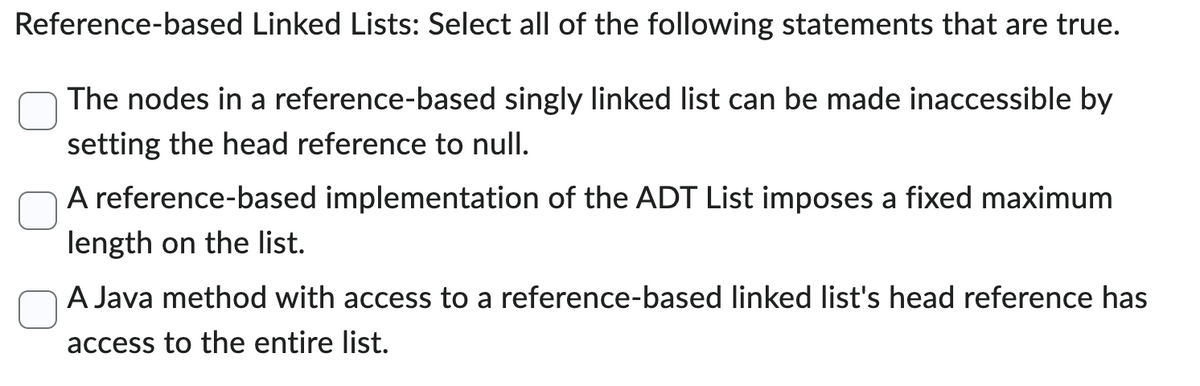
The nodes in a reference-based singly linked list can be made inaccessibl setting the head reference to null. A reference-based implementation of the ADT List imposes a fixed maxin length on the list.
Q: What is the difference between POP3 and IMAP Mail Server?
A: The answer to the question is given below:
Q: Is there a comprehensive catalog of malicious software and the harm they cause?
A: The study of secure communication techniques that allow only the sender and intended recipient of a…
Q: If you're working on a software team to create a smartphone user interface, you'll need to have a…
A: Introduction: GivenUser interfaces take a lot of work to build. A team has five tasks to implement…
Q: If the company's initial Network Address (NA) is known as as follows : 172 . 20 . 0 . 0 /16 What is…
A: Introduction: An IP host is a machine that participates in networks that utilize the Internet…
Q: Explain what is the role of network administrator?
A: A computer network's daily operations are managed by network administrators. They are in charge of…
Q: How to configure Proxy Server in Windows?
A: The question is solved in step2
Q: nd text typing work only We should answer our question
A: Consider the employee table with : Employee Table with attributes [Empid] [int] NULL,[Projectid]…
Q: This game requests a number from the player. The game then throws the dice that number of times. The…
A: The question is to write JAVA code for the problem.
Q: The routing protocol has led to the discovery of how many networks?
A: Routing protocols share routing information between routers for routing choices. Routers must know…
Q: TASK 2.4 Implement the missing code for the method specialize(specialization_map) of class…
A: Coded using Python 3.
Q: Learn to address common problems with Linux by exploring its documentation.
A: Definition: Linux hardware issues may develop for a variety of reasons. Before attempting a…
Q: What exactly is a paradigm, and what does a paradigm shift in human-computer interaction imply?
A: PARADIGM: Everyone is subject to restrictions, thus paradigms play a crucial role in how we see…
Q: • Create a sequential file Students.txt and open it for output. Allow the user to input the…
A: The solution is given in the below steps
Q: Explain why WINS server is required?
A: INTRODUCTION: The WINS server is a server that runs Windows Internet Name Service (WINS) and is…
Q: What is the maximum theoretical data transfer speed between an IEEE 802.11g rated HP laptop and…
A: IEEE 802.11g-2003 or 802.11g is an amendment to the IEEE 802.11 specification that operates in the…
Q: Specifically, how does one define and attain a state of consistency in a database?
