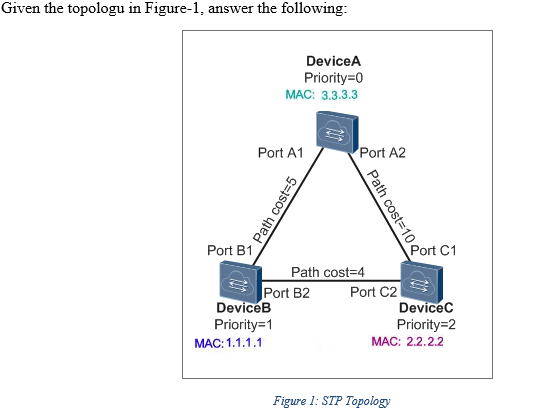
What is the purpose of spanning tree protocol? How it achieves this purpose? What are the fields that compose the bridge ID of a switch?
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: Introduction: here in this question we will discuss about why web application security is critical t...
Q: Proof that for T(n)=2T(n/2)+n^2, the worst case complexity will be n^2.
A: The answer is given below:-
Q: Vrite a C+ program that prompts the user to enter the earthquake magnitude and utputs its class. We ...
A: so, here we have to write a c++ Program that prompts the user to enter the earthquake magnitude and ...
Q: Using the encoding system described above, answer the following questions. Analysis 1. From previous...
A: Encoding a message with assigning each letter of the alphabet with a positive integer using a specif...
Q: :Write a python code to show the properties of AES.
A: Program explanation: Pip install the pycrypto in the command prompt. Import the AES library. Input ...
Q: Examine the benefits and drawbacks of various system models.
A: answer is
Q: On the Sales Data worksheet, calculate the total earnings for each sales associate. In cell G2, cal...
A: Note: I have given the answer as asked in the question Select the cell G2 Enter the formula in G2 a...
Q: Write code in C++, C# or Python to solve the following problem: Instead of a regular Fibonacci numb...
A: Write code in C++, C# or Python to solve the following problem: Instead of a regular Fibonacci nu...
Q: Write a program in c to implement a Stack using array. In order to implement the stack, program for...
A: Stack is a linear data structure that follows a particular order in which the operations are perform...
Q: What type of possible error messages you can get when you try to login with the ssh-i option?
A:
Q: Write an algorithm and draw a flow chart to read a number from the user and check whether the number...
A: Algorithm:- Step 1: Start Step 2: Read a number to Number Step 3: Divide the number by 2 and stor...
Q: Task:implement a function that reverses a list of elements by pushing them onto a stack in one order...
A: We need to write a function in Python programing language that takes a list of elements as a paramet...
Q: our knowledge about t, explain: (a) What are the differences between the operational modes 'f', 'a' ...
A: Lets see the solution.
Q: Print "CS2253" with a program starting at address x3000 that loops rough the individual characters, ...
A: 3000: MOV 30A0, 000F /* loads the value 000F into the memory address 30A0 */ 3001: LOAD 3020, @30A...
Q: What part of a disk drive consists of columns of tracks on two or more disk platters? Head ...
A: Option(b) is correct.
Q: Which is the highest operator precedence in Java ?
A: Operator precedence is a concept of determining the group of terms in an expression. operator prece...
Q: Comment on the current status of IPV4 and idencly d in lv6 Author: Abnan S ONI Henry F. Korth, S. Su...
A: The lack of address space - the number of different devices connected to the Internet grows exponent...
Q: A hexagonal cell within a seven-cell system has a radius of 1.52 km. A total of 140 channels are use...
A: Below is the Answer to above question. I hope this will be helpful for you...
Q: Compare this two, Study from home and studying in school
A: The answer to the following question:-
Q: Compare and contrast the Boolean operators AND, OR and NOT.
A: I have provided detailed explanation in Step 2----
Q: ormation described below, you are to sketch are to identify the objects (only object names are re bj...
A:
Q: Stable algorithms a. Explain the meaning of stability in a sorting algorithm. b. Explain a situation...
A: Part(a) The consistency of a sorting algorithm is determined by how it handles equal items. In cont...
Q: The Diamond Model of Intrusion Analysis is a framework for examining network intrusion events. Use t...
A: the answer is given below:-
Q: Make a simple c++ program that does the following: Monthly Sales
A: Explanation: Include all the necessary header files. Create a structure Am that will store the data...
Q: In designing an online e-commerce shopping platform app, it is best advised by a consultant to apply...
A: here we have given the use of gray box testing and gave few points to test the program for the onlin...
Q: Is aacccdcc in the language generated by the following grammar? If so, draw the parse tree. If not, ...
A: Yes the grammar generates aacccdcc.
Q: Explain peering gateway?
A: Looking is a technique that permits two organizations to interface and trade traffic straightforward...
Q: In Python, write the program to display the multiplication table of any number.
A: here in this question we have asked to write a program to display the multiplication table of any nu...
Q: ### Problem 6 Explain how one can identify connected components of a graph by using 1. a depth-first...
A: the answer is given below:-
Q: Explain the idea of a system model. What considerations should be considered when creating core mode...
A: Intro In the systems model, information flows between modules are represented as influences or flows...
Q: Find the correct asymptotic complexity of an algorithm with runtime T(n) where T(x) = O(n) + T(3 * x...
A: As you recuriment photo type computer language
Q: In one of the labs performed you were to examine a .jpg and write the first 2 bytes of Hexadecimal i...
A: answer is FF D8 JPEG (Joint Photographic Experts Group) is a commonly used method of lossy compress...
Q: For each invoice, list the invoice number, invoice date, item ID, quantity ordered, and quoted price...
A: Answer: -- create database KIMTAY create database KIMTAY; -- ensure that KIMTAY is used use KIMTAY; ...
Q: Question:: Case Exercises Amy walked into her office cubicle and sat down. The entire episode with t...
A:
Q: When utilizing a logic programming language such as Prolog to tackle computing problems, what are th...
A: Intro when utilizing a logic programming language such as Prolog to tackle computing problems, what ...
Q: Write a MATLAB function, called fixed_point_iteration that inputs a function, g, an initial guess x)...
A: The answer is givwn below:-
Q: lQuestion:: There are blank 3 digit counting numbers that are made using only the odd digits 1,3,5,7...
A: Here in this question we have asked that how many 3 digit number are possible with odd digit 1,3,5,...
Q: Exercise 7 Create a Python program that asks the user to enter the parameter Atand an upper limit of...
A: Create a Python program that asks the user to enter the parameter lambdat and upper limit of the sto...
Q: Write a Python function called reverse that takes two file names as arguments. The function should c...
A: Answer :
Q: Is there a difference between a system subsystem and a logical division?
A: The answer is given below.
Q: Discuss a problem with concurrent processing in an operating system.
A: Concurrent processing is technique to execute processes parallely.
Q: 15. Use sets to find the two six-digit numbers with all different digits where the square of the num...
A: c=0for i in range(100000,1000000): s=set(list(map(int, str(i)))) if len(s)==6: m=i*i ...
Q: The production rules for the derivation tree are as follows −E=E+E E=E*E E=a|b|c Here, let the inpu...
A: The production rules for the derivation tree are as follows −E=E+E E=E*E E=a|b|c Here, let the inpu...
Q: What are the benefits of including animation into a presentation?
A: Introduction: A PowerPoint presentation might benefit from animation to make it more vibrant and mem...
Q: Why is Access preferable than Excel when it comes to tracking this data?"
A: When it comes to tracking data, there are two major options: Excel and Access. Both have their benef...
Q: Describe why web application security is critical. What may go wrong with an unsecured application? ...
A: the answer is given below:-
Q: Please provide comments as I'm still a beginner in Python. Below is a list of input examples: 6+7 Th...
A: Explanation: Import necessary header files. Define the grammar as if the term is added then additio...
Q: 852 Which of the following can be used to return the maximum salary (SALARY) for each location (LOC)...
A: query to find out maximum salary for each location : select LOC,max(SALARY) from emp group by LOC;...
Q: Simplify the following function, and implement the same with two-level NAND gate
A: NAND gate means the combination of two logic gates that are NOT and AND gate. Nor gate switch the va...
Q: Design an Entity-Relationship for each system described below. Use the (min,max) notation. State cle...
