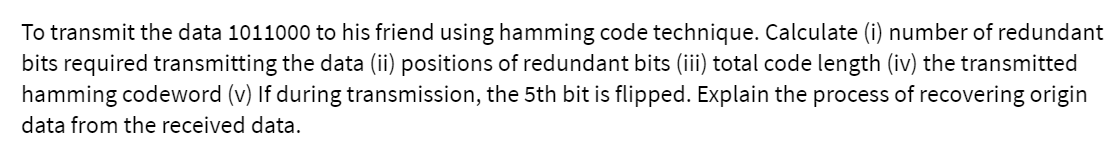
To transmit the data 1011000 to his friend using hamming code technique. Calculate (i) number of redun bits required transmitting the data (ii) positions of redundant bits (iii) total code length (iv) the transmitte
Q: Describe four challenges that might arise while merging relationships.
A: Given: With the merging of relationships, four challenges arise, and their resolution is as follows:…
Q: When should a network update be scheduled, and how long should it last?
A: Intro Modern technologies make business faster and smarter than ever before. Clouds and mobility…
Q: What does the term "agent" signify in AI?
A: What does the term agent signify in AI? in below step.
Q: What are some of the numerous possible techniques that a company may use when it is putting in place…
A: An organization may employ the following approaches to install a new system: Parallel: When the new…
Q: 2. Write a recursive function printNum()that prints any given number by putting spaces between…
A: I give the code in C along with output and code screenshot
Q: What distinguishes a quantum computer from a regular computer are its defining characteristics? In…
A: Today we live in an age of classical computers, which operate based on the binary system of 1 and 0.…
Q: In order for an instruction set to be termed orthogonal, the computation performed by each set must…
A: For an instruction set to be orthogonal, each set value's calculation must be independent of the…
Q: Quality Control: publish a report on the GIT and GitHub application
A: The term "quality control" (QC) refers to a technique or group of procedures designed to verify that…
Q: Fingerprinting, according to the opinions of a number of cybersecurity experts, is a kind of misuse…
A: Browser fingerprinting: Browser fingerprinting (sometimes called device or online fingerprinting) is…
Q: What are the two primary functions of an operating system, as well as the two separate modes in…
A: Introduction: The most fundamental system performance function. Process of Management. 1. During the…
Q: On average, which component of a high-end gaming PC consumes the most power on a daily basis?
A: Introduction: A gaming computer is a specially configured personal computer made for the exclusive…
Q: In compared to connection-based protocols, connectionless protocols should have their merits and…
A: Examine the benefits and drawbacks of connectionless protocols against connection-based protocols. A…
Q: What exactly is meant when someone makes a reference to DHCP, also known as the dynamic host…
A: Start: Dynamic Host Configuration Protocol is the abbreviation for DHCP. The Dynamic Host…
Q: Let's say that in addition to being a component of the primary key, an attribute is also a candidate…
A: Required: What do you respond if someone suggests that an attribute which is a component of a…
Q: Computing at the quantum level and block chains are two topics that are timely and should be…
A: Given: Even more exciting is the fact that the technology behind blockchain is gaining popularity at…
Q: What distinguishes traditional computers from their quantum analogues, and how do these differences…
A: The History of Computing: Traditional computing is defined by the use of physical data centers for…
Q: What precisely does the phrase "quantum computing" refer to, and how does the corresponding process…
A: AT THE QUANTUM LEVEL COMPUTING: Quantum computing is a kind of computer that uses an item's quantum…
Q: What are the main distinctions and similarities between on-premises data center and cloud IT…
A: The major difference between the cloud based and premises based security is that the cloud based IS…
Q: If management of a firm want to enhance or buy new technology in the future, are there any factors…
A: The above question is answered in step 2 :-
Q: Is it feasible to utilise object-oriented programming with VB.NET? Example illustrating OOP's…
A: Given: In order to circumvent the limitations of structured programming, object-oriented programming…
Q: In order for an instruction set to be termed orthogonal, the computation performed by each set must…
A: Introduction: In order for an instruction set to be considered orthogonal, the calculation of each…
Q: Let's say that in addition to being a component of the primary key, an attribute is also a candidate…
A: Given: What do you respond if someone suggests that an attribute which is a component of a composite…
Q: What is the truth about the assertion that data structures and algorithms are becoming obsolete in…
A: In the period of Machine Learning, it isn't a fact that information designs and calculations are…
Q: Would you be able to discern the difference between a candidate key and a composite primary key in a…
A: Introduction: Key Key is an attribute or group of characteristics that identifies a relation or…
Q: The primary key of a connection and the functional interactions that occur among its features are…
A: Introduction: Primary and foreign keys are the cornerstones of relational database theory.
