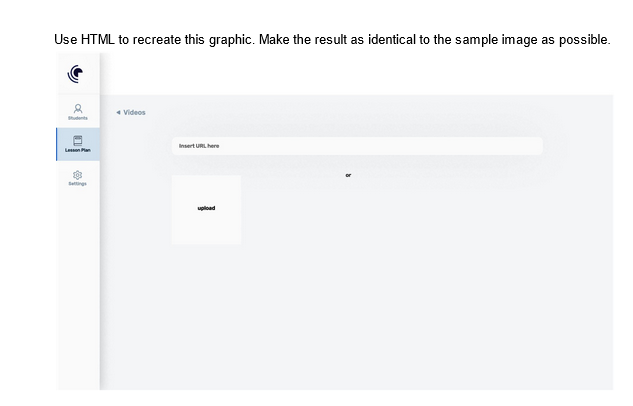
Use HTML to recreate this graphic. Make the result as identical to the sample image as possible. Videos
Q: The terms "digital data" and "digital device" are often used interchangeably.
A: Introduction Digital Data: It is data that is kept in a computer system's memory as a binary series…
Q: This is how you may utilize system analytics to discuss the BYOD movement and its impact on the…
A: Given: Can you explain the Bring Your Own Device (BYOD) trend and discuss the good and bad effects…
Q: How come our method showPrice works with CompactDisc and DvdMovie objects? What can you say about…
A: Dear Student, The answer to your question is given below -
Q: Specify the following for me in great detail: International problems (globalisation in terms of…
A: Globalization: "Globalization may be described as the rising interdependence and interconnection of…
Q: During the software development process, what purpose did software development kits (SDKS) serve?
A: Software development is the process of creating software in accordance with user specifications. The…
Q: 4. Which of these code snippets is the most readable? A B ellipse (x, y, 15, 5); ellipse (x, y,…
A: Find your Answer Below A. The Space between the function name and parenthesis makes it difficult to…
Q: To what extent may the most vital aspects of an OS be summarized?
A: The simplest possible summary of an operating system is that it is a piece of software that is in…
Q: Consider all aspects of a contingency plan. What distinguishes a mobile backup plan from a backup…
A: Introduction Plan for computer backup: A system backup is the a process of backing up a computer…
Q: There are several aspects of firewalls that contribute to network security and protection. Remember…
A: It is necessary to provide an explanation of the function of the firewall with regard to the…
Q: For the given graph below, use the Breadth First Search (BSF) algorithm to visit the vertices and…
A: Answer is given below
Q: You as a network administrator want to protect the network from unauthorized traffic, and for this…
A: Answer: We need to write the which option is the correct among the following so we will see in the…
Q: Graphing tools are used to present data and processes in a comprehensible manner.
A: The following are the three different graphical tools used in data processing modelling: Diagrams of…
Q: Insufficiently integrated information systems generate a multitude of concerns and complications.
A: The reality above is that systems produce a deluge of problems and troubles. Significant problems…
Q: Where are the system journals saved when they are not being manually overwritten?
A: Provided - In what location are the system journals stored by default?' When the "auto" option is…
Q: Which framework is used for software testing?
A: Answer is in step 2 Answer: A Rayleigh model is used whenever there is a need to evaluate the…
Q: When it comes to the testing process, what benefits do you see from using automated tools?
A: 1. The process of creating a set of instructions that tells a computer how to perform a task is…
Q: Discuss the evolution of computer systems and how they have influenced the introduction of…
A: Introduction: Computer systems have developed rapidly as technology has advanced. The development of…
Q: During the software design phase, software engineers define details about the product construction,…
A: According to the information given:- We have to define Unified Modeling Language (UML) with at least…
Q: The elements that affect the network's communication capacity are varied.
A: Important elements that have an impact on how well a network can communicate include: 1) The…
Q: C++ pointer variables are a special kind of data storage. Is its use something you're familiar with?
A: Pointers are variables used to store the address of a variable , of particular data type , i.e. if…
Q: When people say they have a "memory vacuum," what do they mean exactly? What triggers it, and how…
A: Introduction : A "memory vacuum" is used to describe a feeling of forgetting or not being able to…
Q: Why is it beneficial to build operating systems with several layers? Is it worthwhile to put in the…
A: Semantics studies the meaning of words, sentences, and symbols. Semantics has several categories. By…
Q: There are three parts to the von Neumann architecture that need to be defined precisely. How can…
A: Introduction : Von Neumann architecture is a design for computer systems that uses a processing…
Q: For each of the following functions, indicate how much the function’s value will change it its…
A: According to the information given:- We have to define functions, indicate how much the function’s…
Q: How dissimilar are regular and associative memory? Which one is more pricey, and why does it cost…
A: INTRODUCTION: Memory is the location of data that will only be used temporarily. In contrast,…
Q: In the context of manual testing, what exactly does the term "Test Coverage" refer to?
A: Given What does manual testing's test coverage entail? Finding out whether or not our test cases…
Q: For how long have computers been able to run programs?
A: A series of instructions written in a programming language for a computer to follow is referred to…
Q: Strategy for Automation Migration (with a Schematic) with Appropriate Industrial Equipment
A: Automation Migration strategy:- This is the process of moving data between information repositories…
Q: How much does primary storage cost, and how does it compare to secondary storage in terms of…
A: Primary storage, also known as main memory, and secondary storage, also known as peripheral storage,…
Q: Orthogonality arises when the design of an instruction set provides a "backup" instruction for each…
A: The CPU requires the following to function properly: For the programme to function, it must first be…
Q: Describe a real-world CSP, the solution it offered, and how it impacted the local and global…
A: The Answer is in step2
Q: what a data dictionary is for and how it is utilised.
