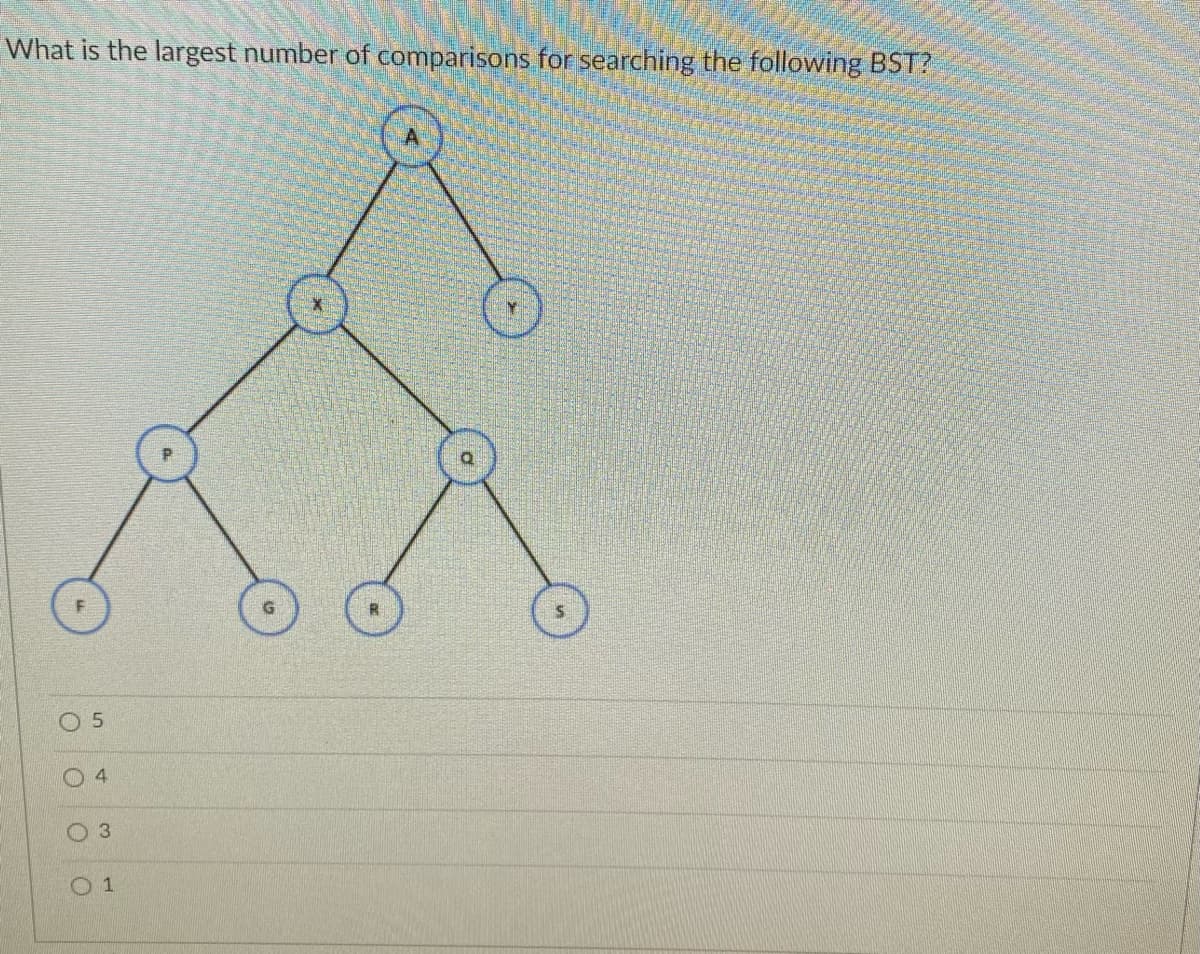
Vhat is the largest number of comparisons for searching the following BST? 3 O 1
Q: Which of the following represents hashing algorithms? RSA MD5 O SHA-256 O All of the above
A:
Q: Which of these is NOT a characteristic of a secure hash algorithm? a. Collisions should be rare. b.…
A: Answer: a. Collisions should be rare.
