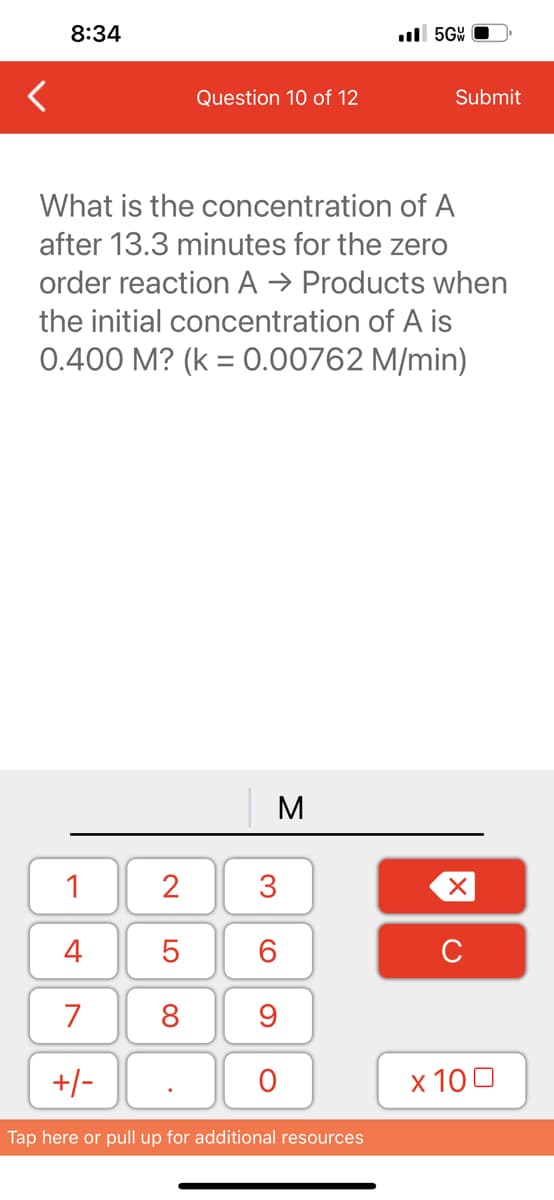
What is the concentration of A after 13.3 minutes for the zero order reaction A → Products when the initial concentration of A is 0.400 M? (k = 0.00762 M/min)
Q: > Find X the maximum from the following data: y - 2 2 -0.25 and minimum value of 1 -0.25 22 2 2 3…
A: Algorithm for the program uses Newton's forward difference method to find the maximum and minimum…
Q: List and explain eight of the most foundational principles of computer architecture.
A: Computer architecture's Eight Great Ideas Moore's law design Abstraction simplifies design. Fasten…
Q: When compared to other disc scheduling algorithms, how dangerous is the SSTF one?
A: Introduction Disk Scheduling Algorithms: Disk Scheduling Algorithms are algorithms used by the…
Q: In cell A11, increase the indent of the cell contents twice.
A: Given Excel contains, One column and 11 rows. The values are present from row 6 to 11. Row 6…
Q: cases would you defend the use of assembly language
A: Introduction: Assembly Language: Assembly language was created to alleviate some of the issues with…
Q: s in the laye
A: Introduction: The ICMP protocol works at the network level. ICMP messages furnish data about issues…
Q: Use Dr Racket please
A: Answer in next step
Q: in C# i need to Write a program named InputMethodDemo2 that eliminates the repetitive code in the…
A: In this question we have to write a C# program for the InputMethodDemo2 method that eliminates the…
Q: The hospital would like to set up a relational database corresponding to this form. a. Normalize the…
A: Normalization Normalization is the term used to describe the process of organizing the data in the…
Q: What perspectives have to be taken into consideration when designing models for software-intensive…
A: There are numerous types of software-intensive systems, ranging from business systems to IoTs and…
Q: Create a Java program to output information for two payees including the following information about…
A: Introduction Classes in Java are the basic building blocks of code and are used to define objects…
Q: Why should I invest in software that automates server software installation and configuration? Can…
A: What are the benefits of providing and configuring servers automatically? What are the downsides of…
Q: MUST BE DONE IN C#!!! Create a class called StudentGrades. This class should be designed based off…
A: Algorithm: 1. Create a StudentGrades class with a List of double grades_list as a property, and…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: Alphabet: A = 0, B = 1,…
A:
Q: How many parity bits may be found in a message at most?
A: Introduction: A parity bit is a type of error-detecting code used in communication systems. It is a…
Q: Please give a bulleted list detailing the steps taken by the computer during startup.
