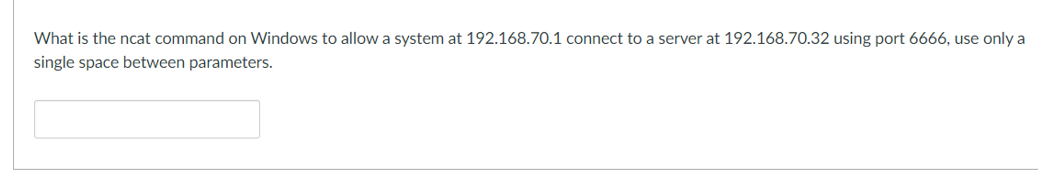
What is the ncat command on Windows to allow a system at 192.168.70.1 connect to a server at 192.168.70.32 using port 6666, use only a single space between parameters.
Q: What is the significance of managing information security?
A: Significance of managing information security : The management of the information security is very…
Q: 6. When a website operator states in its privacy notice that it will not share financial information…
A: Here is your solution -
Q: The difference between laws and ethics in terms of information security is that laws define security…
A: Information security is a critical concern in today's digital age, and it is essential to understand…
Q: In the event that there is a data breach, could cloud-based security mechanisms leave users open to…
A: A data breach is defined as a breach of security leading to accidental destruction, loss, or…
Q: A case study on a recent incident involving an authentication or access control security…
A: According to the information given:- We have to define above case study.
Q: evaluate the whole sphere of insider threats, how and to what extent these threats impact the…
A: Insider threats are defined as any malicious or unintentional activity taken by workers,…
Q: A Cyber Treaty can be paralleled to which treaties defined before it? Group of answer choices…
A: The world has become increasingly interconnected with the rapid development of technology,…
Q: To what end is this Cyber Kill Chain Model being implemented?
A: Dear student, Actually before directly know the purpose of cyber kill chain model, first we need to…
Q: 2) A memory system has a page size of 1024 (2¹0), four virtual pages, and three physical page…
A: The virtual address is a binary number in virtual memory that processes the use of a location in…
Q: 52. Which of the following is not one of the recognized four states of privacy? A. Pseudonimization.…
A: Privacy has been an important part of human life since ancient times. It is about not seeing or…
Q: In the United States, who is officially in charge of cybersecurity policy?
A: In this question we need to explain who is official in charge of cybersecurity policy in the United…
Q: Describe the many meanings that might be attached to the word "terrorism."
A: Cybersecurity refers to the practice of protecting computer systems, networks, and digital devices…
Q: Instructions Research the eight exceptions to information blocking. What are the objectives of these…
A: The 21st Century Cures Act, enacted in 2016, includes eight data protection exemptions that allow…
Q: Cybercrime and society 2) Determine the best Internet-crime prevention methods.
A: Internet crime, otherwise called cybercrime, has turned into a huge danger to people, organizations,…
Q: Talk about the benefits as well as the drawbacks of utilizing symmetric encryption. How exactly does…
A: In this question we need to explain the benefits and drawbacks of symmetric encryption along with…
Q: FS-ISAC stands for?
A: Information of FS-ISAC.
Q: Why You Should Employ the Cyber Kill Chain Model.
A: The Cyber Kill Chain model is a framework that was originally developed by Lockheed Martin to help…
Q: 1. The Children's Online Privacy Protection Act ("COPPA") was enacted to primarily prevent which of…
A: In this question we need to choose the main purpose of Children's Online Privacy Protection Act…
Q: What are the two types of Intrusion Detection Systems that are used to protect data-at-rest and…
A: According to the information given:- We have to define the two types of Intrusion Detection Systems…
Q: For your additional piece of mind, debit cards supplied by banks often include a unique security…
A: Financial institutions need to use encryption and ad hoc management solutions to protect the…
Q: Carry out a quick risk management analysis on your laptop. Determine what you have, what you need to…
A: In the age of the digital era, most of our daily activities are done through computers and laptops.…
Q: CDM stands for?
A: What does CDM stands for in cybersecurity.
Q: 34. Which rule within the HIPAA Privacy Rule requires transfer of only the protected health…
A: In this question we need to choose the correct HIPAA privacy rule which requires transfer of the…
Q: What is the main difference between a "top down" and a "bottom up" approach to information security?
