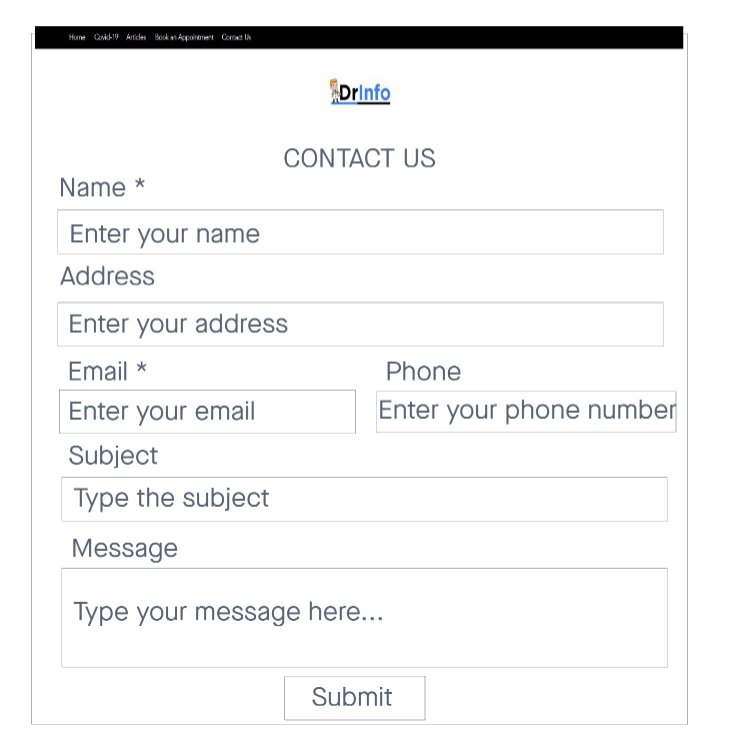
Use HTML CSS please.
Q: How can I compute the interpolating polynomial p5 with the function "newinterp" as described in this…
A: This is very simple. The previously written code is completely wrong whoever has written it. Let's…
Q: What are the four most important characteristics that may be categorized in software development? Is…
A: Software development processes - It defines all the steps involved in the development of software…
Q: Explain why a system requires a stalemate.
A: Introduction: Deadlock in the system is required by the following conditions: - Circular Wait…
Q: 11. You have three identical prizes to give away and a pool of 10 finalists. The finalists are…
A: Here is the approach : Create the list to store the random numbers Create the loop to run till the…
Q: Why do transport protocols such as HTTP, FTP, SMTP, and POP3 use TCP as opposed to UDP?
A: The application data may also be received over the HTTP, FTP, SMTP, and POP3 protocols in the…
Q: Algorithm for Check Schedulability With Locks Data: Periodic program P with locks, WCET estimates Ci…
A: Data: Periodic program P with locks, WCET estimates Ci for τi and Ci l,k for lock block Bi…
Q: ry along with css else downvote fir incorrect plz.
A: I have written code below Of CSS and Jquery:
Q: n is in theta(n) true or false
A: Here in this question we have given a statement and we have to comment weather it is true or false.
Q: public static void simpleLoop(int total) { String tmp = for (int x = 0; x< total; x++) { (x + ",");…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: Why is UDP not utilized in any of the preceding protocols?
A: Introduction: HTTP, FTP, SMTP, and POP3 all employ TCP rather than UDP because it provides a more…
Q: What are the key differences between designing network apps and other kinds of applications?
A: Introduction: OTHER SOFTWARE PROGRAMS: Software systems and software applications are examples of…
Q: How do conventional and web-based software development methodologies vary with regard to the…
A: Software Acquisition: In a conventional or web-based business, a software interface with many…
Q: What are the most effective techniques for firewall administration? Explain.
