Transform the ERD below to a relational model using the text-based form. STORAGE SID Location & Phone Number Capacity ITEM no Brand Type Release Date Provide your answer in the format given below. Table_Name(Column1, Colump2, Column3,...) Note: Use solid line) to indicate the primary keys and use dash line (- foreign keys. -) to indicate the
Transform the ERD below to a relational model using the text-based form. STORAGE SID Location & Phone Number Capacity ITEM no Brand Type Release Date Provide your answer in the format given below. Table_Name(Column1, Colump2, Column3,...) Note: Use solid line) to indicate the primary keys and use dash line (- foreign keys. -) to indicate the
Chapter3: Creating Tables
Section: Chapter Questions
Problem 7SCG: The SERVICE_REQUEST table uses the CHAR data type for the DESCRIPTION and STATUS fields. Is there an...
Related questions
Question
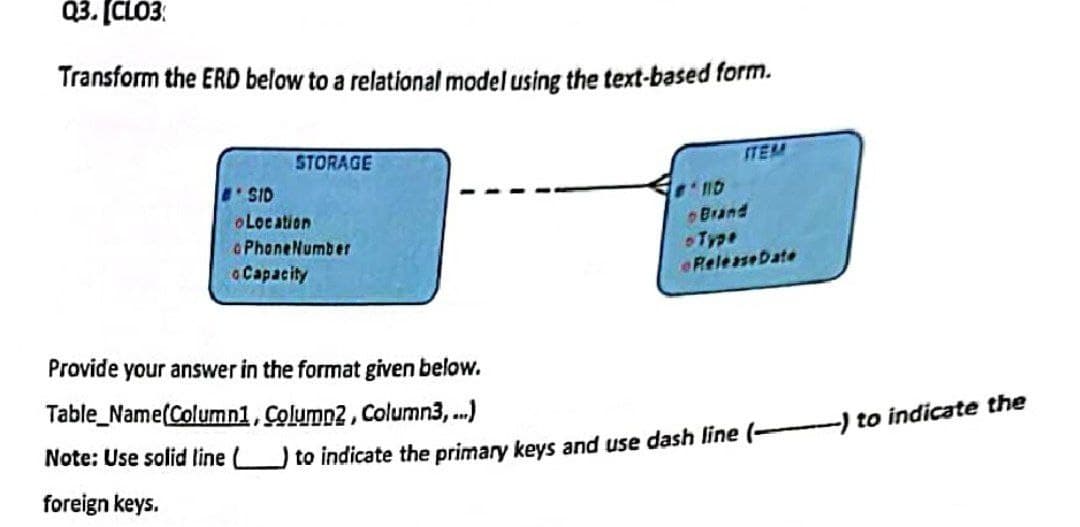
Transcribed Image Text:Q3. [CLO3:
Transform the ERD below to a relational model using the text-based form.
STORAGE
SID
Location
Phone Number
Capacity
Provide your answer in the format given below.
Table_Name(Column1, Colump2, Column3,...)
Note: Use solid line L
foreign keys.
ITEM
ND
Brand
- Type
Release Date
to indicate the primary keys and use dash line (-
-) to indicate the
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage

A Guide to SQL
Computer Science
ISBN:
9781111527273
Author:
Philip J. Pratt
Publisher:
Course Technology Ptr

Np Ms Office 365/Excel 2016 I Ntermed
Computer Science
ISBN:
9781337508841
Author:
Carey
Publisher:
Cengage