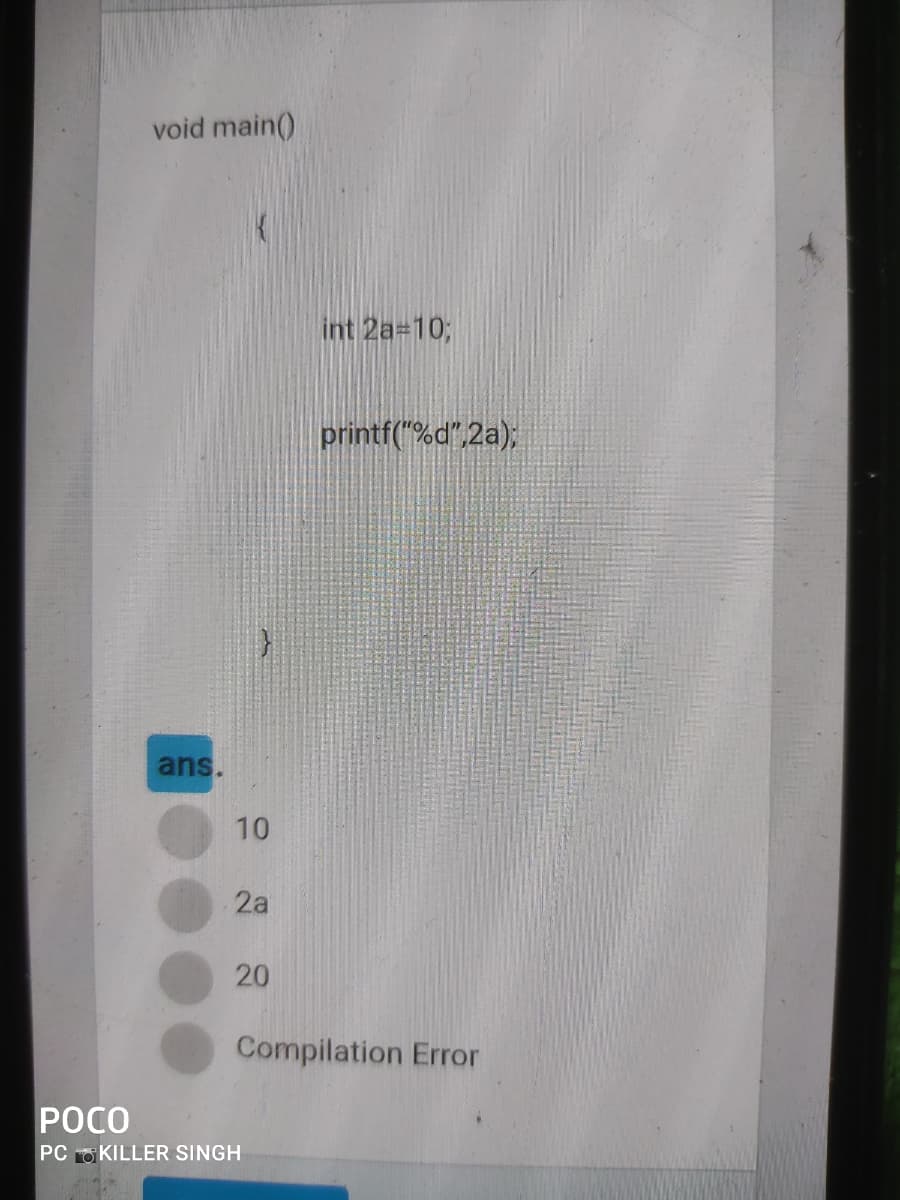
void main() int 2a-103; printf("%d",2a); ans. 10 2a 20 Compilation Error
Q: Explain the difference between Harvard computer architecture and von Neumann computer architecture.
A: INtro Explain the difference between Harvard computer architecture and von Neumann computer arch...
Q: There were a lot of things in the first electronic digital computer.
A: Introduction: ENIAC was the first programmable general-purpose electronic digital computer, develope...
Q: Write a multithreaded program that calculates various statistical values for a list of numbers. This...
A: The answer is given below:-
Q: magnitude and direction of the friction force u
A: Here we have to determine magnitude and direction of frictional force
Q: Draw the ER diagram of the following scenario with their attributes: 1) A team consists of many pla...
A: Below is the answer to above question. I hope this will be helpful
Q: What is an abstract class?
A: abstract class: abstract class are that class which contains both abstract and non-abstract methods ...