A: Firewall administration: The term "firewall" refers to a security system that guards a computer…
Q: draw turing machine Contains the state of reject and accept ,Ex; L=b(a∪b)*a
A: The turing machine is 7-tuple (Q, T, B, ∑, δ, q0, F) Q is a finite set of states T is the tape…
Q: How do you define database security? A complicated administrative procedure governed the physical…
A: Database security considerations include using information security measures to secure database…
Q: What is a disaster recovery plan, and why is it essential for a business to have one? How do you…
A: A disaster recovery plan (DRP) is a conventional document made by an association that contains…
Q: Return a list containing all pairs of distinct elements that satisfy the function fn. We say the…
A: Hi please find the solution below and I hope it is helpful for you.
Q: Please write a detailed code in C++ and also provide some explanations as much as you can, thanks.…
A: Here is the c++ code of the above problem. See below step for code and output.
Q: 2. Write a recursive definition of i- j (integer subtraction), where j> 0 and i>j. Define the…
A: Here is the java code. See below step for code
Q: You wash ashore an island with two types of people, knights who only speak the truth, and knaves,…
A: Question: You wash ashore on an island with two types of people, knights who only speak the truth,…
Q: Recognize and explain some of the challenges associated with developing an information system…
A: A formal, sociotechnical, and hierarchical system that is meant to acquire, cycle, store, and…
Q: Consider a simple in-order processor with the following characteristics: Consists of a pipeline…
A: A sequence is an arranged rundown of something. Successive execution implies that each order in a…
Q: take a look at two classes in JavaScript that implement the same method but with two different…
A: JavaScript (often abbreviated to JS) is a programming language and one of the core technologies of…
Q: Train reservation and ticketing system assessment has been assigned to you. How will you assure the…
A: Given: The system development life cycle defines project development phases. Software development…
Q: In order to answer this question, we must define "jump drive."
A: A USB jump drive is a data storage device that includes flash memory with an integrated USB…
Q: List the issues that arise while establishing the information system architecture needed to serve…
A: Introduction: Make a list of the challenges involved in developing an IT infrastructure to support…
Q: (log(n))2 is in O(log n2) true or false?
A: Here in this question we have given a statement and we have asked weather this is true or false.…
Q: What are the differences between Computer Science and Computer Engineering?
A: Computer science vs computer engineering: Software engineering belongs to the same field as computer…
Q: Data structures dict_from_string(dict_str:str)->dict This function will be given a single parameter,…
A: Python:- The programming language Python is versatile, effective, and general-purpose. Short and…
Q: What are the numerous methods for acquiring software, such as traditional software creation and…
A: Introduction: Describe conventional and web-based software acquisition strategies. Traditional or…
Q: What is a disaster recovery plan, and why is it essential for a business to have one? How do you…
A: Start: A formal document known as a disaster recovery plan contains comprehensive instructions and a…
Q: Assembly language programming for the microprocessor 8085 is based on what? Could this be classified…
A: The microprocessor 8085 assembly language programming is based on this basic logic: Writing the…
Q: Why are reviews and inspections of software quality conducted as they are?
A: Your answer is given below. Introduction :- An objective of a review is to detect and fix flaws as…
Q: Hi what is the expression for X
A: Expression of x would be:
Q: First, write a Java method merge that takes as parameter a non-empty double array representing…
A: Code: import java.io.*; import java.util.*; public class MergeSalary { private static Scanner…
Q: 10 11 12 13 14 15 22 23 24 P 1 KB VPN bits Number of VPO bits PPN bits PPO bits
A: The answer is
Q: What precisely is a pile? "A heap operation has a temporal complexity of O(nlogn)" - give an…
A: Heap: When it comes to trees, a heap is in a class of its own, particularly when it comes to binary…
Q: What are the many firewall types and how do you characterize them?
A: FIREWALL TYPES:- Protocol filtering Firewalls Gateways at the circuit level Gateways at the…
Q: What techniques are used to enhance the quality of software?
A: Software Quality: The suitability of a piece of software for a certain purpose defines its quality.…
Q: what are the Common applications of machine learning?