Q: When an attribute is a component of a composite primary key, that attribute is also considered to be…
A: Inspection: A single field or a composite phrase that satisfies the criteria of a primary key might…
Q: The characteristics that are inherently present in wireless networks give rise to a variety of…
A: Introduction: The characteristics that are inherently present in wireless networks give rise to a…
Q: Is there a link between software design and the ideas of cohesion and coupling?
A: Link between software desing and idea of Cohesion and coupling
Q: Your computer may be shielded from any threats coming from the outside world if you have a firewall…
A: Firewall is installed: Software firewalls, such as the Windows firewall, are installed on personal…
Q: It's possible to have both a primary key and a candidate key for a single property at the same time.
A: Required: What should be mentioned if it is asserted that an attribute of a composite primary key…
Q: Describe how the Internet and the World Wide Web have grown throughout the years.
A: Given: Internet and WWW expansion gives the impression of a new technology. The Web is a primary…
Q: Is there a specific function that a computer's core processing unit serves?
A: A CPU is a computer brain, which contains all the circuitary needed for processing inputs, data…
Q: What other concerns do you have before choosing if database as a service is the best solution for…
A: Answer:
Q: Consider the following relational schema: violations(VID BID SNu SNa Zip InD Bor BoI NVI NVD).…
A: Following is the Answer: PFA Let FD=Functional Dependency Let all FD be from FD1 to FD6 SK= Super…
Q: .35 (Sides of a Triangle) Write an application that reads three nonzero values entered by the user…
A: #include <iostream>using namespace std; int main(){ double a, b, c;…
Q: Cookies are used on websites in order to monitor the behaviour of visitors and their browsing…
A: Start: Cookies are simply text files that are stored on the user's system by the webserver. This…
Q: An individual is using a computer with the IP address 10.0.0.5 to carry out their job on a local…
A: UDP: UDP (User Datagram Protocol) is a common communications protocol used to send data between…
Q: What is s semaphore and what are its types
A: Your answer is given below.
Q: What would you say is the best way to explain the typical synchronisation error known as a race?
A: Given: A race situation is a synchronisation error caused by errors in the operating system's code.…
Q: What does it imply precisely when people talk about "instruction pipelinelining"? Provide the…
A: Given: Instruction pipelining is a method that is employed in the design of contemporary…
Q: What is the following variables in camel case: NUMBEROFDAYS
A: In programming language, there are mainly three types of variable cases, that are: Camel case Snake…
Q: Investigate in further detail the distinctions that exist between TCP and UDP.
A: Given: Transmission Control Protocol (TCP) is an acronym for Transmission Control Protocol. The User…
Q: Is it feasible to utilise object-oriented programming with VB.NET? Example illustrating OOP's…
A: In order to circumvent the limitations of structured programming, object-oriented programming was…
Q: Explain why the TCP/IP stack is so vital to the process of data transmission and why its importance…
A: Introduction: 1) TCP/IP is the core communication system of the World Wide Web. It lets every device…
Q: ctor affecting the speed of the parall
A: Introduction: Below the key factor affecting the speed of the parallel adder is
Q: How does a quantum computer differ from a normal computer? What challenges must be overcome before…
A: Introduction: Qubits, which can represent both 0 and 1 simultaneously, are used in quantum…
Q: What is natural language processing (NLP) and how does it work?
