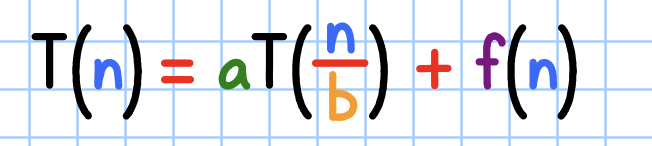
T(n) = aT (^) + f(n) F(n) = 3 F()+n, use el Teorema Maestro
Q: The following should be done in a user experience analysis to understand the problem being addressed…
A: Step 1: All the options are correct Document and understand the content that is presented as part…
Q: please read the instruction carefully and answer the question
A: Let's go through the solution in detail.The given problem is the Sum-of-Subsets problem, where we…
Q: In the below cases, comment on the situation about what type of instructions won’t work correctly if…
A: a) MemtoReg = 0 - This instruction selects the source of the data for the register file. If this…
Q: Given integer inputs howMany and maxNum, generate an array of howMany unique random integers from 0…
A: Introduction: In this program, we aim to generate an array of unique random integers within a given…
Q: Retrieve information from this webpage "https://www.chewy.com/b/dry-food-294", Dry Dog Food. The…
A: Products listed on the Chewy webpage for dry dog food along with their prices for auto-ship and…
Q: Provide Full C++ Code Solutions for: Creature.h, Creature.cpp, Human.cpp. Human.h, Elf.h, Elf.cpp,…
A: referencegithub.com/Fidget-Cube/Old-C--Assignmentsgithub.com/LinnierGames/Assignment-9github.com/kei…
Q: in the image below the Red "X" denotes the horse has fallen While the Race class is almost complete,…
A: Approach to solving the question: Dear student, we can systematically address the issues in the Race…
Q: Assume that a customer purchase a new car every 5 years, for a total of 10 cars through her…
A: Let's delve into a detailed explanation of the problem and its solution.Understanding the…
Q: What are the purposes of the HLR and VLR in GSM networks? What elements of mobile IP are similar to…
A: The Home Location Register (HLR) and Visitor Location Register (VLR) are crucial components of GSM…
Q: A system has a CPU utilization of 80%. If the total time is 1000 seconds, calculate the time the CPU…
A: Solution:
Q: What are DAM Classes: Designing data access and manipulation classes and explain its rule: create…
A: Approach to solving the question: DAM Classes, or Data Access and Manipulation classes, are a…
Q: Please identify the correct statement(s) for the following code snippet. addrDiv =…
A: In the provided code snippet, the variable "addrDiv" is assigned the result of a method chain,…
Q: The class in Java from which all other classes are derived is called the ........ class.
A: The objective of the question is to identify the base class in Java from which all other classes are…
Q: Please answer the attached image! Automata and computation!
A: Step 1:After the transition to state 'p', what is the element that is located on the top of the…
Q: Q2. RSA Alice starts the RSA, with key generation. She selects p-19 but she is confused with the…
A: Step 1 RSA consider 2 numbers P and Q which are prime numbers. n=p*q and phi(n) = (p-1)*(q-1) and e,…
Q: Assume that a customer purchase a new car every 5 years, for a total of 10 cars through her…
A: The objective of the question is to calculate the expected lifetime profit of a customer who starts…
Q: College of CSIT Database Management System (IS 304) Pharmacy Prescriptions Case Study 1. Problem:…
A: Approach to solving the question: Approach to Designing the Pharmacy Prescriptions DatabaseThe…
Q: Need help ! I have attached the problem! I am taking database management course.
A: Prof_ID | Course_Name | Course_FeeThe composite key for this table is (Prof_ID, Course_Name), as…
Q: The B_____method of threads begins but does not execute a thread. The ______ method executes a…
A: The question is asking about two methods in thread execution in computer programming, specifically…
Q: Both interfaces and abstract classes can be used to specify common behavior for objects. Explain…
A: When deciding between using an interface or an abstract class to specify common behavior in objects,…
Q: Could you assist me in understanding this intricate algorithm and guide me through transforming it…
A: Approach to solving the question:Designing a Turing machine for division requires careful planning…
Q: For a tree which uses lazy deletion, implement a function which counts the # of deleted nodes.