A: Introduction When a computer is turned on, its operating system is sent off during the booting…
Q: When moving data from locally housed servers to a cloud-based data center, what potential governance…
A: Answer: The infrastructure of the charity information is maintained by the charity administration…
Q: If you see a mistake in the following situation, please mark it. The sender includes the number…
A: Odd Parity : It means that if the number of one's present in data transmission is odd then Parity…
Q: How can we make sure that our LAN is always up and running smoothly?
A: Introduction LAN (Local Area Network) is a type of computer network that connects computers and…
Q: What are the four most important tasks that a computer system must perform? For clarification,…
A: Any computer system will have four primary roles that allow it to be recognized.
Q: Which encrypted tunneling protocol could be able to circumvent firewalls that are created…
A: Tunneling Tunneling is in many cases utilized in virtual private networks. It can likewise set up…
Q: an analytical solution for this In this question, please write out the first 10 terms (from 0 to 9)…
A: The sequence hn can be found by analyzing the function f. For n = 0, h0 = 1, as the function prints…
Q: Ms 123993 code Resources.
A: Here from question As JAVA/ Python is mentioned in the question I am solving with java Java method:…
Q: This is a result of the incredible powers that modern computers are gifted with, which is a…
A: Introduction: We must emphasize the significance of computer use in our educational system and the…
Q: What are the primary distinctions between a system architecture that uses fat clients and one that…
A: Introduction: While all other layers are built on the server, the presentation layer is introduced…
Q: What are some of the primary factors that have contributed to the rise in importance of…
A: Introduction Object-Oriented Systems: OOP stands for ( Object-Oriented Programming ). It is a…
Q: For this project, your task is to mark up a letter that needs to be hosted on a university intranet.…
A: Algorithm: Start by creating the document structure with the appropriate doctype declaration and…
Q: Do we need a router if there is only one possible connection between the origin and destination…
A: The term "router" refers to a piece of hardware or a software application that can receive, process,…
Q: How should one go about compiling information for a thorough how-to guide? If you run a sequential…
A: In this question, it is asked what is the method for compiling information for a thorough how-to…
Q: So, what are the advantages of Azure Domain? In addition to Microsoft, several other firms provide…
A: Introduction: Azure Domain is a cloud-based service provided by Microsoft that offers domain name…
Q: When building models for software-intensive systems, what perspectives have to be taken into…
A: Systems that rely heavily on software for their conception, creation, deployment, and evolution are…
Q: In the process of designing models for software-intensive systems, which views need to be taken into…
A: In software design, various views or perspectives need to be considered to have a comprehensive…
Q: What are the primary distinctions between a system architecture that uses fat clients and one that…
A: Fat client: Fat client is a networked computer with many locally-stored programs or resources and…
Q: How does computer science differ from other academic fields, and what does it include exactly? What…
A: Introduction: The study of computer hardware and software is known as computer science. It covers…
Q: In each question below, provide a brief explanation, a formula and the numerical value for your…
A: The entropy of a password is given by the formula: entropy = log2(number of possibilities). To find…
Q: Best Cryptocurrencies for Beginners in 2023 and explain thoroughly why.
A: Introduction:- Financial technology is the use of technology in the financial sector to increase the…
Q: The pattern that provides a way to access the elements of an aggregate object sequentially without…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: What kind of interface, a graphical one or a command line one, do you like to use? Why?
A: A command-line interface (CLI) is a kind of user interface (UI) that requires the user to enter…
Q: In order to improve speed, your organization has decided to spread its product database over many…
A: The solution to the given question is: Some of the issues that must be overcome when the product…
Q: want use case diagram and for Train booking app
A: The interactions between the many components of the train booking app system are graphically…
Q: What are some key ways in which application architecture and network architecture differ from one…
A: The communication process may be divided into levels in network organisations thanks to network…
Q: Sample Output 2 Enter first number: 5 Enter second number: 10 Enter third number: 6 Maximum Value:…
A: //java code with explanation import java.util.Scanner; public class Main { // Define a function…
Q: The number of addressing schemes used in a computer network.
A: Answer the above question are as follows
Q: What kind of contribution does the Model-View-Controller (MVC) architecture make to the overarching…
A: How does MVC aid in structuring web applications? MVC is a superior method for organizing code. You…
Q: Can you explain the inner workings of distributed data processing and what it entails?