A: Introduction: Natural language understanding (NLU) is a subset of natural language processing (NLP)…
Q: A candidate key is present for each of the properties that make up a composite primary key. What…
A: Introduction: A key is a property or group that allows us to identify a tuple in a relation or a row…
Q: Your computer may be shielded from any threats coming from the outside world if you have a firewall…
A: Answer 1) many times yes. because if we have installed firewall , so protected against outside…
Q: Give a condensed description of the positives and negatives of connectionless protocols in…
A: Given: Give a condensed description of the positives and negatives of connectionless protocols in…
sure strict report dont post existing or unnecessaruy skip if not 100% know
Step by step
Solved in 2 steps with 2 images

- What are the CRC bits (R) associated with the payload containing first four bit 1101 and last four bit is the last digit of your reg number (i.e. 5, payload = 1101 0101). Suppose that the 4-bit generator (G) is 0101, and r = 3Question 17 Aa.For an original message size of 14 bits in a Hamming code FEC system, which one of the following bit position in the resulting message does the third parity bit NOT protect? 5 13 7 4 16 14 6 12 15 Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this linea. Compute for the data efficiency of transmitting if the data format is a General Synchronous Data Frame. b. For an asynchronous data transmission (wherein 1 byte of data is accompanied by a specific number of auxiliary bits), how many start and stop bits are there if the data efficiency in transmitting is ? The number of start bits is equal to the number of stop bits.
- If an error happened in the following scenario, please mention whether it occurred. The sender sends the number “001011010” to the recipient. The devices make use of odd parity, 8-bit data, and a 1-bit (LSB) parity for each bit of information. What happens if the devices are utilizing even parity instead than odd? What are the communication protocols that are utilized in TESLA automobiles? Insert the schematic of the one(s) that you have discovered.We want to transmit 1000 characters with each character encoded as 8 bits. a. Find the number of transmitted bits for synchronous transmission. b. Find the number of transmitted bits for asynchronous transmission. c. Find the redundancy percent in each case.2) Compute data sent for a bit stream of 101011 with CRC using a generator 1010 Randomly assume any bit to have been corrupted, Illustrate how the receiver can detect if the data was corrupted.
- Any errors in the following scenario would be greatly appreciated. The sender sends "001011010" to the recipient. For each piece of information, it utilizes 8-bit data with odd parity and 1-bit (LSB) parity. If devices utilize even parity, why don't they use odd parity as well? The communication protocols used in Tesla vehicles may be found on the company's website. Provide a schematic if you have one.Why is the gap time between bytes vary in asynchronous transmission?Please check my answer and correct the part which is need to be foxed.And provide justification for the answer. a) The transmission time of a frame can be calculated as follows: Propagation delay (Tp) = distance/speed = 5km / 200000 km/s = 0.0025ms Transmission time (Tt) = frame size/bandwidth = 10000 * 8bits / (1Mbps * 10 ^ 6) = 0.008sec = 8ms Total time for transmission = 2 * Tp + Tt(since the frame has to travel from A to D and then D to A) = 2 * 0.0025ms + 8ms = 0.005ms + 8ms = 8.005ms The transmission time of the frame from A to D is 8.005 ms. b) The efficiency of the CSMA/CD protocol is given by the formula: Tt is the transmission time of a frame C is the number of collisions, Tp is the propagation time of a signal from one end of the segment to the other. Efficiency = Tt / (C * 2 * Tp + Tt + Tp) Assuming that there are no other stations transmitting or attempting to transmit on the segment, the transmission from A to D will succeed without collisions. Therefore,…
- 1. If they each want to send the following bit show the total signal sent Reciever Code R1 1 R2 1 R3 0 R4 1 2. How would R1 recover its signal?. 3. Consider a case with the same codes but only R1 wants to send. Reciever Code R1 1 R2 - R3 - R4 - What signal would be sent, and how would R1 recover its signal now? 4. If an error occurs in question 12, and some bits are flipped in the signal sent from positive to negative or the other way around, how many bits minimum would need to be flipped for R1 to recover the wrong signal? 5. CDMA has another important real-world use in addition to multiple access. Given the answer to the previous question, what do you think that purpose is? How does it accomplish this? Note: this is one big question where each part couldn't be seperately asked. The picture below is the 4 recievers from the start of the question.Consider the 3rd ,6th , and7th digits of your student ID composed of seven digits. Convert it to binary format (each digit is represented by a maximum of 3 bits). For example, 1060385 is simplified to 685 and then converted to 0110 1000 0101. Assume now that we want to send your simplified student ID while being able to detect and correct single bit errors. 1.1) Using two-dimensional parity check show what will be transmitted using datawords of size 4 bits.Consider the example below that shows both the payload and the two-dimensional parity bits (shown in blue), and where exactly one of the payload or parity bits shown has been corrupted. In this example, odd parity is used.

