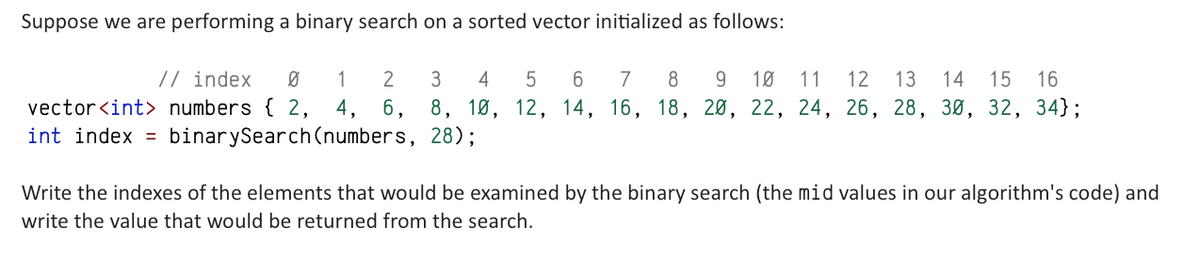
Suppose we are performing a binary search on a sorted vector initialized as follows: // index Ø vector numbers { 2, int index = binarySearch (numbers, 28); 1 5 6 7 8 9 10 11 12 13 14 15 16 2 3 4 4, 6, 8, 10, 12, 14, 16, 18, 20, 22, 24, 26, 28, 30, 32, 34); Write the indexes of the elements that would be examined by the binary search (the mid values in our algorithm's code) and write the value that would be returned from the search.
Q: Is there a specific purpose for wireless networks in third world countries? This shift away from…
A: - We need to talk about wireless networks in third world countries.
Q: Should the large software be divided into smaller modules, with each module responsible for a…
A: We will comprehend how functions work in C++ and how and why they are employed. This is accurate, so…
Q: Make use of a database transaction to record work done on a project. The positive aspects of the…
A: Introduction: Any coherent logical calculation is referred to as a database transaction. An example…
Q: You'll get a solid grounding in topics including cloud computing, social media blogging, and more…
A: Given: Improve your knowledge of social networking blogs, cloud computing, and any other topics that…
Q: Specifically, how does Oracle's database differ from relational databases?
A: Databases with relations: The mathematical set theory behind the relational model forms the basis of…
Q: Python's range() function does not include the cutoff value. Combine the range() function with a…
A: Tip \explanation When dealing with Python code, range() is crucial for looping. Python's range()…
Q: What is the three-character identifier for button labels?
A: The three character ID used to name the buttons in Visual Basic is btn. It allows the user to modify…
Q: DIRECTION (4-5): One card is drawn from a well-shuffled deck of 52 cards. Find the probability of…
A: '8' of diamond: (C) 1/13 Red ace: (B) 2/26
Q: Why is it crucial to have a systems analyst on board throughout the building of a system?
A: A systems analyst plays a crucial role in the building of a system as they are responsible for…
Q: uestion
A: The answer is
Q: When will Deadlock Prevention work, and what requirements does it have?
A: An operating system is a programme that runs application programmes and acts as a communication…
Q: How simple or complicated is it to add or delete users in Windows 10 and Linux?
A: In accordance with the inquiry, we must determine the difficulties associated with adding and…
Q: To build a computer, what do you think are the four most crucial parts of logic?
A: Name four essential computer logic design requirements. The solution is next. logic design, A…
Q: The inner workings of an OS are beyond our ken.
A: A software programme known as an operating system serves as an administrator for other application…
Q: How to do the tree method
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: What measures must be taken to ensure the security of network "building blocks" such switches,…
A: Introduction:- A computer network is a system that connects two or more computers together for the…
Q: Let's now split our input data X and labels y into a train and test set using the train_test_split()…
A: Code: from sklearn.model_selection import train_test_split X_train, X_test, y_train, y_test =…
Q: Content, accessibility, logical structure, and physical organization are all factors that should be…
A: Database A database is an assortment of effectively accessible information. Data, like deals…
Q: Do gaps exist in software engineering theory? Explain?
A: Reversible Software Development: Any software engineering ideas missing? Explain? Database…
Q: Which four advantages of continuous event simulation are considered to be the most significant?
