A hexagonal cell within a seven-cell system has a radius of 1.52 km. A total of 140 channels are used within the entire system. If the load per user is 0.028 Erlangs, and 1 = 2 call/hour, compute the following for an Erlang C system that has an 8% probability of delayed call: a) How many users per square kilometer will this system support? b) What is the probability that a delayed call will have to wait for more than 9 sec?
A hexagonal cell within a seven-cell system has a radius of 1.52 km. A total of 140 channels are used within the entire system. If the load per user is 0.028 Erlangs, and 1 = 2 call/hour, compute the following for an Erlang C system that has an 8% probability of delayed call: a) How many users per square kilometer will this system support? b) What is the probability that a delayed call will have to wait for more than 9 sec?
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section20.11: The M/g/s/gd/s/∞ System (blocked Customers Cleared)
Problem 4P
Related questions
Question
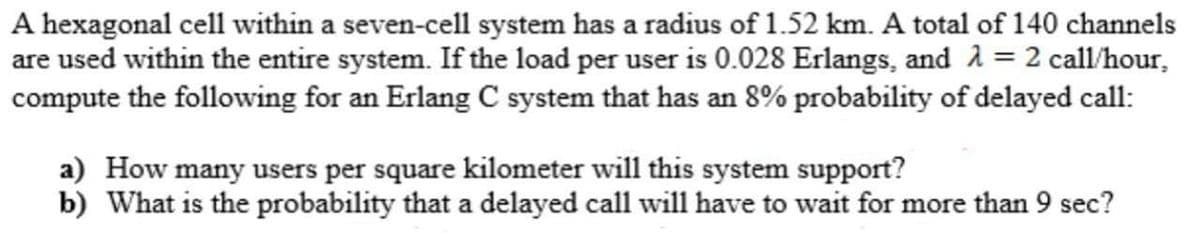
Transcribed Image Text:A hexagonal cell within a seven-cell system has a radius of 1.52 km. A total of 140 channels
are used within the entire system. If the load per user is 0.028 Erlangs, and 2 = 2 call/hour,
compute the following for an Erlang C system that has an 8% probability of delayed call:
a) How many users per square kilometer will this system support?
b) What is the probability that a delayed call will have to wait for more than 9 sec?
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole