What is the purpose of conditions in programming? O Used to explain how the program works or functions. These lines are ignored by the compiler during runtime. Conditions are a step-by-step plan to solve a problem. O Conditions are used to perform the same steps over again. O Conditions are used to affect the flow of the steps.
What is the purpose of conditions in programming? O Used to explain how the program works or functions. These lines are ignored by the compiler during runtime. Conditions are a step-by-step plan to solve a problem. O Conditions are used to perform the same steps over again. O Conditions are used to affect the flow of the steps.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter6: User-defined Functions
Section: Chapter Questions
Problem 20SA
Related questions
Question
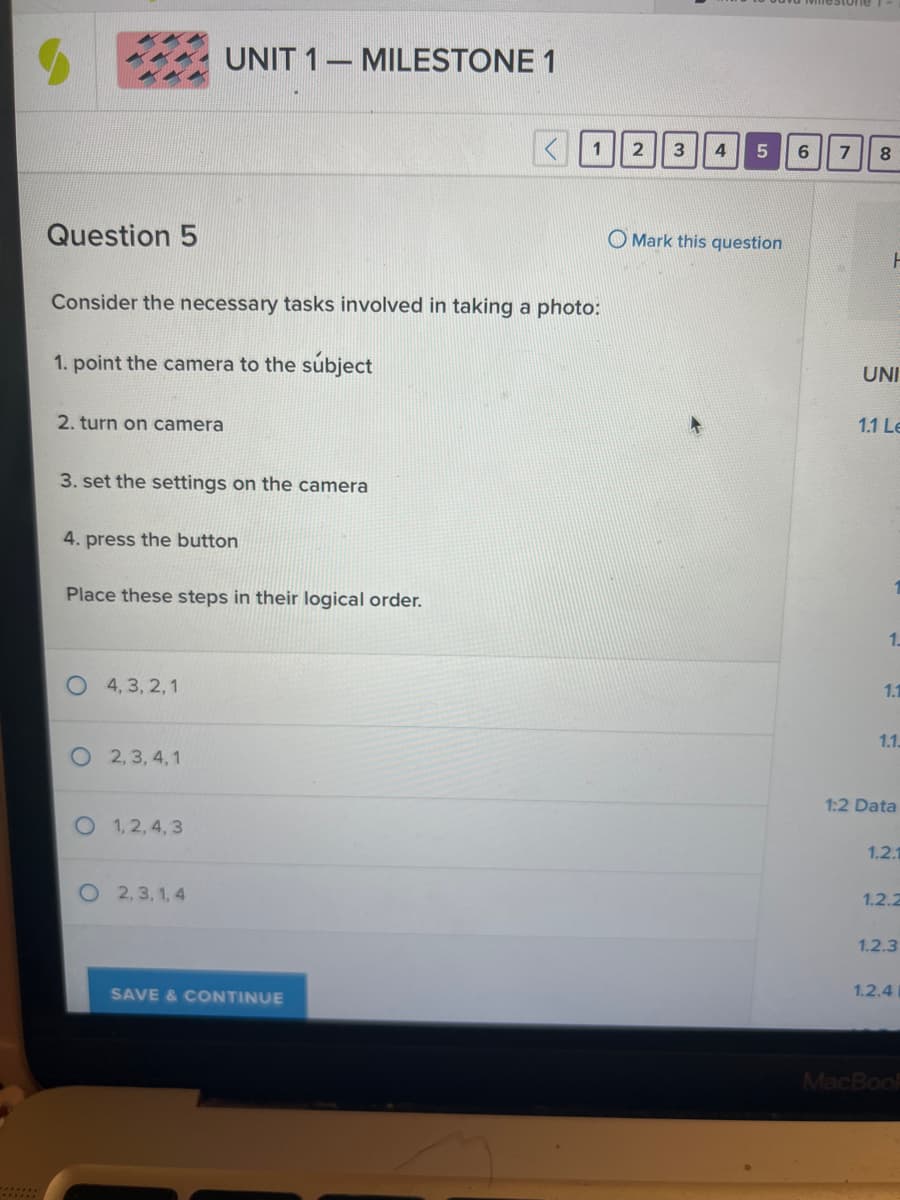
Transcribed Image Text:Question 5
Consider the necessary tasks involved in taking a photo:
1. point the camera to the subject
2. turn on camera
3. set the settings on the camera
4. press the button
UNIT 1 MILESTONE 1
Place these steps in their logical order.
4, 3, 2, 1
2,3,4,1
O 1,2,4,3
O2,3,1,4
SAVE & CONTINUE
2 3 4
5
Mark this question
6
7 8
F
UNI
1.1 Le
1.
1.1
1.1.
1:2 Data
1.2.1
1.2.2
1.2.3
1.2.4
MacBook
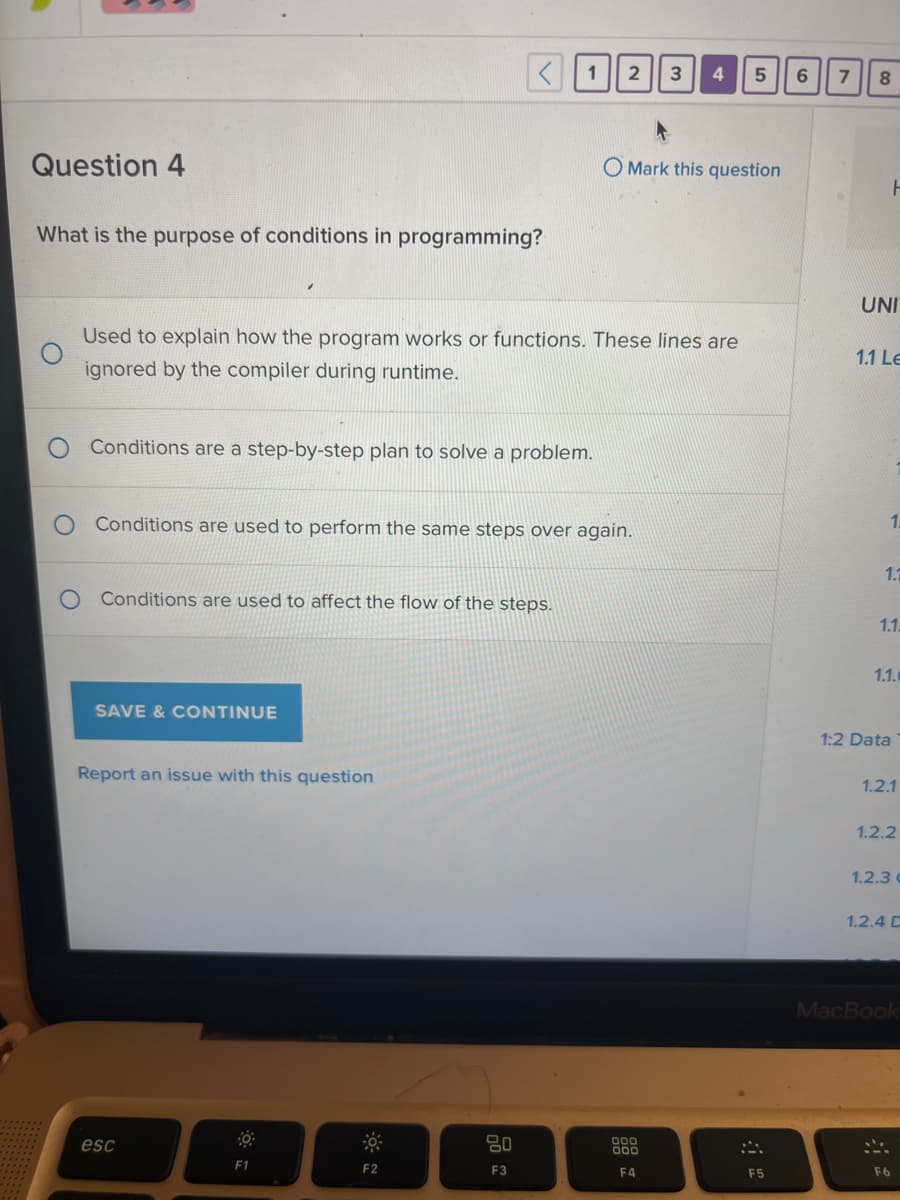
Transcribed Image Text:Question 4
What is the purpose of conditions in programming?
Conditions are a step-by-step plan to solve a problem.
Used to explain how the program works or functions. These lines are
ignored by the compiler during runtime.
Conditions are used to affect the flow of the steps.
SAVE & CONTINUE
Conditions are used to perform the same steps over again.
Report an issue with this question
esc
O
1
F1
F2
2 3 4
20
F3
OMark this question
5
000
000
F4
F5
6
7
8
UNI
ㅏ
1.1 Le
1.
1.1
1.1.
1.1.
1:2 Data
1.2.1
1.2.2
1.2.3 c
1.2.4 C
F6
MacBook
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning