The National Security Agency (NSA) is in need of a program that will store a message, encrypt the message using a hash function and decrypt the message. They need something simple that works as soon as possible as the agent sending the message via Bluetooth technology will only be near the infiltrated agent for a couple of seconds.
Q: Describe benefits of REST over SOAP.
A: The answer is given below.
Q: Write for statements that print the following sequences of values: c) 30, 20, 10, 0, –10, –20, –30
A: Due to company policies I am compelled to solve only one question and that is the first part. Please...
Q: There are no cycles in a DAG, only directed edges. Graphs can be dense (with many edges) or sparse (...
A: INTRODUCTION: ARRAY: Arrays are collections of items stored in a series of contiguous memory locatio...
Q: You have a binary tree with 12 levels of nodes. Every level is full except the last level that is ex...
A: Number of nodes in the tree will be : 3071
Q: Use the isPrime() method that you wrote in (a) above to write a short program segment that uses a fo...
A: STEP 1: START STEP 2: define a function isPrime(n) STEP 3: result = True STEP 4: if n < 2 then ...
Q: When you open a photo and then resize the frame, what happens? What if you resize the frame first, t...
A: Image Processing:- Image Processing is defined as a technique in which we collect some information ...
Q: You may decrease the quantity of spam you get by using opt-out links. What do you think?
A: Given statement: The most safe and trustworthy approach to decrease the quantity of spam you get is...
Q: The user of an insulin pump device must change the needle and insulin supply on a regular basis, as ...
A: Introduction: When a safety-related system or component fails to work correctly in such a manner tha...
Q: The cloud is protected by implementing a shared responsibility model and implementing identity acces...
A: In order to ensure responsibility, an accountability model is a cloud security architecture that des...
Q: What is the distinction between uncertainty and risk?
A: Intro Risk and uncertainty are both associated with the project on which team is working.
Q: Let's say a top secret user wishes to utilise a file existence covert channel to leak the PIN number...
A: Introduction: A database with multilevel security has data that has been categorise and, as a result...
Q: What are the primary distinctions between a phone network and a high-speed Internet connection?
A: Introduction: A telephone network can only allow voice conversations in the 300 Hz to 3400 Hz audio ...
Q: language program which should display 4 items (keyboard, mouse, monitor and speaker) with their prod...
A: Note: As not mentioned I have solved the question in Python language Code: name = ["keyboard", "mo...
Q: Write a program that asks the user to entera floating point numbers representing the radius ,r and h...
A: Define a macro named PI and initialize with value Then we can calculate the volume
Q: Consider Figure 2.12, for which there is an institutional network connected to the Internet. Suppose...
A: Introduction Consider Figure 2.12, for which there is an institutional network connected to the Inte...
Q: Explain the use of the Interoperability matrix in the formulation of a purposed Enterprise Architect...
A: According to the question we need to explain giving examples the application of the Interoperability...
Q: The cloud is protected by implementing a shared responsibility model and implementing identity acces...
A: Introduction: Identity and access management (IAM) allows your organization's appropriate workers an...
Q: State which values of the control variable x are printed by each of the following for statements: d)...
A: I wrote a code which includes both parts.
Q: void administerExam(String examFile) { // readExamItems() is used to retrieve the 1ist of examinatio...
A: Solution : we have given code screenshot and we have to find some missing information so we will see...
Q: Explain briefly the controls you would consider for protecting your organization's network against c...
A: Protection of organization network against cyber threats. Day in and day out we receive cases from ...
Q: Give an example of a data structure for which no plausible array- or link- based solutions exist. Wh...
A: Introduction: The simplest data structure is an array, which allows each data element to be retrieve...
Q: Describe benefits of REST over SOAP.
A: REST: It stands for Representational state transfer and helps in transferring the data between the s...
Q: An airline in Pakistan might use any one of five different marketing orientations to help shape its ...
A: INTRODUCTION: Pakistan Airlines can pursue the following marketing orientations to help guide its ma...
Q: Consider diagrams below. List rule violations on these diagrams Context Diagram DF3 Ship Cap & Gown ...