A: Because machine learning goes so neatly hand-in-hand with large datasets, many common machine…
Q: What precisely is a pile? "A heap operation has a temporal complexity of O(nlogn)" - give an…
A: Heap is a unique kind of tree, more especially a binary tree. In terms of structure, a heap is…
Q: After a software product has been released, it may be changed for mistake correction, performance…
A: Complete the system shown below: After delivery, a software product may be modified to fix bugs,…
Q: Discuss recent developments in the field of information management, the evolution of business…
A: Answer:
Q: How can a firewall be operated most efficiently? Explain.
A: Define: A firewall protects a computer against unwanted access. In today's PC world, intelligent…
Q: C++ Write a program that simulates the minute-by-minute operation of a checkout line, such as one…
A: The complete answer in C++ programming Language is below:
Q: Describe some of the challenges you will have in establishing a system to support this new service.…
A: The above question is solved in step 2 :-
Q: What are the most effective methods for keeping a firewall operational?
A: Introduction: Even though major businesses have made tremendous improvements to network perimeter…
Q: What does the term database integrity mean? Enumerate all Oracle limitations required to maintain…
A: Database: The two main types or categories of databases are relational or sequence databases and…
Q: It is essential to understand what system image recovery is.
A: In this question we need to explain whether understanding system image recovery is essential or not.
Q: What are the four most essential traits for software development success? Which of the following…
A: Introduction: According to IBM Research, software development involves creating, designing,…
Use HTML CSS please.
Step by step
Solved in 3 steps with 1 images

- %)/20 @ @ (ol S ETC S (&) 32 @ docs.google.com @i laboratory's question : write c++ program find fib(x)+y if x in class A and y in class B using friend function * Your answer Jloosl ode a1 LAY oo ST way * (@™ Back Next Never submit passwords through Google Forms. This form was created inside of Imam Al-Kadhum College (IKC). Report AbuseCompulsory Task 2Follow these steps:● Using one of the patterns described, write the code needed to create 3student objects. Each student object should have a describe() methodthat returns a string that describes the student. Each student will bedescribed using a full name and a student number. The rest of thedescription will be built up based on the student’s activity at HyperionDev.For example, the description should explain which Bootcamps thestudent has registered for and which level of the Bootcamp has beencompleted.Below is sample output:Student 1: Susan Smith:- Registered for the Software Engineering Bootcamp- Completed level 1Student 2: Michael Jansen:- Registered for the Web Development Bootcamp- Completed level 1- Completed level 2- Completed level 3- Registered for the Software Engineering BootcampStudent 3: Saoirse Ronan- Registered for the Web Development Bootcamp- Completed level 1- Completed level 2- Completed level 3- Registered for the Software Engineering Bootcamp-…AlgorithmDeclare a variable named balance with initial value of 300Declare a constant names INTERST_RATE with value 0.03Declare a variable named interest, multiply balance and INTERST_RATEand assign the result to interest.Display interest to console.
- Cide_Task Programming Language and Advancements▪ C# Programming Language.▪ Visual Studio 2019. Fabricate a strategy called Scramble to get a string and return another string.The technique will be a static.Fabricate a strategy called Unscramble to return unique string.The encryption technique will be an extremely straightforward one: to scramble add 1 to eachcharacter and to unscramble take away 1 to each person.Note: we don't have to make any object of type Encrypter..#4. Task Programming Language and Technologies▪ C# Programming Language.▪ Visual Studio 2019. Build a method called Encrypt to receive a string and return another string.The method will be a static.Build a method called Decrypt to return original string.The encryption method will be a very simple one: to encrypt add 1 to eachcharacter and to decrypt subtract 1 to each character.Note: we do not need to create any object of type Encrypter..{python language}Dan’s recently announced that he’s teaching n top-secret courses next semester. Instead of enrolling in them through ACORN, students need to email Dan to express their interests. These courses are numbered from 1 to n in some arbitrary order.In particular, if a student named s is interested in taking a course c, they need to send an email to Dan containing the message c s.Notethatifastudentis interested in taking multiple courses, they need to send multiple emails, one per course.Upon receivinga message c s,Danl ooks at the list of students already enrolled in course c. If there’s already a student on the list whose name is too similar to s, Dan assumes s is the same student and ignores the message. Otherwise, he enrolls s in the course.Dan considers two names too similar if and only if they have the same length and differ in at most one letter (note that “a” and “A” are considered the same letter). For example, “Josh” and “Josh” are too similar. “Sam” and “CaM” are…