A: Introduction : Distributed data processing is a type of computing that involves multiple computers…
Q: Recently, Google established an office in Pakistan. You have just landed a job there. During the…
A: Introduction: The data processing logic and control for a microprocessor are housed on a single…
Q: You are asked to design an automation support unit for telecommunication company. A request that is…
A: Communication:- Communication is the exchange of information, thoughts, or ideas between individuals…
Q: What are the most significant differences that distinguish a data warehouse from a database?
A: Introduction: Any collection of data structured for storage, accessibility, and retrieval is a…
Q: When exchanging data between a browser and a server, which protocol, like SSL or TLS, provides the…
A: Internet Security Protocols: Internet Security Protocols are a set of protocols, standards, and…
Q: You are working as a software developer on NASA's Mars Explorer robotic rover project. You need to…
A: Algorithm: 1. Define a function that takes three parameters (r, n, h).2. Calculate the surface area…
Step by step
Solved in 2 steps

- Consider the following code for a process P0 (assume turn has been initialized to zero): --- Etc. --- while (turn != 0) {} Critical Section /* … */ turn = 0; --- Etc. --- For process P1, the code is: --- Etc. --- while (turn != 1) {} Critical Section /* … */ turn = 1; --- Etc. --- Does the above code meet all the required conditions for a correct mutual-exclusion solution? Explain and justify your answer.Using Kleene’s Theorem Turn the following FAs to REs. Label each elimination step by step and explain the each step (e.g. step 1: eliminate state x).Create the Kmaps and then simplify for the following functions (leave in sum-of-products form): a) F(w,x,y,z) = w'x'y'z' + w'x'yz' + w'xy'z + w'xyz + w'xyz' + wx'y'z' + wx'yz' b) F(w,x,y,z) = w'x'y'z + w'x'yz' + w'xy'z + w'xyz + w'xyz' + wxy'z + wxyz + wx'y'z
- Using Kleene's Theorem Turn the following FAs to REs. Label each elimination step (e.g. step 1: eliminate state x).Find solution [AX]= 1000H, [BX]= 4000H, [SI]=3000H, [DI]= 4000H, [BP]= 5000H, [SP]= 6000H, [CS]=0000H, [DS]=9000H, [SS]= 2000H, [IP]= 7000H. 1-MOV AX, [3F27H] 2-MOV DX, [BX] 3-MOV AX , [BX + SI] 4-MOV AX, [BX + SI + 100H] 5-MOV DL,[2400]The NoSQL CAP theorem states the following. Why can't we use both C and A?
- > Now calculate the relativeperformance of adders. Assume that hardwarecorresponding to any equation containing only OR orAND terms, such as the equations for pi and gi on pageB-40, takes one time unit T. Equations that consist ofthe OR of several AND terms, such as the equations forc1, c2, c3, and c4 on page B-40, would thus take twotime units, 2T. The reason is it would take T to producethe AND terms and then an additional T to produce theresult of the OR. Calculate the numbers andperformance ratio for 4-bit adders for both ripple carryand carry lookahead. If the terms in equations arefurther defined by other equations, then add theappropriate delays for those intermediate equations,and continue recursively until the actual input bits ofthe adder are used in an equation. Include a drawingof each adder labeled with the calculated delays andthe path of the worst-case delay highlighted.Theory of Computation Prove that XY is undecidable XY = { ⟨M⟩ ∣ M is a TM where x∈L(M) and y∈L(M) } Prove this by reducing it from ATM which is proven to be undecidableUsing Kmaps, determine all the minimal sums and minimal products for the following functions: F(w,x,y,z) = ∑m(6,7,9,10,13) + dc(1,4,5,11,15) F(w,x,y,z) = ∑m(1,2,3,4,6,9,12,14)+dc(5,7,15) F(w,x,y,z) = ∏M(0,2,3,5,6,9,10,11,13) F(w,x,y,z) = wx + y’z + wx’y’ + w’xyz F(w,x,y,z) = (w+x’)(w+y+z)(w’+x’+z’)(w+y’+z)
- Given the formal definition of the finite state machine (FSM):M1= { {A, B}, {0,1}, { ((A,0),A), ((A,1),B), ((B,0),B), ((B,0),A) } , A, {B} }· Convert M1 from a non-deterministic FSM into a deterministic FSM.· Draw them both (non-deterministic and deterministic FSMs in STD) and write the State Transition Table and the formal definition of the deterministic FSM.Plz sir must solve this question.From the given, answer the following. 1. The ramp response of the the transfer function G(s) will yield how many terms when applying partial fraction expansion? 2. Which of the following is a valid denominator of any term in the partial fraction expansion? a. s3 b. s+1 c.s d. s+3

