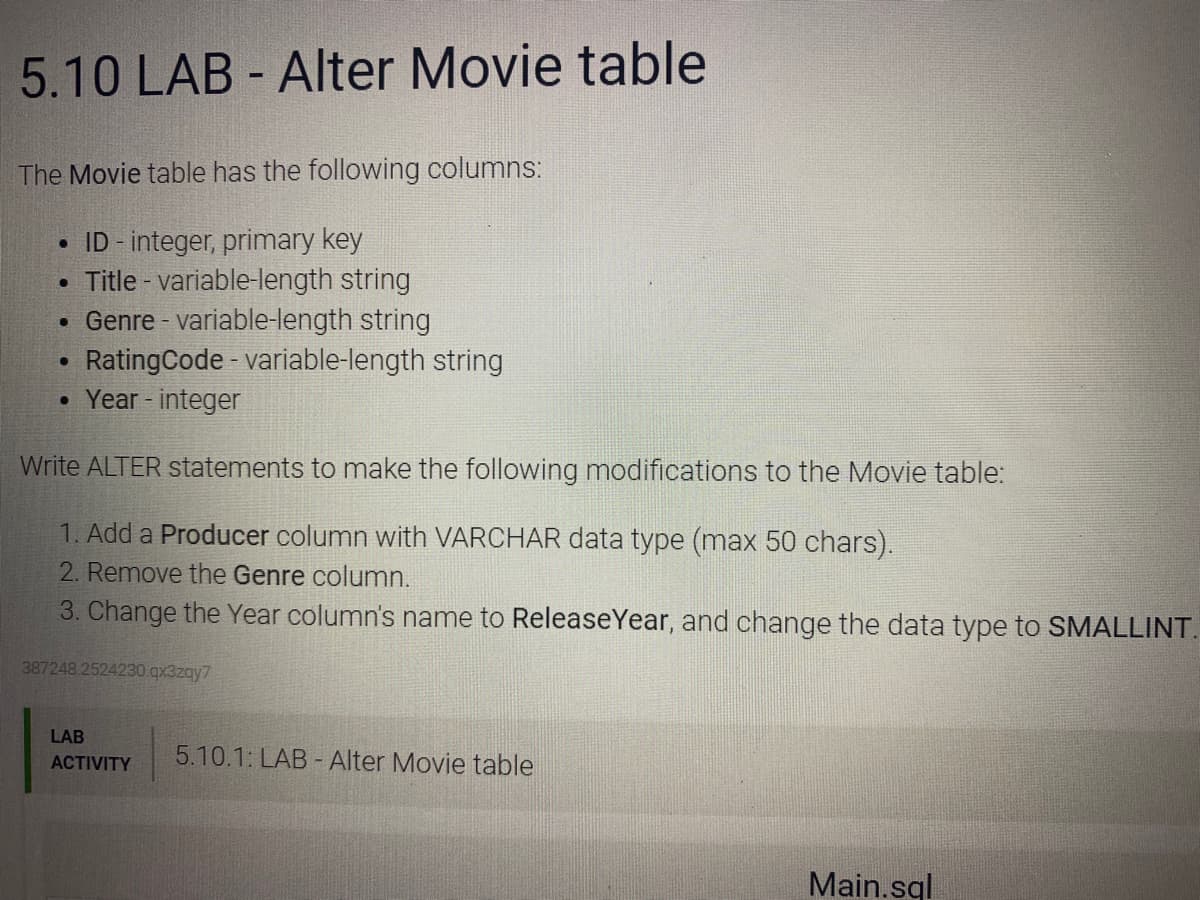
The Movie table has the following columns: ID - integer, primary key Title - variable-length string • Genre - variable-length string RatingCode - variable-length string Year- integer Write ALTER statements to make the following modifications to the Movie table:
Q: Give two separate examples when a process changes its state to waiting and ready from the running st...
A: Program in it's execution is called as Process. The process state diagram contains mainly 5 states, ...
