Welcome to Know Your Loan Company Enter the loan amount Enter the paymment amount Month 1 Balance is 901 Month 2 Balance is 801 Month 3 Balance is 701 Balance is 601 Month 4 Month 5 Month 6 Month 7 Month 8 Month 9 Month 10 Balance is 1 Month 11 Balance is 0 Your Original Loan Amount was: 1001 Thank you for using this program Balance is 501 Balance is 401 Balance is 301 Balance is 201 Balance is 101 1001 100
Q: . The set of binary numbers has 0's in all even positions. Σ= {0,1}.
A: Given : From the above description, we can say the language contains a set of all strings that can…
Q: Determine the network topologies of the five most popular kinds of networks that are used today. Of…
A: Network Topology: Topology of stars All nodes are linked to a central hub through cables in a star…
Q: In the subject of software engineering, are there any topics considered as fundamental that are not…
A: The fundamentals of software engineering is the division of work into distinct phases that don't…
Q: Is there a way to protect vehicle-to-vehicle communication by using security approaches and…
A: The answer is given in the below step
Q: A farmer had to remove a field of pulpwood trees because of Moore's Law. How would you use systems…
A: Moore's law it is stated that number of transistors which can be placed in a square inch on an…
Q: Write a program in c++ to calculate the power of a number using resursion. Call the function power…
A: Given that, it is asking for program to calculate power of a number using recursion in c++ language.…
Q: Exactly how and when did the internet of things come to be, and what is its present state?
A: Internet of Things: The Internet of Things, or IoT, is the name given to the rapidly expanding…
Q: ose we create a binary seard
A: Solution - In the given question, we have to create the binary search tree of the given numbers and…
Q: Today's mobile devices vary and are similar to previous generations of personal computers in what…
A: The Answer is in step2
Q: Give two examples of commonly used fingerprinting algorithms.
A: Fingerprint algorithms: An arbitrarily big data item (such as a computer file) is mapped to a much…
Q: Step1-Study the scenario below and create a Java Program for Builders Warehouse, The program must…
A: A linked list is the collection of nodes each containing two fields, i.e., data and the pointer…
Q: What specific goals do we want to accomplish via the use of AI? Each kind of domain has its own set…
A: Given: What specifically do we want to accomplish with artificial intelligence? There are two…
Q: a) Give an example of a string that is neither in the language of R nor in S. b) Give an…
A: Given R = (0*10+)+1* Given S = (1*01+)* * means zero or more occurrence + means zero or more…
Q: A control's property determines whether or not it appears on the form during runtime.
A: There are many controls accessible in visual fundamentals. The planning form is utilized. Controls…
Q: Was the Internet of Things (IoT) always this big, and where does it stand now?
A: Start: IoT is a natural programme for linked devices that exchange data via a wired or wireless…
Q: It's conceivable that the principles of software development are missing. Explain?
A: Answer: A set of executable instructions called a programme is utilised to carry out a particular…
Q: In your view, which of the following characteristics should an ideal programming language include,…
A: Fingerprints consist of a series of ridges known as friction ridges. Under the epidermis are sweat…
Q: write a function that returns the name of the root property that a particular integer lives in. *…
A: Root Object Properties is refers to the root is the graphic objects in the systems. There is the…
Q: list two recommendation that would help to solve this issue
A: This is very simple. To start practicing the new education system (online education) in poor areas…
Q: Is it true that computer technology and other forms of technical progress are almost…
A: To support training technologies, computer technology combines computer hardware with…
Q: The diagram below shows a multiple inheritance case where Student is duplicated. Write class…
A:
Q: The life cycle of system development is broken up into five separate stages, each of which is highly…
A: An effective System Development Life Cycle (SDLC) should result in a high-quality device that…
Q: What are the most significant differences that set a Disruptor apart from an Interrupt? It is…
A: How Does a Disruptor Differ from an Interrupter? The word "interrupt" refers to a signal sent to the…
Q: In the following two words, identify two problems that you notice with the information systems that…
A: Describe two flaws you notice with existing information systems in the following two lines. Network…
Q: It's difficult for a software engineer to accurately estimate the cost of a project.