A: Introduction: Continuous event simulation is a modeling technique that is used to simulate the…
Q: Is UDP just as shaky as IP, or is this not the case at all? I'm curious as to why you think this is…
A: Answer is
Q: List and discuss the pros and cons of the various online communication methods, keeping in mind how…
A: Globalization and the rise of business collaboration worldwide mean that online communication is no…
Q: Write HTML code to create following table. Also set its border color to “red”
A: For creating the required table with merged cells, we will be employing the concept of rowspan and…
Q: Learn to differentiate between network services and apps hosted in the cloud and those hosted…
A: Definition: The on-demand availability of computer system resources, particularly data storage and…
Q: What makes the usage of foreign keys in a database so important for guaranteeing its continued…
A: Foreign key: A relational database foreign key links data from two relations. It links two…
Q: List the many types of electronic computers that exist.
A: There are several types of electronic computers, including: Personal computers (PCs) - These are…
Q: Q2 You have a dynamic array with 3 elements in it and a capacity of 4. The capacity doubles when…
A: In this question, it is asked to calculate the capacity of the dynamic array after the sequence of…
Q: Don't discount the value of wireless networks in today's developing nations. Wireless technology has…
A: Introduction: A WLAN creates a wireless network (LAN) between two or more devices in a small space,…
Q: #include #include using namespace std; void PrintVectors(vector numsList) { unsigned int i;…
A: In this question, it is asked to edit the code statements to pass all the test cases. One of the…
Q: Participating in this course will help you get a deeper understanding of blogs, social media, and…
A: According to the information given. We have to define the deeper understanding of blogs, social…
Q: The Problem: Strange things are happening to one of your classes. Data is getting corrupted somehow.…
A: Given: Strange things are happening to one of your classes and data is getting corrupted. Task:…
Q: Is service-oriented architecture inappropriate for these applications, and if so, why? Give…
A: Introduction : A collection of guidelines and techniques known as service-oriented architecture…
Q: Project 14: Class scores Write a program that calculates the total grade for N classroom exercises…
A: According to the information given:- We have to follow the instruction in order to get desired…
Q: "Free" Yes No Spam Class ents) NoSpam onsider above contingency table listing counts d NoSpam email…
A: A contingency table, also known as a cross-tabulation or cross-tab, is a type of table in statistics…
Q: can u show the graph with all the fuctions lines r showing ?
A: In this question we will plot all the function visible in the graph using python Let's code.
Q: Kindly elaborate on the benefits of constructed languages and how they differ from interpreted ones.…
A: There is a difference between multiprogramming and multithreading, as will be discussed in this…
Q: Where do input and output streams diverge? To what extent does using the fstream.h file affect one's…
A: The stream that feeds the programme with data is referred to as the "input stream," and it is…
Q: Learn what cloud computing and social media blogs have to offer.
A: Learn as much as you can about social networking blogs and cloud computing? Internet social…
Q: Wireless networks are becoming more important in today's developing countries, especially in Africa.…
A: 1. A computer network refers to interconnected computing devices that can exchange data and share…
Q: Is there a real need for academics to investigate software engineering questions?
A: The following list of 15 of the highest-paying software jobs includes information on tasks, salary…
Q: After working on it some more this is what I am getting now.
A: Expected file contents are sorted in decreasing order whereas your file contents are in ascending…
Q: Is it true that it's always less expensive to prevent a problem than it is to fix it after it's…
A: According to the information given:- We have to define the mentioned statement is true or not.
Q: It's possible to get data from social media platforms.