Q: If the last index of a hash table is d - 2, where d is a positive integer value, what is the size of…
A: Note: index range in hash table is 0 to hash table size-1 means first index is :0 last index = hash…
Q: What is the height of an empty BST
A: Given What is the height of an empty BST?
Q: What is direct addressing in hashing? O Unique array position for every possible key O Fewer array…
A: Hashing is the process of transforming any given key or a string of characters into another value.
Q: Select an integer N where 12 < N < 60. Rehash the original hash table to the larger hash table array…
A: Given, Original array: 8 16 33 43 12 h(k)=k mod Tablesize g(k)=5-(k mod 5) Table size of…
Q: Question 36 Which one of the following is true about SHA 256 Hashes: O They include letters and…
A: SHA 256 is 256 bits long as the name indicates. Since SHA 256 returns a hexadecimal representation,…
Q: Which of the following statements about cryptographic hash functions is correct: A. Cryptographic…
A: CRYPTOGRAPHIC HASH FUNCTION: The Cryptographic Hash function is an algorithm that maps data of any…
Q: Which of the following binary search trees (BSTS) provides the best performance among them in…
A: Binary search tree with minimum height have maximum search time complexity of log(n). because tree…
Q: What the output for the following code? ID A B D 12 Huda 27 23 13 Ali 14 34 11 Sami 17 35 Il suppose…
A: c. 6 7 8
Q: Insert the following sequence of 12 keys into a separate-chaining hash table with 3 chains: key hash…
A: Given the sequence of 12 keys we have find search miss for the key k , whose value is 0. And find…
Q: Which of the following is the suitable answer for the Dynamic Hashing? The hash table is not used to…
A: In step 2, you will get the answer.
Q: Insert the following data to an initially empty hash table with a size of 19. ALONGDATASTRINGFORT…
A: Introduction of Hash Table: Hashing is a data structure that used a special function hash function…
Q: How do I load/move URL information from one column into a seperate column on power BI?
A: Power BI is a product interactive software developed by Microsoft that focuses on business…
Q: Load factor (A ) of a hash table is the ratio of. O The size of key to the size of hash table. O No.…
A: Answer :
Q: Which of the following operations are not usually supported/performed by hashing? O a. Delete an…
A: We can delete any item from a hash table.
Q: Consider the following linked list: head D-E-E newlode 50 Which of the following contains the…
A: Objective: A single linked list is designed with some values. A newNode is required to add to the…
Q: Which of the following binary search trees (BSTS) provides the worst performance among them in…
A:
Q: Which of the following statements state the advantage of hashing table? O Insertion and deletion…
A: Please find the answer below
Q: convert UNF for 1NF to 2NF to 3NF, progressively. UNF: Order(OrderID, OrderDate, CustID, CustName,…
A: The given table, Order, is unnormalized. FIRST NORMAL FORM (1NF) The first normal form only…
Q: Which of the following is not a collision resolution technique? a. Separate chaining b. Linear…
A: Hello student. Warm welcome from my side. Hope you are doing great. I will try my best to answer…
Q: integer N into the larger hash table array as well.
A: Hash of size N
Q: Which of the following technique stores data in the hash table itself in case of a collision? a)…
A: Here, Four options are given.
Q: Which statement about the Hash function (H) is false: 1. For a message of any length, the size of…
A: H function stands for Hash function.
