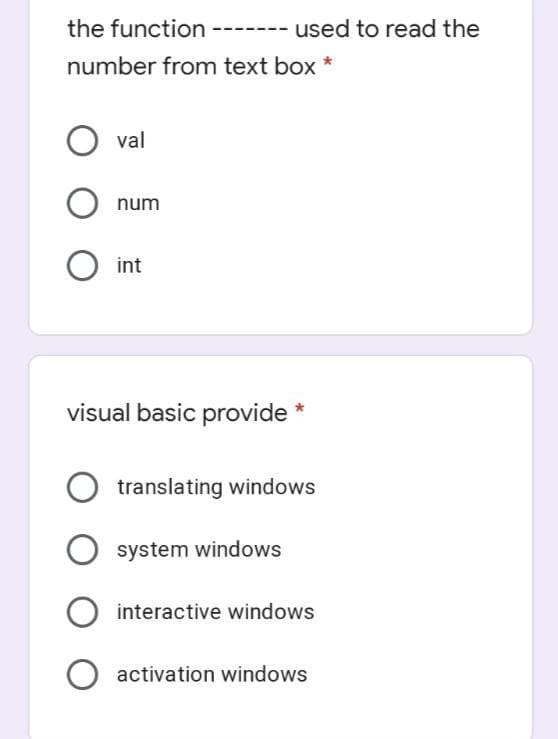
the function used to read the number from text box O val
Q: Assume I have a technique for responding every single question from a certain set of feasible querie...
A: Intro In the 21st century, we have been confronted with numerous data breaches that require governme...
Q: Picking numbers at random, what exactly does it mean?
A: Random Random is a term that means that anything, a number, a quantity, or whatever else is picked a...
Q: Consider a server (one core) where 30 computational jobs need to be scheduled for processing. Let Ti...
A: Given :- Consider a server (one core) where 30 computational jobs need to be scheduled for processin...
Q: ply for embedded
A: given - What does the Internet of Things imply for embedded developers?
Q: Recall the "better" algorithm to determine whether or not the input positive integer is a prime numb...
A: Answer : The time complexity of that algorithm is O(N). where N is integer.
Q: * A PDA employs data structure Linked list Hash table Stack Queue
A: The solution to the given problem is below.
Q: What is it called when a value that exceeds the format's numeric range and is treated as an error by...
A: When we assign a value that is out of range of the format's numeric range and it is too large to be ...
Q: The qualities of the technology used to wirelessly and automatically transfer photographs and videos...
A: Here is the solution with an explanation:-
Q: a)Define Wifi, Winax and ATM. b)Diff btn Winax and Wifi. c)Explain where wifi and Wimax are commonly...
A: Wi-Fi:-Wi-Fi is the wireless innovation used to interface computers, tablets, cell phones and differ...
Q: Understand when it is appropriate to employ supertype/subtype relationships in data modelling.
A: Modeling Data: Data modelling is the process of developing a data model for the data that will be ke...
Q: Which statement performs overwriting .2 ?assignment * x=h+1 h=e+1
A: INTRODUCTION: Here we need to explain which statement performs overwriting.
Q: Your data warehousing project team is discussing whether to build a prototype before implementing it...
A: INTRODUCTION: Here we need to give suggestions.
Q: What are the commercial implications of the cloud computing movement? Do you know how to work well w...
A: Intro Cloud computing might be a general term that involves delivering hosted services over the web...
Q: One of the following tuples not exist in a * :CFG set of variables final symbol O
A:
Q: 4. Declare a two-dimensional array that has 3 columns and 4 rows. 5. Write a for loop that will prin...
A: Ans 4: Declare the two dimensional array that has 3 columns and 4 rows is:\ int arr[4][3] ={1,2,3,4,...
Q: Which of the following procedures may be performed in constant time on an unsorted singly linked lis...
A: Intro There are both head and tail pointers pointing to the first and last element of the linked lis...
Q: Resolve IPv6 Compression FE80:0000:0000:0300:AAFF:0000:0000:00A3
A: Introduction: An IP address is a logical address. It is a Network Layer address(Layer 3), IP addres...
Q: een the array implementation and the linked list implementation of queues. Describe the advantages ...
A: Discuss the differences between the array implementation and the linked list implementation of queue...
