Using the affine cipher, encrypt the string "TABLE" using the keys a 3 and b = 2. Given the definition below:
Q: Encrypt the following plain text by using RSA cipher technique. 1. Prime keys: P=3, and Q= 5 2.…
A: C++ Program: #include<bits/stdc++.h>using namespace std; // Given prime Keys int P = 3;int Q =…
Q: Q4: Based on Hill cipher algorithm, if the decryption key is -2 22 -5 17 -11 10 1 -12 In the case…
A: Here i explain about hill cipher encryption:…
Q: Explain how a monoalphabetic substitution cipher works. Illustrate your explana- tion by using the…
A: In questions with many questions we must answer the first one.
Q: Answer the following question: What is the average block size when using a block cipher?
A: Ans: The average block size when using a block cipher is 64 bit or 128 bit block size is the fine…
Q: In an RSA cryptosystem, you intercept a ciphertext C = 2022 sent to a user whose public key is (e =…
A: Given C=2022 e=27893 n=124711 n=p*q where p and q are prime numbers 124711 can be written as the…
Q: Use the two prime numbers p = 5 and q =13 in the first step to give ONE integrated example to show…
A:
Q: In the Affine Cipher, To decrypt a message, we use: O f(p) = (ap + b) mod 26, %3D O f(p) = (ap * b)…
A: The affine cipher is a type of monoalphabetic substitution cipher, where each letter in an alphabet…
Q: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the message with the…
A: The Answer is
Q: Use Rail fence cipher to encrypt the following plain text where key is length of your first name.…
A: The rail fence cipher is a transposition cipher that jumbles up the order of the letters of a…
Q: The difference between some block cipher modes of operation, which solely employ encryption, and…
A: Introduction: To offer information security, such as secrecy or authenticity, an algorithm is used…
Q: Affine cipher is less secure than caesar cipher. 1. true 2. false
A: Question. Affine cipher is less secure than caesar cipher. 1. true 2. false
Q: The digital signature algorithm (DSA) is based on the standard for digital signatures in…
A: The Digital Signature Algorithm(DSA) is standard for digital signature, which depends on the…
Q: Suppose that we instead use an asymmetric cryptographic scheme. How many keys are required in
A: The answer is
Q: In a public key, cryptosystem using RSA algorithm, user uses two prime numbers 5 and 7. He chooses…
A: RSA Encryption Algorithm RSA Data Security invented RSA encryption, which is a public-key…
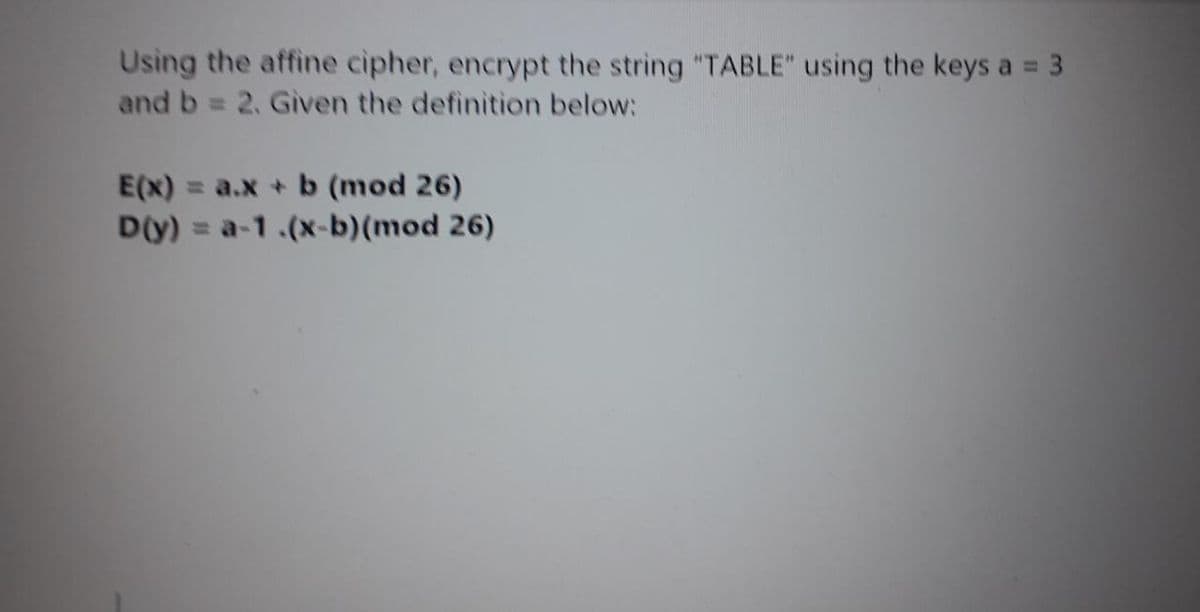
Q: Using the affine cipher, encrypt the string “TABLE” using the keys a = 3 and b = 2. Given the…
A: Plaintext = TABLE Value of x is taken based on alphabetical order, with A = 0, B = 1, C = 2 and so…
Q: Use the two prime numbers p = 5 and q =13 in the first step to give ONE integrated example to show…
A: Here i take all 5 steps and find description and encryption. =======================================
Q: Encrypt and decrypt the plaintext C using the Vernam one-time pad cipher for the key value 23.