A:
Q: What is the difference between a subsystem and a logical subdivision, and why is it important?
A: Introduction: The blocks are logically divided at the common plate joints. Arrows pointing inwards i...
Q: What precisely is random access memory (RAM)? Make two separate lists of items. Computer science
A: Introduction RAM stands for "random access memory" in computers, and while it may seem cryptic, RA...
Q: What is the status of technology now, as well as the many types of technical systems?
A: Introduction: We live in the twenty-first century, and technology is at its pinnacle. New artificial...
Q: Discuss the five most critical security characteristics of a so ftware-as- a-service-based business ...
A: Introduction Software-as-a-service-based business : Software as a Service (SaaS) is also known as we...
Q: Q2: The signal-to-noise ratio in decibels. SNR = 36 and the channel bandwidth is 4 MHz. Compute The ...
A: 2. It is given that the signal to noise ratio in decibels. Bandwidth = 4 MHz = 4 * 10 6 Hz SNR dB = ...
Q: Define computer environment in your own terms and describe THREE distinct kinds of computing environ...
A: Define computer environment The term computer environment alludes to the condition of a PC, dictated...
Q: - Explain what is Cryptocurrency, how it gains its value? what is the future of Cryptocurrency?
A: Due to company policies I am compelled to solve only one question and that is the first question. Pl...
Q: Describe the steps involved in the processes of authentication, authorisation, recording, and auditi...
A: Authentication, authorization, and accounting are acronyms for authentication, authorization, and ac...
Q: In terms of advice and conclusions, what can we draw from cybercrime ?
A: Introduction: The goal of cybercrime is to make money, damage equipment, or disseminate viruses or u...
Q: Describe how you picture e-mail in your head. Where does an email message originate? Make a list of ...
A: Introduction: When using email, be sure to follow proper etiquette and safety precautions, just as y...
Q: 10, and 1. Suppose that a1 = 5, a2 ak = ak-1 + ak-2 for k = 3, 4, . . Use strong induction to prove ...
A: Please upvote. I am providing you the correct answer below.
Q: No, I don't think it was an inside job that caused the current security breach concerning access con...
A: NOTE :- Below i explain the answer in my own words by which you understand it well. As organiza...
Q: Python Array's which tunction will remove the element with value? O remove() O pop0 O append() O ext...
A: Here in this question we have asked that in python arrays which function will remove the element wit...
Q: Only the register addressing mode was supported by a datapath. In this instance, which component of ...
A: Intro ALU data storage and retrieval reminiscences of instructions registers ALU: ALU is an abbrevi...
Q: Describe the interface and implementation in brief. How are the many components of planned software ...
A: Introduction: The interface is that part of a class that is accessible to the outside, namely what i...
Q: When it comes to overall performance, interrupt-driven operating systems beat non-interrupted ones
A: Let's first understand what is interrupt driven operating system . As the name suggest the interrup...
Q: Provide at least five rules for the knowledge base and one fact for working memory in a topic where ...
A: Introduction: In contrast to long-term memory, which is the enormous amount of information retained ...
Q: Explain why legacy systems should be seen as sociotechnical systems rather than just software system...
A: Introduction: A legacy system, within the context of computing, refers to superannuated laptop syste...
Q: What precisely is autonomic computing, and how does it contribute to the advancement of cloud comput...
A: Introduction: Autonomous computing refers to the self-managing qualities of distributed computing re...
Q: Security issues in buying and merchandising systems are what? Make note of what happened, as well as...
A:
Q: In what ways was a meeting hijacked? If someone were to attack you, how would you protect yourself?
A: Introduction: Session Hijacking is a kind of attack that allows an attacker to get unauthorized acce...
Q: What is the output from the following program? #include #define AMT1 a+a+a #define AMT2 AMT1 - AMT1...
A: Given To know about the C programing .
Q: Different ideas and principles relating to security management should be discussed in detail.
A: Introduction: Security management concepts and principles must be incorporated into both the securit...
Q: What is the decimal equivalent of the binary number 1100110110110100 written in excess-15 notation? ...
