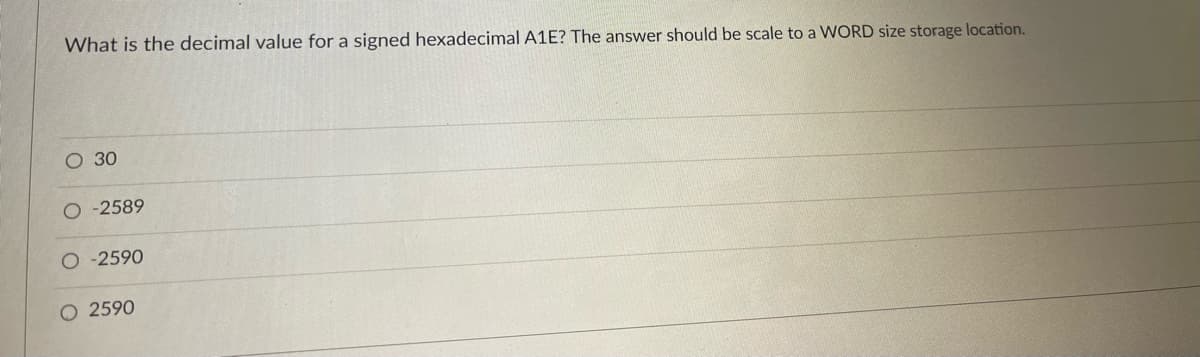
What is the decimal value for a signed hexadecimal A1E? The answer should be scale to a WORD size storage location. O 30 -2589 -2590 O 2590
Q: Are there any examples or descriptions of the operating environment you'd like to give?
A: The environment in which software applications are executed is the operating system or the IAE. For…
Q: sms of a more complicated kind for the protection of information incorporated in the OSI security…
A: To assess effectively the security needs of an organization and to evaluate and choose various…
Q: 1) Add the element 8 to the end of the list numbers = [1,2,3,4,5,6,7]
A: Use append function to add elements at the end of the list Code:…
Q: In what Ways Does a Computer System Differ from Other Systems?
A: The word "system" is abbreviated as SYSTEM. The system consists of a connected and planned set of…
Q: ently utilised by embedded syst
A: Introduction: A watchdog timer (WDT) is a safety mechanism that restarts the system if it crashes…
Q: please solve question 9 python
A: The following are the Statement printed in python
Q: Is there any extra software included with the operating system? Give four particular examples to…
A: Answer Introduction Computing devices, such as smartphones, tablets, computers, supercomputers, web…
Q: Q6:Rewrite the following Matlab code using a while loop to avoid using the beak command clc; clear;…
A: Find the required code in matlab given as below and output :
Q: Which parts of the information system are regarded organizational, managerial, and technical?
A: Given: Organizational, administrative, and technical factors all have a role. Senior managers often…
Q: Which of these is true for Single Layer Perceptrons? O Have exactly one hidden layer O Cannot be…
A: SLPs are the most basic artificial neural networks.
Q: cles and bottlenecks the framework will encounter when developed, then examine what issues and…
A: Introduction: A bottleneck occurs when a single or small number of components or resources limit…
Q: How would you describe information systems in terms of their managerial, technological, and…
A: Introduction: Administrative, organisational, and technological considerations Senior management…
Q: Provide a high-level overview of the process through which users are able to charge their mobile…
A: Introduction: When it comes to USB charging, there is always one host and one device; power is…
Q: Describe the steps involved in the program's analysis phase
A: Introduction: In every project, analysis is the process of defining the characteristics of the…
Q: Architecture and computer organization are two separate concepts in the context of computers.
A: Given: Computer architecture explains what a computer performs and computer organisation how.…
Q: Why do we have more than one activity_main.xml file? Alternative folders for resources for different…
A: In given figures, we have more than one activity_main.xml.
Q: Errors may occur in wireless networks because of their vulnerability to flaws. Identify three of…
A: Given: There are issues with the internet connection. It might be aggravating when you can't connect…
Q: Wireless networks perform poorly than cable networks for a variety of reasons. What can be done to…
A: Introduction : Wired Network : A wired network is where you physically plug your computer or…
Q: Describe the ways in which the performance of peripherals and communication lines have improved in…
A: As a replacement for the ISA the PCI i.e. Peripheral component interconnect was developed which was…
Q: Explain the difference between ASCII and Unicode in simple terms.
A: Unicode and ASCII are the two most widely utilized character encoding formats now in use worldwide.…
Q: make a simple java program that can calculate the area of a circle add this button: 1.…
A: The code implementation is done in the Java AWT. The answer is given below.
Q: As an example, have a look at the file system in your favourite operating system of choice. a. How…
A: File system is the part of the operating system which is responsible for file management. Create…
Q: A forensic picture can be copied from a hard drive with a capacity of 1 terabyte to a flash drive…
A: Given: A hard drive is a nonvolatile data storage device that is used to store large amounts of data…
Q: Wireless networks face a broad variety of challenges because of their inherent features. Three of…
A: INTRODUCTION: Today's industrial enterprises depend on robust, secure wireless networks to operate…
Q: We are not competent to describe how operating systems carry out procedures.
A: Answer: An Operating System offers types of assistance to both the clients and to the projects. It…
Q: Construct the CFG for the language having any number of a's over the set >= {a}.
A:
Q: Given a positive integer n and a digit d, return the count of the occurrences of the digit d in the…
A: First we will ask user to input an integer and digit whose number of occurrence is to be found out.…
Q: Which one is characteristic of data traffic? ★ Data traffic consumes lots of network resources. Data…
A: For good voice quality, the amount of latency should be less than 150 milliseconds and packet loss…
Q: what decimal number does 1001010 represent?
