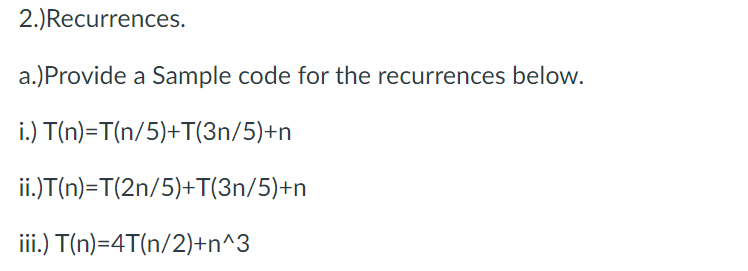
2.)Recurrences. a.)Provide a Sample code for the recurrences below. i.) T(n)=T(n/5)+T(3n/5)+n ii.)T(n)=T(2n/5)+T(3n/5)+n iii.) T(n)=4T(n/2)+n^3
Q: How can app makers generate money if the app requires internet connectivity to function?
A: According to specific estimations, the market for agile apps will reach $100 billion by 2020.…
Q: I'm trying to edit column DEGREE_TYPE_MAJOR to DEGREE_TYPE and add a column MAJOR in Snowflake. How…
A: The queries are given in the below step with output screenshots after each query. Happy to help you…
Q: JAVA CODE PLEASE Functions With No Parameters But With Return Values Practice I by CodeChum Admin…
A: ALGORITHM:- 1. Create the method that takes input from user and returns it. 2. Call the created…
Q: What is a Trojan horse, and how does it operate? Provide three concrete instances.
A: Given: A Trojan horse is a piece of malicious software or malware that poses as legitimate but is…
Q: Look at the assaults coming from inside the academy. If you have any suggestions on how to stop…
A: Consider college's internal attacks. Please provide any tips for preventing attacks. Students…
Q: e remote interface serve,
A: Solution - In the given question, we have to tell what purpose does the remote interface serve, and…
Q: Suppose we apply the Mix Columns operation to a *column* vector [0x19, 0x85, 0x91, 0x02] (given with…
A: Introduction The process of changing one number in a number system to another is known as…
Q: How does secret key cryptography function? Please provide a short explanation, maybe with an…
A: Given: How does secret key cryptography function? What is it? Please include a brief description,…
Q: Images are not shareable. When you email your real estate partner, you include images of a home that…
A: You want to attach pictures of a home for sale to an email you sent to your real estate partner.
Q: Do you agree that "there is no concept of client and server sides of a communication session" in a…
A: P2P (or peer-to-peer) is a file-sharing technique that is used in the field of computer networking.…
Q: Create a LWC component to display the output. You can create the dummy data in JS file. HelloForEach…
A: Create a LWC component to display the output. You can create the dummy data in JS file. HelloForEach…
Q: Which is preferred when it comes to linking the CPU to memory? Thanks. How did you arrive at this…
A: Motherboard is among the one of the most important component present in a computer.
Q: Describe the most successful ways for discovering images that may be used without authorization.
A: Given: The best approaches to look for photographs that are copyright-free must be discussed.…
Q: It's as a result of how powerful computers have become. How can it be shown that computers have had…
A: Computers have brought revolution in this 21st century.
Q: Give the names of the three different kinds of servers that a local bank could use.
A: Introduction Everywhere in today's growing period, technologies are being utilized.
Q: Explain the purpose and usage of cellphones, digital cameras, portable and digital media players,…
A: Answer the above question are as follows
Q: Debate against the following statement: "It is unethical to share photographs or recordings of…
A: INTRODUCTION: When a person creates a picture in the United States, that image is immediately…
Q: What sort of connection is required to link a Pega PRPC Assignment to another form?