A: It is challenging to evaluate a project accurately since the projects have different dynamic…
Q: When creating software system models, what points of view should be considered?
A: By definition, a software-intensive system is one in which software has a significant effect on the…
Q: What is the return code for this procedure?
A: The CPU of the computer runs the code when a procedure is called. The method's calling code will…
Q: In your interface, provide a label and 3 buttons, and a timer. Initially, your label will display…
A: Solution Below in this program for javax framework BasicMain.java package basic Window; import…
Q: Is it feasible engineering to condense the ultimate purpose of software into a few sentences?…
A: Purpose of software: Software's main goal is to transform data into information. Information is…
Q: There should be a discussion on OOP concepts What is the degree to which they are accounted for in…
A: object-oriented programming: A computer programming paradigm known as object-oriented programming…
Q: What is the correct combination of function and parameter to create a pie chart in Matplotlib?
A: Please check the step 2 for solution
Q: The graphics card is the most power-hungry part of a high-end gaming PC.
A: Given: Which component of a high-end gaming computer uses the most power on average? Answer: A…
Q: Security breaches and data loss are made more likely by troubleshooting
A: It is possible for security breaches and data loss to occur as a consequence of troubleshooting.…
Q: nstruction execution cycle"
A: What is meant by the term "instruction execution cycle"?
Q: Oues. W Wap lap Consol. class. in jana that demonstrates the
A: A constant is a value that, once assigned, cannot be changed. The constants are not directly…
Q: In what ways are horizontal and vertical partitioning different?
A: Vertical and horizontal partitioning are beneficial. Why? Horizontal information partitioning means…
Q: What sort of future influence will artificial intelligence have? What software based on artificial…
A: Artificial intelligence (AI) is intelligence shown by machines, instead of the normal intelligence…
Q: In order to be a successful systems analyst, what specific talents and areas of knowledge are…
A: Whether professionally certified or not, a System Analyst should possess the following skills:…
Q: Why is it essential to use structured programming? What core ideas are necessary to make a computer…
A: Definition: In contrast to using straightforward tests and jumps like the go to statement,…
Q: For what reasons are foreign keys so critical to the integrity of a database? I'd want to know what…
A: Unusual key: A relational database relation is an object or set of entities that creates a…
Q: The four most important functionalities of the operating system should be included.
A: system of operation: The operating system serves as a channel of communication between the user and…
Q: How much power is required to operate a powerful gaming PC?
A: Solution: Name a premium gaming computer component that will probably use the most power. Gaming PCs…
Q: Can you provide a brief explanation of what a "nested procedure call" means?
A: Nested Procedure Call: Procedures that don't call other procedures are known as leaf procedures,…
Q: locations of substations
A: A substation is an electrical system with high-voltage capacity and can be utilized to control the…
Q: Is expanding one's knowledge of programming languages by the study of other languages advantageous…
A: Programmers can connect with computers by using a programming language (developers). It is a set of…
Q: Power-hungry components abound in gaming PCs. At its peak, how much power does it have?
A: Introduction: Buying a high-quality power supply is essential if you want to construct your own…
Q: When someone says that the internet is like a cloud, what exactly are they referring to? What is the…
A: Overview: Global data and communication access is the main objective of the Internet. The…
Q: An information system's evolution may be broken down into a number of stages, and one of these…
A: According to the information given:- We have to define the number of stages, and one of these…
Q: Interprocess communication in UNIX is the most efficient technique of doing this task.