A: Please refer below for your reference: 1001010 base 2 : Inorder to convert binary into decimal we…
Q: Why is a modem required for computer networks to exchange data?
A: Introduction: Because of this, modems make it feasible for traditional forms of data communication,…
Q: Please provide an overview of the various access technologies
A: As per the question statement, We need to discuss various access technologies.
Q: Q6:Rewrite the following Matlab code using a while loop to avoid using the beak command.
A: here in given question ask for output of matlab code,
Q: Wireless networks face a broad variety of challenges because of their inherent features. Three of…
A: Given: Wireless networks that are reliable and secure are essential to the operation of modern…
Q: Please explain the foundations of effective data entry fields to us. There may be times when these…
A: Intro while this may seem obvious, it is necessary to say. Many illustrations deceive the viewer by…
Q: 6. What is printed by the following when executes? 1 str= "His shirt is red" 2 pos= str.find("is") 3…
A: Solution of question 6: Right answer - Option (D) 1 Explanation - Here find function of string is…
Q: hat exactly is heuristic search? What are
A: Heuristic search is class of method which is used in order to search a solution space for an optimal…
Q: What are social content sites?
A: Social content sites are also known as social media sites. Social media sites are websites and…
Q: Which method is said to be direct ?method Gauss-Seidal method. O Newton-Raphson method. O…
A: Answer the above question are as follows:
Q: +stream fp; item produc; void save_item() { fp.open("database.dat", ios::outlios::app);…
A: Please refer below for your: From line 66 refer below: 1) fp is the file pointer 2) item produc; //…
Q: You plan to create a GitHub workflow that will use the GitHub Script action to automatically post a…
A: About the first work flowGitHub provides the first workflow for a variety of languages and tools.…
Q: explain the use of .length in this statement and the importance of string
A: A string in C language is an array of characters that is ended with a null character (\0). The…
Q: Describe two of the duties that are expected of a device driver.
A: A device driver in computing is computer software that runs or controls a particular device linked…
Q: students = new Student [size]; (the use of dynamic array) *please explain the use of dynamic array…
A: A dynamic array is a random access and variable size list data structure that allows elements to be…
Q: What is the type of traffic imposed by this ACL? HTTP HTTPS DNS Telnet FTP
A: Answer: That type of traffic imposed by ACL : 1.HTTP, 2.Telnet, 3.FTP
Q: 8) Read a number and print the remainder of division by 5. number=input ("Enter a number") print (
A: I am solving only question 8 in Python.
Q: The reliable delivery service provided by TCP is not redundant despite the fact that all Internet…
A: Given: Why is the TCP reliable delivery service not redundant, even if all Internet lines offer…
Q: C++ program Write C++ program to find the summation and the average of all odd numbers between…
A: In mathematics, when a number cannot divide by 2 and produce two equal integer numbers, is called…
Q: A discussion on information privacy and the strategies that may be utilised to improve it.
A: Introduction: The condition of not being exposed to public scrutiny or having your secrets or…
Q: Both the sequential search algorithm and the binary search algorithm have distinct benefits, but…
A: Encryption: Performing the search in a certain sequence. Having a list that is sorted is not…
Q: User manuals, online assistance, and tutorials may all be classified into one of these three…
A: Intro Manuals: This manual describes the system's operations and capabilities, as well as…
Step by step
Solved in 2 steps

- Bytes, which have 8 bits, are often used to group computer memory into different types. How many dist values can a tell? How many different valueytes can two bytes stand for?What decimal value does the 8-bit binary number 10010110 have if it is represented using Excess-M representation? a) If high-order interleaving is used, where would address 37 (base 10) be located? b) If low-order interleaving is used, where would address 28 (base 10) be locatedWhat is the range of unsigned integers that can be represented using 8 bits binary cells? A. -127 to 127 B. -128 to 127 C. -127 to 128 D. 0 to 255 E. 0 to 256
- What distinguishes the numerous unsigned binary formats, other than the underscore character?Using a 4-bit cell to store integers in 2's complement, what is the largest positive integer that can be stored? Question 9 options: A. 15 B. 32 C. 63 D. 31 E. 7What would -0.6 look like in binary using 16 bit real numbers?
- It is common practise to divide computer memory into many categories using bytes, each of which consists of 8 bits. How many dist values can a tell? How many distinct valueytes may be represented by two separate bytes?In an 8-bit binary number, which is the most significant bit (MSB)?Show Steps Please 17. Show how floating-point value 12.5 would be stored using IEEE-754 single precision (be sure to indicate the sign bit, the exponent, and the significand fields): 18. If the floating-point number representation on a certain system has a sign bit, a 3-bit exponent and a 4-bit significand: a) What is the largest positive and the smallest positive number that can be stored on this?system if the storage is normalized? (Assume no bits are implied, there is no biasing, exponents use two's complement notation, and exponents of all zeros and all ones are allowed.) b) What bias should be used in the exponent if we prefer all exponents to be non-negative? c) Why would you choose this bias? 19. Assume we are using the simple model for floating-point representation as given in this book (the representation uses a 14-bit format, 5 bits for the exponent with a bias of 15, a normalized mantissa of 8 bits, and a single sign bit for the number): a) Show how the computer would…
- What is binary code, and why is it fundamental to the operation of digital computers?1.You read the number 11111101111100 from a memory which uses error detection and correction (Hamming algorithm). What was the original correct data word that was written to memory?11. Using a 6-bit cell to store integers in 2's complement, what is the decimal number that stored in the cell as 001110 Question 10 options: A. 12 B. 14 C. -12 D. -14 E. None of the above