- Q4: Colouring Book Having spent the last couple of hours grading assignments, I decide it’s time for a break. I take out my favourite colouring book, turn to a random page I haven’t coloured in yet, and lay it on my desk. I then take out all my n crayons and line them up on the desk (it’s a very long desk). The colour of the ith crayon is a string c[i] (e.g. "blue"). Many of the crayons have the same colour. In fact, no matter how many crayons I have, there are at most 30 distinct colours amongst them. To start colouring, I always take a sublist (see Q1 for a definition) of the crayons laid on the desk and put away the rest (too many options can be overwhelming and can lead to indecision). I take a look at the line art in front of me and wonder, “How many different colours do I need to make this look great? One? Two? Maybe three?”. Now you understand my dilemma and are fully aware of my indecision. You kindly decide to help me out by telling me for every number k, if I were to use…steps involved in making a strong passward Step 1: Write the first name of a cartoon character. sophiaStep 2: Rewrite your cartoon character’s name and add a random number after thename. sophia 2Step 3: Now rewrite the word and number above and add the last name of a historicalfigure after the number. sophia2charles darwinStep 4: Rewrite the words and numbers above and add a phrase you know in anotherlanguage to the end. sophia2charles darwin QUESTION: Did i follow the steps well? did i rewrite as appropriate? please correct my answerInternet Technologies Class.HTMLWrite a script that asks for a user's name and age, then prints the user's name and age on the screen over and over until it loops as many times as the user's age. Security Feature: Do not let users named "Raymond" run this program
- Assume you are working for a company and given the task to build an Email Registration Program. Theemail registration program functions as follows.• Prompt the user four things: first name, last name, security question answer, and birthyear.o Example:Enter first name: LeBronEnter last name: James(Security Question) Favorite car maker: BentleyEnter birth year: 1984• Generate a default Kean email address based on the first name and last name.o The default Kean email address consists of the first letter of the first name, a period, theentire last name all in lower case appended with @kean.edu.o Example: LeBron James → l.james@kean.edu• Generate a default password based on the first name, security question answer, and birthyear.o The default password is a sequence of 3 letters from last name, birthyear, and 3 lettersfrom the security question answer all in upper case.o Example: LeBron, 1984, Bentley → LEB1984BEN• Display the email information with first name, last name, email address, and…Assume you are working for a company and given the task to build an Email Registration Program. Theemail registration program functions as follows.• Prompt the user four things: first name, last name, security question answer, and birthyear.o Example:Enter first name: LeBronEnter last name: James(Security Question) Favorite car maker: BentleyEnter birth year: 1984• Generate a default Kean email address based on the first name and last name.o The default Kean email address consists of the first letter of the first name, a period, theentire last name all in lower case appended with @kean.edu.o Example: LeBron James → l.james@kean.edu• Generate a default password based on the last name, security question answer, and birthyear.o The default password is a sequence of 3 letters from last name, birthyear, and 3 lettersfrom the security question answer all in upper case.o Example: LeBron, 1984, Bentley → LEB1984BEN• Display the email information with first name, last name, email address, and…subject:internet fundamentals and scripting Make a Polling game. A poll has a question, an array of options from which people can choose, and an array with the number of replies for each option. This data is stored in the starter'poll' object below.Your tasks:1. Create a method called 'registerNewAnswer' on the 'poll' object. The method does 2 things:1.1. Display a prompt window for the user to input the number of the selected option. The prompt should look like this:What is your favourite programming language?0: JavaScript1: Python2: Rust3: C++(Write option number)13FINAL EXAM1.2. Based on the input number, update the 'answers' array property. For example, if the option is 3, increase the value at position 3 of the array by 1. Make sure to check if the input is a number and if the number makes sense (e.g., answer 52 wouldn't make sense, right?)2. Call this method whenever the user clicks the "Answer poll" button.3. Create a method 'displayResults' which displays the poll results. The…