Q: You had previously prepared a file that you intended to use in a dictionary attack against a target…
A: introduction: Some distinctions between developing operating systems for personal computers and…
Q: Given hash function h(key), when inserting an item with key k to the hash table A, which linked list…
A: Given hash function h(key), when inserting an item with key k to the hash table A, which linked list…
Q: If the last index of a hash table is p - 4, where p is a positive integer value, what is the size…
A: A hash table is implemented as an array of buckets or slots. Let the size of hash table be N. We…
Q: : Which of the following data structures requires more than constant average time for insertions?…
A: Actually, the answer has given below:
Q: D. Which one of the following hash functions on integers will distribute keys most uniformly over 10…
A: Answer: The correct answer is option (b) h(i) =i3 mod 10 Below is the Explanation:
Q: In each example, when would you use a hash and when would you use an array? Counting the…
A: We have a better choice-hash, so we will use hash to count the number of occurrences of an IP…
Q: Binary Search BinarySearch(A, key) 1. mid e (low + high)/2 2. while (A[mid]!=key) and ( lowA[mid])…
A: This question is from the subject data structure where we have to run the psudo code of binary…
Q: How do you read, delete, or search a list of user id and passwords using a BST (Binary Search Tree)?
A: Binary Search Tree is a one-site binary tree data structure with the accompanying elements: The…
Q: The hash key of the value 30 in the following hash table is: 1 3 6 7 8 18 2 93 13 30 24 88 53 O 5 O…
A: Hash table is a data structure used to store value. It consists of 2 main components: Key and Value.…
Q: For an alphabet of size R, N total keys, and an average key length of L: (a) What is the minimum…
A: In an R-way search layer, the minimum number of connections is R - 1. In an R-way search layer, the…
Q: From the material that we discussed in the lecture about the cryptographic hash function, answer the…
A: Cryptographic hash functions are collision-resistant one-way functions, with which it is not…
Q: If this is the hash of a certain block below, what are the first 6 characters of the hash of this…
A: Hashing: Hashing is generating a value from a string of text the usage of a mathematical function.…
Q: write a php code to get the hash of a user entered string using the MD5 Message-Digest Algorithm
A:
Q: Assuming that a hash table uses separate chaining to address collisions, which of the following data…
A: Separate Chaining is one of the techniques that is used to resolve the collision. It is implemented…
Q: Which of the following types of modifications to a block chain data structure can be detected by…
A: - We need to highlight the correct option which follws with modification to a blockchain. The…
Q: 1. Insert the contents of the two hash tables in the boxes below. The size of the hash table is 9.…
A: Actually, given hash function H(k)= k mod 9 The given values 18,16, 10, 7,26
Q: Which of the following statements about hash pointers in Blockchain is CORRECT? A. A hash pointer…
A: The answer has given below:
Q: Mr. Akbar is senior software developer working on an ecommerce website he wants to add the following…
A: Actually, given information is: Mr. Akbar is senior software developer working on an ecommerce…
Q: Which of the following statements indicate termination of probing of the buckets when searching for…
A: which of the following statements indicate termination of probing when search for item in hash table…
Q: Which of the following is the suitable answer for the Dynamic Hashing? O The hash table is not used…
A: A hash function is any function that can be used to map a data set of an arbitrary size to a data…
Q: What is the shape of a BST that is O(n) to delete the root? Draw an example with at least 8 nodes.