A: Introduction Websites and apps that allow users to produce and share information or engage in social…
Q: Just what does "taking into account" imply in this context? Incorporating ideas from the field of…
A: What's critical concern? Consideration may be anything. Consider past, present, or future factors.…
Q: Part 1 You will implement the following three methods to find the GCD of two numbers. You may not…
A: Introduction Euclid GCD: Euclid's GCD (Greatest Common Divisor) is an algorithm used to determine…
Q: If you were asked to define the term "network security," what would you say? You can explain the…
A: Network security involves a vast array of strategies, tools, and processes. Software- and…
Q: int factorial (int n) { /* Calculate a factorial using loop. * A factorial of a number is the…
A:
Q: If you are bored then Play games else Do nothing endif MAKE A FLOWCHART FROM THE PESUDOCODE,…
A: A flowchart is a diagram that depicts the process or a computer program. It shows the flow or order…
Q: = 0(n²³) n(n+1)/2 c. n(n+1)/2 = (n³) b. n(n+1)/2 = O(n²) d. n(n+1)/2 = $2(n)
A: Time complexity measures how efficient an algorithm is in terms of time and space. It is usually…
Q: What are the three most important components of a network that ensure it runs smoothly and…
A: Start: Performance, dependability, and security are the three most significant criteria for network…
please find: indexes examined and value returned
Here is your solution -
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Suppose we are performing a binary search on a sorted vector initialized as follows: // index 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 vector<int>numbers {-5, -1, 0, 3, 9, 14, 19, 24, 33, 41, 56, 62, 70, 88, 99}; int index=binarySearch(numbers, 18); Write the indexes of the elements that would be examined by the binary search (the mid values in our algorithm's code) and write the value that would be returned from the search. please find : indexes examined and value returnedSuppose we are performing a binary search on a sorted vector initialized as follows: // index 0 1 2 3 4 5 6 7 8 9 10 11 12 13vector<int>numbers {-23, -5, 9, 14, 15, 18, 23, 24, 25, 29, 34, 62, 85, 87};intindex=binarySearch(numbers, 25); Write the indexes of the elements that would be examined by the binary search (the mid values in our algorithm's code) and write the value that would be returned from the search. Now suppose we are performing both an iterative (loop-based) sequential search and then a recursive binary search on the same list. The sequential search is a standard version that does not take any advantage of the sortedness of the list, simply looking each element in order from the start to the end of the list. Suppose we are searching the list for the value 25. Also suppose that we are operating on a special computer where reading an element's value in the list (such as examining the value of numbers[0]) costs 7 units of time; calling any…Suppose we are performing a binary search on a sorted vector initialized as follows: // index 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16 vector<int> numbers{ 2, 4, 6, 8, 10, 12, 14, 16, 18, 20, 22, 24, 26, 28, 30, 32, 34}; int index = binarySearch(numbers, 28); Write the indexes of the elements that would be examined by the binary search (the mid values in our algorithm's code) and write the value that would be returned from the search. NOTE: When writing the indexes (mid values), separate them by comma followed by spaced. Example: 7, 3, 5 find: indexes examined value returned
- Write the state of the elements of the vector below after each of the first 4 passes of the outermost loop of the insertion sort algorithm. (After the first pass, 2 elements should be sorted. After the second pass, 3 elements should be sorted. And so on.) // index 0 1 2 3 4 5 6 7 vector<int> numbers{29, 17, 3, 94, 46, 8, -4, 12}; insertionSort(numbers); NOTE: Write your answer inside curly braces with numbers separated by commas {29, 17, 3, 94, 46, 8, -4, 12} after pass 1 after pass 2 after pass 3 after pass 4please convert the code to C language //C++ program to check if two arrays //are equal or not #include <bits/stdc++.h>using namespace std; bool similar_array(vector<int> arr1, vector<int> arr2){ //create teo different hash table where for each key //the hash function is h(arr[i])=arr[i] //we will use stl map as hash table and //will keep frequency stored //so say two keys arr[0] and arr[5] are mapping to //the same location, then the location will have value 2 //instead of the keys itself //if two hash tables are exactly same then //we can say that our arrays are similar map<int, int> hash1; map<int, int> hash2; //for each number for (int i = 0, j = 0; i < arr1.size(); i++, j++) { hash1[arr1[i]]++; hash2[arr2[i]]++; } //now check whether hash tables are exactly same or not for (auto it = hash1.begin(), ij = hash2.begin(); it != hash1.end() && ij != hash2.end(); it++, ij++) {…please convert the code to C language // C++ program to find maximum distance between // two occurrences of same element in array#include <bits/stdc++.h>using namespace std; int maximum_distance_bw_occurences(vector<int> arr, int n){ //create a hash table where for each key the //hash function is h(arr[i])=arr[i] //we will use stl map as hash table and //will keep i stored(i of arr[i]) //so say two keys arr[0] and arr[5] are mapping //to the same location, then the location will have value 0,5 //instead of the keys itself map<int, vector<int> > hash; //for each number for (int i = 0; i < arr.size(); i++) { hash[arr[i]].push_back(i); } //now to find max distance b/w two occurrences //we need to check difference b/w first and //last position for each unique keys //maxdiff=max(last-first) for each unique key int maxdiff = 0; for (auto it = hash.begin(); it != hash.end(); it++) { int first…