A: Given: The PegaRULES Process Commander, also known as PegaPRPC, automates process optimization based…
Q: Describe how a computer program might be tuned to operate fast and efficiently on a modern pipelined…
A: The language C is procedurally oriented: Polymorphism, encapsulation, and inheritance programming…
Q: In the majority of retail locations, barcode scanners are already standard equipment. Include one…
A: Introduction: Optical scanners include barcode readers and barcode scanners. These…
Q: List the many preventive steps that may be taken to thwart phishing and spoofing techniques, and…
A: Phishing Attack Phishing attacks are the practice of sending fraudulent communication that appears…
Q: What is the authentication procedure? What are a few of the goals? Examine how the advantages and…
A: The answer to the question is given below:
Q: The amount of times a _______________-controlled loop repeats depends on a true/false condition. 1>…
A: Loop is a control structure that performs a certain task number of times , Let's discuss which is…
Q: Is using a computer in your everyday life something you consider important?
A: Because it is integrated into so many facets of people's lives, technology is an indispensable…
Q: Understanding the factors that lead to video data requiring and using more storage space than other…
A: Introduction: Why does video data need and consume more storage than other types of data? A video is…
Q: Is it feasible to distinguish between various authentication mechanisms in terms of safety?
A: The answer to the question is given below:
Q: Give real life example of ring topology and where do they use it
A: Topology of ring networksIn a ring network topology, nodes are connected in a ring or loop. Data is…
Q: How does ransomware function in terms of computer security?
A: Infected computers get infected with ransomware, which encrypts and locks the user's data until a…
Q: mpare the difference between a resource template and a text analysis packa
A: Lets see the solution.
Q: The idea of two-factor authentication seems unclear to me. Does it make a difference in the…
A: Multifactor Authentication, or MFA, is a method of security where more than one factor must be used…
Q: Why doesn't C belong in the list of object-oriented languages?
A: Object-oriented language : Object-oriented programming is a programming worldview based on the idea…
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: We need to discuss the Domain Name System (DNS), including iterated and non-iterated searches,…
Q: Understanding the factors that lead to video data requiring and using more storage space than other…
A: Introduction: Why do video data need more storage space than other data types. A video is a picture…
Q: Show all of the steps needed to encrypt and decrypt the ASCII message “YES” without a modular…
A: The answer is
Q: What benefits come from knowing how to utilize technology, including computers and other devices?
A: Computers are essential in professional situations in the twenty-first century, and a lack of…
Q: Suppose we have the following sets: P, Q, and R. Prove or disprove that if for all x, (x ∈ P) → ((x…
A: Hello student The answer will be in next step :-
Q: What is the definition and implication of a poison package attack? Please provide two instances of…
A: ARP Poisoning, also known as ARP Spoofing, is a method of attacking a LAN via the Internet in which…
Q: On the other hand, it has been suggested that a processor be used that can decode encrypted data and…
A: In response to your inquiry, When a computer is shut down to execute instructions, the instruction…
Q: Why doesn't C belong in the list of object-oriented languages?
A: Introduction: The language C is procedurally oriented. Polymorphism, encapsulation, and inheritance…
Q: Question 7 Match the items on the left with the ones on the right. Hint: program using sizeof…
A: Hey dear, I hope you will be fine the above questions are done below.
Q: What are some of the authentication procedure's goals? Compare the pros and downsides of various…
A: We need to discuss authentication procedure's goals and compare the pros and downsides of various…
Q: Do you believe there is a difference between the user's computer and the server's computer while…
A: Introduction P2P File Sharing Application lets users access and share media files through…
Q: (Looping statement) java Tell whether a given word is a palindrome or not, Sample…
A: These question answer is as follows
Q: When explaining the DNS, be sure to mention authoritative and root servers, iterated and…
A: DNS (Domain Name System ) : The phonebook of the Internet is the Domain Name System (DNS). Domain…
Q: What do you think are some possible solutions to the issues that these people confront, and what…
A: The answer is given in the below steps Happy to help you ?
Q: What purpose does the remote interface serve, and what requirements must it fulfill?
