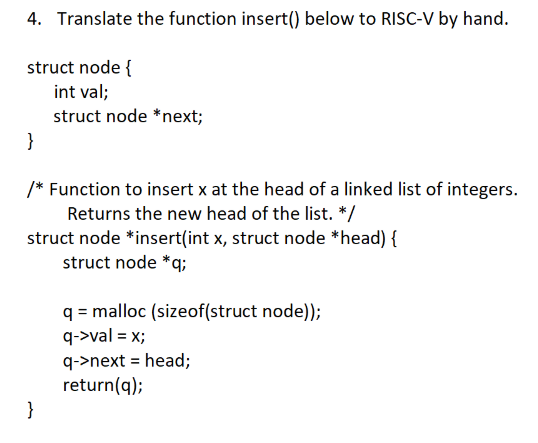
Translate the function insert() below to RISC-V by hand.
Q: System A takes 50 seconds to run a program. The same program takes 30 seconds to run on a new syste...
A: System A takes 50 seconds to run a program. The same program takes 30 seconds to run on a new system...
Q: Write code that outputs variable numMonths as follows. End with a newline. Ex: If the input is: 3 ...
A: Write code that outputs variable numMonths as follows. End with a newline. Ex: If the input is: 3 th...
Q: 2. A friend needs to drive from City X to City l and would like to find the shortest route between t...
A: Here, I have to find the minimum distance from city X to city I.
Q: 5. Suppose in a multiprocessing system, four threads namely T1, T2, T3, and T4 are running with four...
A: About user level and kernel level: =================================================================...
Q: How are centralized and parallel/distributed databases different?
A: In Step 2, I have provided difference between centralized databases and distributed databa...
Q: Please do it with regular expression. Don't use loops please. Do fast, I have no time left Write a j...
A: Required:- Please do it with regular expression. Don't use loops, please. Do fast, I have no time l...
Q: mary storage.
A: given - Create a definition for primary storage.
Q: The importance of effective security policies, as well as their constant enforcement, has long been ...
A: Introduction: It enables the business to protect its information assets against illegal disclosure, ...
Q: programme counter
A: In step 2, I have provided answer.
Q: ADD [R1], R2, [R3]; Here [R1] and [R3] indicate memory locations pointed by R1 and R3 register respe...
A: The Answer is
Q: the network engineer, you are asked to design an IP subnet plan that calls for 3subnets. The largest...
A: So, According to the given question ,To have a minimum of 52 hosts we need Atleast 6 bits in hos...
Q: Define the number of CPU clock cycles.
A: CPU clock cycles define below :
Q: Consider the graph in Figure 1. Unless otherwise indicated, always visit adjacent nodes in alphabeti...
A:
Q: What kind of worries and challenges arise from the use of an unintegrated information system?
A: kind of worries and challenges arise from the use of an unintegrated information system -:- Computer...
Q: The Pinewood Derby involves racing Derby cards down multiple lanes and calculating the average time ...
A: racers=int(input("Enter number of racers: ")) times=[] for i in range(racers): time=int(input("Enter...
Q: Create a class calculate that uses two separate functions:-a function to multiply two float numbers ...
A: Introduction: The program's programming technique is provided by: Including header files, the class ...
Q: Create a program that calculates the interest on a loan. Console Interest Calculator Enter loan amou...
A: from decimal import Decimal def calculate(): loan_amount = float(input("Enter loan amount: ")) ...
Q: What function did we use to display a single row function in database? Scalar function or Vector Fun...
A: We are only obligated to react to one inquiry at a time, according to our standards. Please submit a...
Q: estion 42: Return whether a string consists of a single letter In the function below, return True if...
A: #FUNCTION DEFINATION ACCORDING TO INFORMATIONdef is_a_single_letter(string_arg):# CHECKS IF THE STRI...
Q: Write a program to print following data
A: All the programs are written in Python: Program 1: Print the requirement print(''' -----------...
Q: Following the development and testing of individual software modules, they must be combined and test...
A: Introduction: Software development refers to computer programming, which is the process of writing a...
Q: Encode the following ARM assembly instruction to ARM machine language code. ORRS r4,r5,r6,ASR #6 Ox
A: The solution is given below for the above-given question:
Q: Why is it necessary for the maximum packet lifetime to be large enough to ensure that not only the p...
A: Introduction: TCP - Transmission Control Protocol is a network protocol that connects two hosts and ...
Q: rite at least 10 requirements for a calculator. Make sure you use the word SHALL in each requirement...