A: Here in this question we have given a BST and we have asked to find the shape of BST such that…
Q: Research perfect hash functions. Using a list of names (classmates, family members, etc.), generate…
A: Algorithms are the set of the rules or the instructions that are used for solving of the complex…
Q: Q13. Which of the following types of linked lists is faster in the search process? O Singly Linked…
A: In system, A generic type of collection, which is defined in programming language is known as Linked…
Q: Q13. Which of the following types of linked lists is faster in the search process? * Singly Linked…
A: Please refer below for your reference: The correct answer is b
Q: Which of the following is true of SHA-256 hash function? A. It has been proven not to have a…
A: The SHA-256 algorithm is one of version of SHA-2 (Secure Hash Algorithm 2), which was created by…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- In BASH, how do you make it so your script can deal with both absolute and relative paths?Can someone explain this code segment to me ? <?phpsession_start();extract($_SESSION);foo($_SESSION["bar"]);echo $bar;function foo($bar) {$bar = 1;};?>If we only want to download a file if the Web server has a newer version than the one the client has already cached, we can attach the header…Group of answer options If-Modified-Since Time-to-live Expires Out-of-date
- How to remove the item from the cart if the quantity is 0? I have included my code below that I am confused about how to implement this on. <?php session_start(); $page = 'cart'; //DATABASE CONNECTION INFO include_once ('includes/database.php'); include_once ('includes/header.php'); if(!isset($_COOKIE['loggedIn'])) { header("location: login.php"); } if (isset($_POST['update'])) { for ($x = 0; $x < sizeof($_SESSION['quant']); $x++) { $quant_id = 'quant_'.$x; if($_POST[$quant_id] > 0) { $_SESSION['quant'][$x] = $_POST[$quant_id]; } elseif($_POST[$quant_id] == 0) { //HOW DO I REMOVE THE ITEM FROM THE CART IF QUANTITY IS = 0? } else { echo "Quantity must be greater than 0 to purchase."; } } } if(isset($_POST['remove'])) { //HOW DO I REMOVE THE ITEM FROM THE CART IF THE "REMOVE" BUTTON IS CLICKED? } if(isset($_POST['submit_order'])) {…The requirement is as follows: to make aRероsіtоry/dіrесtоry syոсhrоոіzеr: сlіеոt-sеrvеr аррlісаtіоո whісh іs сараblе tо syոсhrоոіzе thе lосаl сhаոgеs tо а rеmоtе fоlԁеr. Сhесk ԁrор-bох fuոсtіоոаlіtydoes the following meet this requirment? https://github.com/hussain0613/Directory-Compare-and-Syncfurthermore, please explain each part of the material and how it accomplishes synchronization - explain what techniques it usesRewrite the same code with a different logic make sure you have the same output. <?php$cookie_name = "user";$userID = $_COOKIE[$cookie_name];if(!isset($_COOKIE[$cookie_name])){ echo "Please login in first!<br>"; exit();} include "dbconfig.php";$conn = new mysqli($hostname, $username, $password, $dbname) or die($conn->connect_error);$name = $_POST['name'];$description = mysqli_real_escape_string($conn, $_POST['description']);$term = mysqli_real_escape_string($conn, $_POST['term']);$enrollment = $_POST['enrollment'];//Query course name$Rid = '';$userGivenFacultyID = $_POST['Fid'];$userGivenRoom = $_POST['Rid'];$queryRid = "SELECT Rid FROM TECH3740.Rooms WHERE CONCAT(Building,Number) like '%$userGivenRoom%' ";$resultRid = mysqli_query($conn, $queryRid);$rid_row_ct = $resultRid->num_rows;if($rid_row_ct = 1){while($ridRow = $resultRid->fetch_assoc()){$Rid = $ridRow['Rid'];}} $queryRoomSize = "SELECT Size FROM TECH3740.Rooms WHERE Rid = $Rid";$resultRoomSize =…
- Which of the following types of modifications to a block chain data structure can be detected by someone who holds a hash pointer to the latest block (select all that apply) ? A. Insertion of a block. B. Deletion of a block. C. Re-Ordering of a blocks. D. Tampering of data in a block.Let your key be the IP address 234.10.90.0 and you want to hash it and then put it in a slot in the hash table with size 257. Do this using Modulo Primes Method and Polynomial Hash. Write all the details.MD5 hash can be applied to which of the following data streams? .ppt file .doc file .dll file all of the above
- given the chunk codes, what will be printed on screen? intx=5; x= x+6; x++; print("%d", x);Since we're on the subject, why don't you bring up the concept of "Reuse" as well as the "host-target" phenomenon?What exactly is a fork on the blockchain? Explain the difference between the two types of forks.