A: 1) This Entity-relationship diagram: For more than 35 years, the entity relation (ER) data structure...
please solve this, thanks.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Explore devices that operate at the Transport layer (Layer 4) of the OSI model, outlining their functions and importance.The Open Systems Interconnection (OSI) Reference Model defines seven layers that describe standards from the physical wire all the way up to the application interfaces on computers. Each layer has a specific function, common among all devices, and a specific way of communicating with the layer above and the layer below in the stack. Answer the following questions: Why is it important to wireless networking to understand the layers of the OSI Reference Model? Fully address the questions in this discussion; provide valid rationale for your choices, where applicable; and respond to at least two other students’ views. use at least two scholarly articles.Complete the table below by analyzing any of the given IoT (Internet of Things) applications: IoT Architecture layer Deviced used Device layer Gateway layer Platform Layer
- CIN 603 QUIZ The OSI model consists of seven layers. Which of the following best state all the seven layers and in order? a. Application layer, presentation layer, session layer, transport layer, network layer, data link layer b. Application layer, presentation layer, session layer, transport layer, network layer, data link layer, physical layer. c. Application layer, presentation layer, session layer, transport layer, network layer, data link layer, physical layer. d. Application layer, presentation layer, session layer, network layer, data link layer, physical layer. 2. Client/server systems enable the firm to scale the system in a rapidly changing environment Select one: True False 3. Which of the following could be a reason for web integration for organizational information systems? a. Avoids compatibility issues b. Its interesting. c. its trendy d. client request 4. Scalability refers to a system’s ability to expand, change or downsize…It can be challenging to select the proper security virtual device for cloud computing, primarily due to the lack of a model similar to the OSI model for traditional networking. You decide to present a proposed model for cloud-based networking. Which of the following layers is likely to be the most similar between the two models? a. Transport b. Physical c. Native Service d. NetworkWhen comparing the advanced capabilities of Pfsense, Opnsense, and other commercial wireless router software, as well as the pros and drawbacks, cost, and simplicity of use of the program, you may find it helpful to make use of a table. Find out which of the many operating systems for routers is the best and explain why.
- Design a star topology consisting of the devices seen in Table 1. 1. Configure the devices using the following IP addresses and subnet masks:Device IP Address Subnet maskPC1 172.16.33.2 255.255.0.0PC2 172.16.33.3 255.255.0.0Server1 172.16.33.4 255.255.0.0Server2 172.16.33.5 255.255.0.0Router LAN interface 172.16.33.6 255.255.0.0Router WAN interface 196.12.45.66 255.255.255.0Table 1:Network Devices2. Without testing for connectivity and just observing the addresses above, will all the workstations be able to communicate with the servers? If no, troubleshoot were necessary and rectify the issue.2 Testing the Network1. Test network connectivity with ping. Fill `yes' or `no' into the matrix below, depending on the success of the ping.DEVICE PC1 PC2 Server2 Server2 LAN interfaceWAN interfacePC1 -PC2 -Server1 -Server2 -LAN interface - -WAN interface - -2. Why are the pings to the Router WAN interface unsuccessful?Explanation:3. Which device in this topology would be the candidate for the…Describe why utilizing the UDP protocol instead of the TCP protocol can be beneficial for an application developer. Even if it is the application itself, is it even possible for a software to have dependable data transfer while it is operating through UDP? If so, just how?Derive the relationship for efficiency of ALOHA protocol. Compare the performanceof ALOHA, Slotted ALOHA, 1-persistent, non persistent and p- persistent CSMAprotocols graphically. Please explain briefly
- Consider the below image EIGRP topology and answer the following questions accordingly. 1. Calculate the EIGRP metric using the composite metric formula to reach the internet from R2 to THE INTERNET trough R1 : 2. Calculate the EIGRP metric using the composite metric formula to reach the internet from R2 to THE INTERNET trough R4: 3. Calculate the EIGRP metric using the composite metric formula to reach the internet from R2 to THE INTERNET trough R5: 4. Which router is considered a feasible successor to reach THE INTERNET from R2? * R1 R3 R4 R5 5. Calculate the reported distance from the other 2 routers to reach THE INTERNET: 6. Is there a feasible successor of R2 to reach the Internet? * R1 R3 R4 R5 None of the aboveBelow is example simulation based on Cisco Packet Tracer! Try to make an interconnection between 3 pieces of network that are connected to a router. Innetwork-1 has a DNS Server and 1 workstation, on network-2 there is an HTTP Server(.com domain) and 1 work station, on network-3 there is an HTTP Server(on the domain .com) and 1 work station. Do such a configuration so that each work station can access the existing server services on the three those networks?Suppose five stations A, B, C, D, and E are in a wireless network with the following configuration: See attached for the rest --> please add explanation while answering