A: The answer to the question is given below:
Q: A G B F C E D
A: In this question we need to find the Breadth-First Search (BFS) traversal by applying Breadth-First…
Q: In order to successfully complete this assignment, you will need to perform research, create a list…
A: If an "anti-pattern" is simply the opposite of a "pattern," which is just a known-to-work solution…
Q: The following C code is a formula representing the Volume of a Sphere. Convert into MIPS code. (You…
A: ANSWER:-
Q: Consider the following C-statement(s). Assume that the variables f, g, h, i, and j are assigned into…
A: ANSWER:-
Q: ames of people separated by spaces and newlines. The second file is called scam.txt which contains a…
A: #include <iostream>#include <fstream>#include <string> using namespace std; int…
Q: In your own words, define the terms used in human-computer interaction (HCI).
A: Introduction: HCI is the study of how to design computers and devices to best serve their users…
Q: etail how the ICT department can quickly and effectively provision software including the Operating…
A: Lets see the solution.
Q: How to perform subnet addressing?
A: Dividing large network into many small networks is called as Subnetting. In the process of subnet…
Q: We'll go through the key features and benefits of descriptive models in more detail down below.
A: DESCRIPTIVE MODEL: Descriptive research is a kind of research approach that explains all of the…
Q: When we connect to the internet, we move from one LAN technology to another. How should the TCP/IP…
A: Introduction: LAN stands for - Local Area Network, and it is made up of a collection of computers…
Q: In the context of company performance management, please explain how obtaining a better…
A: Please go to the next step for a solution. Any new project, service, or initiative created at work…
Q: What exactly is a "mini laptop," and how does it perform its functions?
A: Introduction A mini laptop is a scaled-down version of a standard laptop, and is formally known as a…
Q: Write Algorithm to Constructing dead reckoning messages. Dead-Reckoning-Message(s,t,P,Q) in: state…
A: data supplied time stamp t, prediction data P, state value s, and previously communicated state…
Q: For the initial post, choose the method you think is the best method to manage a database -- by…
A: The question is solved in step2
Q: Using the cloud for computing What is involved in SLA management?
A: Service Level Accord: A service level agreement is a contract that specifies, generally in financial…
Q: Write a note on Schema of DTD.
A:
Q: is question and text typing work only We should answer our question within 2 hours tak
A: Dear Student, As no programming language is mentioned, I am assuming it to be Python. The correct…
Q: Write a recursive implementation of Euclid’s algorithm for finding the greatest common divisor (GCD)…
A: According to the information given:- We have to write a recursive implementation of Euclid’s…
Q: How to perform subnet addressing?
A: WHAT IS SUBNET Subnetting is the technique of dividing a larger network into smaller sub-networks…
Q: Write a python Program to find out the prime numbers not exceeding 100.
A: find the prime number not exceeding 100 using python program
Q: What are the functions of the various parts of a computer?
A: Because of how computers function, they are basically computational tools. Additionally, it may be…
Q: Using the program in Figure 3.23, identify the values of pid at lines A, B, C, and D. (Assume that…
A: I have answered below:
Q: Prefixes For a list L, the prefix of L of length n is the first n items of L. For example, the…
A: def allPrefixes(L): prefixes = [[]] for i in range(len(L)): prefixes.append(L[:i+1])…
Q: Identify four distinct external disk interfaces.
A: An interface conveys data or information between input and output devices by acting as a channel…
Q: Why would someone choose to use visuals over text and vice versa?
A: It is recommended to use visual over text in case - As all humans have a brain and brain process…
Q: Exists a specific type of candidate system that could be used in the creation of a system?
A: Introduction: A need is an essential aspect of a new system that may involve data processing or…
Q: A database analyst has developed the following ER Diagram for a small company. WORKER Status…
A: so we are adding dash hypens before each line in text file containing business rules using python
Q: What is DORA process?
A:
Q: Using the program in Figure 3.23, identify the values of pid at lines A, B, C, and D. (Assume that…
A: Here we have given solution for the given task. You can find the solution in step 2.
Q: To what precisely does the NRZ problem pertain? And, what is maybe more significant, what possible…
A: No Going Backwards: Ones are typically represented by a positive voltage in NRZ line code, while a…
Q: What are the different types of fields included in the instruction process?
