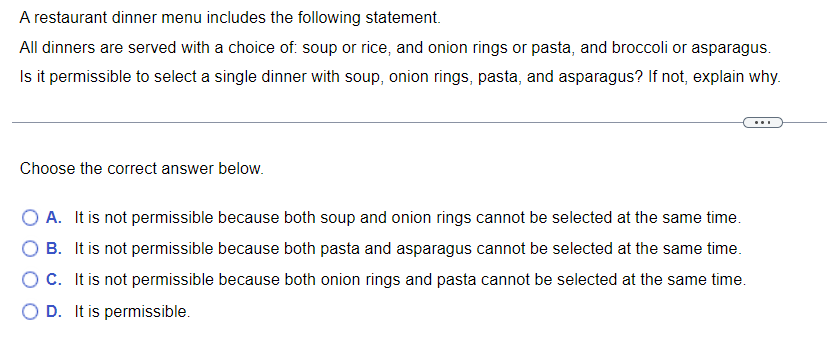
ved with a choice of: soup or rice, and onion rin select a single dinner with soup, onion rings, p
Q: This thorough book will cover everything from DNS records to authoritative servers to iterative and…
A: DNS transforms domains to IP addresses, allowing: Web browsers access the Internet. Each network…
Q: What does this mean? Unable to copy files into table. Number of columns in file (3) does not match…
A: Answer: It looks like you have a header row in your file. Have you tried using the optional…
Q: Why does video data need more storage than other types of data and why does it use up more storage…
A: It's important to discuss why video data needs more storage space than other forms of data. Several…
Q: When does regularization come into play in Machine Learning?
A: When does regularization come into play in Machine Learning?
Q: What are mobile apps exactly, and why are they so crucial?
A: Apps are intended to operate on mobile devices such as tablets, phones, watches, etc. The…
Q: The idea of two-factor authentication seems unclear to me. Does it make a difference in the…
A: MFA, or multifactor authentication, is a method of security in which several factors must be used to…
Q: Why doesn't C belong in the list of object-oriented languages?
A: Object-oriented language : Object-oriented programming is a programming worldview based on the idea…
Q: What precisely do you mean when you state authentication's objectives? Contrast and compare the…
A: The answer to the question is: Your sign-in procedure is more secure when authentication mechanisms…
Q: What are mobile apps exactly, and why are they so crucial?
A: Introduction: Mobile app: An application for mobile devices is a kind of software. The program was…
Q: What precisely is a Trojan horse and how does it work? Please provide three examples to support your…
A: Given: A harmful virus or piece of software that masquerades as legitimate but has the power to take…
Q: Compare the advantages and disadvantages of solid-state secondary storage devices to magnetic…
A: Intro Solid-state secondary storage devices: SSDs offer quicker startup times, perform speedy file…
Q: Examine how solid-state and magnetic secondary storage systems vary from one another and from one…
A: Start: Memory is where the facts and information are kept in reality. There are two categories of…
Q: Compilers and assemblers may rearrange asm instructions to reduce pipeline dangers to the maximum…
A: Compilers and assemblers will attempt to rearrange instructions to reduce pipeline hazards, but they…
Q: Hi could you explain which line of code is doing what? I am new to python and need help figuring out…
A: program that takes any number of integers as input, and outputs the average and max. Ex: If the…
Q: On the other hand, it has been suggested that a processor be used that can decode encrypted data and…
A: In answer to the question you posed: The instruction cycle is the cycle that is followed by the…
Q: siven relations PRO New York and pz: in Fig. 2.2 in our textbook, "New York be two simple predic…
A: Let's do the predicts p1 = LOC <= "New York" p2 = LOC > "New York"
Q: What sort of connection is required to link a Pega PRPC Assignment to another form?
A: Given: A modem is the main piece of hardware you require.The kind of modem you require will depend…
Q: We want our DSL to be non-invasive so that we may rely on the benefits of inheritance. The method we…
A: Inheritance is one of the concept of object oriented programming in which a child class inherit all…
Q: Question 11Aa Computer Science What command will show us the current enviorment paths that is…
A: What command will show us the current environment paths that is tied to a user in Windows? Answer:…
Q: PCM Sampling Explain the relationship between dynamic range, resolution, and the number of bits in a…
A: ANSWER:-
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Optical scanners include barcode readers and barcode scanners: These scanners can decode printed…
Q: What description to Array and Linked List is mistake? O a. Using Linked list, if there is a existed…
A: c. If the size of main memory is enough, there is no upper bound limitation to increase new data…
Q: What benefits come from knowing how to utilize technology, including computers and other devices?
