To 3 7 $ 3 6 %24 2.
Q: Determine all the essential prime implicants. с) d) not determine the additional prime implicants (i...
A: Truth table is given. WE need to determine the Essential prime implicants and prime implicant and mi...
Q: 5. Define a A-term called or such that or is a binary logical or function for Church booleans. Also,...
A: The creator of the lambda calculus, realised this and consequently set about to make a series of enc...
Q: Q2. Implement the following expression using 0-address, 1-address, 2-address, 3 address ISA's A= B*(...
A: In computer organization, computer provided by the task to perform in the form of instructions. It i...
Q: Android system has several application building blocks, such as, Activity, In and IntentReceiver, No...
A: a) In Android app development, a content provider is utilized to centralize material in one location...
Q: Q1) Write a C++ program to compute the value of S using function, where the value of S(x, n)= X/2! -...
A: below is the code for Q 1 according to policy mention Q 2 and Q 3 in different questions
Q: Why is it that the single-precision real format does not support an exponent of 127?
A: Introduction: the question is about Why is it that the single-precision real format does not support...
Q: What is manifest XML in android? а. It has information about the application O b. It has information...
A: What is Android Menifest ? An Android Manifest would be an XML file that inc...
Q: Attach code and output screenshots
A: Program: #include <stdio.h>#include <stdlib.h>#define SIZE 16int** ints2int_ptr(int* arr...
Q: In the main.asm file, you are to create a few arithmetic calculations using the following instructio...
A: Answer is give below:
Q: How will you create and deploy a business information system for your corporation using the primary ...
A: Introduction Information System Development Stages:- System survey, needs analysis, design, impleme...
Q: Man-in-the-middle (MITM) attacks can be averted in several ways. Give a step-by-step respons
A: Actually, given question regarding Man-in-the-middle (MITM).
Q: Describe the procedures involved in the programming analysis phase.
A: Introduction the question is about to Describe the procedures involved in the programming analysis p...
Q: What does the function that overloads the operator >> for a class return?
A: Intro It is possible to provide a different implementation to common operators such as + or - in C++...
Q: 1. Consider this very simple function: def cube(x): answer = x * x return answer (a) What does this ...
A: answer is
Q: What are the pros and drawbacks of employing cloud computing in financial systems?
A: Cloud Computing: Cloud computing refers to the on-demand availability of computer system resources, ...
Q: Write a program that takes a sequence of non-negative numbers and performs the computation suggested...
A: Here I have created an empty list. Next, I have created an infinite while loop, and inside the loop,...
Q: f:A B A = {0, 1, 2}, B = {0,1} f(0) = 1, f(1) = 0, f(2) = 1 1.Is f, as described above, a function? ...
A: Yes f is a function. This is because each element of its domain A is assigned to exactly one element...
Q: When using an ellipsis in a function (i.e., x <- function(...), how can you compare the lengths of t...
A: Step 1 : Start Step 2 : Define an ellipsis function checkArguments() which takes indefinite number o...
Q: Which of the following are characteristics of BIOS? i) The data stored in BIOS is temporary. ii) I...
A: BIOS is firmware that is embedded on a small memory chip on the computer's motherboard. It acts as a...
Q: details the rules and policies needed to address confidentiality (C), integrity (I), and availabilit...
A: Confidentiality: - Confidentiality is often equivalent to protection. Acceptable measures to ensure ...
Q: When do signature-based detection methods become ineffective?
A: Introduction: One of the biggest shortcomings of the signature-based malware detection approach is t...
Q: What exactly is a memory address? What is its function?
A: Memory address is a reference to a particular memory location that is utilized at different levels b...
Q: 5. Why do people keep currency in their pockets when bank deposits pay interest? Because bank depos...
A: Here is the detailed explanation of the solution
Q: using Huffman encoding. What is your binary representation of the message? Draw your Huffman trie ...
A: Given message: “algorithms design and analysis is an art" We need to encode using Huffman encoding a...
Q: P4: 0 is an equivalence relation
A: Big theta is either the exact performance value of the algorithm, or a useful range between narrow u...
Q: As the CISO, you're in charge of developing an information security programme that's backed up by a ...
A: Introduction: Program of security measures: Unified threat management (UTM) refers to the process of...
Q: In order for a network to function properly and efficiently, what three characteristics must it meet...
A:
Q: Write code that outputs variable numBirds as follows. End with a newline. Ex: If the input is: 3 the...
A: The required Java program is in the next step with explanation given in code comments.
Q: Clustering is connected to the organising of parts, chapters, sections, and subsections in a book. E...
A: Introduction: the question is about clustering is connected to the organizing of parts, chapters, se...
Q: What security policy would mitigate the use of no encryption or hashing to regulate data flow and un...
A: Introduction the question is about What security policy would mitigate the use of no encryption or h...
Q: = (a*y)*x*
A: Given as, x+y*=x*y*x*
Q: List five ethical principles and (FIVE) five policies that regulate the usage and deployment of big ...
A: Introduction: Here we are required to list five ethical principles and five policies that regulate t...
Q: What exactly is a race condition? What exactly is synchronisation?
A: Answer: 1. Race condition: A race condition is a problem that occurs when a system attempts to perf...
Q: 7. Determine whether the following graphs are trees. Explain your answer. а) V3 V5 V6 b) vo Vネ v5 V6
A: Solution: For determine the given graph is tree, if it has the following properties. 1) In the undir...
Q: Which one of the following is the built-in database in android? O a. Java O b. MS Access O c. SQL O ...
A: I have answered all the 3 parts. First we will see which one is the built-in database in android.The...
Q: Boolean expressions are used to symbolically define logic functions by employing input variables and...
A: Intro the question is about Boolean expressions are used to symbolically define logic functions by e...
