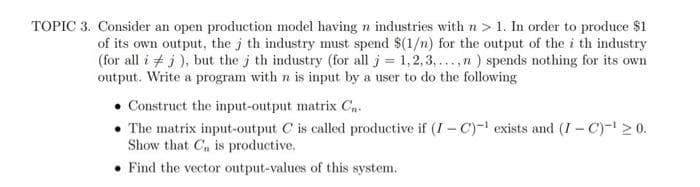
TOPIC 3. Consider an open production model having n industries with n> 1. In order to produce $i of its own output, the j th industry must spend $(1/n) for the output of the i th industry (for all i #j), but the j th industry (for all j = 1,2,3,.,n) spends nothing for its own output. Write a program with n is input by a user to do the following Construct the input-output matrix C,. • The matrix input-output C is called productive if (I - C)- exists and (I - C)- 2 0. Show that C, is productive. • Find the vector output-values of this system.
Q: Which of the following features of IoT devices can remotely control, program, and switch off?
A: Internet of Things (IoT): IoT is a related computer program; can be any size capable of performing…
Q: What is the significance of the word Magnitude in the context of computer technology?
A: The signed-magnitude representation is used in computer science to describe how a number's magnitude…
Q: What exactly does application partitioning entail?
A: Introduction: Application partitioning is a word used to describe the process of developing…
Q: How do we close the window by adding a condition if escape key is entered then close the window. i…
A: If you set the Form's 'KeyPreview Property to 'true, then it handles a Key Event before any of the…
Q: Assume a program requires the execution of 75 x106 FP instructions, 112 x106 INT instructions, 88…
A: The answer as given below steps:
Q: What is parametric polymorphism in a subprogram, and can you give an example with an explanation of…
A: Introduction: Parametric polymorphism is a programming language method that allows for the general…
Q: Maite a python program to take a list of integen from user e aquare each element woing the dict…
A: Required:- Write a python program to take a list of integers from the user & then square each…
Q: Total = a + b + c; %3. Average Total / 6; A. Logic Errors B. Run-time Errors
A: Introduction We have the following code : Total = a + b + c; Average = Total / 6; Given Options:…
Q: ivate int x; blic int y; otected int z; blic A() private int x; public int y; protected int z;…
A: The answer is below:
Q: What exactly is an open environment?
A: Introduction: An open environment is a system that provides for the free flow of information and…
Q: Computer science Explain how the BI architecture's primary components interact to produce a system.
A: Introduction: how the BI architecture's primary components interact to produce a system. A gadget…
Q: Describe enterprise storage systems, file servers, network attached storage, RAID systems,…
A: Introduction: Devices for Mass Storage: As the name implies, they are used to store a large amount…
Q: Logical data modeling demonstrates how data is arranged and how it connects to other data without…
A: Data models: Data models are those models that serve as the foundation for an organization's project…
Q: Which of the following is a method of the Object class? O a. super) O b. encrypt) O c. equals) O d.…
A: Answer is in Below Steps
Q: Total = a +b+ c; Average = Total / 6; A. Logic Errors В. Run-time Errors C. None of the above D.…
A: A programming language must follow rules and regulations to execute task successfully. Logical…
Q: relatively compare any two transmitting media(twistted piars, coxial cable, microwave, satalitte,…
A: Transmission Media: Together in the data transmission method, the repeater is the series circuit…
Q: How can you avoid accidentally corrupting class fields?
A: Protecting fields from accidental corruption : There are primarily two methods for preventing class…
Q: What is modular programming?
A: Introduction What is modular programming?
Q: The words subnet, prefix, and BGP route should be defined and contrasted with one another.
A: Subnet: A subnetwork, often known as a segmented piece of a more extensive network, is a network…
Q: i The medel belew caleulates eral utputs frem the gen inguts. (Thi madeled in all ef the rcies in…
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining…
Q: What is the significance of software development? The software development process may benefit from…
A: Software development :It refers to a set of computer science activities dedicated to the process of…
Q: Computer science Today's employment of computers in health care in Kenya is discussed in this…
A: Introduction: Today's employment of computers in health care in Kenya is discussed in this article.
