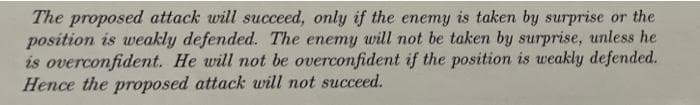
The proposed attack will succeed, only if the enemy is taken by surprise or the position is weakly defended. The enemy will not be taken by surprise, unless he is overconfident. He will not be overconfident if the position is weakly defended. Hence the proposed attack will not succeed.
Q: QL Help I need to create a PL/SQL trigger called aprove_rental that will prevent an INSERT if a clie...
A: Code create table client (client_num char(4), client_lname varchar2(15) not null, client_fname varc...
Q: Using C Language, write a program: PROGRAMMING EXERCISES 7-5 Write a program that takes nouns and ...
A: The Answer is
Q: 1. Explain the following with suitable examples. a. Keyword, Topic and Placement Targeting b. Ad s...
A: Introduction: Digital marketing, is additionally called Internet marketing or Online Marketing, is u...
Q: Given matrix A, assign the second column of A to a
A: Given Given matrix A, assign the second column of A to a variable v. Afterwards change each element ...
Q: 1ist is best to answer questions such as "What is the item at position n?" À. Lists implemented with...
A: The answer for the given question is as follows.
Q: Consider a 16-bit binary floating point number representation system: + SE EE EEE m | m | m т т т т ...
A:
Q: Write MIPS assembly code for the following C program. Use the stack pointer (sp) to store the return...
A:
Q: Four criteria were defined for comparing search strategies: completeness, optimality, time complexit...
A: DFS which stands for Depth First Search is designed in a way which will go to each child first if a ...
Q: Which Win32 function moves the file pointer to a specified offset in relation to the beginning of a ...
A: A 32-bit API for Windows 95 and later is known as Win32. As with Win16, the API is comprised of func...
Q: Explain to me how to implement a generic linked list from scratch (Java) step by step (note: do not ...
A: Linked list : It is an ordered set of data elements, each containing a link to next link. Steps of ...
Q: List and describe each scheduler showing the importance of each of them.
A: answer is
Q: Question 3: Complete a Simulation table for checkout counter using the Event Scheduling/ Time Advanc...
A: To advance the clock time, a simulation table is being used and with that, a new snapshot of systems...
Q: If the English Philosopher Thomas Hobbes could be called 'grandfather' of artificial intelligence, t...
A: if grandfather' of artificial intelligence :- Thomas Hobbes father of ai :- A.M. Turning real fa...
Q: Write a program to read the names stored in three different files: file1.txt, file2.txt and file3.tx...
A: Write a program to read the names stored in three different files: file1.txt, file2.txt and file3.tx...
Q: ide an approximate sol
A: In these way you can provide an approximate solution for Subset sum problem.
Q: q) Derive the complexity of Newton's divided difference.
A: Interpolation is used to estimate the value in a sequence of values. For example: (1,1), (2,2), (3,3...
Q: With the lessons today, were there changes in the Internet?
A: The answer is given below:-
Q: Discuss Big Data and how corporations are using it these days, as well as why they are doing so.
A: The answer of this question is as follows:
Q: Fully justify your choice of network devices with reference to their intended function and where the...
A: A LAN connects computers over a relatively short distance, allowing them to share data, files, and r...
Q: In an information system, "information" is: Data that has been subjected to a "value-added" proce...
A: answer is
Q: In Java Determine the output of the following: x = 3; while (x = 25) x = 4 * x
A: Java is one of the languages, which is considerably used in many sectors of Computer. In older time...
Q: Scooter to commute a certain distance (that is not known
A: Please check the step 2 for solution
Q: 10.4 (THE MYPOINT CLASS) Design a class named MyPoint to represent a p with x- and y-coordinates. Th...
A: I give the code in Java eclipse along with output and code screenshot
Q: s the message box that was triggered instantly appear before or after the applicati
A: CreateWindow functionThis function creates a pop-up or child window that is overlapped. It provides ...
Q: What feature allows EIGRP to perform unequal-cost load balancing across multiple paths?
A: Answer: The feature allows EIGRP to perform unequal-cost load balancing across multiple paths are as...
Q: Write Programm using oop in c++ Some form of simplified physics simulation, e.g. multiple interactio...
A: Solution: Given, Some form of simplified physics simulation, e.g. multiple interactions in an i...
Q: In this question don’t change code, just in python postgreSQL but solve the question and follow the ...
A: .!/usr/bin/env python from operator import itemgetter import sys currentword - None current_count - ...
Q: For the network below what is the length of the longest geodesic path closeness and betweenness cent...
A:
Q: How soon before or after the main window shuts does the message box that was triggered by WM CLOSE a...
A: Answer : Milliseconds
Q: What is data mining and how does it benefit you? What are some data mining tasks that you might writ...
A: Step 1) Data mining : Data mining refers to extracting knowledge from large amount of data The pro...
Q: How many comparsions would be needed for selection sort algorithm for these 3 types of arrays and al...