A: Vernam One-time pad: The one-time pad is a random sequence of characters used as a key for…
Q: In block ciphers, if we use AES for encryption, it does not matter whether the cipher is CBC-based…
A: In block ciphers, if we use AES for encryption, it does not matter whether the cipher is CBC-based…
Q: With one-time pad (OTP), if the key is composed of all zeros then the plaintext and the ciphertext…
A: Answer : yes , if plain and cipher text are identical then there is no strongest should be left in…
Q: Use the two prime numbers p 5 and q-13 in the first step to give ONE integrated example to show how…
A: Here i explain about RAS alogithm…
Q: Say you obtain a ciphertext of an English sentence encrypted with an unknown key using this scheme.…
A: The answer is
Q: Both cipher feedback mode and cipher block chaining are superior methods for encrypting huge data.…
A: Data Encryption Standard (DES) Cipher Block Chaining Mode: To prevent block replacement, it is a…
Q: A Caesar cipher is a simple substitution cipher based on the idea of shifting each letter of the…
A: def caesar_cipher_encode(string, n): ans = '' for i in string: # traversing string if not…
Q: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the message with the…
A: Required: Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the…
Q: Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses…
A: RSA algorithm is public-key encryption or asymmetric cryptography algorithm. It uses two separate…
Q: Design your own stream cipher to encrypt the message X.
A: Explain own stream cipher text encrypt message
Q: If someone gives you 343 as the ciphertext they created using your public key, what is the plaintext…
A: RSA approach - Using RSA encryption techniquehere, p and q are prime numbersp=53 q=41 n=p*q…
Q: Find the ciphertext using DES if the shared key is "SECURITY" and the output of round 15 is "IT?…
A: INtroduction Shared Key and Public Encryption KeySKIP uses a combination of cryptography shared…
Q: How is the Caesar Cipher more secure than the mono-alphabetic cypher?
A: Introduction: we will look at how a mono-alphabetic encryption is more secure than a Caesar cypher.
Q: The following text has been encoded using the affine cipher with key "9x+3". (That is, multiplying…
A: Below is the answer with calculation:
Q: What does the term "avalanche effect" mean exactly? In current block ciphers, how do you get the…
A: Given: What does the word "avalanche effect" mean? In current block ciphers, how do you get the…
Q: Based on Hill cipher algorithm, if the decryption key is -2 2-5 17-11 11 1 13-12 In the case that we…
A: #include <iostream>using namespace std; void getKeyMatrix(string key, int keyMatrix[][3]){ int…
Q: "The RSA Algorithm" as a model, apply the RSA algorithm using the following values: p = 3, q = 11, e…
A: In this question we have to apply the RSA Algorithm with the given prime numbers and public key.…
Q: . Using the RSA public key cryptosystem, with a = 1, b = 2, etc., a. If p = 7 and q = 11, list five…
A: Question 1a If p = 7 and q = 11, legal values for d are: d = 3d = 5d = 9d = 15d = 21 Question 1b If…
Q: Permutation ciphers hide the message contents by rearranging the order of the letters. choose…
A: Given: Permutation ciphers hide the message contents by rearranging the order of the letters.…
Q: One kind of cryptographic technique is the one-way hash algorithm. Describe it and its…
A: A cryptographic hash function (CHF) is a mathematical procedure that converts data of any size…
Q: Consider the following plaintext message P = Follow us What is the corresponding ciphertext if a…
A: Hey there,I am writing the required solution for the above mentioned question below. Please do…
Q: a) Implement Vigenère Cipher to encrypt the following using the Vigenère table. Is there any…
A: We need to find the encrypted cipher text for the given key and planetext using vigenere cipher…
Q: The definition of a Shift Cipher can be expressed as follows: Def. Let x, y, k ∈ Z26 with the…
A: Given the provided letter encoding, what would be the encoding of the plaintext word ATTACKafter…
Q: Using the affine cipher, encrypt the string “TABLE” using the keys a = 3 and b = 2. Given the…
A: As per our honor code, we are answering the first question.