A: here we have to write at least 10 requirements for a calculator.
Q: For what reason is it a good idea to hash a password that is saved in a file rather than encrypting ...
A: It a good idea to hash a password that is saved in a file rather than encrypting that password. We w...
Q: Explain excel and give a tip increase skills in Excel.
A: It is a software program created by Microsoft that uses spreadsheets to organize numbers and ...
Q: Show how to create a view tot credits (year, num credits) that returns the total amount of credits t...
A: Introduction: The query below is used to calculate the total number of credits earned by students in...
Q: What are the distinctions between EBS and Instance Store?
A: Amazon Elastic Container Service (Amazon ECS) is a cloud-based managed container runtime that makes ...
Q: 1.Define a JavaScript function that takes a parameter and prints the datatype of that parameter in t...
A: Define a JavaScript function that takes a parameter and prints the datatype of that parameter in the...
Q: What exactly is the internet, and where did it come from?
A: INTERNET: The Internet is a vast network that connects computers all over the world. Through...
Q: Write a program that takes website names as keyboard input until the user types the word stop and co...
A: Given :- Write a program that takes website names as keyboard input until the user types the word st...
Q: what is the coding for panel data for fixed effects in stata?
A: use xtset industryvar in Stata to indicate that you want fixed effects for each unique value of ind...
Q: Write a java program that will take a text as input and convert the first letter of each word into ...
A: Java is a high-level, class-based, object-oriented programming language that is designed to have as ...
Q: how Linux may be used in several elements of rocket technology
A: Linux is an open source operating system that is highly secured.
Q: Define the term "superscalar."
A: SuperScalar : Superscalar is a form of ComputerArchitecture. Except in low budge processors , it is...
Q: Modify the below existing codes to print the output in Python. Explain the changes made to the code...
A: Below i have given the code:
Q: Give a DFA accepting all strings over (0,1} consisting of an odd number of repetitions of the string...
A: According to the question we need to answer: Give a DFA accepting all strings over (0,1} consistin...
Q: te an EBNF description for a Java class definition header statement te a BNF description of the Bool...
A: 1.A Java class definition header statement <class_head> ® {<modifier>} class <id>...
Q: In an RPC-like protocol, where numerous requests can be active at the same time and responses can be...
A: Introduction: Calling a Remote Procedure (RPC): Programmatically, Remote Procedure Call (RPC) is how...
Q: Write a program that reads in hours, minutes, as input, and outputs the time in minutes only.
A: The language i used is C++. I explained the program in comments of the code and also attached the sc...
Q: Give examples of five general responsibilities of a database administrator.
A: A DBA is frequently involved in the initial setup of a modern Oracle, SQL Server, or other database....
Q: You write "call puts wrt ..plt" and assemble, link, and run the code. a. What does the call point to...
A: SUMMARY: -Hence, we discussed all the points
Q: In Windows 7, how does the user threads transfer to the kernel thread? Is it a one-on-one model, a m...
A: Introduction: So, with Win 7, a user needs first to understand thread, thread types, and thread mode...
Q: Personal computer should be defined.
A: Answer:
Q: Display the list of only leap years from years 2000 to 2025. If year/4 is equal to 0 and years/100 n...
A: #include <iostream>using namespace std;int main(){ int year; for(year=2000;year<=2025...
Q: write a linear integer programming of the below problem Formulate the following manpower planning p...
A: C++ Code: #include<bits/stdc++.h> using namespace std; int main() { int required_saf[15]; in i...
Q: a relational datab
A: given - Why would we pick a non-BCNF architecture for a relational database?
Q: Explain what distributed databases and distributed processes are and give at least one example of ea...
A: A computerized data-keeping system is all that a database management system (or DBMS) really is. The...
Q: How can we fix this python program: def number_is_odd(num): if num % 2 == 1: ...
A: Logic: here only odd number case is returned, In case if a user enters even number , nothing is ret...
Q: Write a java program to check if a list of integers contains only odd number. Please do it using par...
A: Required:- Write a java program to check if a list of integers contains only odd numbers. Please do ...
Translate the function insert() below to RISC-V by hand.
