a) Implement Vigenère Cipher to encrypt the following using the Vigenère table. Is there any relation between plain text and key? Key = Possible Plaintext = Possibility
a) Implement Vigenère Cipher to encrypt the following using the Vigenère table. Is there any relation between plain text and key? Key = Possible Plaintext = Possibility
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
Cryptography
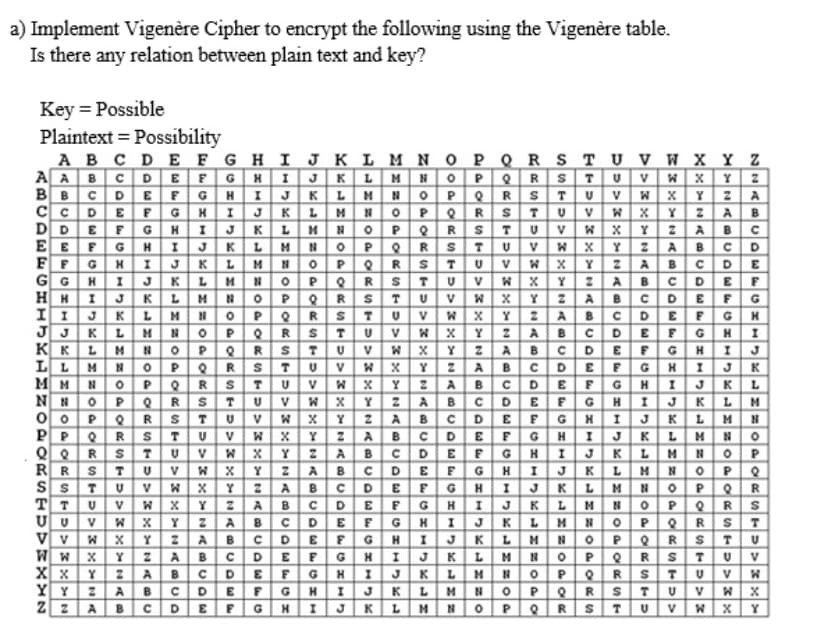
Transcribed Image Text:a) Implement Vigenère Cipher to encrypt the following using the Vigenère table.
Is there any relation between plain text and key?
Key = Possible
Plaintext = Possibility
AB C DE F GHI JK LM N OP QRS TU V W XYZ
AABCDEFGH I J KL MNOPQRSTU VWx Y 2
BBCDEFGH IJKLMNOPORST U VWx Y 2 A
CCDE FGHI JKL M NOPeRSTUVW XY2AB
NOPQ R
OPe RS
NOPeRST
DDEFGH
E E FG
FFGH 1 JKL
G G
H H
I I JK
J J
KKLM
LLMN 0POR
MMNO PQRS
NN O PQR
IJK LM
I JK
U V W X Y 2ABC
W XYZABCD
U VWX Y ZAB CDE
W XY2ABCDEF
W XY 2ABCDEFG
STUVW XY2ABCDEFGH
TUVWXY 2 A BCDE FGHI
W XY ZABCD EFGHIJ
W XY ZABCD EFGH IJK
W XY 2ABCDE FGH IJKL
2 ABCDEFGHIJKLM
H
L
TU
H
I JK LM
OPe R
MN O PQR
MN OP eR
NOPQR
OPQ
I
K
L.
STU v
L.
K
UV
V
WxY
O0PO RSTU VW XY 2ABCDEFGHIJK LMN
2ABC DEFGHIJK LMNO
XY ZABCDE FGHI JKLMNOP
NOPO
PQR
BCDEFGHI JKLM NOPQR
EFGH I J KLMNOP ORS
STU
RR
S S
BCDE FGHI JKLM
HIJKLM
U V
ZA
B
CDE FG
V
XY z A
W XY 2ABCD
W xY ZABCD EFG H I JK LMNOPQ
Y2AB CDEFGHI JKLM NOPeR
2ABCDEFG HIJKLMN OPOR
V
T
V v
W W
X x
YY
U VW
CDE
E F
A
B
G
K
L.
D.
G.
L.
V
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education