Q: software maintenance
A: Answer is in given below:-
Q: If you assign a new instance of a subclass object to a super-class variable without casting, what…
A: Let us see the answer,
Q: Because a data warehouse is too large for business intelligence, a data mart is preferable to a data…
A: Justification: A data warehouse is a sort of data management system that is intended to facilitate…
Q: What does privacy mean in the context of information security? Information technology
A: Introduction: The term "security" refers to the protection of data, whereas "privacy" refers to the…
Q: What five graphical data properties does data visualization use to convey a story?
A:
Q: Create an ordered, rooted tree that represents the infix form of the following equation. Then write…
A:
Q: Discuss the architecture of Hopfield neural network with an illustration application algorithm. Also…
A: Solution A Hopefield neural network is a type of recurrent artificial neural network, which was…
Q: Why is it required to provide a base case for every recursive function?
A: Introduction Why is it required to provide a base case for every recursive function?
Q: What is the underlying principle of using a prototype method while developing a software product?
A: When constructing a system, prototyping is creating, evaluating, and tweaking a prototype until an…
Q: When you invoke a method on an object instance, the version of the method that will be executed will…
A: True
Q: SOQL Assignment Salesforce: You have to write a SOQL query in which we have to find out all the 1000…
A: Use the Salesforce Object Query Language (SOQL) to search your organization’s Salesforce data for…
Q: What types of timing issues, such as signal delay, may arise during the testing of the sequential…
A: What types of timing issues, such as signal delay, may arise during the testing of the sequential…
Q: In Java, code a program that rolls a dice 100,000 times and prints out the result of how many 3, 4,…
A: INTRODUCTION: Here we need to write a code in java that rolls a dice 100,000 times and prints out…
Q: you’re going to be creating C++ a Heap Sorter. It should be able to take input (using CIN), place it…
A: A binary tree can find the children and parent of any node If the index of any element in array is…
Q: 7.9 LAB: Sorting TV Shows (dictionaries and lists) Write a program that first reads in the name of…
A: As No Programming Language is Given. Doing it in Python Programming.
Q: task7.c Compare 2 strings function cmp will print out > if s1 is "bigger" than s2, #include void…
A: We can use int asc = (int)'a'; to convert char to ascii values. count1 and count2 shound be used to…
Q: Software engineering Short answer Why Speech recognition is difficult to implement in real-time…
A: Introduction: Speech recognition is the process of recognising any sound using software and then…
Q: Is it true that one of the key principles of continuous delivery, Ajail, contradicts the software's…
A: Introduction: The quality of the software is one of the fundamental concepts of continuous delivery,…
Q: In what sense could software process model be described as “waterfall
A: There are various types of software process models and they have their own approach. Waterfall is…
Q: Q1/Write a C++ program to find the nearest integer to a real positive number. The program should…
A: The round() function is used to round off the double, float or long double value passed to it as a…
Q: When you invoke a method on an object instance, the version of the method that will be executed will…
A: Find the answer with explanation given as below :
Q: List and briefly discuss three methods an identity thief can use to steal your personal information.
A: Introduction: Among the information that could be compromised are your name and address, credit card…
Q: ode in Prolog. Do not use in built libraries. Implement the following relation to get a vector…
A: Input : Two vectors. Output : Element wise product of two vectors.
Q: Depending on X which is the last digit of your student number, implement the following function F by…
A:
Q: 3. The table below represents five lines from a cache that uses fully associative mapping with a…
A: Mapping Combinatorial: This indicates that perhaps the phrase id bits are being utilized to…
Q: 2. What are the advantages of using exception
A: In computing and computer programming, exception handling is the process of answering the event of…
Q: can I know the pseudocode and flowchart for this programm..thank you
A: In the question, we are asked to write a pseudo code and flow chart of the given code. Given Code:…
Q: List the nine major components of a typical database environment.