Step by step
Solved in 2 steps

- In C++, Consider a singly linked list where each node contains two fields – integer dataand node type pointer next. The head pointer of the list, a position, and a valueof data is given. You have to insert a node with the given value at the givenposition. You have to consider any position including first or last. You have toImplement an insert operation as per the above specification.1-Write a C program to show operations on a singly linked where each node consists of integers. (a) Insert (At beginning, At end) (b) Delet (At beginning, At end) (c) Search (d)reverse (e) Print middle element 2 Write a C program using dynamic variable & pointers to construct a singly linked list consisting of the following information in each node. Student id (integer), student name (character string) & semester (integer). 3 Write a C program using dynamic variables & pointers to construct an ordered (ascending) singly linked list based on the rank of the student, where each node consists of the following information student id( integer) student name(character), rank(integer).Please code this in Java Or C or C++ Given two numbers represented by a linked list, where each node contains a single digit. The digits are stored in reverse order, such that the 1's digit is at the head of the list. Write a function that adds the two numbers and return the sum as linked list: Example : Input : (7-> 1 -> 6) + (5-> 9-> 2). That is 617 + 295 = 912 Output : 2-> 1 -> 9 Expected time complexity : O(m+n), where m and n are no. of nodes in first and second linked list respectively.
- This is assignment used C++. Develop a linked-list processing function, IsolateTargetSoloAsTail, to process a linked list as follows. ● If a target cannot be found on the given list, a new node containing the target is created and added to the list's end (made the new tail node). ► This includes the case where the given list is empty, in which the new tail node added is also the new head node. (This is so because the only node in a 1-node list is the list's head and tail node.) ● If the target appears only once on the given list, the target-matching node is moved to the list's end (made the new tail node). ► Nothing needs to be done if the target-matching node is already the tail node (of the given list). ● If the target appears multiple times on the given list, the first target-matching node is moved to the list's end (made the new tail node), and all other target-matching nodes are to be deleted from the list. ► Note that although…You are to work to develop a linked-list processing function IsolateTargetSoloAsTail that is to process a linked list as follows. ● If target cannot be found on the given list, a new node containing target is created and added to the end (made the new tail node) of the list. ► This includes the case where the given list is empty, in which case the new tail node added is also new head node. (This is so because the only node in a 1-node list is both the head and tail node of the list.) ● If target appears only once on the given list, the target-matching node is moved to the end (made the new tail node) of the list. ► In case the target-matching node is already the tail node (of the given list), then nothing needs to be done. ● If target appears multiple times on the given list, the first target-matching node is moved to the end (made the new tail node) of the list, and all other target-matching nodes are to be deleted from the list. ►…Write a function that changes the places of the first and second nodes of a linked list. I.e. the First node will become the second node, and the second node will become the first node. THE FUNCTION WILL NOT EXCHANGE DATA, IT WILL CHANGE LINKS.
- From page 147, #25: Design and implement an experiment that will compare the performance of a Python list with a list implmentd as a linked listWrite a C program to perform following operations on Single LinkedList: Create() - Create a Single Linked list with 8 Nodes Insert() - Insert a node in the ending OddDisplay () - Display only those Nodes which has Odd Value and sum it Count() - Count the length of the Linkedlist Note: It must be a menu-driven program and User defined functions must be there for all the functionalities.Write programs for the following operations on linked list in python.a. To search for an element in a single linked list.b. To count the occurrence of an element in a single linked list.c. To implement stack operations using single linked list.d. To implement queue operations using single linked list.e. To check whether two single lists are same or not.f. To count the occurrences of all the elements in a single linked list.g. To find the smallest element in a double linked list
- Suppose a node of a linked list is defined as follows in your program: typedef struct{ char data; struct Node* link; } Node; Write the definitions of two functions (i) Node* pop(Node* top) – which removes the top element of the stack, and (ii) bool compare(Node* topA, Node* topB) - which returns true if the both stacks have identical data. The function returns false if the data in both stacks are not identical. In the function definitions, top, topA, and topB point the top elements of corresponding stacks. You must use the following function definitions in your answer. The peek function has already been defined. You need to write the definition of pop and compare functions. You are not allowed to modify the parameters and/or return types of the functions. Node* pop(Node* top){ //write the function definition } char peek(Node* top){ return top->data; } bool compare(Node* topA, Node* topB){ //write the function definition } Write the time complexity in Big-O notation…Short answer: Answer the following in your own words: 1) Your friend says they implemented a stack as a linked list with reference pointers to both a head and the tail node (i.e. they implemented a stack as a double endedlinked list). They said this significantly improved the performance for all functions (push, pop, search, and update). Are they correct? Why or why not?1-Write a C++ Function that returns the data of the middle node in a linked list and in case the linked list contains only one node return the data inside this node and returns the sum of all the nodes in linked list and returns the maximum data value in the linked list