A: The three fundamental instruction fields are Opcode, source address, a destination address, and…
Q: Let f(x) = sin(ex). Find the ƒ'(x) by using limit definition of the derivative and compare your…
A: The solution is given in the below step
Q: Explain The Lists in HTML.
A:
Q: State Advantages of DTD.
A: DTD stands for Document Type Definition. It is a document that defines the structure of an XML…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- import java.util.ArrayList; /** * This class describes a user of Twitter. A user has a user ID * (e.g. @testudo), a list of tweets, a count of the number of followers, * and a list of users that this user follows. Unlike P5, * there is no upper limit on the number of tweets or users to follow. * * You may NOT import any library class other than java.util.ArrayList. * You may NOT add any instance variables to keep a count of the number * of tweets or users being followed. You may add instance variables * for other purposes as long as they are private. */public class TwitterUser { private String userID; private int followers; private ArrayList<Tweet> listTweets; private ArrayList<TwitterUser> toFollow; /** * A constructor that takes the user's ID. If the ID is null, or * longer than 32 characters, or it does not start with "@", * throw an IllegalArgumentException. * * All other instance variables should be initialized…Create a SameItem Interface: The SameItem interface will be a generic interface.SameItem will have a single method: isSameAs(T) that returns a booleanPlease, help me to do this in Java. Create a program to view the waiting list. The list (5 entries) is created in the program and is an object of the LinkedList class. The list entry is a QueuePerson object that contains the queue's last name, first name, and patronymic fields (of type String), an AddressValue field for the queue's address, and queue priority (int type). In turn, the field of the AddressValue type contains three fields of the String type: the name of the city, the name of the street and the house number, as well as an int type field - the apartment number (if the apartment number is 0, the house in which the subject lives does not have apartments). Entries in the queue are sorted according to priority, and the queue is added last in the queue of its priority. Provide the possibility of receiving so that there is no repetition in the queue by the name of the person on the waiting list, for which use TreeSet.
- Java Program: There are errors in the lexer and shank file. Please fix those errors and there must be no error in any of the code at all. Below is the lexer, shank, and token files. The shank file is the main method. There is a rubric attached as well. Lexer.java import java.util.ArrayList;import java.util.HashMap;import java.util.List; import mypack.Token.TokenType; public class Lexer { private static final int INTEGER_STATE = 1;private static final int DECIMAL_STATE = 2;private static final int IDENTIFIER_STATE = 3;private static final int SYMBOL_STATE = 4;private static final int ERROR_STATE = 5;private static final int STRING_STATE = 6;private static final int CHAR_STATE = 7;private static final int COMMENT_STATE = 8; private static final char EOF = (char) -1; private static String input;private static int index;private static char currentChar;private static int lineNumber = 1;private static int indentLevel = 0;private static int lastIndentLevel = 0; private static…JAVA Create a new class HashMapManipulation with a main method. Import the necessary classes from the java.util package, including the HashMap class. Create a HashMap object, named mapand use the put() method to add key-value pairs to the map. The keys are strings "A", "B", and "C", and the values are integers 1, 2, and 3 respectively. Use the size() method to print the size of the map. Use a for loop to print the key-value pairs in the map. The loop should iterate over the entries in the map using the entrySet() method, which will return a set of Map.Entry objects representing the key-value pairs in the map. The key and value of each entry are printed using the getKey() and getValue() methods, respectively. Use theget() method to get the value of key "A", and assigns it to a variable value. The value is then printed. Use the put() method to add a new key-value pair to the map. The key is "D" and the value is 4. The map is then printed again, to show the added key-value…Consider the LinkedList in the given figure. Assume that the nodes are objects of the ListNode class given below. Assume further that list, ptr1 and ptr2 are reference variables of the ListNode type. Write a Java statement (one statement only) to make ptr2 point to the node containing the info 44. * list 18 32 23 16 43 25 44 . null ptri ptr2 public class ListNode<T> { private T info; private ListNode<T> link; public ListNode(T info, ListNode<T> link) { this. info = info; this.link = link; public void setInfo(T info) { this. info = info; public void settink(ListNode<T> link) { this.link = link; public T getInfo() { return info; public ListNode<T> getlink() { return link;