Q: ed Engine and
A: given - C# programming question 9. Suppose an application contains a structure named Engine and that...
Q: In data integrity, mention four main considerations that are put in place to validate collar data
A: four main considerations that are put in place to validate collar data In data integrity are
Q: Consider the characteristics of big data and how data types are described in terms of data analytics...
A: Introduction: It is characterized by information flow's volume, variety, and velocity. The Amount of...
Q: e type declaration? type1 :: a -> b -> c type2 :: (a -> b -> c) -> (a,b) -> c type3 :: (a -> b) -...
A: From a Programming language Haskell, what could be a answer for these type declaration? type1 :: a -...
Q: 3. Given the following minterm expansion: F(a, b, c, d) = Em(0, 2, 3, 4, 8, 10, 11, 15) Draw the K-M...
A:
Q: Create a program that will compute the simple interest loans in the bank. The program will ask the u...
A: import java.util.Scanner;public class JavaExample{ public static void main(String args[]) { ...
Q: Which of the following refers to the network scanning techniques that indicate the active host withi...
A: In this problem we need to provide a best option that is used for network scanning techniques with a...
Q: alues for all fields. Save this class as Apartment.java. b. Write a class named showApartment that...
A: Create classes Apartment, showApartment and Renter according to the given specifications. Run the ma...
Q: NVIDIA chip set architectures: complete information please
A: The NVIDIA Turing architecture is a combination of GeForce RTX platform, It fuses together in real-t...
Q: Two threads (A and B) are concurrently running on a dual-core processor that implements a sequential...
A: We need to find the number of ways for the given thread situation.
Q: (or disprove) that n2 is 2(n²+n)
A: We are given a function f(n) which is n2 and g(n) which is n2+ n and we are going to prove n2 is Ω(n...
Q: In the physical world, what is required to create a database? Make a list of some of the most widely...
A: Introduction: A database is a structured collection of data stored and retrieved electronically in c...
Q: Take the list of elements from the user and after that, you realised that you forgot an element to p...
A: Required:- Take the list of elements from the user and after that, you realised that you forgot an e...
Q: Describe a case in which a user's total denial of a service (i.e., the user receives no answer from ...
A: INTRODUCTION: A Denial-of-Service (DoS) attack is an attempt to prevent a computer or network from f...
Q: o an existing order, include the product id, unit price, quantity. The output of the function is the...
A: given - Create a function to insert a new product into an existing order, include the product id, un...
Q: What exactly does the term "boilerplate" imply?
A: Introduction: Boilerplate is a word that refers to standardized language, copy, papers, processes, o...
Q: A Caesar cipher is a simple substitution cipher based on the idea of shifting each letter of the pla...
A: Caesar cipher is the simplest encryption and decryption technique in which we use a key to encrypt o...
Q: By default, passwords are displayed unencrypted when a 'show running-config command is executed. Wha...
A: Please refer below for your reference: The below command was used in early IOS encrypting passwords:...
Q: What function does logging play in network administration and monitoring? Distinguish between the di...
A: Introduction: The following are the functions of logs in network monitoring and management: As organ...
Q: n each of the following questions, you are given an input array A with n elements, where n is a very...
A: answer: a) the array is in decreasing order, so in quick sort we divide the array into half and proc...
Q: Write a program C++ to print the even number between 1-1000. e 5:27
A: We are going to write a C++ code which will print even numbers from 1-1000 range. We will do it usin...
Q: Write three advantages and disadvantages, of the major traffic components. Provide table
A: The distinction between disadvantage and advantage as nouns is that disadvantage is a flaw or unwant...
Q: . In this java program, explain everyline of this code. Source Code: import java.util.*; public c...
A: Algorithm: 1)This program randomly generates two number between 0 to 4 and assign it to array arr at...
