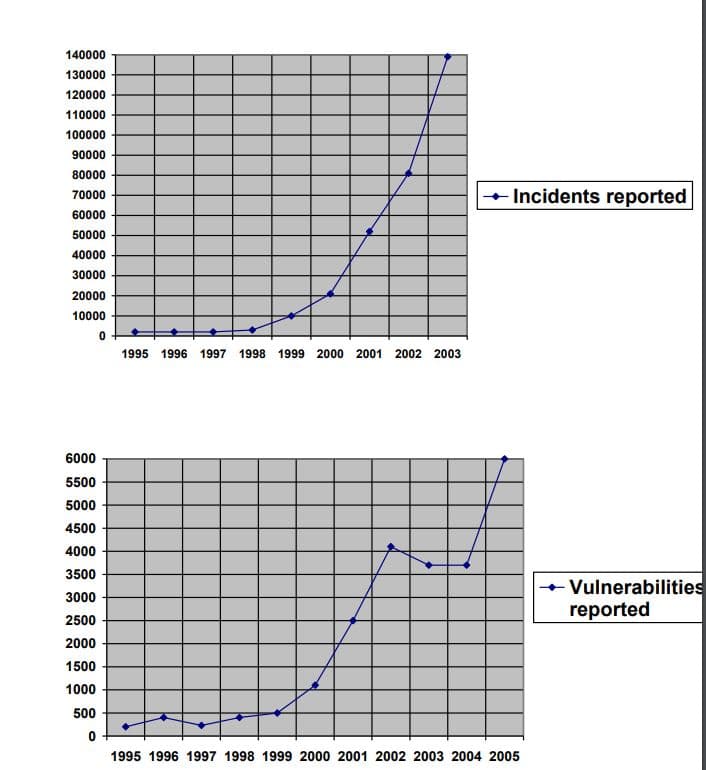
There are two graphs presented from the CERT on reported incidents and vulnerabilities. Keep in mind the difference between an incident and vulnerability. While these charts are dated they still provide valuable trend information that continues to rise. Today, both security incidents and security vulnerabilities continue to rise for a variety of reasons. What reasons can you provide for the continuing upwards trend in the number of incidents reported? You should provide at least four (4) reasons with supporting data and reasoned arguments to support your answer. Good answers will provide facts, reasoned arguments and references that go beyond anecdotal information. Explain using facts, reasoned arguments and references that go beyond anecdotal information and link to sources. PLEASE ADD YOUR SOURCES! Please have clear writing as well! Thank you!
There are two graphs presented from the CERT on reported incidents and vulnerabilities. Keep in mind the difference between an incident and vulnerability. While these charts are dated they still provide valuable trend information that continues to rise. Today, both security incidents and security vulnerabilities continue to rise for a variety of reasons.
What reasons can you provide for the continuing upwards trend in the number of incidents reported? You should provide at least four (4) reasons with supporting data and reasoned arguments to support your answer. Good answers will provide facts, reasoned arguments and references that go beyond anecdotal information.
Explain using facts, reasoned arguments and references that go beyond anecdotal information and link to sources. PLEASE ADD YOUR SOURCES! Please have clear writing as well! Thank you!
Step by step
Solved in 2 steps