A: Computers are essential in professional situations in the twenty-first century, and a lack of…
Q: Hi just having a little trouble understanding what this is asking me to review and I have no idea…
A: Finite State machines which represents that machine or finite-state automaton, finite automaton, or…
Q: Examine how solid-state and magnetic secondary storage systems vary from one another and from one…
A: Storing magnetic data: Magnetic storage or magnetic recording refers to the capacity of data on a…
Q: What is the authentication procedure? What are a few of the goals? Examine how the advantages and…
A: Username and password combination is the most popular authentication mechanism and it is also known…
Q: What sort of connection is required to link a Pega PRPC Assignment to another form?
A: Connector - A connector defines an outbound request for information based on metadata that is…
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: P2P (or peer-to-peer) is a file-sharing technique that is used in the field of computer networking.…
Q: Do you believe there is a difference between the user's computer and the server's computer while…
A: Introduction: A correspondence meeting is when two devices who are interested in the correspondence…
Q: It's as a result of how powerful computers have become. How can it be shown that computers have had…
A: Question: It's as a result of how powerful computers have become. How can it be shown that computers…
Q: Q.4 Use polyalphabetic ciphers to encrypt plain VERY HAPPY AND BEAUTIFUL GIRL" use key 'ANOTHER'…
A:
Q: Match the data types on the left with range of values they can represent. The range depends on the…
A: Although it is a keyword, the sizeof operator calculates the size, in bytes, of a variable or data…
Q: Which of the following is a key part of physical design in an entity relationship model? O This…
A: I have given answer below.
Q: Describe how a computer program might be tuned to operate fas and efficiently on a modern pipelined…
A: Architecture pipelining It collects processor instructions in a pipeline. It organises storing and…
Q: The idea of two-factor authentication seems unclear to me. Does it make a difference in the…
A: Multi-factor authentication - (MFA), commonly referred to as two-factor or dual authentication,…
Q: What is the authentication procedure? What are a few of the goals? Examine how the advantages and…
A: Everything is dependent on how authentication is implemented. If we rely only on it as a security…
Q: Is it possible that, in light of the recent data breaches that have been publicized, cloud security…
A: Introduction Access to data that is sensitive, confidential, or otherwise protected because of…
Q: Instructions: Answer the following questions. Do not be short with answers. Each answer should be…
A: Hacktivism:- Hacktivism—a term created by fusing the words "hack" and "activism"—describes the act…
Q: What precisely do you mean when you state authentication's objectives? Contrast and compare the…
A: The response to the question is Your sign-in procedure is more secure when authentication mechanisms…
Q: in computer organization and architecture create a simple program to evaluate the performance of a…
A: INTRODUCTION: The quantity of work a computer system can complete is called its performance. The…
Q: Compare IS-IS and OSPF routing protocols in terms their similarities and differences? List and…
A: What Does Routing Protocol mean? The most efficient pathways for network data transfer and…
Q: Cipres Q.13 How is a Hill cipher vulnerable to chose plaintext attack?
A: The answer is given in the below step
Q: 2.)Recurrences. a.)Provide a Sample code for the recurrences below. i.) T(n)=T(n/5)+T(3n/5)+n…
A: a. i.) def recurrences(n): if n == 1: return 1 else: return…
Q: The relationship between digital devices and mobile cellphones, as well as the current convergence…
A: Digital convergence is simply the process of digital material being accessible via many…
Q: lef foo(arg): if isinstance (arg,-): return 'yeah' else: return 'oops' print (foo (3.14)) print (foo…
A: So here in the code, I am checking the type of input. For foo(3.14) it is returning oops that is in…
Q: algorithm MatrixMultiplication (A1, A2, ... , An) pre-cond: An instance is a sequence of n…
A: algorithm MatrixMultiplication (A1, A2, ... , An) pre-cond: An instance is a sequence of n matrices.…
Q: CIA triad is an important model designed to guide information security policies for businesses and…
A: CIA Model:- Confidentiality, Integrity, and Availability are represented by the "CIA tried three…
Q: Why is studying Introduction to Computing essential, and how will it help you comprehend and…
A: Your answer is given below. Introduction :- One of the most important inventions of the 20th century…
Q: When does regularization come into play in Machine Learning?
A: Have you ever encountered a situation where your machine learning model models the training data…
Q: Do you believe that after a data breach, it is still feasible to impact cloud security? Can this be…
A: The answer to the question is given below:
4
Step by step
Solved in 2 steps with 1 images

- Question Sum implify the following expression by using the prope (x^(3))^(6)(x^(6))^(3) Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line.A restaurant dinner menu includes the following statement. All dinners are served with a choice of: bread or salad, and onion rings or pasta, and carrots or peas. Is it permissible to select a single dinner with bread, salad, and peas? If not, explain why.You need to choose a password for computer account. The rule is that the password must consist of two lowercase letter (a to z) followed by one capital letter (A to Z) followed by four digits (0, 1, …, 9). For example, the following is a valid password:Find the total number of possible passwords.