Q: Decrypt ciphertext (kx mod p = 7, ge mod p = 8). The ciphertext was created using Elgamal encryption…
A: Here is the solution which is mentioned below:
Q: Q-5: Using a one-time pad version of the Vigenere cipher, the key is a stream of random numbers…
A:
Q: Encrypt the word "BREAK" using the shift cipher with the key of 4.
A:
Q: In an affine cipher, if k = (a, b) = (3, 7), then what is the encryption of x=9. Answer by typing…
A: An affine cipher, (like a shift cipher), is an example of a substitution cipher: In encryption using…
Q: Prove that decryption in a Feistel cipher can be done by applying the encryption algorithm to the…
A: Feistel Cipher is not a specific scheme of block cipher. It is a design model from which many…
Q: DECRYPT the following Cipher Text – ‘GMLNFNPNECSTTF’ with the Key – ‘SALALAH’ using VIGENERE CIPHER…
A: def decrypt(ciphertext, key): key_length = len(key) key_as_int = [ord(i) for i in key]…
Q: Suppose that when a long string of text is encrypted using a Vigen`ere cipher, the same string is…
A: Vigen`ere cipher: Vigen`ere cipher is a method which is used to encrypt the alphabetic text. It…
Q: Let k=( 4 1 3 2) be the encryption and key k = (2 4 3 1) be the decryption key used in a…
A: In cryptography, when we desire to hide the original text in the disguise of any unreadable text, we…
Q: Using the IDEA cipher in CrypTool, encrypt the following plaintext using the given key. Plaintext:…
A: The ciphertext or the encrypted message for your plaintext using CrypTool is given below -
Step by step
Solved in 2 steps with 1 images

- Perform the Encryption using the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".Encrypt the plaintext “CAT” using the following RSA model if A uses P = 11 and Q = 19 whereas B uses P = 13 and Q = 17. Then Decrypt the cipher to get back the plaintext.Using the affine cipher, encrypt the string “TABLE” using the keys a = 3 and b = 2. Given the definition below: E(x) = a.x + b (mod 26) D(y) = a-1 .(x-b)(mod 26) 2. You have been recently employed as part of a Network Snooping Association. You first task requires the use of a One-Time Pad to scramble a message. Given the Pad below: PAD1: 25 17 12 11 22 1 26 2 29 3 11 15 22 5 15 25 30 4 16 1Scramble the message “I_AM_ _PREGNANT._ _ _”. The result cipher text should be descrambled to get back the original message or plaintext.
- Find the decryption key for the affine cipher with n=26, a=5 and b=8. Encrypt the messagewith the code 15 and 19Using Shift Cipher with Key = 4, encrypt the plaintext CONFIDENTIALITY ISASSUREDPerform the Encryption and then the Decryption for the Hill Cipher where the Plain text: "POH" and the key is: "GYBNQKURP".
- Briefly describe the RSA cipher. If the prime numbers e, p, and q are 17, 7, and 11, respectively, in the RSA technique, derive the public and private keys.Suppose that when a long string of text is encrypted using a Vigen`ere cipher, the same string is found in the ciphertext starting at several different positions. Explain how this information can be used to help determine the length of the key.What is the formula used for encryption of data using affine cipher(a,b are constants and x is the numerical equivalent of a letter to be encrypted)? 1. ax+b 2. (ax+b)%26 3. a(x^2) +bx 4. (a(x^2) +bx)%26
- The following text has been encoded using the affine cipher with key "9x+3". (That is, multiplying the letter by 9 and add 3 (mod 26) to encode.) For example, the encryption result of letter “A” is “D”. Decrypt the following ciphertext. GNVBAXSL XG QWBUse a Caesar Cipher with digraph coding to encrypt the following plaintext: ‘buffer’ with a key ofK=100In Affine cipher, imagine the plain text is SUN and a=3 and b=8 are the two numbers for the key. What is the encrypted text? Please show all your calculations.