A:
Q: Using c++ Basic student grade encoding program instructions: 1. Create a simple program that would l...
A: According to the question, first take the student name, year and section, and 3 subject grades from ...
Q: What difficulties does an operating system need to address when implementing a concurrent multithrea...
A: INTRODUCTION: The operating system itself provides support for kernel threads.Multithreaded programm...
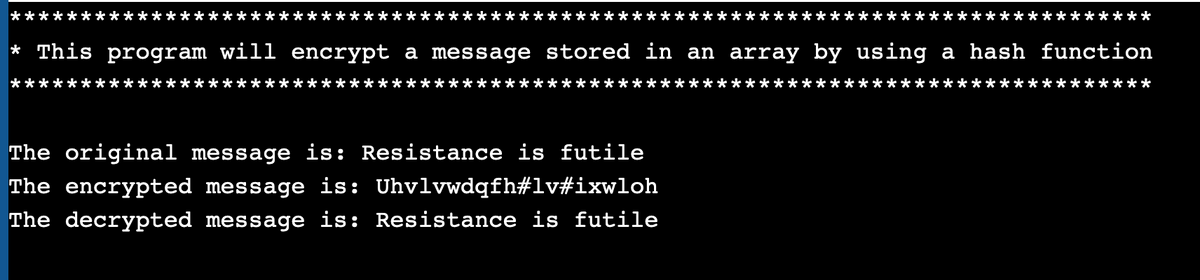
The National Security Agency (NSA) is in need of a
Your mission if you accept it will be to create a C++ program that stores the message in an array, encrypts the message, and decrypt the message. Please see the output example below
Step by step
Solved in 3 steps with 1 images

- java random matches. Write a BinarySearch client that takes an int value T as a command-line argument and runs T trials of the following experiment for N = 103, 104, 105, and 106: generate two arrays of N randomly generated positive six-digit int values, and find the number of values that appear in both arrays. Print a table giving the average value of this quantity over the T trials for each value of N.PLEASE CODE IN PYTHON Crypto Columns The columnar encryption scheme scrambles the letters in a message (or plaintext) using a keyword as illustrated in the following example: Suppose BATBOY is the keyword and our message is MEET ME BY THE OLD OAK TREE. Since the keyword has 6 letters, we write the message (ignoring spacing and punctuation) in a grid with 6 columns, padding with random extra letters as needed: MEETME BYTHEO LDOAKT REENTH Here, we've padded the message with NTH. Now the message is printed out by columns, but the columns are printed in the order determined by the letters in the keyword. Since A is the letter of the keyword that comes first in the alphabet, column 2 is printed first. The next letter, B, occurs twice. In the case of a tie like this we print the columns leftmost first, so we print column 1, then column 4. This continues, printing the remaining columns in order 5, 3 and finally 6. So, the order the columns of the grid are printed would be 2, 1, 4, 5, 3, 6, in…in c++ Create a student hash table that contains information, studentID (int), name (string), marks_oop345 (float). The size of hash table is equal to the number of students in the class. Use linear probing in case of collisions. Perform insertion, deletion, display and search operations.