Q: Using a binary search tree, store the words and keep count of number of occurrences per word. The ma...
A: Include a header file. Take the string as input and pass it to the function of count occurrence. Ins...
Q: write c programming in raspberry pi # Write the command to copy the information from info.txt to th...
A: Lets see the solution in the next steps
Q: Implement a combinational circuit with three inputs x, y, and z and three outputs A, B, and C. When ...
A: Combinational circuit with three inputs x, y, and z and three outputs A, B, and C are as follows:
Q: What is an abstract class?
A: abstract class: abstract class are that class which contains both abstract and non-abstract methods ...
Q: What is an abstract class?
A: According to the information given:- We have to define an abstract class
Q: s chapter, we talked about four types of RAM. Name th
A: Lets see the solution.
Q: What is the point of having a motherboard?
A: answer is
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position...
A: Internet of things is a system of interrelated computing devices which are provided with the unique ...
Q: What is the distinction between a White Hat and a Black Hat Hacker?
A: Introduction: While white hat hackers look for and solve security flaws in a system, black hat hacke...
Q: Vx E N, x? + x + 41 € P .
A: Let P be the set of prime numbers. Prove or disprove the following statement:
Q: #include int main() { int a = 50; int ans = a++ + ++a + a++ + ++a; printf("%d", ans); ...
A: As given, we need to find out the output of the given code. The given code is - #include <stdio.h...
Q: What exactly is dual-channel memory architecture, and how does it function?
A: Introduction: Computer Memory: In computer science, several forms of memory are utilized. Memory is ...
Q: Decrite how web caching Can reduce delary in recimng a reguested btject
A: Web caching is a process of storing the data for reuse, such as a copy of a web page served by the w...
Q: Write a C program which uses Scanf() to take a test integer (x) which will create the following arra...
A: For taking user input for value x, the scanf() method is used having two parameters. The first param...
Q: If you wanted to know the position of the letter v (i.e. return 2) in the String str containing the ...
A: A String is a pre defined class in Java which has various methods in it to perform the operations on...
Q: Sort the following in order of asymptotic order: f1(n) = n" f2(n) = nvn f3(n) = 2" f4(n) = fa(n/2) +...
A: The increasing order of the asymptotic functions is: constant < logarithmic < root < linear...
Q: Regardless of how user level threads are implemented, if a programme has two or more user level thre...
A: Introduction: Kernel: A kernel is the heart of a computer's software or operating system. Provide a ...
Q: Please don't copy Programming language used : Groovy Write a program in Groovy that retrieves a URL...
A: The answer is given below.
Q: Explain why web application security is so important. What might go wrong with an unprotected applic...
A: Web security is essential for preventing programmers and digital swindlers from obtaining critical a...
Q: What is the output of the following code. Enter the numbers with only one space between them for(int...
A: the answer is
Q: program controls
A: A program is a set of logical instructions that is developed in order to obtain a solution to a prob...
Q: What is the distinction between data, information, and knowledge, and can you give some examples of ...
A: Introduction: In its most basic form, data consists of raw alphanumeric values. When data is process...
Q: Write a C Program to demonstrate pointers to functions in a menu-driven program. The program should ...
A: The solution is given below for the above given question:
Q: /** * This class will use Nodes to form a linked list. It implements the LIFO * (Last In First Out...
A: Here, I have to provide a complete solution to the above-given program.
Q: Answer this question fast
A: SUMMARY: - Hence, we discussed all the points.
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position...
A: According to the information given:- We have to define the internet of things on our everyday lives ...
Q: Make sure to list at least two things about the Intel P965 Express chipset.
A: I have written few things about Intel P965 Express Chipset.
Q: When did the first flash drive appear?
A: Introduction: Flash Drive: An external hard drive, often known as a flash drive, is a portable dev...
Q: Explain how you would choose which of TPCC, TPC-H, or TPC-R best fits the application.
A: TPC-C:- TPC-C simulates a complete computing environment where a population of users executes transa...
Q: What is an abstract class?
A: abstract class: abstract class are that class which contains both abstract and non-abstract methods ...
Q: If you wanted to know the position of the letter v (i.e. return 2) in the String str containing the ...
A: A String is a pre defined class in Java which has various methods in it to perform the operations on...
Q: Create a list of two vectors (dog, cat, mouse) and (True, True, False) called a.list. Name the vecto...
A: import numpy as np animal = np.array(["dog", "cat", "mouse"]) pet = np.array([True, True, False]) #C...
Q: Explain how you can improve the theoretical capacity of a process?