- Question 4 There are 10 agents to sell tickets and totalTickets= 400. Use multithreading representing the agents each trying to sell the total tickets without any race condition using semaphore on the following function. void sellTickets(int agent, int* totalTickets) { ……. } Use print function when agents sell the ticket and when all tickets are sold. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineClunker Motors Inc. is recalling all vehicles in its Extravagant line from model years 1999-2002 as well all vehicles in its Guzzler line from model years 2004-2007. Given variables modelYear and modelName write a statement that assigns True to recalled if the values of modelYear and modelName match the recall details and assigns False otherwise.When you use a mortgage to purchase a home, the lending institution effectively owns the home. You buy back part ownership in the home with each monthly payment. The part you have bought back is your equity in the home. If the mortgage amount is P dollars, the monthly interest rate is r as a decimal, and the term of the mortgage is t months, then your equity after k payments is E(k) = P((1 + r)k − 1) (1 + r)t − 1 dollars. In this exercise, assume that the mortgage amount is $200,000, the APR is 6% so r = .06/12 and the term of the loan is 30 years (360 months). (a) Find a formula for the equity. (b) Make a graph of the equity over 360 months, the term of the loan. (c) Does the graph show that you have half-ownership in the home halfway through the term of the mortgage? Halfway through the term of the mortgage corresponds to k1 = _______ payments. From the graph, we see that E(k1) is ________ half of the mortgage amount, so we _______ have half-ownership in the home…
- Must answer 4 and 5 questions both with correct and detailed else i will give u downvoteCreate the following variables: Gender (e.g. male or female) Age (e.g. 0, 1, 2, etc.) Handedness (e.g. left, mixed, right) Average number of minutes of exercise each week (e.g. 120, 180, 0, 30, etc.). Average number of daily calories consumed (e.g. 1400, 2500, etc.) Average number of cigarettes smoked per day (e.g. 0, 20, 5, etc.) Average number of alcoholic beverages consumed each week (e.g. 2, 20, 0, etc.) Self-Esteem (measured on a scale from 0-10 - e.g. 3, 8, 2, etc.) General Life satisfaction (measured on a scale from 0-10 - e.g. 2, 10, etc.). Enter data for each of the variables. Pay attention to the information in the parentheses next to the variables listed above as this will guide you to the type of information that needs to be entered. Try to make your data varied (e.g. do not make all your participants age 20). Please make 10 of your participants male and 10 of your participants female. Part 2: Using StatCrunch calculate the descriptive statistics (e.g. measures of central…Ask the user to enter a day of the week in 3 letters.* Respond with the meal plan for that day. Here's the* plan:* Meatless Monday* Taco Tuesday* Wings Wednesday* Thrifty Thursday* Filet O Fish Friday* (Weekend is "Buffet Day")* * Ignore case, e.g. "Wed" or "WED" or "wed" all refer* to Wednesday.* * Example 1:* Enter a day of the week (3 letters): Wed* It's Wings Wednesday!* * Example 2:* Enter a day of the week (3 letters): SAT* It's Buffet Day!* Although my code isn't finished, it keeps printing out It's Meatless Mondays for the "TUE".
- Step 1: Consider the following values set to variables. myAge = 32 yourAge = 18 myNumber = 81 yourNumber = 17 votingAge = 18 myName = “Katie” yourName = “Bob” Based on the values to the variables in Step 1, do the following conditions result in a true or false statement? (Reference: Boolean Expressions, page 119). The condition True or False myAge >= yourAge yourAge > myAge myAge == 45 yourAge == votingAge votingAge <= yourAge myAge <= votingAge myName != yourName myNumber <= myAge yourNumber >= myAge yourNumber != 17Rustic Tastes is a brownie shop that sells 30 kinds of brownies, where brownies of thesame kind are indistinguishable, and there are at least 25 brownies of each kind. Vibrant Flavorsis a newer brownie shop that sells 40 kinds of brownies, where brownies of the same kind areindistinguishable, but there are only at least 15 brownies of each kind. Please leave your answer ina compact form, e.g. C(9, 4) instead of 126. (a) Which shop has more ways that you can get a box of 7 brownies, and by how much?(b) How many ways can you get a box of 10 brownies from Vibrant Flavors if you want to be sure to get at least 2 Citrus Central brownies and 4 Caramel Turtle brownies?(c) How many ways can you get a box of 12 brownies from Rustic Tastes if you want to get exactly 3 Basic Blondie and 3 Chocolate Melt brownies?Complete the function below that takes in three integers (a,b,c) and returns the number of integers between a and b (inclusive of the endpoints) that are divisible by c. Make sure it tests a and b for divisibility by c! In [ ]: defhow_many_divisible(a,b,c):counter=0# YOUR CODE HEREraiseNotImplementedError()returncounter In [ ]: assert how_many_divisible(10,20,5) == 3 assert how_many_divisible(30,77,7) == 7 PYTHON jYPYTER