A: 1. A database management system (or DBMS). It is essentially just a computer-based data storage…
Q: What are the advantages and disadvantages of storing data on the cloud? Please share examples of…
A: Storage of clods putting data in the cloud we may access data in the cloud without needing any…
Q: All of them rely on firewalls, which are crucial for network security and cybersecurity. Be careful…
A: Please elaborate on the role that firewalls play as a fundamental component of both network defense…
Q: A brief essay detailing three testing objectives relative to testing maturity is needed.
A: By using a testing maturity model, the software testing process may simultaneously identify its…
Q: Show that if A ⊆ C and B ⊆ D, then A × B ⊆ C × D
A: Here is the explanation regarding the proof.
Q: 8. 9. The statement, "Some musician play instruments" where M(x) is "x is a musician" and I (x) is…
A: In this question we have to answer the following question A. The statement, "Some musician play…
Q: Write a program to read data and save data in the array sewage_amt[100] using GetData function. Find…
A: Create a file called "EX6_1.DAT" in the directory. 123 134 122 128 116 96 83 144 156 128 138 121…
Q: Domain in Microsoft Azure: An Explanation
A: For the solution, please see the next step: Assistance with Domains We can connect to the company's…
Q: Normalization and denormalization are two separate processes that happen in computer science, but…
A: Differentiate Normalization from denormalization. Normalization is the elimination of duplicated…
Q: Write a complete Java program to execute what is asked in each item below: Using a parallel array,…
A: In this question we have to write a complete java program to execute Using a parallel array, Input…
Q: In your view, what does it mean to be safe? It's growing more and more difficult to keep secure in…
A: Given: What exactly does it mean to say that one is secure? What are some of the most pressing…
Q: Are you interested in exploring system authentication and access?
A: Authentication It verifies identification to give system access; verification is performed for…
Q: Is there a way to use the internet for health promotion that actually helps the user? What…
A: Internet connects computers globally. People with Internet access may converse and exchange…
Q: Is it feasible to define the term "intrusion prevention system"?
A: Introduction To decide whether there is an example match, the IPS looks at parcel streams comparable…
Q: Describe the differences between procedural and object-oriented programming languages. How does…
A: The solution to the given question is: Procedural programming languages are based on the idea of a…
Q: In what ways do information systems that are not interconnected generate problems?
A: Information systems have evolved over the times, requiring redefinitions as the new technology have…
Q: What advantages does the deep web give to enterprises reliant on information systems?
A: All information that is stored in independent databases hidden from the online front-ends of portals…
Q: Do C's relational and boolean expressions fare well?
A: Relational Definition: A relational expression is an expression that requires two operands and a…
Q: Detail the key differences between object-oriented and procedural programming languages.
A: Differences between object-oriented and procedural programming languages are: Objects are the…
Step by step
Solved in 3 steps with 1 images

- Recreate the contents of the document below using HTML elements. Document and the picture.How to perfectly aligned the rows and columns as seen at the photo? Please write the following HTML code and where to put it.we need to edit our values to only pad the left side of our paragraphs, and only apply a margin to the bottom of each.write html code for it
- Use HTML to recreate this graphic. Make the result as identical to the sample image as possible.Using HTML5 code, create cart_checkout.html as shown in the below given picture. Fill the checkout form with all necessary details and add a screenshot to your answer. I attached file The CVV should be obscured so that it cannot be read.Write html code and attach screenshot of form
- Need an HTML Code with inlined elements Build this initial home page inside a 2x2 html table. Using the proper table attributes , make the table 800 pixels wide and 500 pixels high. Using html attributes, make the first row 100 pixels high and the first column no more than 200 pixels wide. Tentatively label each cell of the table like this:Add a form on the checkout.html page that takes your name, email, phone number, and a credit card number. Use a regular expression to validate the email, phone number, and credit card. Existing code: checkout.html <html lang="en"> <head> <meta charset="UTF-8"> <meta name="viewport" content="width=device-width, initial-scale=1.0"> <title>Document</title> <style> img { width: 80px; height: auto; } </style> </head> <body> <div id="productsFromCart"> </div> <script> let items = localStorage.getItem("myItems") ? JSON.parse(localStorage.getItem("myItems")) : []; items.forEach((element,index) => { let products = ""; products += "<div id='product" + element.id + "' class='card'>"; products += "<img src='" + element.image + "' />"; products += "<h1>" + element.name + "</h1>"; products += "<p class='price'>" + element.price + "</p>"; products += "<p>" + element.category +…Write HTML5 code that will create the following linked pages. You can use the interface code from the previous exercise.
- make this webpage in html with same colorsWrite html and css for the following using div. Table format should be same as given in table For remarks text box write a CSS style specification rule that would make all unordered lists (<ul> tags) have square bullets and a pink background. Solve this question using VSCODE and paste screenshot of code and output screen on your answer sheetWrite some HTML and CSS to make horizontally reflected layout of this half width layout:(Use Lorem Ipsum to fill out the paragraph)It's very urgent. Please sir, give me answer in less than 50 minutes.