A: Given: The coordination of tasks among working processes is referred to as interposes communication…
Q: f ALE=0, that mean the numbers on A7-A15 ar address bus
A: Lets see the solution.
how do i create this in gaddis pseudocode in flowgorithm
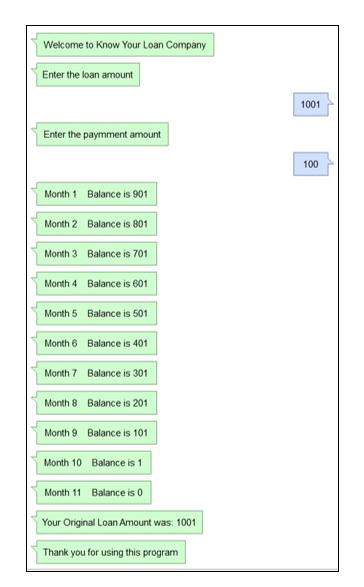
Step by step
Solved in 3 steps with 3 images

- A company has various rules for how payments to suppliers are to be authorized.Some payments are in response to an approved purchase order. For approved purchase orders under $5,000, the accountingclerk can immediately issue a check againstthat purchase order and sign the check. Forapproved purchase orders between $5,000and $10,000, the accounting clerk can immediately issue a check but must additionallyobtain a second signature. Payments for approved purchase orders over $10,000 alwaysrequire the approval of the accounting manager to issue the check as well as the signature of two accounting clerks. Payments thatare not covered by a purchase order that areunder $5,000 must be approved by the accounting manager and a departmental manager who will absorb the cost of the paymentinto that department’s budget. Such checkscan be signed by a single accounting clerk.Payments that are not covered by a purchaseorder that are between $5,000 and $10,000must be approved by the accounting…Case Study:Consider an online shopping website that maintains a shopping cart. A user can search productsand place order and can make payment for it either online or cash on delivery. If a user placean order of amount RS 2500 or above he gets home delivery of the product for free, otherwisehe has to pay Rs 250 extra for home delivery. There are different types of users based onmembership Guest User (No membership), Gold User, Platinum User. Guest user doesn’t getany discount, Gold user gets 5% off on every product, Platinum User get 7.5% on everyproduct. Question No. 2: Draw Activity diagram for the case study above ? Question No. 3: Draw Class diagram for the case study above. ?can you make ER Diagram with Crow`s foot method about library system. The rule: 1. A member can borrow more than one book at a time 2. A member can have more than one phone number 3. A book can have more than one author 4. All book registration, member and borrowing processes can only be done/served by officers 5. Data for books, members and officers are stored with a unique id, so no id is the same.
- Label each phrase as either interpretation sharing, projection sharing, or fact sharing. Note: each information sharing type is used once. Diesel is leaking from the ship onto the dock. Answer (circle one): interpretation sharing, projection sharing, fact sharing. There is a fire station near the diesel leak. Those firefighters have been trained to respond to small diesel spills. Answer (circle one): interpretation sharing, projection sharing, fact sharing. If the ship leaks more than 10,000 gallons of diesel, then we will need to send in additional firefighters and specialized equipment trucks through Route B. Answer (circle one): interpretation sharing, projection sharing, fact sharing.Please solve this one I need help: Auto Workshop is a vehicle service centre located in the city ofMuscat, which provides vehicle maintenance/repair services.The charges of vehicle maintenance/repair are based on the type of theservice.Details of charges are as follow:Basic Tuning: 50 OMRSoftware Re-installation: 60 OMRParts Replacement: 100 OMRBody Paint: 120 OMRThe workshop offers 10% discounts to the customers who have membershipof the service centre.You are required to draw a flow chart diagram and write a C++ computerprogram that takes customer’s name, car plate number, membershipstatus(Y/N) and the required service (mentioned above). The programoutputs the input data and maintenance charges based on the serviceprovided by the service centre with discount, if applies.Question 10 sis Good always tell the truth Bad always lies. use a truth table to determine what type each person is or if their status cannot be determined.A: “I am Good or B is Bad”B: “A is Bad if C is Good”C: “I am Bad or A is Bad only if B is Good" Please show work and address all parts Don't ignore any part all part work u