Q: How is a mistake in a database system more serious than a mistake in a non-database setting?
A: Introduction : Here we are required to state the reason, why a mistake in a database system more ser...
Q: Write an assembly program to set RO-1 if there's a 5 in one of ten memory locations 5 is found, it s...
A: 1. First we set R0=1, R1=-5 ,r3=10, R4=x3100 , R2=M[R4] then we check if there is value 5 at memory ...
Q: You are given a hash map implementation that can store key-value pairs with the following operations...
A: I have answer this question in step 2.
Q: C++ Create a class and a vector of that class. Show usage of it
A: The C++ Standard Library vector class is a class template for sequence containers. A vector stores ...
Q: Why is it that on today's Internet, audio and video traffic is frequently carried through TCP rather...
A: Introduction: UDP and TCP: The UDP is an abbreviation for "User Datagram Protocol," It is a protocol...
Q: Select one of the following and prepare a worker-machine chart that describes and activities and tim...
A: Work machine chart is similar to flow chart which contains flow or series of steps one by one. The A...
Q: Which of the following is not a characteristic of binary system? a. It has the largest base among a...
A: Option a is answer
Q: Which XXX should replace the missing statement in the following BSTReplaceChild algorithm? ESTReplac...
A: The question is to fill the missing statement in BSTReplaceChild algorithm.
Q: Prove that gcd(a + b, a – b) = gcd(2a, a – b) = gcd(a + b, 2b). Show your work! Justify each step.
A: Given that, Prove gcd(a+b, a-b) = gcd(2a, a-b) = gcd(a+b, 2b) Suppose d divides a+b and a-b.Then d d...
Q: What programming language is used to develop programmes by assembling a collection of objects?
A: Introduction the question is about What programming language is used to develop programs by assembl...
Q: User- and kernel-level threads Using ULTS instead of KLTS has a number of advantages. Could you tell...
A: Disadvantages of the KLT approach for threads implementation are below: 1) Kernel Level Threads are ...
Q: What class can you use to view the current IP address of a network adapter? Does the class have any ...
A: CIM is a Common Information Model. It tells and gives instruction on how information should be struc...
Q: Q1/w.p. to read 3 nodes and print it? Q2/ W.P. to read 3 nodes and print only even numbers/ Q3/ W.P....
A: The solution to the given problem is below. ***Note: According to Bartleby policy we are not allow...
Q: What are the four non-job roles in the performance framework, how important are they, and how might ...
A: Non-performance framework: The performance framework is a declaration of planned performance and eff...
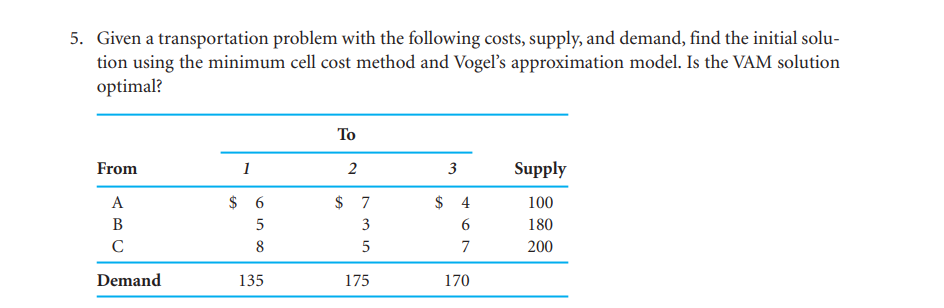
Step by step
Solved in 2 steps with 1 images

- Find the initial basic feasible solution for the following transportation problem using VAM. Explaineach step.Ram ,mohan and sohan took loan of RS.x,y and z on rate of intrest r%,p%,q% for time t1,t2 and t3 years respectively.calculate simple intrest they will pay and find who will pay the most using ternary operator?A contractor owns three excavators of different capacity. He/she wants to dispatch these excavatorsinto three different jobs. The performance of the excavators is measured as the time consumed toperform each job. The data of the time tests are shown as given in the table below. (a) Draw a network flow diagram.(b) Formulate a mathematical model to obtain the minimum time.(c) Solve this model using the Vogel’s approximation model.
- Consider the dual of a minimum cost network flow problem in which the costs are integer. Prove that the basic feasible solutions are integer.Please extract this tabular form using the least cost method Part 4-Network Problems(10)The U.S. government is auctioning off oil leases at two sites: 1 and 2. At each site, 100 000 acres of land are to be auctioned. Cliff Ewing, BlakeBarnes, and Alexis Pickens are bidding for the oil. Governmentrules state that no bidder can receive more than 40% of the land being auctioned. Cliff has bid $1,000/acre for site 1 land and $2,000/acre for site 2 land. Blake has bid $900/acre for site 1 land and $2,200/acre for site2 land. Alexis has bid $1,100/acrefor site 1 land and$1,900/acre for site 2 land. Formulate a balanced transportation model to maximize the government’s revenue.The city of Smallville consists of five subdivisions, Mayor Takeda wants to build telephone lines to ensure that all subdivisions can communicate with each other. The distances between the subdivisions are given in the figure below: Assume that no telephone line can be built between subdivisions 1 and 4. ______ 1) What is the minimum length of cable required? 12 units b. 14 units c. 15 units d. 16 units ______ 2) Which arcs should be connected to obtain the least cable wires needed? (1, 3), (3, 5), (3, 4), (3, 2) c. (1, 5), (5, 3), (3, 4), (3, 2) (1, 3), (3, 5), (5, 4), (4, 2) d. (1, 2), (2, 4), (4, 3), (3, 5) ______ 3) What would be the total length if the following arcs are connected: (1, 3), (3, 4), (4, 5), (3, 2) 18 units b. 17 units c. 15 units d. 16 units