A: SELECTION SORT: The selection sort algorithm sorts an array by repeatedly choosing the smallest memb...
Q: What are six of the most common causes for computer mishaps today?
A: A computer is a powerful electronic machine that takes user input, processes it and produces output....
Q: The CreateConsoleScreenBuffer method should be described in detail.
A: The Answer is
Q: (The HyPoint class) Design a class named MyPoint to represent a point with x- and y-coordinates. The...
A: Answer
Q: Use loop instruction to implement the following in assembly program (using unsigned 32-bi int number...
A: Solution :- Step 1 code #include<stdio.h> int main(){ int number=10; int sum=0; int counter; f...
Q: PIC18F87J11 Do the following: a) Copy data 0xA to data memory location 0x400 b) Toggle the value in...
A: SUMMARY: - Hence, we discussed all the points.
Q: What are basic elements or c omponents of Linux?
A: Basic Components of the Linux Operating System are: Bootloader: Your computer must go through a star...
Q: Who or what is the Virtual Key Symbol for the Left Menu on the computer?
A: Virtual key: Virtual keys are keys that are not physically present on the keyboard but are mapping t...
Q: 1. (a) 1 A) Design an algorithm that inputs two lists of numbers, A, and B, of lengths n and m re...
A: Given The answer is given below.
Q: Design 4 networks each with 6 hosts for network 10.10.10.0 then write for each network:- 1-Network I...
A: The address 10.10.10.0 belongs to class A IP address where number of network bits is 8 and number of...
Q: Convert the following ER diagram into relational schema. Write the relational schema in SQL.
A: An entity relationship model (or ER model) describes interrelated things of interest in a specific d...
Q: What happens next once you click on the A thread:
A:
Q: You have two integers stored in variables var1 and var2. Make C # Program to determine if one of the...
A: Given: C# Program to determine if one of the integers is more than 10 but not both.
Q: Discuss the exact algorithm for Subset sum problem
A: Here is the detailed explanation of the algorithm.
Q: Identify and briefly discuss four reasons why computer incidents have become more prevalent. Use you...
A: A computer is an electronic device which takes data from user , processes it and produces output. Co...
Q: You will write a program that will calculate the area of a square based on a randomly generated inte...
A: I give the code along with output and code screenshot in Python
Q: Write a program to find the sum for the following series: اكتب برنامج لايجاد المتسلسله التاليه : (1*...
A: here in this question we have asked to write a program which compute the sum of some series
Q: What are some of the ways sequential files might cause issues for users?
A: Introduction: A Logical File Object is a logical file's object.
Q: What are the parts of a good project vision? Because they're important.
A: The project vision is an important starting point for the project, it should be very easy to explain...
Q: C++ Create a program that reads a simple arithmetic expression and evaluates it. More precisely, ...
A: Answer is given below:
determine if this arugment is valid or not using propoational logic/ premises/ a justify each step
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- Write a python code of this problem Problem Statement Assume that there are two teams and they are team attacker and team defender. Therefore, at a state of the game one agent in each team is left alive respectively. Here, the defender is given a lifeline called HP which will be assigned randomly. Furthermore, the attacker agent will try to give maximum negative HP to the defender agent to decrease his(d) chances of survival in the game. On the other hand, the defender agent will try to protect himself by receiving the lowest negative HP possible from the attacker agent. Furthermore, the attacker can have a choice from a number of bullets from his gun and the optimal moves will cost a certain maximum negative HP (chosen from randomly assigned values within the range of minimum and maximum negative HP). Here, are the following things you need to do using Alpha-Beta Pruning algorithm: Sample Input 1: Enter your student id: 17301106 Minimum and Maximum value for the…Three prisoners have been sentenced to long terms in prison, but due to over crowed conditions, one prisoner must be released. The warden devises a scheme to determine which prisoner is to be released. He tells the prisoners that he will blindfold them and then paint a red dot or blue dot on each forehead. After he paints the dots, he will remove the blindfolds, and a prisoner should raise his hand if he sees at least one red dot on the other two prisoners. The first prisoner to identify the color of the dot on his own forehead will be release. Of course, the prisoners agree to this. (What do they have to lose?) The warden blindfolds the prisoners, as promised, and then paints a red dot on the foreheads of all three prisoners. He removes the blindfolds and, since each prisoner sees a red dot (in fact two red dots), each prisoner raises his hand. Some time passes when one of the prisoners exclaims, "I know what color my dot is! It's red!" This prisoner is then released. Your problem…Correct answer will be upvoted else downvoted. In the event that the thing was a Pink Slip, the mission is finished, and you won't play additional races. In any case, In the event that a≤v, the likelihood of the thing drawn becomes 0 and the thing is as of now not a legitimate thing for every one of the further draws, decreasing x by 1. In addition, the decreased likelihood an is disseminated similarly among the other excess substantial things. In the event that a>v, the likelihood of the thing drawn diminishes by v and the decreased likelihood is conveyed similarly among the other substantial things. Input :The primary line of input contains a solitary integer t (1≤t≤10) — the number of experiments. The first and the main line of each experiment contains four genuine numbers c, m, p and v (0<c,m,p<1, c+m+p=1, 0.1≤v≤0.9). Also, it is ensured that every one of c, m, p and v have all things considered 4 decimal spots. Output :For each experiment, output a…
