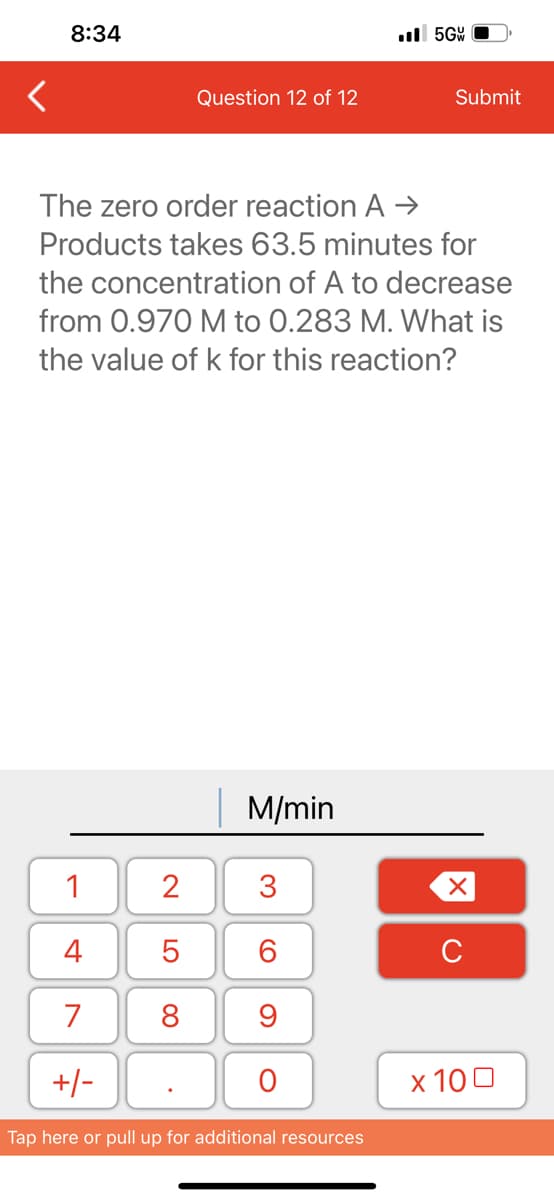
The zero order reaction A → Products takes 63.5 minutes for the concentration of A to decrease from 0.970 M to 0.283 M. What is the value of k for this reaction?
Q: Step 5 (c) Find the function value q(-x), if possible. Replace the variable t with -x in the…
A: The solution is given below for the above-given question:
Q: Provide an example of a situation when employing a command-line interface would be preferable over a…
A: Let's first examine what the CLI and GUI are. Through the graphical icons of the Graphic User…
Q: What would be the output of the following code be? import requests url = 'https://httpbin.org/' try:…
A: 1. Programming is the process of creating a set of instructions that tells a computer how to perform…
Q: When exchanging data between a browser and a server, which protocol, like SSL or TLS, provides the…
A: Internet Security Protocols: Internet Security Protocols are a set of protocols, standards, and…
Q: Saudi National CyberSecurity Authority Essintial CyberSecurity Controls (NCA ECC) in 5-1-2 control…
A: Introduction Protecting networks, systems, and software from online dangers is the discipline of…
Q: What are some of the most common objections to implementing IoT?
A: In this question we have to understand most common objections for implementing the Internet of…
Q: When it comes to software engineering, what exactly is the point and purpose of prototyping?
A: Introduction: In this section, we must explain the objectives of software engineering prototyping.…
Q: dex is a new an up and coming software development company. They recently started offering…
A: I have written the code below in JAVA as mentioned in the question:
Q: Create a Java program to output information for two payees including the following information about…
A: Introduction Classes in Java are the basic building blocks of code and are used to define objects…
Q: When creating a new system, why would you want to use the concept of prototyping?
A: Solution: System Analysts are entirely responsible for creating a model that can commit to the end…
Q: We propose adding a new tier to Flynn's taxonomy. What are the characteristics that set apart more…
A: Introduction: Parallel computing allows activities to be executed in parallel when they are divided…
Q: /etc/passwd specifies the default interactive shell as /sbin/nologin for accounts that cannot be…
A: We need to give the unix command for the given scenario.
Q: Where should you start looking for governance problems if you're moving your IT infrastructure to…
A: Due to that What are some of the governance issues to be on the lookout for while switching from…
Q: What characteristics are typical of network diagrams?