A: Information security is a critical aspect of any organization that deals with sensitive information…
Q: 0. In the healthcare sector, cybersecurity through IoT devices like wireless insulin pumps hich…
A: Correct mcq answer is explained below Please note explaination for incorrect answers is also given
Q: 60. The European Union takes which approach to privacy protection? A. Comprehensive B. Sectoral C.…
A: In this question we need to choose the correct option related to European Union (EU) privacy…
Q: It has an impact on society. 2) Establish which cybercrime prevention techniques are most effective.
A: According to the information given:- We haev to define an impact on society. Establish which…
Q: 4. One of the lessons that can be derived from the Equifax Data Breach is that companies should…
A: Millions of people's personal information was compromised in 2017's huge cyberattack known as the…
Q: What cyber security dangers will you prepare for while creating a MIS information security strategy?
A: In this day and age, information security is turning out to be progressively significant for…
Q: Better and cheaper technology will allow it to be distributed across the global, this is known as…
A: The global technology revolution is defined as the revolution of materials, devices, and…
Q: Which key presumptions and behaviours now make up the overwhelming majority of illegal conduct…
A: The internet is a breeding ground for various types of illegal conduct, which often involve…
Q: We can split the kill chain up into two different types of actions, what are they?
A: What is an information: Information refers to data that has been organized or processed in a…
Q: 66. The Fourth Amendment is intended to curb the issuance of what type of warrant? A. General…
A: A warrant is a legal document issued by a court, judge, or other authorised authority that certifies…
Q: What are the pros and cons of two cyber security regulatory frameworks?
A: In this question we need to explain the pros and cons of two cyber security regulator frameworks.
Q: Explain what you mean by the term "cybersecurity" and why it's so important to put it into effect.
A: Here is your solution -
Q: 37. Which of the following is not an example of an administrative safeguard? A. Trainings for staff…
A: Here is your solution -
Q: What common beliefs and practises define the vast majority of current cybercrime? Please include…
A: Cybercrime refers to criminal activities that are committed using a computer, network, or other…
Q: 40. The act of auditing your data to determine the level of financial and reputational and legal…
A: Dear student, I will provide you most correct answer with detailed explanation and I will also…
Q: Filling out the "FIA's Complaints Registration Form" is required prior to submitting a complaint on…
A: Online criminal activities, also known as cybercrime, encompass a wide range of illegal activities…
Q: On this link: https://nca.gov.sa/legislation?item=182&slug=guidelines-list you can find different…
A: According to the information given:- We have to define Cloud Cybersecurity Controls Policy. Based…
Q: When referring to a specific circumstance, what precisely does it imply when someone says that they…
A: In this question we need to explain the term system security.
Q: Define the firewall's network security function. Explain the term and provide industry-relevant…
A: A firewall is a network security device that acts as a barrier between an organization's internal…
Q: Choose security devices (video cameras, monitoring, Intrusion Protection/Detection systems,…
A: According to the information given:- We have to define choose security devices that you will install…
Q: The options for b is 108,5001,78, 99- choose one The options for a is 99,78,120, none-choose one…
A: The definition of error correction codes communication protocols are designed error detection and…
Q: In a large corporation, what are the typical steps involved in obtaining clearance to update a…
A: Here is your solution -
Q: What specifically is the significance of information security administration?
A: In this question we need to explain the significance of information security administration.
Q: What type of data enrichment can be done on information collected from a honeypot? Geolocation of…
A: According to the information given:- We have to choose the correct option to satisfy the statement.
Q: Why have we seen these advancements in cybercrime occur so recently? Kindly enlighten me as to the…
A: The recent advancements in cybercrime can be attributed to a number of factors. One of the main…
Q: 55. The GDPR replaced which of the following EU regulations? A. Cookie Policy 3. GLBA C. Data…
A: Correct answer is given below
Q: A denial of service attack may interfere with ordinary email in several ways. Put your new knowledge…
A: According to the information given:- We have to define denial of service attack may interfere with…
Trending now
This is a popular solution!
Step by step
Solved in 4 steps