Q: copy constructor of the class
A: #include<iostream.h> #include<conio.h> #include<string.h> class student { char nam...
Q: Because it needs to relocate members after the removal operation, the remove method of the reference...
A: Introduction: Here we are required to tell whether the remove method of the reference-based list imp...
Q: Make a list of two external and two internal barriers to good listening.
A: Listening effectively: Listening effectively is paying close attention to what the speaker is saying...
Q: Fill in the blanks. Provide the number immediately before and after the given number in the given ba...
A: here we have given value of before and the after of present values.
Q: The following terminologies are used to describe interruptions: Describe their kinds in detail and e...
A: Introduction: An interrupt is a signal that is received by the processor to interrupt the present pr...
Q: Consider the following Country class: public class Country{ String name; Integer population; Rewrite...
A: According to the information given:- We have to follow instruction mentioned to rewrite the class i...
Q: Assume that an imaging system's display and printer aren't fully calibrated. In print, a picture tha...
A: Introduction: The calibration procedure is a desirable and well-defined step in the production proce...
Q: nsider each of these four (4) factors while evaluating cloud computing. Dependable Manageable Ada...
A: Four (4) factors while evaluating cloud computing. Dependable Manageable Adaptable Affordable
Q: Find out the value of R7 P[i] is a price of item whose lenght is i meters and array of prices Array ...
A:
Q: Open Control panel. In windows 10, Tap or click on the windows Update link in control panel open it....
A: First of all it was very easy to navigate through apps and settings. Anyone can easily reach to the ...
Q: What happens if the ios:out function is invoked by itself to open a non-existent file?
A: Introduction : All output actions are carried out at the file's conclusion, adding the content to th...
Q: What is a virtual switch, and how does it work ?
A: Introduction: A virtual switch can determine which virtual machines are logically linked to each of ...
Q: Are there any IoT devices that you have very little interest in trying because you don't see the ben...
A: Are there any IoT devices that you have very little interest in trying because you don't see the ...
Q: Question 1: Consider following scenario for a program running on two computers A and B. Computer A E...
A: Below is the answer to above question. I hope this will meet your requirements...
Q: In what ways may we as programmers be defensive, and what are some examples of defensive programming...
A: Defensive programming:- Defensive programming is a kind of "defensive design" that aims to guarantee...
Q: Determine potential sources of digital evidence that might pose a risk.
A: Introduction: Most people believe that digital evidence can only be discovered on computers, smartph...
Q: What function do storage reports play in file server implementation?
A: Introduction: It is sometimes referred to as a Domain Name System. When we get access to a website, ...
Q: What are the two forms of file access that exist in the world? What exactly is the difference betwee...
A: The question is what are the two forms of file access that exist in the world and what exactly is th...
Q: What is a content engine, and how does it work?
A: Introduction: Content website engine is a marketing strategy that involves attracting, engaging, and...
Q: Write a recursive function np(n) which takes a non negative n and generates a list of numbers from n...
A: Below recursive function np(n) which takes a non negative n and generates a list of numbers from n+...
Q: the chemical changes that occur within the earth and on its surface. Geochemistry Petrology Physical...
A: I have answered both the questions and will understand their studies.
Q: Using Hill-climbing search, transform the initial-state 8-puzzle to goal-sate ...
A: Answer:
Q: What are three examples of information system applications in a collegiate setting?
A: Please find the different applications of the collegiate systems.
Q: In the cloud, what is scalability? Is scalability supported by cloud computing's features?
A: In cloud, scalability means according to the demand ability to add resources or decrease resource t...
Q: ow to convert 500 KB to MB?
A: According to the Question below the Solution:
Q: Mobile Device Operating Systems Discuss your mobile device and its operating system (and version). ...
A: The mobile I use is one plus nord which has oxygen 11 operating system. OxygenOS is an Android-based...
Q: How many subnets are possible in a network with a /19 CIDR? show your works on the paper.
A: INTRODUCTION: Here we need to tell that how many subnets are possible in a network with a /19 CIDR.
Q: Computer science State and explain three effective practises that can help an organisation achieve ...
A: Introduction: Continuous software development, integration, testing, deployment, and monitoring are ...
Q: Discuss about Database Schema and Database State with example? Why Relational Database Model is bett...
