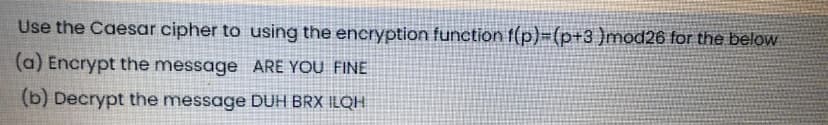
Use the Caesar cipher to using the encryption function f(p)=(p+3 )mod26 for the below (a) Encrypt the message ARE YOU FINE (b) Decrypt the message DUH BRX ILQH
Q: Encrypt the following message using Caesar cipher with a key of 3 The message is (SECURITY IS THE…
A: answer starts from step 2
Q: Use a Caesar Cipher with digraph coding to encrypt the following plaintext: 'buffer' with a key of…
A: Required: Use a Caesar Cipher with digraph coding to encrypt the following plaintext:'buffer' with a…
Q: Q5) Using RSA algorithm, Assume: p= 7 , q = 13, e = 5, d = 29. c) What is the ciphered text if the…
A: The RSA algorithm:- Two Primes are chosen, p and q. Now, compute the value of n = p *q and z =…
Q: 2. The following ciphertext message was encrypted using Vigenére Cipher cipher with keyword JEDI.…
A:
Q: 1. Encrypt the following messages using RSA cryptosyster a) Message : ATTACK , with p=43, q=59 and…
A: It is defined as the process of converting ordinary plain text into unintelligible text and…
Q: Use Rail fence cipher to encrypt the following plain text where key is length of your first name.…
A: The rail fence cipher is a transposition cipher that jumbles up the order of the letters of a…
Q: Use the modified Caesar cipher described in the assignment instructions to encrypt the following:…
A: C code to encrypt the plaintext " ELECTRONIC " using modified Caesar cipher
Q: 2. Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29.
A: Given: Message :"THIS" n=2633 e=29 Using the RSA cryptosystem the encryption can be done with the…
Q: Using the affine cipher, encrypt the string “TABLE” using the keys a = 3 and b = 2. Given the…
A: Plaintext = TABLE Value of x is taken based on alphabetical order, with A = 0, B = 1, C = 2 and so…
Q: Consider the following cipher text message that was encrypted using an additive cipher with a k =…
A: Additive cipher is the simplest cryptography algorithm to encrypt and decrypt the message. In this…
Q: Q16: if the following message "paperx" is encrypted by using Hill cipher and converted into cipher…
A: The matrix used for encryption is the cipher key, and it should be chosen randomly from the set of…
Q: 2. Consider the following plaintext message. Happy Friday a. What is the corresponding ciphertext if…
A: In this problem we have to study about the cryptography, encryption and decryption and Transposition…
Q: Using the affine cipher, encrypt the string "TABLE" using the keys a 3 and b = 2. Given the…
A: The Answer is
Q: Use the modified Caesar cipher described in the assignment instructions to encrypt the following:…
A: Below i have given answer:
Q: Encrypt and decrypt the plaintext C using the Vernam one-time pad cipher for the key value 23.
A: Vernam One-time pad: The one-time pad is a random sequence of characters used as a key for…
Q: Decrypt the message TEA ONS EAS TCN AND TRH THE TEE if it was encrypted using a tabular…
A: The solution is given below for the above given question:
Q: You are given the affine cipher E(x) ≡ 17x - 3 (modulo 26). Using the cipher text alphabet,…
A: The answer for the given question is as follows.
Q: RSA cryptosystem
A: It is given as, N = P × Q and Φ = (P-1) × (Q-1) Here in the example, N = 17 × 11 = 187 Φ =…
Q: The following cipher text was encrypted using a shift cipher AOPZTLZZHNLPZHMHRL Find the plain…
A:
Q: 2. Use the rail fence cipher to encrypt the statement "meet me after the toga party" 3. Using…
A: 2) In rail fence cipher the plaintext is written down as a sequence of diagonals and then read off…
Q: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the message with the…
A: Required: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the…
Q: Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses…
A: RSA algorithm is public-key encryption or asymmetric cryptography algorithm. It uses two separate…
Q: Use the Caesar cipher to (a) Encrypt the message WHAT ARE YOU (b) Decrypt the message ZKHUH DUH BRX
A: REQUIRED:
Q: Try to decipher the following (OYKT) using Hill Cipher if:- [11 16] K [17 21 Select one:
A: converting decipher the following 'OYKT ' converting using hill cipher using given above ->…
Q: 5 Suppose we received the ciphertext "YLUJLQLD" that was encrypted using a Caesar cipher (shift k =…
A:
Q: Use the Caesar cipher to decrypt the message SRUTXH BR WH DPR PDV
A: The Message is SRUTXH BR WH DPR PDV The Cipher used for Encryption is Caesar Cipher. We need to…
Q: 8. The Rabin public-key encryption scheme is similar to RSA. Research this cryptosystem and decrypt…
A: Lets see the solution.
Q: Using transposition cipher, encrypt the message "hello" and then decrypt it.