Q: n̲t̲o̲ ̲m̲a̲c̲h̲i̲n̲e̲ ̲c̲o̲d̲e̲.̲ ̲A̲s̲s̲u̲m̲e̲ ̲t̲h̲e̲ ̲m̲e̲m̲o̲r̲y̲ ̲a̲d̲d̲r̲e̲s̲s̲ ̲o̲f̲ ̲t̲h̲e̲...
A: given - S̲h̲o̲w̲ ̲h̲o̲w̲ ̲e̲a̲c̲h̲ ̲o̲f̲ ̲t̲h̲e̲ ̲f̲o̲l̲l̲o̲w̲i̲n̲g̲ ̲M̲I̲P̲S̲ ̲i̲n̲s̲t̲r̲u̲c̲t̲i̲o̲...
Q: Find the output of the following code. Public class Solution{ Public static void main(String args[])...
A: The loop starts from i=1 and goes till i<6 but there is no operation being performed within the l...
Q: A Caesar cipher is a simple substitution cipher based on the idea of shifting each letter of the pla...
A: Here is the detailed explanation of the program
Q: Share TWO best IT applications that support your daily routine.
A: There are many IT applications that I use in day-in-day-out. Some of the them which are really good ...
Q: Why should you use the new operator to generate instances of a structure?
A: Introduction: New operator: Developers can now build an instance of a user-defined object type or on...
Q: 3. Consider the following set of two-dimensional vectors from three categories: W2 Ws X1 Y1 X1 Y1 X1...
A: Answer : Nearest Neighbouring Algorithmn is used for regression and additionally for classification ...
Q: Caesar cipher is a simple substitution cipher based on the idea of shifting ach letter of the plaint...
A: Code: # function for encryption passing plain text and keydef encrypt(msg,key): # initialize empty...
Q: What is database security, exactly? What are two approaches to database security?
A: Database security defines the range of tools, controls, and measures designed to establish and prese...
Q: I need a class diagram for the following scenario: An application for tracking and managing videos ...
A: Let's see the class diagram in the next steps
Q: Write a program to calculate y from the equation using (switch) statement
A: in this question, we are asked to write a C++ program to display the value of y when x in given Give...
Q: Describe a case in which a user's total denial of a service (i.e., the user receives no answer from ...
A: The Denial of Service (DoS) attack is focused on making a resource (site, application, server) unava...
Q: Matlab code for the periodic signal. Show running code and output
A: Explanation: Code works fine, I have provided screenshot and output for no error. See below step for...
Q: Provide pseudocode for a real-life range check. Explain how it works.
A: Pseudocode is an informal way of programming description that does not require any strict programmin...
Q: An If contained within another If statement is called
A: None of the above NOTE:- As no value of X is given, none of the cases will run. Missing the us...
Q: What is the point of creating inheritance relationships between classes?
A: We are going to understand why we have inheritance concept in classes and we will understand it with...
Q: A star configuration of a network represents its structure as a graph with an edge from a single, ce...
A: Here, I have to provide a solution to the above question.
Q: Given the invoice table with sample data, Please determine an appropriate Key. Then list...
A: First Normal form(1NF):According to the standard of first ordinary structure, a characteristic (sect...
Q: What is the rationale behind Angular's use of the AOT compiler
A: Introduction: During the build process, the Angular ahead-of-time (AOT) compiler turns your Angular ...
Q: In a short paragraph, explain how the DOM tree works, and how elements can be added and removed from...
A: The DOM is frequently alluded to as the DOM tree, and comprises of a tree of objects called hubs. In...
Q: Sort DNS records by the kind of record they include. Describe each with examples and a brief explana...
A: Introduction: A DNS record is a database entry that maps a web address to an IP address. DNS records...
Q: The output * x= 99; if (x++< 100) cout <<" it's true \n"; else cout <<" it's false ":
A: INTRODUCTION: In the above problem, we are given with one piece of code with initialization of varia...
Q: The MIPS assembly language command: add $t0, $s1, $s2 when converted to machine language code loo...
A: Here i explain the given command: ================================== add $t0, $s1, $s2 funct: 100000...