- A Maze Room : In this lab, we will make a maze game. The maze is based on Linked Lists. Instead of having one possible direction (next), we will have 4 possible directions. Rooms: Use the below code as a basis to build your own room class. Implement this class in the file room.py A room will be the basic object for our maze game. A room can have 4 doors (pertaining to north, south, east, and west). Attached to each these directions we have either another room or None (we could also imagine that the None doors are just walls). We want the player to be able to tell what room they are in. Each room will have a unique description. When the player enters a room, the program will describe the room. This way the player will know if they went back to a room that have already been to. You MAY NOT change the method's arguments/names in ANY way. class Room():def __init__(self, descr):#Description of the room to print out#These should be unique so the player knows where they areself.descr =…Java Collection Framework. (https://docs.oracle.com/javase/8/docs/technotes/guides/collections/overview.html) A collectionis an object that represents a group of objects. There are several classes that implement the collection interface. Examples of them are ArrayList, HashMap and LinkedList. Please make a report for each of ArrayList, HashMap and LinkedList including the description of the class and its major methods. Please specify the 3 real world problems to apply each class (ArrayList, HashMap and LinkedList). Make 3 code snippets to solve the real-world problem. The code snippet can be written in pseudo code. In the code snippets, please create an instance of each of the class, and use its key methods. Make sure the # of key methods in use for each class should be over 6.Python For this assignment, you will write a program to allow the user to store the names and phone numbers of their contacts. Create the following classes: Contact: two attributes. One for the contact's name and the contact's phone number. Node: two attributes: _data and _next. For use in a linked list. ContactList: One attribute: _head, a reference to the head of an internal linked list of Node objects. Note: self._head is an attribute of the class, so any method which updates the internal linked list can simply update the list self._head references. There is no need to return anything like we did in methods such as add_to_end in the lecture. Note also that for the same reason, we do not have to pass a reference to the head of the list to any method, because each method should already have access to the self._head attribute. ContactList should also have the following methods: add(name, new_number). Creates a new Node with a Contact object as its _data. The new Node is then added…
- Implement LinkedListclass for this problema.Create an Employeeclass which will have details like EmployeeNo, EmployeeName and Address. You should pass value for EmployeeNo, EmployeeName and Addressthrough constructor.b.Create a method addInput( ) which will add employee details to LinkedList.c.Create method display( ) which should display all data from LinkedList using forward and reverse order using Iterator and ListIterator interfaces.d.Note:addInput( ) and display( ) should not be member functions of EmployeeclassIn Java, Question 15: Answer the following questions You are asked to Implement an ADT for MyQueue. The following is a class definition of a linked list Node: class Node { String content; Node next; } The following is a class definition of a linked list MyQueue: class MyQueue { Node head; } Implement the following methods for your class MyQueue. a) Constructor that does not requre any parameters b) Constructor that accepts a parameter of type MyQueue and creates a new instance of MyQueue that is a clone of the one passed as parameter c) public int AppendCopy method that accepts a single parameter of type MyQueue and clones all elements from the MyQueue instance passed as a parameter and appends them to the instance on which we called the method. Return the number of elements that are cloned and appended d) public int FindElements(String filter) - finds all elements that match the filter and returns their count e) overload the FindElementsmethod to include a…Complete the following class with the appropriate methods shown in the rubric import java.util.HashMap; import java.util.Set; /** * Stores and manages a map of users. * * @author Java Foundations * @version 4.0 */ public class Users { privateHashMap<String, User> userMap; /** * Creates a user map to track users. */ publicUsers() { userMap = newHashMap<String, User>(); } /** * Adds a new user to the user map. * * @param user the user to add */ publicvoidaddUser(Useruser) { userMap.put(user.getUserId(), user); } /** * Retrieves and returns the specified user. * * @param userId the user id of the target user * @return the target user, or null if not found */ publicUsergetUser(StringuserId) { returnuserMap.get(userId); } /** * Returns a set of all user ids. * * @return a set of all user ids in the map */ publicSet<String> getUserIds() { returnuserMap.keySet(); } }