- Create a file named minesweeper.pyCreate a function that takes a grid of # and -, where each hash (#) represents amine and each dash (-) represents a mine-free spot.Return a grid, where each dash is replaced by a digit, indicating the number ofmines immediately adjacent to the spot i.e. (horizontally, vertically, anddiagonally).Example of an input:[ ["-", "-", "-", "#", "#"],["-", "#", "-", "-", "-"],["-", "-", "#", "-", "-"],["-", "#", "#", "-", "-"],["-", "-", "-", "-", "-"] ]Example of the expected output:[ ["1", "1", "2", "#", "#"],["1", "#", "3", "3", "2"],["2", "4", "#", "2", "0"],["1", "#", "#", "2", "0"],["1", "2", "2", "1", "0"] ]C++ Quadratic Probing: You have a file called athletes.txt Jamie, basketball Justine, soccer Ned, badminton Shelley, hopscotch etc... The file contains 9 athletes. The user will specify the size of the hash table. Write a function that keeps track of the total number of collisions and searches into the hash table. Each index is assigned hash_index = i % table_size where "i" is an int in a for loop up to table_size If the table is full then: int t = (hash_index + i* i) % table_size; Display the number of collisions and searches.java program: If in the ArrayStack, the first element that we push to the stack, is stored in location capacity – 1 (capacity is the capacity of the array theData) in the array theData and the subsequent elements that we push, we keep on adding before the last element added in the array. That is, in the constructor of class ArrayStack, we initialize the topOfStack to capacity and we write the push method as follows: public E push(E obj) { if (topOfStack == 0) reallocate(); topOfStack--; theData[topOfStack] = obj; return obj; } This push method can work but the if statement should be: if (topOfStack == theData.length - 1) reallocate(); This push method will work provided we modify the reallocate method. This push method can work, but topOfStack-- ; should come after theData[topOfStack] = obj; This push method can work, but topOfStack-- ; should be topOfStack++;
- Complete the method loadBuses(String bfile) that reads information bus information from afile (bfile contains the filename) . Each row in the file should trigger the creation of aninstance of bus or an appropriate subclass, according to the data in table 1. All buses createdshould be added to an arraylist. LoadBuses should return the populated arraylist. public ArrayList<Bus> loadBuses(String bfile ) { Scanner bscan = null; ArrayList<Bus> blist = new ArrayList<Bus>(); return blist; }Find a duplicate . Write a program FindDuplicate.java that reads n integer arguments from the command line into an integer array of length n, where each value is between is 1 and n, and displays true if there are any duplicate values, false otherwise. Example: java FindDuplicate 2 10 8 5 4 1 3 6 7 9false java FindDuplicate 4 5 2 1 2trueAn array may contain multiple duplicate values, as shown below. In order to design an algorithm with the best average performance to remove all duplicate values, which of the following data structures should be used? 110, 1100, s, 10, s6, s, 96, 34, s, 34, 20, 110, 30 Question 16 options: hash table stack list priority queue
- This problem is based on Hashing. Please use Python and do not make it overly lengthy and complicated making it difficult to understand. PLEASE USE PYTHON and do not make the code too difficult to understand. Keep it simple. Thanks Given an array containing Strings, you need to write a code to store them in a hashtable. Assume that the Strings contain a combination of capital letters and numbers, and the String array will contain no more than 9 values. (total number of consonants*24 + summation of the digits) %9. In case of a collision, use linear probing.For a String “ST1E89B8A32”, it’s hash function will produce the value=(3*24+(1+8+9+8+3+2))%9=4, hence it will be stored in index 4 of the hash table.PYTHON import randomrandom.seed = 1 class array: def __init__(self, valuelist): self.__atos = valuelist.copy() # this variable is the array that holds the data def additem(self, value): # adds a item to the array def printarray(self): # prints the self.atos def __contains__(self, key): # To test the binary search change the "__linearsearch" to "__binsearch" return self.__linearsearch(key) def __linearsearch(self, key): # Implements the linear search to find an item in the array ####################################################################### # Remove the pass and write code ####################################################################### pass ####################################################################### # End code ####################################################################### def __binsearch(self, key): temp = sorted(self.atos)…Problem Given the target file f0 and candidate files f1-f20, there is an identical copy of f0 among the files f1-f20. Write a python program to perform the following tasks: · Read in each file and calculate the hex hash values by using SHA3 function with the length of 512 for all the given files f0, f1-f20. · Save the hex hash values of each file as a new line in a .txt file named hash.txt file. · Read hash values from hash.txt and compare them to find the identical copy of f0 among f1-f20. · Write the finding result (the matched file name) back to hash.txt Submission • Name your project fileHash.py and submit both fileHash.py and hash.txt on Blackboard. • The program should be properly documented. • The program should have user friendly Input/Output design • Duplicate work (or obviously similar one) will result in an F grade in the course. Grading 1. Include comments as specified in the course syllabus. (10%) 2. Source code and results. · Correctness (70%) · User-friendliness…