A: Introduction: When implementing RMI, the following remote interfaces must be used: In RMI, a remote…
Q: please solution with explain Q1:In database ER diagram, how do we uniquely identify relationships?…
A: Solution in step 2:
Q: 2. Assume we are using the simple model for floating-point representation as given in this book (the…
A: floating-point format:- Single-precision floating-point format, often known as FP32 or float32, is a…
Q: Improving the memory system for the above so that each Load instruction takes just 25 CPI would…
A: Let's see the answer:
Q: What are the goals of employing a variety of visual aids? Describe how you would use three unique…
A: Intro Visual aids include objects, photographs, diagrams, data graphs, charts, and videos. Visual…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- def longest_unique_substring(s: str) -> str:"""Given a string <s>, return the longest unique substring that occurs within<s>.A unique substring is a substring within <s> which DOES NOT have anyrepeating characters. As an example, "xd" is unique but "xxd" is not.If there are two equal length unique substrings within <s>, return the onethat starts first (i.e., begins at a smaller index).tips:In order to get your function to run fast, consider using a dictionary tostore the indexes of previously seen characters, from there, you canfollow a set of rules based on each new character you see to determinethe length of the longest unique substring seen so far.>>> longest_unique_substring('aab')'ab' >>> longest_unique_substring('abcabcbb')'abc'""" RESTRICTIONS: - Do not add any imports and do it on python .Do not use recursion. Do not use break/continue.Do not use try-except statements.def longest_unique_substring(s: str) -> str:"""Given a string <s>, return the longest unique substring that occurs within<s>.A unique substring is a substring within <s> which DOES NOT have anyrepeating characters. As an example, "xd" is unique but "xxd" is not.If there are two equal length unique substrings within <s>, return the onethat starts first (i.e., begins at a smaller index).tips:In order to get your function to run fast, consider using a dictionary tostore the indexes of previously seen characters, from there, you canfollow a set of rules based on each new character you see to determinethe length of the longest unique substring seen so far.>>> longest_unique_substring('aab')'ab'""" RESTRICTIONS: - Do not add any imports and do it on python .Do not use recursion. Do not use break/continue.Do not use try-except statements.Describe each of the following sets by listing its elements:a. {x | x ∈ N and x2 − 5x + 6 = 0}b. {x | x ∈ R and x2 = 19}c. {x | x ∈ N and x2 − 2x − 8 = 0}}d. {x | x ∈ Z and x ∗ x = 4}
- Implement the following function, without using any data structure or #include <bits/stdc++.h> /* Given two vectors of chars, check if the two vectors are permutations of each other, i.e., they contains same values, in same or different order.e.g., V1=[‘a’,’b’,’a’] and V2=[‘b’,’a’,’a’] stores same multi-set of data points: i.e., both contains two ‘a’, and one ‘b’. e.g., V3=[‘a’,’c’,’t’,’a’] and V4=[‘a’,’c’,’t’] are not same multi-set. V3 contains two ‘a’s, while V4 has only one ‘a’. Note: when considering multiset, the number of occurrences matters. @param list1, list2: two vectors of chars @pre: list1, list2 have been initialized @post: return true if list1 and list2 stores same values (in same or different order); return false, if not. */ bool SameMultiSet (vector<char> list1, vector<char> list2) THIS IS NOT THE CORRECT SOLUTION / include headers #include <bits/stdc++.h> // deinfe the namespace using namespace std; // function fo rchecking same bool…def find_root4(x, epsilon): ''' IN PYTHON Assume: x, epsilon are floating point numbers and epsilon > 0 Use bisection search to find the following root of x such that If x >=0, return y such that x - epsilon <= y ** 2 <= x + epsilon Else, return y such that x - epsilon <= y ** 7 <= x + epsilon Note: You must use bisection search to implement the function. ''' passWith the following C++ code, implement the “indirect sum” method of computing a sum. You will need to provide an implementation inside both the setup() and sum() functions in the sum_indirect.cpp file in the code harness. Here, setup() consists of initializing an array of length N to contain random numbers in the range 0..N-1 (hint: use lrand48() % N). --- #include <algorithm> #include <chrono> #include <iomanip> #include <iostream> #include <random> #include <vector> #include <string.h> void setup(int64_t N, uint64_t A[]) { printf(" inside sum_indirect problem_setup, N=%lld ", N); } int64_t sum(int64_t N, uint64_t A[]) { printf(" inside sum_indirect perform_sum, N=%lld ", N); return 0; }