A: Introduction: A typical database setup consists of a number of critical components. There are nine…
Step by step
Solved in 2 steps

- This problem exercises the basic concepts of game playing, using tic-tac-toe (noughtsand crosses) as an example. We define Xn as the number of rows, columns, or diagonals with exactly n X’s and no O’s. Similarly, On is the number of rows, columns, or diagonals with just n O’s. The utility function assigns +1 to any position with X3 = 1 and −1 to any position with O3 = 1. All other terminal positions have utility 0. For nonterminal positions, we use a linear evaluation function defined as Eval (s) = 3X2(s)+X1(s)−(3O2(s)+O1(s))."Mark on your tree the evaluations of all the positions at depth 2."Suppose that a manufacturing company builds n different types of robots, sayrobots 1, 2, . . . , n. These robots are made from a common set of m types of materials, saymaterials 1, 2, . . . , m. The company has only a limited supply of materials for each year,the amount of materials 1, 2, . . . , m are limited by the numbers b1, b2, . . . , bm, respectively.Building robot i requires an aij amount from material j. For example, building robot 1requires a11 from material 1, a12 from material 2, etc. Suppose the profit made by sellingrobot i is pi. Write an integer linear program for maximizing the annual profit for thecompany(i) Describe Banker’s algorithm for deadlock avoidance with supporting example Consider a computer system with has four identical units of a resource R. There are three processes each with a maximum claim of two units of resource R. Processes can request these resources in anyway, that is, two in one shot or one by one. The system always satisfies a request a request for a resource if enough resources are available. If the process doesn’t request any other kind of resource, show that the system never deadlock Give a solution for the following synchronization problem using semaphores Producer- Consumer Problem Readers- Writers Problem List out the issues in preprocessor scheduling that causes performance degradation in multiprocessor systems
- A firm is considering projects A, B, . . . , H. Using binary variables x_a, ..., x_h and linear constraints, model the following conditions on the projects to be undertaken. At most one of A,B,...,H. Exactly two of A,B,...,H. If A then B. If A then not B. If not A then B. If A then B and C. If A then B, and if B then A. If A then B or C. If B or C then A. If B and C then A. If two or more of B,C,D,E then A. If m or more than n projects B,...,H then A.Consider the following computation problem in two variables Plus: Input -14 <= x <= 28, x ∈ Z; -10 <= y <= 32, y∈ Z Output the integer x+y-7 and the following partition of the input domains: Ax = {[-14,-1], [0,10], [11,18]} for the variable x Ay = {[-10,12], [13, 32]} for the variable y Consider the following test suite: S: Test case x y Expected result T1 -5 5 -7 T2 5 5 3 T3 15 15 23 Say what holds for S: Consider the following computation problem in two variables Plus: Input -14 <= x <= 28, x ∈ Z; -10 <= y <= 32, y∈ Z Output the integer x+y-7 and the following partition of the input domains: Ax = {[-14,-1], [0,10], [11,18]} for the variable x Ay = {[-10,12], [13, 32]} for the variable y Consider the following test suite: S: Test case x y Expected result T1 -5 5 -7 T2 5 5 3 T3 15 15 23 Say what holds for S: a) It has more test…Consider the following Job Scheduling problem. We have one machine and a setof n jobs {1, 2, . . . , n} to run on this machine, one at a time. Each job has a start time sifinish time fi and profit pi where 0 ≤ si < fi < ∞ and pi > 0. Two jobs i and j are compatible if the intervals [si, fi)and [sj , fj ) do not overlap. The goal is to find a set A of mutually compatible jobs with the maximumtotal profit, i.e.,P j∈A pj is maximized.Consider the following two greedy choices. For each one, determine whether it is a “safe” greedy choicefor this Job Scheduling problem. If your answer is yes, prove the “Greedy-choice property”. If your answeris no, please give a counterexample and show that the greedy choice will not lead to an optimal solution. a.Greedy choice 1: Always select a job with the earliest finish time that is compatible with allpreviously selected activities.b.Greedy choice 2: Always select a job with the highest profit per time unit (i.e., pi/(fi − si))that is…