A: Components of a Network Diagram A network diagram is a graphical depiction of the mapping of a…
Q: When discussing the JVM, we mentioned that only one method may be in use by a given thread at any…
A: INTRODUCTION: The Java Virtual Machine (JVM) is an engine that provides the runtime environment…
Q: C# i need to Write a program named SortWords that includes a method named SortAndDisplayWords that…
A: CODE in C#: using System;using static System.Console;public class SortWords{ public static void…
Q: When moving from on-premises servers to an IaaS-based design, what are some of the governance…
A: Introduction A type of cloud-based computing actually named infrastructure as a service (IaaS)…
Q: Give both the benefits and drawbacks of using magnetic secondary storage systems as opposed to…
A: The answer is given in the below step
Q: The size of the intersection divided by the size of the union is used to determine how similar two…
A: The code for the above-given question is given below:
Q: A software development lifecycle is made up of several moving pieces. In what stage of the system's…
A: Software development lifecycle (SDLC) is a process which is used by the software to design, develop…
Q: distinctions between parallel and serial code development.
A: Introduction : Parallel code development is the process of writing code that takes advantage of…
Q: 1. Company X is conducting a survey on their redesigned spinning drives. They need to compare the…
A: 1a. The average booting time using spinning drive is 37.5 seconds. b. The histogram for booting…
Q: Which views need to be taken into account and how can this be done when designing models for…
A: An application is divided into three fundamental logical parts using the Model-View-Controller (MVC)…
Q: There are several things to think about while putting up a software development team. How do you…
A: Introduction Software development is the method of designing, coding, testing, & maintaining…
Q: What exactly is the relevance of design patterns, and how do they work in the context of software…
A: A design pattern in software engineering is a general, repeatable solution to a common software…
Q: 1___Codex Registration System Codex is a new an up and coming software development company. They…
A: The JAVA code is given below with output screenshot
Q: When moving data from locally housed servers to a cloud-based data center, what potential governance…
A: Answer: The infrastructure of the charity information is maintained by the charity administration…
Q: Explain why the maintenance procedures for the interactive model vary from those of the waterfall…
A: The differences between the waterfall model and the interactive model are described below: The…
Q: Let's pretend Host C is running a Web server on port 80. Suppose this Web server allows both Hosts A…
A: Enduring relationship Each persistent connection receives its own connection socket from the web…
Q: Take a look at the three IPv6 transition strategies.
A: Your answer is given below.
Q: Case Project 4-2: Testing DNS Security Time Required: 30 minutes Objective: Create a report…
A: Introduction The Alexander Rocco Corporation employs many IT staff members to manage the company's…
Q: What are the primary distinctions between a system architecture that uses fat clients and one that…
A: Introduction: While all other layers are built on the server, the presentation layer is introduced…
Q: In order to improve speed, your organization has decided to spread its product database over many…
A: The solution to the given question is: Some of the issues that must be overcome when the product…
Q: Recognize the many categories of books that may be found in the stock at the moment. There should be…
A: By using the DISTINCT clause, it is possible to filter out duplicate entries from the result set.…
Q: Can a company's IT problems really be solved by moving to the cloud?
A: Some of a company's IT issues may be resolved by moving to the cloud, but this is not a guarantee…
Q: Write down two external and two internal factors that are interfering with your ability to hear…
A: Introduction Interfering: Interfering refers to something that hinders, obstructs, or impedes…
Q: In each question below, provide a brief explanation, a formula and the numerical value for your…
A: The entropy of a password is given by the formula: entropy = log2(number of possibilities). To find…
Q: Setting up solid security policies and consistently applying them is widely acknowledged to be…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: In what ways do the SPEC CPU benchmarks improve upon the shortcomings of the Whetstone, Dhrystone,…
A: SPEC CPU benchmark addresses deficiencies of Dhrystone benchmark, Whetstone benchmark, and LINPAC…
Q: It's common for character devices to transfer data more quickly than block devices. Is that…
A: Both block devices and character devices are included here. The normal processing speed of block…
Q: Both abstract classes and interfaces may be used to specify the expected behavior of an object. What…
A: INTRODUCTION: Abstract class : It is a class that has been declared to be abstract, and it may or…
Q: Implicate heap-dynamic variables: when to use them, how to use them, and why they're useful.
A: 1. Dynamic heap variables, also known as dynamically allocated variables, are a way of allocating…
Q: ROM is preprogrammed before the machine is even built.
A: Correct! Read-Only Memory (ROM) is a type of non-volatile memory that stores permanent data, which…
Q: When a person listens to another person and really takes in what they are saying, this is called…
A: Introduction: The most fundamental aspect of effective communication is listening. The act of…
Q: The total cost of a group of items at a grocery store is based on the sum of the individual…
A: Here is the code for NecessaryProduct and LuxuryProduct classes: CODE in JAVA: public class…
Q: What precisely is the point of having the LDAP standard in the first place if it can easily be put…
A: • The entries are saved in the LDAP directories together with other items that are comparable to…
Q: ata cable between two office labs that are 80 meters apart. What is two advantages of using a copper…
A: Twisted pair cable One type of wiring is twisted pair wire, which consists of two conductors from a…
Q: To what extent did these considerations influence the decision to require system developers to use…
A: The object-oriented approach is a programming paradigm based on the concept of "objects". An object…
Q: The image files used by image buttons in the Android Studio IDE can be located anywhere in the…
A: Introduction Since any directory within the Android directory may be accessed by the picture button…
Q: When is the best time to upgrade the network?