- John is training for a marathon and he can easily alternate between running a mile and walking a mile. If he runs for 2 miles in a row, he becomes fatigued, and must then walk for 2 miles in a row in order to no longer be fatigued. When he is fatigued, he can still alternate between running a mile and walking a mile, but if he runs 2 miles in a row while already fatigued, he will collapse on the side of the road. If he runs 3 miles in a row at any point, he will also collapse. Let the letter 'a' stand for John running 1 mile, and the letter 'b' stand for John walking 1 mile. Draw a DFA which accepts all possible runs in which John does not collapse on the side of the road.What is the difference between the decrease-and-conquer strategy and the divide-and-conquer strategy? Intuitively, which strategy is more efficient? Justify your answer.Simulated annealing is an extension of hill climbing, which uses randomness to avoid getting stuck in local maxima and plateaux. a) For what types of problems will hill climbing work better than simulated annealing? In other words, when is the random part of simulated annealing not necessary? b) For what types of problems will randomly guessing the state work just as well as simulated annealing? In other words, when is the hill-climbing part of simulated annealing not necessary? c) Reasoning from your answers to parts (a) and (b) above, for what types of problems is simulated annealing a useful technique? In other terms, what assumptions about the shape of the value function are implicit in the design of simulated annealing? d) As defined in your textbook, simulated annealing returns the current state when the end of the annealing schedule is reached and if the annealing schedule is slow enough. Given that we know the value (measure of goodness) of each state we visit,…
- With reference to the graph, let the roughness index R of a path to success be R = T +2E, where T is the time to get from L to W and E is the total number of enemies made. (a) Find the smoothest (least rough) path to success. (b) Find the smoothest path to success that includes edge ( f, i); this edge can be traversed in either direction.Consider the following scenario:A high school has 1000 students and 1000 lockers, one locker for each student. On the first day of school, the principal plays the following game: She asks the first student to open all the lockers. She then asks the second student to close all the even-numbered lockers. The third student is asked to check every third locker. If it is open, the student closes it; if it is closed, thestudent opens it. The fourth student is asked to check every fourth locker. If it is open, the student closes it; if it is closed, the student opens it. The remaining students continue this game. In general, the nth student checks every nth locker. If it is open, the student closes it; if it is closed, the student opens it. After all the students have taken turns, some of the lockers are open and some are closed. The program see in the photo, when ran, should ask the user to enter the number of lockers in the school. The program will output the number of lockers and the…In a prison, there is a door b/w any pair of adjacent cells and one exit guarded by a guard G. One prisoner is a maniac M which kills anybody he can see when he enters a cell. If M returns to the cell with his victim, then he loses consciousness and stops. In the evening all inmates and the guard went to sleep in their cells. In the morning, maniac M is gone and all other prisoners with the guard were found dead in their cells. Show the route of the maniac.
- In the new post-apocalyptic world, the world queen is desperately concernedabout the birth rate. Therefore, she decrees that all families should ensure that they have one girl orelse they face massive fines. If all families abide by this policy-that is, they have continue to havechildren until they have one girl, at which point they immediately stop-what will the gender ratioof the new generation be? (Assume that the odds of someone having a boy or a girl on any givenpregnancy is equal.) Solve this out logically and then write a computer simulation of it.Amanda, Javier, Joel and Pamela are on the edge of ariver, and they want to cross this river using a smallboat to the opposite shore. The boat can carryAt most two people on each lap. Amandacan cross the river only in 1 minute. Javier,Joel and Pamela take longer, 2, 5 and 10 minutes,respectively. If there are two people in the boat, theThe slowest person is the one who determines the time ofcrossing. The objective is for all four to be on the shoreopposite in the shortest possible time.- Identify at least two feasible plans to crossthe river. Remember that the boat is the only means oftransport, and that it cannot travel empty.- Define the criteria to evaluate the alternatives- What is the minimum time to pass the fourto the other end of the river?a. Given n items, where each item has a weight and a value, and a knapsack that can carry at most W You are expected to fill in the knapsack with a subset of items in order to maximize the total value without exceeding the weight limit. For instance, if n = 6 and items = {(A, 10, 40), (B, 50, 30), (C, 40, 80), (D, 20, 60), (E, 40, 10), (F, 10, 60)} where each entry is represented as (itemIdi, weighti, valuei). Use greedy algorithm to solve the fractional knapsack problem. b. Given an array of n numbers, write a java or python program to find the k largest numbers using a comparison-based algorithm. We are not interested in the relative order of the k numbers and assuming that (i) k is a small constant (e.g., k = 5) independent of n, and (ii) k is a constant fraction of n (e.g., k = n/4). Provide the Big-Oh characterization of your algorithm.

