: returns number of elements in the queue. contains: Search…
- Create a class Student with the fields: name (a String) and gpa (a double). Create a linked list of Student objects, called students using the LinkedList class from java.util.Sort the linked list students “by length” of name (see Sect. 11.3 in textbook) using the sort method from class Collections.Sort the initial linked list students by gpa using the sort method from class Collections. Apply the toArray() method from class LinkedList to the initial linked list students and sort the obtained array “by length” of name using the sort method from class Arrays. After each sort, print the result.Do NOT use the sort method from the List interface (also available from a LinkedList).Hey, Please fill in the missing code needed for the three sum implementation in Java. Please provide code comments aswell. Thanks. Code required to fill in is in the do something area. import java.util.Arrays;import java.util.List;public class ThreeSum {private static final List<String> filePaths = new ArrayList<>();static {filePaths.add("resources/1Kints.txt");filePaths.add("resources/2Kints.txt");filePaths.add("resources/4Kints.txt");filePaths.add("resources/8Kints.txt");filePaths.add("resources/16Kints.txt");}public static void main(final String[] args) {for (final String path : filePaths) {// do something}}public static int threeSumA(final int[] array) {final int length = array.length;int count = 0;for (int i = 0; i < length; i++) {for (int j = i+1; j < length; j++) {for (int k = j + 1; k < length; k++) {if (array[i] + array[j] + array[k] == 0) {count++;}}}}return count;}public static int threeSumB(final int[] array) {final int length =…Write a code for a simple text editor/Nodepad. Use fully connected linked list, with four pointers next,prev,up and down. Note: Use linkedlist DSA C++ and also file handling. Please complete the requirements. I asked this question multiplie times before. I don't want incorrect answer this time.
- Give me the answer in one Visual Studio file, not Visual Studio Code - Give me full code near and simple Develop a C++ "doubly" linked list class of your own that can hold a series of signed shorts Develop the following functionality: Develop a linked list node struct/class You can use it as a subclass like in the book (Class contained inside a class) You can use it as its own separate class Your choice Maintain a private pointer to a node class pointer (head) Constructor Initialize head pointer to null Destructor Make sure to properly delete every node in your linked list push_front(value) Insert the value at the front of the linked list pop_front() Remove the node at the front of the linked list If empty, this is a no operation operator << Display the contents of the linked list just like you would print a character string operator [] Treat like an array Return the value stored in that element of the linked list If element doesn’t exist, return…i) Create a Node class which will hold two fields i.e an integer element and a reference to the next Node. ii) Create a Linked list Abstract Data Type (ADT)named MyList.The elements in the list are Nodes consisting of an integer type key (all keys are unique) and a reference to the next node. Use Python Language.THE QUESTION IS ATTACHED: PLEASE AVOID USING import java.util.ArrayList; import java.util.HashMap; import java.util.Map; BECAUSE I HAVEN'T STUDIED THEM YET, YOU CAN USE 1D AND 2D ARRAYS. YOU ARE FREE TO USE import java.io.File; import java.io.FileNotFoundException; import java.io.FileWriter; import java.io.IOException; EFFECTIVELY USE LOOPS AND CONTROL STATEMENTS. TXT. FILE IS INCLUDED BELOW: MOVIE NAME, MOVIE YEAR, RATING AND GENRE. The Martian2015Adventure8.0Murder on the Orient Express2017Crime6.5X-Men: First Class2011Action7.7X-Men: Days of Future Past2014Action7.9This Means War2012Action6.3Godzilla vs. Kong2021Adventure6.5Black Widow2021Action7.5Zack Snyder's Justice League2021Action8.1The Ten Commandments1956Drama7.9The Father2020Drama8.3Nobody2021Crime7.5Promising Young Woman2020Crime7.5What Lies Below2020Horror4.4Shrine2021Horror5.1Bram Stoker's Dracula1992Horror7.4
- please update generateRandoms, letterToGrades, sumBetween, countCharacters //A6Utilities.java import java.io.IOException;import java.nio.file.Files;import java.nio.file.Paths;import java.security.SecureRandom;import java.util.List;import java.util.TreeMap;import java.util.function.Function;import java.util.stream.Collectors;public class A6Utilities {/*** Returns the corresponding letter grade. Don't modify this method, simply use it when converting single* grades to their equivalent letter grade** @param grade the integer grade to convert* @return the letter grade equivalent to the integer grade*/private static char letterGrade(final int grade) {if (grade < 0) return '?';else if (grade < 60) return 'F';else if (grade < 70) return 'D';else if (grade < 80) return 'C';else if (grade < 90) return 'B';else if (grade <= 100) return 'A';else return '?';}/*** The method uses Java Streams only. Don't use any looping structures, conditional statements are OK (IF, TERNARY,…import java.util.ArrayList; public class Bus { privateStringname; privateintsize; privateintbasePrice; privateArrayList<Trip>approvedTrips; privateintlevel;// 1,2,3 for low,medium, high repectively; privateintid; privatestaticintnextId=0; privateMinistrymny; protectedStringtripTypes; privateintgetNextId(){ returnnextId++; } publicBus(){ approvedTrips=newArrayList<Trip>(); } publicBus(Stringname,intsize,intbasePrice,intlev,Ministrymny){ approvedTrips=newArrayList<Trip>(); this.name=name; this.size=size; this.basePrice=basePrice; this.level=lev; this.id=getNextId(); this.mny=mny; tripTypes="BASICTRANSPORT"; } publicbooleanavailable(Datedate){ booleanretval=true; for(Tript:approvedTrips) if(t.getDate().getDay()==date.getDay()) retval=false; returnretval; } publicintgetBasePrice(){ returnbasePrice; } publicintgetId(){ returnid; } publicStringgetName(){ returnname; } publicdoublegetSize(){ returnsize; } publicStringtoString(){ returnname; }…Code In Java Using Array or doubly Linklist instead of linklist COVID-19 has effect whole world. People are interested in knowing current situation of COVID-19. You are required to write JAVA program for storing information in a Array Following JAVA classes are provided. // Node class public class COVIDDetail { public String country; public int activecases; public COVIDDetail next; } // linked List class public class COVIDList { COVIDDetail start=null; } You are required to add following methods to COVIDList class void add(COVIDDetail n) this method receives a node as argument and adds it to given list. Nodes are arranged in descending order with respect to number of cases. Note that you are not required to sort the list in fact while adding first find its appropriate position and then add given node to that position. void updateCases(String country_name , int cases) this method receives two argument country name and cases (can have…