A: TreeNode class: Defines a class representing a node in the binary search tree. Each node has…
Q: Given a family LCP(I*) of languages over a common alphabet Σ, let denote the set-theoretic union of…
A: To prove that if ℒ(Σ*) is finite and each A ∈ ℒ is decidable, then ℒ is decidable, we can use the…
Q: For each of the following problems, you should write your answer as an expression. Do not give the…
A: Step 1: Analyze the problem and list down the givenEnglish Alphabet contains 26 lettersnumber of…
Q: Consider the processes P1 and P2 as shown below. Use semaphores to ensure that the functions are…
A: To ensure that the functions f1(), g1(), g2(), and f2() are executed in the correct order using…
Q: Let a, b, c denote the statements: "It is raining", "It is humid", "It is sunny". Represent the…
A: 1. "It is not raining": This is represented by the statement ¬a, where "a" represents the statement…
Q: Please give step by step solution so i can fully understand. I a unsure how to go about solving…
A: To find candidate keys for the relation R(A, B, C, D, E, F) with the given functional dependencies,…
Q: Could you lend me your expertise with this question? I'm having difficulty grasping how to approach…
A: To create a Turing machine that computes the quotient and remainder of two binary numbers, we need…
Q: can you help me with this:
A: To calculate the total path cost to each of the cities connected to Arad (Sibiu, Timisoara, and…
Q: ⚫ Each prescription is exclusive to a doctor. However, each doctor may compose a large number of…
A: This set of tasks involves designing and implementing a database system for managing prescriptions,…
Q: (stack, 0xffffffffffffffdc, 4) INDIRECT (stack, 0xffffffffffffffdc, 4) , (const, 0x2b, 4) indicates…
A: The p-code instruction (stack, 0xffffffffffffffdc, 4) INDIRECT (stack, 0xffffffffffffffdc, 4) ,…
Q: In single-cycle processor, what are the values (in binary) of instruction[31-26],…
A: Note: Please be aware that if you encounter any difficulties or need further clarification,…
Q: Your ReadRoomFile program reads a room file. Is it possible to tell how many rooms are in the file…
A: Determining the number of rooms in a file from its size alone is generally not possible due to…
Q: Could you assist me in understanding this intricate algorithm and guiding me through the steps of…
A: Creating a Turing machine for division can indeed be complex, but breaking down the process step by…
Q: Consider a program where 95% of the code can be parallelized. If you have aninfinite number of…
A: Approach to solving the question: To understand how to derive the maximum speedup using Amdahl's…
Q: What is DAM classes and what is the rule to create them
A: "DAM" often refers to "Digital Asset Management," which involves organizing and managing digital…
Q: A Python Program with 10 menu choices. program could answer 1. Which states did not present data?2.…
A: I have provided the comments in the code so that you can easily…
Q: Hello, I am researching about the two following topics in reverse engineering and program analysis.…
A: ANSWER 1:-Identifying and Analyzing Obfuscated Code During Reverse EngineeringResearching methods to…
Q: Don't use ai to answer the question and solve all parts
A: 1. Longest Common Subsequence (LCS)The Longest Common Subsequence (LCS) problem involves finding the…
Q: One of two biased coins A and B is selected and flipped 3 times. Let A be the event that coin A is…
A:
Q: Need help ! I have attached the problem! I am taking a database management course. i am using mysql…
A: CREATE TABLE Statement:This statement creates a table named Employee.It defines five columns:Emp_ID…
Q: IN JAVA PLEASE In the course menu of the final project, don't delete class if a student is enrolled…
A: Step 1: Understand the problem The problem requires you to create a Java program that handles…
Q: Decision theory develops methods to make optimal decisions in the presence of uncertainty. A)…
A: Step 1: Define decision theoryDecision theory is the addition of utility theory with probability…
Q: Circuit Assignment (Digital Logic) You have been hired by a home security company to design and…
A: The objective of the question is to design a logical circuit for a home security system. The system…
Q: c) What is the value stored in the AC when the program terminates? Hex Address Label Start,…
A: To provide a comprehensive explanation of the program's execution and the value stored in the…
Q: I try to merge the two datasets below using the following code use test score.dta, clear merge 1:1…
A: Step 1: Step 2: Step 3: Hope you understand if you have any query then raise it Please do rate…
Q: For each of the following functions, determine whether the function is: Injective (one-to-one).…
A:
Q: Design a binary multiplier using full adders and AND gates. (10 points)
A:
Q: question that I need with:7.10 Show that ALLDFA is in P.
