What is the correct term for the situation when the compiler cannot make a decision about the specific behaviour that should be executed by an object and this behaviour is instead determined at runtime? Early Binding Inheritance Encapsulation Polymorphism O Abstraction O Late Binding
What is the correct term for the situation when the compiler cannot make a decision about the specific behaviour that should be executed by an object and this behaviour is instead determined at runtime? Early Binding Inheritance Encapsulation Polymorphism O Abstraction O Late Binding
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter9: Advanced Modularization Techniques
Section: Chapter Questions
Problem 19RQ
Related questions
Question
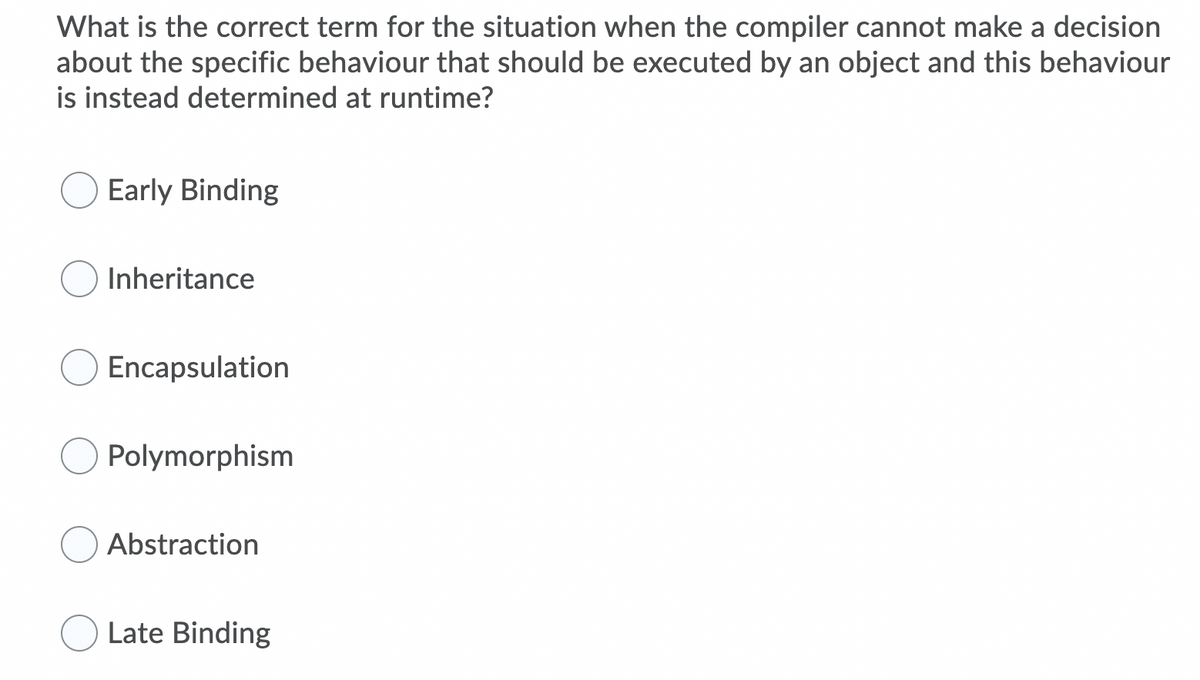
Transcribed Image Text:What is the correct term for the situation when the compiler cannot make a decision
about the specific behaviour that should be executed by an object and this behaviour
is instead determined at runtime?
Early Binding
Inheritance
Encapsulation
Polymorphism
Abstraction
Late Binding
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,