A: Introduction : A network is a system of connected computers, devices, and other components that can…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- To get this o/p (10, 9, 8, 7, 6, 5, 4, 3, countdown aborted!) must correct -------error in the following code *Create the Kmaps and then simplify for the following functions (leave in sum-of-products form): a) F(w,x,y,z) = w'x'y'z' + w'x'yz' + w'xy'z + w'xyz + w'xyz' + wx'y'z' + wx'yz' b) F(w,x,y,z) = w'x'y'z + w'x'yz' + w'xy'z + w'xyz + w'xyz' + wxy'z + wxyz + wx'y'z∑ = {C,A,G,T}, L = { w : w = CAjGnTmC, m = j + n }. For example, CAGTTC ∈ L; CTAGTC ∉ L because the symbols are not in the order specified by the characteristic function; CAGTT ∉ L because it does not end with C; and CAGGTTC ∉ L because the number of T's do not equal the number of A's plus the number of G's. Prove that L ∉ RLs using the RL pumping theorem.
- A. 3-SAT to Hamiltonian CycleReduce 3-CNF Satisfiability problem to an instance of Hamiltonian Cycle problem in polynomial time.Note: Variables in red color are negated.1. Given: Variables: X1, X2, X3 Clause: (X1 v ¬X2 v X3) Ʌ (¬X1 v ¬X2 v ¬X3)2. Given: Variables: X1, X2, X3 Clause: (X1 ∨ X2 ∨ X3) ∧ (¬X1 ∨ ¬X2 ∨ ¬X3) ∧ (¬X1 ∨ X2 ∨ ¬X3)For the following Peterson’s solution from your textbook, for the enter_region called by process ‘0’ and process ‘1’, show all possible combinations, interleaving of the execution paths, focusing on testing the ‘while-loop’. Will there be any violation of mutual execution? Explain showing all possible casesPlease explain all steps: What Boolean equation is represented by the following K-Maps: a) ~y~z ~yz yz y~z ~x 1 1 1 x 1 1 1 1 b) ~y~z ~yz yz y~z ~w~x 1 1 ~wx 1 1 wx 1 w~x 1 1 c) ~y~z ~yz yz y~z ~w~x 1 1 1 1 ~wx 1 1 wx 1 1 1 1 w~x 1 1 d) ~y~z ~yz yz y~z ~w~x 1 1 ~wx 1 1 1 wx 1 1 w~x 1 1 1
- Consider the following code for a process P0 (assume turn has been initialized to zero): --- Etc. --- while (turn != 0) {} Critical Section /* … */ turn = 0; --- Etc. --- For process P1, the code is: --- Etc. --- while (turn != 1) {} Critical Section /* … */ turn = 1; --- Etc. --- Does the above code meet all the required conditions for a correct mutual-exclusion solution? Explain and justify your answer.Consider two cooperating processes P5 and P6. Suppose that, at any time, P6 want toenter its critical section. Write an algorithm using Peterson’s solution which shows thatP6 can finally enter into its criticalsection. Consider the turn value for P5 to be 10 andP6 to be 12.1.Code so on for_A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum.. ..
- A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum..Consider the classical synchronization problem of dining philosophers in which, n philosophers sit at a round table with one chop stick between each philosopher (chop stick on the right hand belong to each philosopher). Philosophers do one work at a time i.e. either are thinking or eating. To eat, they need to have two chop sticks such that the chopsticks to their left and their right. a. Provide an algorithm using Test-and-Set logic (disabling interrupts) to solves the diningphilosopher problem. b. Show the steps of the solution validatingi) Mutual exclusion, ii) Progress, iii) Must be viable for any number of philosophers and ensure that none of them starves to death.Code so on for_A pure full Implement c/c++ to evaluate round robin algorithm. You must use the job list given here: Job (1) arrive at CPU cycle1 Job (2) arrive at CPU cycle2 Job (3) arrive at CPU cycle36 I/O (32) CPU (54) I/O (45) CPU (20) I/O (40) CPU (48) CPU (39) CPU (48) I/O (55) Your job list must contain CPU bust and I/O bust as above. Quantum time = [5, 10, 15, 20, 25, 30, 35, 40, 45, 50, 55, 60] The evaluation of the most suitable quantum time needs to consider the followingperformance metrics, but not limited to:(i) Turnaround time of the jobs;(ii) Waiting time of the jobs; and(iii) Number of interrupts incurred The code must able to read csv file format of the job list as input file. The code must able for user to input time quantum.. .