A: 1) Database Schema: The database schema is a visual representation of the database. A database sch...
Q: With the use of HTML and CSS, create an overlay effect whenever you hover over an image. (a) The ove...
A: In this HTML CSS Development, We have to create a HTML, CSS code which will create a overlay effect ...
Q: QUESTION 30 Which access control principle is most frequently associated with data
A: Solution - In the given question, we have to tell about the access control principle that is most fr...
Q: Let A = {2, 4, 6, 8}, B = {6, 9}, C = {4, 8}. Answer each of the following questions. Justify your a...
A: The answer is
Max Function
Statistical function is of many categories. One of them is a MAX function. The MAX function returns the largest value from the list of arguments passed to it. MAX function always ignores the empty cells when performing the calculation.
Power Function
A power function is a type of single-term function. Its definition states that it is a variable containing a base value raised to a constant value acting as an exponent. This variable may also have a coefficient. For instance, the area of a circle can be given as:
Step by step
Solved in 2 steps

- Using C# language please in Visual Studio 2022 in Windows Form App. As for the folder-- for convenience sake-- create some folders and insert a couple of names in there, not 200.The __________ control displays a standard Windows Save As dialog box. a. SaveAsDialog b. FileDialog c. SaveFileDialog d. StandardDialogwrite a windows forms with c# programmingyou should write a acadiemican automationthere are 4 main steps in the question1- you have login with email and password credential2-if the credentials do not exist in the database you must register the user (credentials) with email and password3-after the academician logs in the system, MARKFORM(second) will appear. in the academician can add "firstName / lastName / Mark" data for a single student .4-when the MarkForm initials you have to show all MarksData in Listbox related to only logged in user which stored the database
- Make a basic Phonebook application using SWITCH CASE with a C program . The application will display the user the menu at first (Add Entry, Edit Entry, Show All, Exit). Only when the user picks Exit from the menu will the program be terminated. The Add Entry option will prompt the user to fill out a form. Edit Entry allows the user to make changes to the details of a specific entry. The option Show All prints the whole contents of the phonebook.A memory box A contains the value of 10, memory box B contains the value of 5, and memory box C contains the value of 7. Using and additional of one variable, prepare a flowchart that would interchange the values of the 3-memory box. After processing memory box A will contain 5, B contains 7 and C contains 10. Requirements:IPOFlowchartPrompt the user for a username and password. Continue to do so until they enter Magic for the username and Palace1 for the password.
- Make a basic Phonebook application with a C program. The application will display the user the menu at first (Add Entry, Edit Entry, Show All, Exit). Only when the user picks Exit from the menu will the program be terminated. The Add Entry option will prompt the user to fill out a form. Edit Entry allows the user to make changes to the details of a specific entry. The option Show All prints the whole contents of the phonebook.n this assignment, you are required to make an application using assembly code that takes two numbers from the user and returns the result of dividing the first number by the second number. Important notes: 1- You should allow the user to Enter to digits number "For the first number only" 2- You should allow two-digit results if necessary. Stretch goal "optional": Handle the remain of the division process and print it on the screen. Submission: Provide two files (.asm and screenshot). Use your university ID for files naming.String prompt = "Would you like to exit the application? Enter (y) to use exit or any other key to continue."; //Prompt user to exit the application or continue;String input = JOptionPane.showInputDialog(null, prompt, "Input", JOptionPane.QUESTION_MESSAGE); //Validate input,//If input is 'y' then exit the system. else loop againif (input.equals("y")) {//Exits the systemSystem.exit(0);} can this be changed to scanner class
- A control’s access key is specified in which of its properties? a. Access b. Caption c. Key d. TextIMP PLEASE HELP, i will give like to all your Q, PLS ASAP , pls send a screen shot of your code Create a function that manipulates a string. Also can you write a code for mainfunction for both of them please allClear Clear string (makes it an empty string) eraseString Erase characters at specified position from stringcan you varify the address for example if i do not have a "-" or a "st" then it prints out invalid put if i do then its valid document.getElementById("AddressLbl").innerHTML = ""; if (!validateVal(document.getElementById("Address").value)) { document.getElementById("AddressLbl").innerHTML = "Mandatory!" }