- Exercise 1 1. Use the following table to answer the questions below. Homeroom# First Name Last Name T-Shirt Size Payment Method 105 Derek MacDonald Large Cash 105 Nathan Albee Medium Check 105 Sidney Kelly Medium Check 105 Christiana Chen Medium Check Bounced 105 Melissa White Small Debit Card 105 Esther Yaron Small Pending 110 Kris Ackerman Large Credit Card 110 Matt Benson Medium Money Order 110 Gabriel Del Toro Medium Cash 110 Lilian Arnold X-Large Cash 135 Anisa Naser Small Check Bounced 135 Davi Bell X-Large Credit Card 220-A Asher Hepburn Large Pending 220-A Brigid Ellison Small Cash 220-A Christopher Peyton-Gomez Small Check 220-B Avery Kelly Large Money Order 220-B Samantha Bell Medium Check 220-B Michael Lazar Small Cash 220-B Malik Reynolds Small Cash 220-B Wendy Shaw Small Cash 1. Sort by Last Name (desc), then T-Shirt Size (asc) and then Payment Method (desc). 2. Freeze…There is only 1question which have 2 subparts. Do it properly if know the concept actually, otherwise i will report your account. Reward :3 upvots from me. Do fast i dont have much time. Do it in 30 minutes. If you don't know how to solve then skip it. Dont click on reject. If you clicked on reject i will report your account to Bartleby. There is no honour code violation in this question.Please solve the (ii) part of the question For this you have to read the whole question only The dining philosopher problem is a classic problem in deadlock management. The problem can be described briefly as follows. There is a round table around which a total of five philosophers are sitting. There are also a total of five plates in front of the philosophers and five forks, one each beside each plate. A philosopher can only eat if s/he can get two forks lying beside the plate. The philosophers do not have any means of communicating with each other to control access to their forks. A situation where none of the philosophers is able to eat because they are all able to access a single fork (but not both) is called deadlock. The goal is to design a protocol of choosing the forks among the dining philosophers so that no deadlock occurs. 1. Assume that the philosophers need to access only a single fork to eat. In addition to the forks, the philosophers also need have access to any one of…
- 1. Which of the following statements about Goofycoin is INCORRECT? A. A designated entity called Goofy can create new coins whenever he wants and these newly created coins belong to him. B. Whoever owns a coin can transfer it on to someone else. C. Goofycoin can address the double spending issue. 2. Which of the following statements about ScroogeCoin is INCORRECT? A. A designated entity called Scrooge publishes an append‐only ledger containing the history of all the transactions that have happened. B. Scrooge can build a block chain, which is a series of data blocks, each with one transaction in it. C. ScroogeCoin can address the double spending issue. D. ScroogeCoin can implement coin minting, transaction, and IDs' assignment in a fully decentralized way.Create an ER Diagram for the following scenario. Please state any assumptions you have madein your answer.A university offers a Mathematics program. This program can offer any amount ofcourses in a semester. Each course has a roster limit, location and time slot. A studentcan be registered for any number of courses in a semester but to register for a coursethey must have a valid student ID and address. Each course is assigned a singleprofessor. Only on completion of a course, a student receives a final grade for thatcourse.Correct answer will be upvoted else downvoted. Computer science. the proprietor needs to eliminate a few (perhaps zero) sunflowers to arrive at the accompanying two objectives: At the point when you are on a vacant cell, you can stroll to some other void cell. All in all, those unfilled cells are associated. There is actually one basic way between any two void cells. All in all, there is no cycle among the vacant cells. You can stroll from an unfilled cell to another in the event that they share a typical edge. Could you kindly give the proprietor an answer that meets every one of her prerequisites? Note that you are not permitted to establish sunflowers. You don't have to limit the number of sunflowers you eliminate. It tends to be shown that the appropriate response consistently exists. Input The input comprises of different experiments. The main line contains a solitary integer t (1≤t≤104) — the number of experiments. The portrayal of the experiments follows.…