- A library must build shelving to shelve 200 4-inch high books, 150 8-inch high books, 300 10-inch high books and 180 12-inch high books. Each book is 0.5 inch thick. The library has several ways to store the books. For example, an 8-inch high shelf may be built to store all books of height less than or equal to 8 inches, and a 12-inch high shelf may be built for the 12-inch books. Alternatively, a 12-inch high shelf might be built to store all books. The library believes it costs $2,300 to build a shelf and that a cost of $5 per square inch is incurred for book storage. (Assume that the area required to store a book is given by height of storage area times book’s thickness.) Formulate and solve a shortest-path problem that could be used to help the library determine how to shelve the books at minimum cost. (Hint: Have nodes 0, 4, 8, 10 and 12, with cij being the total cost of shelving all books of height >i and ≤ j on a single shelf.)Consider the following snapshot of a system: Allocation Max Available A B C D A B C D A B C D P0 2 0 0 1 4 2 1 2 3 3 2 1 P1 3 1 2 1 5 2 5 2 P2 2 1 0 3 2 3 1 6 P3 1 3 1 2 1 4 2 4 P4 1 4 3 2 3 6 6 5 Answer the following questions using the banker’s algorithm: a. Illustrate that the system is in a safe state by demonstrating an order in which the processes may complete. b. If a request from process P1 arrives for (1, 1, 0, 0), can the request be granted immediately? c. If a request from process P4 arrives for (0, 0, 2, 0), can the request be granted immediately?Consider the following snapshot of a system: ALLOCATION MAX AVAILABLE A B C D A B C D A B C D P0 3 2 1 4 3 4 2 7 4 4 3 1 P1 2 5 4 3 4 7 7 6 P2 3 1 1 2 5 3 2 3 P3 2 4 2 3 2 5 3 5 P4 4 2 3 2 6 3 6 3 Answer the following questions using the banker’s algorithm: Illustrate that the system is in a safe state by demonstrating an order in which the processes may complete. If a request from process P4 arrives for (2,2,1,1), can the request be granted immediately? If a request from process P1 arrives for (1,1,3,1), can the request be granted immediately?
- Consider a computer system to which two types ofcomputer jobs are submitted. The mean time to run eachtype of job is m1. The interarrival times for each type of jobare exponential, with an average of li type i jobs arrivingeach hour. Consider the following three situations. a Type 1 jobs have priority over type 2 jobs, and pre-emption is allowed. b Type 1 jobs have priority over type 2 jobs, and nopreemption is allowed.c All jobs are serviced on a FCFS basis.Under which system are type 1 jobs best off? Worst off?Answer the same questions for type 2 jobs.Problem1Given a value `value`, if we want to make change for `value` cents, and we have infinitesupply of each of coins = {S1, S2, .. , Sm} valued `coins`, how many ways can we make the change?The order of `coins` doesn't matter.For example, for `value` = 4 and `coins` = [1, 2, 3], there are four solutions:[1, 1, 1, 1], [1, 1, 2], [2, 2], [1, 3].So output should be 4. For `value` = 10 and `coins` = [2, 5, 3, 6], there are five solutions: [2, 2, 2, 2, 2], [2, 2, 3, 3], [2, 2, 6], [2, 3, 5] and [5, 5].So the output should be 5. Time complexity: O(n * m) where n is the `value` and m is the number of `coins`Space complexity: O(n)""" def count(coins, value): """ Find number of combination of `coins` that adds upp to `value` Keyword arguments: coins -- int[] value -- int """ # initialize dp array and set base case as 1 dp_array = [1] + [0] * value.. (+.The motorway management perceives that the waiting time computed in (a) above is not acceptable and it wishes to reduce it, first, by adding an extra tollbooth assistant to help improve the service rate to 250 motorists every 8-hour-day. The tollbooth attendant will be paid a monthly salary of GH¢400. The second option is that management can add a toll-operated machine which will cost GH¢3,000 and this amount is a free gift from the Minister. This option will reduce the arrival rate to 35 motorists every 2 hours. However, management will have to pay the operator who will man the toll-operated machine a monthly salary of GH¢550. Whichever option management adopts; they avoid lost sales of GH¢1,200.00 per month for every minute that average waiting time is reduced. Advise management which option it must adopt?