A: To do transposition cipher of hello. Write it in form of rail. Here I have choosen row…
Q: The following text has been encoded using the affine cipher with key "9x+3". (That is, multiplying…
A: Below is the answer with calculation:
Q: In RSA, given p = 7, q = 13, and e = 17, find n, Φ(n), and d. Further, find the cipher text…
A: RSA Algorithm RSA algorithm is public-key, asymmetric cryptographic algorithm. An asymmetric…
Q: Use a Caesar cipher to decrypt the following message: RCB XENA WRWN CQXDBJWM
A: Note : As per the guidelines we are supposed to answer one question, please repost other question…
Q: 4. El-Gamal O Consider the El-Gamal encryption scheme and let p = 19 and 9 = 3 (a) Suppose the…
A:
Q: 1. Encrypt the following messages using RSA cryptosystem. c) Message : CONTACT , with p=47, q=59…
A: RSA: The Rivest-Shamir-Adleman (RSA) algorithmic rule is one in every of the foremost common and…
Q: Decrypt the message MAXLJGTEAX which was encrypted using the affine cipher: Alphabet: A = 0, B = 1,…
A: ENCRYPTION E(x) = (ax+b) mod m here, a = 5 and b = 6 [key of the cipher] m = 26 [size of…
Q: 14- The following message has been encrypted using the Caesar cipher with key 22: YHKOA PDA ZKKN.…
A: Solution-14) According to the question we need to decrypt the message using the Caesar Cipher with…
Q: Use a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key of…
A: The answer is...
Q: Based on Hill cipher algorithm, if the decryption key is -2 2-5 17-11 11 1 13-12 In the case that we…
A: #include <iostream>using namespace std; void getKeyMatrix(string key, int keyMatrix[][3]){ int…
Q: Use a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key of…
A: The answer is..
Q: In RSA, n=55, e=17, compute the private key d using extended Euclidean algorithm, and decrypt the…
A: In RSA we are using an extended Euclidean algorithm where the Euclidean algorithm ran backward. so…
Q: 2. Encrypt the following message using RSA cryptosystem. Message : THIS , with n=2633 and e=29. R
A: The following is the Encryption
Q: Decrypt the following transposition cipher. YREEOESXUAOYAWMZ What is the plain text? How many…
A: Given transposition cipher as:YREEOESXUAOYAWMZ
Q: he cipher text LLXR was encrypted by a Hill cipher with a key size of 2 x 2 matrix. The plain text…
A: Lets see the solution in the next steps
Q: Q1 / If you know [k] is key for encryption by hill c a result of multiplying [k]*[B], 1- Find the…
A: The answer is
Q: Decrypt the following plaintext "LNZM using Atbash cipher. You have to genereate the Atbash…
A: Answer: Our guide is answer first there question in details from first question. This is question…
Q: DECRYPT the following Cipher Text – ‘GMLNFNPNECSTTF’ with the Key – ‘SALALAH’ using VIGENERE CIPHER…
A: def decrypt(ciphertext, key): key_length = len(key) key_as_int = [ord(i) for i in key]…
Q: 8. The Rabin public-key encryption scheme is similar to RSA. Research this cryptosystem and decrypt…
A:
Q: Using the IDEA cipher in CrypTool, encrypt the following plaintext using the given key. Plaintext:…
A: The ciphertext or the encrypted message for your plaintext using CrypTool is given below -
Q: DECRYPT the following Cipher Text – ‘GMLNFNPNECSTTF’ with the Key – ‘SALALAH’ using VIGENERE CIPHER…
A: To decrypt a Cipher Text using VIGENERE CIPHER, we use the VIGENERE table. In the row corresponding…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- Use a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key ofK=100Using Columnar transposition encrypt the message “TODAY IS MIDTERM EXAM OF INTRODUCTION TO SECURITY ", using key LEMON. Write the cipher in space provided below:Use Rail fence cipher to encrypt the following plain text where key is length of your first name.Plaintext: “Always go for the quality over quantity in your life” Name: Tooba Nazir
- Use the values below to decrypt the numerical ciphertext c = 9. Use the following cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 63 k = 26 Example:5Encrypt the following message by Caesar’s cipher: “You are welcome” a. Brx duh zhofrph b. brx duh zhofroh c. Dtz fwj bjqhtri d. dtz fwj bjqhtrjEncrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.
- The affine cipher (transformation) C≡3P+24 (mod26) was used to encrypt a message. The resulting ciphertext is RTOLKTOIK. Decrypt this message. A=0,B=1,C=2,...,Y=24,Z=25What is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26Calculate H(K), H(M) and H(C) and the unicity distance for the following cryptographic system:First encrypt your plaintext using(a) a Vernam cipher with key lengths 5 and 7.and then encrypt the cyphertext by(b) 2 x 2 Hill cipher mod 29The cypher system is the combined cypher of (a) and (b).
- In Affine cipher, imagine the plain text is SUN and a=3 and b=8 are the two numbers for the key. What is the encrypted text? Please show all your calculations.Q17. Use the values below to decrypt the numerical ciphertext c = 133 , using the cryptoscheme: Encryption (m + k) mod N = c Decryption (c - k) mod N = m N = 50 k = 42In RSA, given p = 7, q = 13, and e = 17, find n, Φ(n), and d. Further, find the cipher text corresponding to plaintext 5 using RSA encryption algorithm.