A: To explain in detail how the language ALLDFA is in P, we need to delve into the concept of…
Q: Hello. Please answer the attached Operating Systems question and its two parts correctly and…
A: Detailed explanation:Part 1 :Since the receive primitive blocks until a specific message arrives,…
use the master theorem
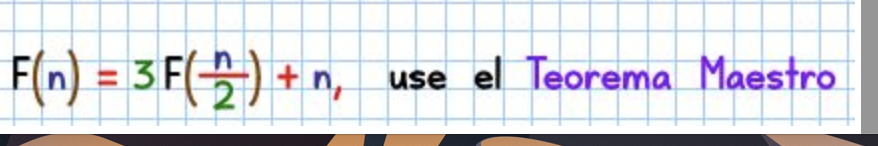
Step by step
Solved in 2 steps

- Write a function that sums all the double values in the major diagonal in an n* n matrix of double values using the following header:const int SIZE = 4;double sumMajorDiagonal(double m[][SIZE])Let N be an unordered array of integers. The maximum number of compares required to find the minimum value is N-1. [True/False]Write Algorithm procedure code to illustrates the procedure for Fibonacci search. Here n, the number of data elements is such that:i) Fk+1 > (n+1); andii) Fk + m = (n +1) for some m ≥ 0, where Fk+1 and Fk are two consecutiveFibonacci numbers.
- Function Name: odd_even_diagParameters: a 2D list (list of lists)Returns: list of lists Description: Given a 2-dimensional matrix (list of lists) with any size (n*n), modify it according to the following rules: Find the sum of the main diagonal. If the sum is an odd number, change all the values of the given matrix (except the main diagonal) to 0. If the sum is an even number, change all the values of the given matrix (except the main diagonal) to 1. Return the resulting matrix. Example 1:If argument is: [[1, 2], [4, 3]] odd_even_diag should return: [[1, 1], [1, 3]] because the sum 1 + 3 is even. Example 2:If argument is: [[1, 2, 3], [4, 5, 6], [7, 8, 9]] odd_even_diag should return: [[1, 0, 0], [0, 5, 0], [0, 0, 9]] because the sum 1 + 5 + 9 is odd.Take example given a list of queries, each consisting of three integers: a, b, and k. Your task is to perform a series of operations on an array of size n such that each element in the array is incremented by k in a specific range defined by a and b.python Create a dict mapping keys (N = 100, 200, 400, ... 51200) to arrays with linear entries (length N) derived from random sampling from a uniform distribution [0, 100000].
- All rows and columns of n X nA data set has 4 columns--index, CUSTOMER_EMAIL, Net Revenue, and Year. For each year we need the following information: New Customer Revenue e.g., new customers not present in previous year only Lost Customers New Customers Total Customers Previous Year Total Customers Current Year Please implement it using python.In elementwise multiplication A.*B each value in one matrix is paired up with a buddy value in the other and they are multiplied together.In matrix multiplication A*B each row in matrix A is dot-producted with each column in matrix B.The value in the upper left corner of the matrix C is the same as which of the following?C = A*B; options: A(1,1) * B(1,1) dot(A(1,:),B(:,1)) A = [3 1; 5 2];B = [1 -1; 4 0];C = A*Bthe value in the upper left corner of the matrix C is which of the following? % Starting with this code:a = [1 2 3]b = [-1 0 1]% All of the following are identical, except which one? Question 4 options: dot(a,b) a*transpose(b) b*transpose(a) sum(a.*b) They are all identical Fill in the blank to calculate the dot product of amounts and costs.amounts = [2 1 2 5 1]costs = [3.5 1.25 4.25 1.55 3.15]____________ Question 5 options:…
- Write a code in "C"that can swap all the values of its first row with its last row in a [n×m] matrix After swapping, add all the values of the last column.Exerxising LogProblem2: A square matrix can be represented by a two-dimensionalarray with N rows and N columns. You may assume a maximum size of 50 rows and 50 columns. 1. Write an algorithm MakeEmpty(n), which sets the first n rows and n columns to zero. 2. Write an algorithm Add(M1, M2, M3), which adds two matrices M1 and M2 together to produce matrix M3. 3. Write an algorithm Subtract(M1, M2, M3), which subtracts matrix M2 from matrix M1 to produce matrix M3. 4. Write an algorithm Copy(M1, M2), which copies matrix M1 into matrix M2.