Q: B) Write a PYTHON script to enter a value of S (between 1 and 3) for (50) entered values of X then f...
A: In this question, we are asked to write a python program or script which sum as per the given condit...
Q: opic: Data Communication and Network (computer science) Convert the bitstream into a digital signal...
A: Data Encoding: Encoding is the process of converting data into a specified format for the secured tr...
Q: What are the 2 types of ISP?
A: ISP is Acronym of Internet Service Provider. Two types of ISP coverage exist narrowband and broadb...
Q: There is a parse element that can act as both a statement or as an expression. Which one is it? Why ...
A: Expressions, Statements, and BlocksVariables and operators, which you met in the previous two sectio...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- 12. What is the output of the following program? (2, 3, 6, 8) #include #include #include #include using namespace std; int main() { double x, y; string str; x = 9.0; y = 3.2; cout (sqrt(pow (y, 4))) = " (sqrt(pow (y, 4))) << endl; str = "Predefined functions simplify programming code!"; cout << "Length of str = " << str.length() << endl; return 0; }6 43 2 Let A-7 3 4 6 5. 1. Using the column operator (;); create a column vector that contains all the columns of A8.26 LAB: Word frequencies (dictionaries) Implement the build_dictionary() function to build a word frequency dictionary from a list of words. Ex: If the words list is: ["hey", "hi", "Mark", "hi", "mark"] the dictionary returned from calling build_dictionary(words) is: {'hey': 1, 'hi': 2, 'Mark': 1, 'mark': 1} Ex: If the words list is: ["zyBooks", "now", "zyBooks", "later", "zyBooks", "forever"] the dictionary returned from calling build_dictionary(words) is: {'zyBooks': 3, 'now': 1, 'later': 1, 'forever': 1} The main code builds the word list from an input string, calls build_dictionary() to build the dictionary, and displays the dictionary sorted by key value. Ex: If the input is: hey hi Mark hi mark the output is: Mark: 1 hey: 1 hi: 2 mark: 1 Use Python, please.
- SOB 35 - (Block 2 - material covered in Week 13) Write a function that takes a list containing characters and numbers as input (in random orders) and displays as output a string containing the character and a list containing the numbers, e.g., given the lists "("h" 1 2 3 "e" "" 4 5 "'" "o"), your method should output: "hello" and '(1 2 3 4 5 6). Please make sure to test your function and to explain how your code works.8.11 LAB: Car wash Write a program to calculate the total price for car wash services. A base car wash is $10. A dictionary with each additional service and the corresponding cost has been provided. Two additional services can be selected. A '-' signifies an additional service was not selected. Output all selected services, according to the input order, along with the corresponding costs and then the total price for all car wash services. Ex: If the input is: Tire shine Wax the output is: ZyCar Base car wash -- $10 Tire shine -- $2 Wax -- $3 ---- Total price: $15 Ex: If the input is: Rain repellent - the output is: ZyCar Wash Base car wash -- $10 Rain repellent -- $2 ---- Total price: $12 what i have so far ( services = { 'Air freshener' : 1 , 'Rain repellent': 2, 'Tire shine' : 2, 'Wax' : 3, 'Vacuum' : 5 }base_wash = 10total = 0 service_choice1 = input()service_choice2 = input() ''' Type your code here ''') but i dont know what else i need to add . 9.3 LAB:…Python 3.7.4 Write a statement that associates d with a one-entry dictionary that maps the str 'answer' to the int value 42.