- Create a merge-sort multithread.A is an array, and p and q are array indexes used to sort the sub-array A[p..r]. B is a subarray that will be filled by the sort. A p-merge-sort(A,p,r,B,s) call sorts items from A[p..r] and places them in B[s..s+r-p].import java.util.Scanner;import java.util.ArrayList; public class UserIDSorting {// TODO: Write the partitioning algorithm - pick the middle element as the // pivot, compare the values using two index variables l and h (low and high), // initialized to the left and right sides of the current elements being sorted,// and determine if a swap is necessarypublic static int partition(ArrayList<String> userIDs, int i, int k) {} // TODO: Write the quicksort algorithm that recursively sorts the low and // high partitionspublic static void quicksort(ArrayList<String> userIDs, int i, int k) {} public static void main(String[] args) {Scanner scnr = new Scanner(System.in); ArrayList<String> userIDList = new ArrayList<String>(); String userID; userID = scnr.next();while (!userID.equals("-1")) {userIDList.add(userID);userID = scnr.next();}// Initial call to quicksort quicksort(userIDList, 0, userIDList.size() - 1); for (int i = 0; i < userIDList.size(); ++i)…Write a recursive function named binarySearch that accepts a reference to a sorted vector of integers and an integer target value and uses a recursive binary search algorithm to find and return an index at which that target value is found in the vector. If the target value is not found in the vector, return -1. The following code shows some example calls and their expected return values: // index 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16vector<int>v {-4, 2, 7, 10, 15, 20, 22, 25, 30, 36, 42, 50, 56, 68, 85, 92, 103};intindex=binarySearch(v, 42); // 10intindex=binarySearch(v, 66); // -1 You should assume that the vector's elements are already sorted; you do not need to handle the case of an unsorted vector. Your function must be recursive and must use a binary search algorithm. Do not use loops or auxiliary data structures.
- Write a program that implements a sorted list using dynamic allocated arrays. DataFile.txt contains the information of poker cards. C: clubs(lowest),D: diamonds, H: hearts, S:spades(highest) 2 (lowest), 3, 4, 5, 6, 7, 8, 9, 10, J, Q, K, A No Joker cards Any C cards are lower than any D cards. DataFile Content(You can write the file specification into your program.): H4,C8,HJ,C9,D10,D5,DK,D2,S7,DJ,H3,H6,S10,HK,DQ,C2,CJ,C4,CQ,D8,C3,SA,S2,HQ,S8,C6,D9,S3,SQ ,C5,S4,H5,SJ,D3,H8,CK,S6,D7,S9,H2,CA,C7,H7,DA,D4,H9,D6,HA,H10,S5,C10 H4, D5, HK, D2 H4, HK, SK C9,C10 For examples, DJ means J of Diamonds;H7 means 7 of hearts. Your job Create a list by dynamic allocated array and set the size to 20 Read the first 20 cards in the first line of the file, the put them one by one into the list by implementing and using putItem(). The list must be kept sorted in ascending order. Then print out all the cards in the list in one line separating by commas. Then delete the cards indicated in the second…Which of the following is true about searching elements in an ordered array? You cannot use binary search on an ordered array so the performance is O(n) If there are no holes in the array and the elements are all next to each other, then the performance for search improves to O(1) If you do a linear search on a sorted array, the performance improves to O(log n) Which of the following is true about the insertBeforeCurrent function for a Circular Linked List (CLL) like you did in programming exercise 1? If the CLL is empty, you need to create the new node, set it to current, and have its next pointer refer to itself The worst case performance of the function is O(n) If you insert a new element with the same data value as the current node, the performance improves to O(log n)this function c++ accept vector , replace this vector to array void merge_sort_4(vector<int> lst,int start,int end){if (start < end){int quarter1 = (start + end) / 4;int quarter2 = (start + end) / 2;int quarter3 = (end - quarter1 - 1); merge_sort_4(lst, start, quarter1);merge_sort_4(lst, quarter1 + 1, quarter2);merge_sort_4(lst, quarter2 + 1, quarter3);merge_sort_4(lst, quarter3 + 1, end); merge4(lst, start, quarter1, quarter2, quarter3, end);}}void merge4(vector<int> lst,int start,int q1,int q2,int q3,int end){vector<int> first_q_list;for(int i=start;i<q1+1;i++)first_q_list.push_back(lst[i]);vector<int> sec_q_list;for(int i=q1+1;i<q2+1;i++)sec_q_list.push_back(lst[i]);vector<int> third_q_list;for(int i=q2+1;i<q3+1;i++)third_q_list.push_back(lst[i]);vector<int> last_q_list;for(int i=q1+1;i<end+1;i++)last_q_list.push_back(lst[i]);int…