A: Since you have asked multiple questions so we have provided the answer of first question. If you wan...
Q: Juestion:: and Q are two processes that share a set of variables that is common. The variable includ...
A: Introduction: In this case, either process can run first. A procedure may also be preempted by anoth...
Q: What happens to a wireless signal when it encounters a massive obstacle?
A: Introduction: Wireless networks are network systems that are not physically linked to one another. ...
Q: In this problem we will work through a round of DES. For notational simplicity, assume it is the fir...
A: Actually, given question regarding DES.
Q: i am getting whitespace error on output : I-290 is auxiliary, serving I- 90 going east/west. it s...
A: Summary after fixing the code, I have provided PYTHON CODE along with SCREENSHOT OF CODE ...
Q: Q4. Explain why few operating systems currently use many-to-one threading model.
A: Many of the user threads are mapped to a single kernel thread in the many to one model. Since the us...
Q: With the key at 3, did quick search or linear search take less iterations? Why? Turn on the debugge...
A: Linear search: Design a function that search an arrays arr[] with n elements for a given element x. ...
Q: What will be the impact of the internet of things (IoT) on our everyday lives? Justify your position...
A: INTRODUCTION: Unique IDs are supplied for each of the interconnected computer devices in the Intern...
Q: Write a procedure Push (x, S) that pushes element x onto stack S, where S is one or the other of the...
A: First of all we should know why two stacks start from the opposite side.This is because so that we c...
Q: What is the difference between a device drive and a network interface card?
A: Intro What is the difference between a device drive and a network interface card?
Q: Review the 8-puzzle problem. Consider that the initial state is 1 3 4 8 2 7 6 5 and the goal state...
A: 8 - puzzle problem The problem. During the 1870s, Noyes Palmer Chapman devised and popularized the 8...
Q: This is how you write a CALL statement that calls a procedure called MyProc in an outside link libra...
A: Introduction: Use the ESQL CALL command to execute a procedure stored in a database. A CREATE PROCED...
Step by step
Solved in 2 steps with 2 images

- T/F 1. Only primitive forms may be returned by Java methods.Code thisc++ computer language what is the output of the following code segment? int main() { int myarray[]={-200, 33, 89, 50, 44}; sub(myarray, 5); for(int i =0; i<5; i++) cout<<myarray[i]<<" "; cout<<endl; system("pause"); return 0; }; void sub(int arr[], int z) { for(int i =0; i<z; i++) arr[i] = arr[i] - i; }
- Fibonacci write 4 function (Recursion version, Memoization version) (Iterative version, Tabulation version) and main function to test the 4 functions ,, by c++.Please help me with this using java Please comment each line of code and use recursionPlease use easy logic with proper indentations and comments for understanding!. Coding should be in C++. 3. Define a class which stores up to 10 integer values in an array. The class should also define the following 4 public methods: setNumber – accepts an integer value to store in the array. The value is stored in the next available element of the array (first call to the method stores the value in element 0 with the second call storing the value in element 1.) The method returns true if there is room in the array and the integer was successfully stored. Returns false otherwise. clear – removes all values from the array so that the array can be reused. displayNumbers – displays the values currently stored in the array. getStats – determines the largest, smallest, and average of the values currently stored in the array. These values are returned to the caller via reference parameters. All methods should produce correct results regardless of the order in which…
- Please help me with this using java and recursion. Please comment each of the code. amAs well as post an image of the program working 1) create a sierpenski triangle (Image 1) 2) create a sierpenski carpet (image 2)C++ A matrix is a rectangular array of numbers that is arranged in a two-dimensional table. Matrices have numerous applications in computer systems. Matrix structures are examined in computer memory, graphics, and cryptography. The Hill cipher, for example, makes use of matrix inversions to encrypt and decrypt data. The intent of this problem is to develop a C++ program that computes and displays the inversion of a 2 x 2 matrix. A matrix is said to have the dimensions m x n if it has m rows and n columns. A square matrix has the same number of rows as columns, and is therefore said to have m x m dimensions. Matrix M shown below is an example of a 2 x 2 matrix. The inverse of a square matrix, M-1, is defined by the equation M(M-1) = I, where I is called the identity matrix. I is a square matrix that is all zeros except for ones along the main diagonal from the upper left corner to the lower right corner. I for a 2 x 2 matrix is: Multiplying a square matrix by its inverse will always…PythonDesign a recursive function that accepts an integer argument, n, and prints the number 1 up through n.