- 7.19 LAB: Adjust list by normalizing When analyzing data sets, such as data for human heights or for human weights, a common step is to adjust the data. This can be done by normalizing to values between 0 and 1, or throwing away outliers. For this program, adjust the values by dividing all values by the largest value. The input begins with an integer indicating the number of floating-point values that follow. Assume that the list will always contain less than 20 floating-point values. For coding simplicity, follow every output value by a space, including the last one. And, output each floating-point value with two digits after the decimal point, which can be achieved as follows:printf("%0.2lf ", yourValue); Ex: If the input is: 5 30.0 50.0 10.0 100.0 65.0 the output is: 0.30 0.50 0.10 1.00 0.65 The 5 indicates that there are five floating-point values in the list, namely 30.0, 50.0, 10.0, 100.0, and 65.0. 100.0 is the largest value in the list, so each value is divided by 100.0.…8.19 (Removing a Particular Word From a Given Line of Text) Write a program that inputs a line of text and a given word. The program should use string library functions strcmp and strcpy to remove all occurrences of the given word from the input line of text. The program should also count the number of words in the given line of text before and after removing the given word using the strtok function. Solve it Without using pointersDo question 11. Q11. Provide the output for the given C++ code about pointers. #include <iostream>using namespace std;int main(){char *ptr;char Str[] = "abcdefg";ptr = Str;ptr += 5;cout << ptr;return 0;} Q12. Provide the output for the given C++ code about arrays. #include <stdio.h>#include<iostream>using namespace std;int array1[] = {1200, 200, 2300, 1230, 1543};int array2[] = {12, 14, 16, 18, 20};int temp, result = 0;int main(){for (temp = 0; temp < 5; temp++){result += array1[temp];}for (temp = 0; temp < 4; temp++){result += array2[temp];}cout << result;return 0;} Q13. Provide the output for the given C++ code about arrays. #include <stdio.h>#include<iostream>using namespace std;int main (){int array[] = {0, 2, 4, 6, 7, 5, 3};int n, result = 0;for (n = 0; n < 8; n++){result += array[n];}cout << result;return 0;} Q14. Provide the output for the given C++ code about arrays. #include <stdio.h>#include <iostream>using…
- 9. Write function getMoveRow to do the following a. Return type integer b. Parameter list i. 1-d character array (i.e. move), size 3 c. Convert the row portion of the player’s move to the associated integer index for the board array d. Example: i. move = ‘b2’ ii. 2 is the row iii. 2 is index 1 in the board array e. Return the row array index that corresponds to the player’s move f. Return a -1 if the row is not valid (i.e. INVALID) 10. Write function getMoveCol to do the following a. Return type integer b. Parameter list i. 1-d character array (i.e. move), size 3 c. Convert the column portion of the player’s move to the associated integer index for the board array d. Example: i. move = ‘b2’ ii. b is the column iii. b is index 1 in the board array e. Return the column array index that corresponds to the player’s move f. Return a -1 if the column is not valid (i.e. INVALID) I am getting an error when entering the code at the very end. please fix it. This is the code in C int…22.3 LAB: Remove all even numbers from a list (Use Python) Write the remove_evens() function, which receives a list of integers as a parameter and returns a new list of integers containing only the odd numbers from the original list. The main program outputs values of the returned list. Hint: If the original list has even numbers, then the new list will be smaller in length than the original list and should have no blank elements. Ex: If the list passed to the remove_evens() function is [1, 2, 3, 4, 5, 6, 7, 8, 9], then the function returns and the program output is: [1, 3, 5, 7, 9] Ex: If the list passed to the remove_evens() function is [1, 9, 3], then the function returns and the program output is: [1, 9, 3]TODO 12 Let's now split our input data X and labels y into a train and test set using the train_test_split() function (docs). Here we'll use the 80-20 split rule where we use 80% of the data for training and 20% for testing. Lastly, we'll seed our split using the random_state keyword argument which will make sure we create the same split every time we run the function. Use the train_test_split() function to get a train and test split. Store the output into X_train, X_test, y_train, and y_test. Pass the required arguments X and y. Further specify we want to use 20% of the training data by setting the test_size keyword argument. Lastly, pass the keyword argument random_state=42 to set the random seed so we get the same split every time we run this code. Print the shape for X_train. Print the shape for y_train. Print the shape for X_test. Print the shape for y_test. # TODO 12.1X_train, X_test, y_train, y_test = todo_check([ (X_train.shape == (413, 29), 'X_train does not have the…