- Answer the given question with a proper explanation and step-by-step solution. #include<stdio.h>#include<stdlib.h>#include"NoteSynth.c" typedef struct BST_Node_Struct{ double key;double freq;int bar;double index;/*** TO DO:* Complete the definition of the BST_Node_Struct***/ } BST_Node; BST_Node *newBST_Node(double freq, int bar, double index){ /*** TO DO:* Complete this function to allocate and initialize a* new BST_Node. You should make sure the function sets* initial values for the data in the BST_Node that can* never occur in an actual musical note from a score!****/ return NULL;} BST_Node *BST_insert(BST_Node *root, BST_Node *new_node){/** This function inserts a new node into the BST. The* node must already have been initialized with valid* note data, and must have its unique key.** The insert function must check that no other node* exists in the BST with the same key. If a node with* the same key exists, it must print out a message* using the following format…Write aJava function given an array of integers nums [passed by reference] and an integer target, return indices of the two numbers such that they add up to target. You may assume that each input would have exactly one solution, and you may not use the same element twice. You can return the answer in any order.Write a function that takes in a list of integers L and an integar n. The function returns the absolute value of the sum of the every other nth element of L. Make sure not to use an index outside the possible locations within L.
- Write a recursive function named binarySearch that accepts a reference to a sorted vector of integers and an integer target value and uses a recursive binary search algorithm to find and return an index at which that target value is found in the vector. If the target value is not found in the vector, return -1. The following code shows some example calls and their expected return values: // index 0 1 2 3 4 5 6 7 8 9 10 11 12 13 14 15 16vector<int>v {-4, 2, 7, 10, 15, 20, 22, 25, 30, 36, 42, 50, 56, 68, 85, 92, 103};intindex=binarySearch(v, 42); // 10intindex=binarySearch(v, 66); // -1 You should assume that the vector's elements are already sorted; you do not need to handle the case of an unsorted vector. Your function must be recursive and must use a binary search algorithm. Do not use loops or auxiliary data structures.Implement the following function, without using any data structure. /* Given two vectors of chars, check if the two vectors are permutations of each other, i.e., they contains same values, in same or different order.e.g., V1=[‘a’,’b’,’a’] and V2=[‘b’,’a’,’a’] stores same multi-set of data points: i.e., both contains two ‘a’, and one ‘b’. e.g., V3=[‘a’,’c’,’t’,’a’] and V4=[‘a’,’c’,’t’] are not same multi-set. V3 contains two ‘a’s, while V4 has only one ‘a’. Note: when considering multiset, the number of occurrences matters. @param list1, list2: two vectors of chars @pre: list1, list2 have been initialized @post: return true if list1 and list2 stores same values (in same or different order); return false, if not. */ bool SameMultiSet (vector<char> list1, vector<char> list2)Write the code for the following function."""def unmask_chars(s1: str, s2: str, mask: str) -> str:'''Return a new string where the character at index i iss1[i] if mask[i] is 0and s2[i] if mask[i] is 1.len(s1), len(s2), and len(mask) are equal.>>> unmask_chars('cat', 'bat', '001')'cat'>>> unmask_chars('a', 'b', '0')'a'>>> unmask_chars('apple', 'graph', '01011')'arpph''''# TODO: Write your code here

