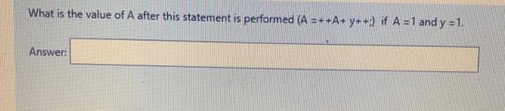
What is the value of A after this statement is performed (A=++A+ y++) if A = 1 and y = 1. Answer:
Q: Rewrite the following code while using the user-defined functions for the mentioned blocks #1 and #2…
A: You can name the two functions to block 1 and block 2, which are constructed, as you see fit. This…
Q: 120 host addresses. The administrator has used 192.168.10.0/24 and
A: The answer is
Q: Algorithm for Mean-payoff learning for black-box MDP Input: MDP M, imprecision εMP > 0,…
A: Algorithm for Mean-payoff learning for black-box MDPInput: MDP M, imprecision εMP > 0,…
Q: 13. Explain role of machine learning the following common un-supervised learning problems: i. Object…
A: The question has been answered in step2
Q: Q. 11 Explain man-in-middle attacks.
A:
Q: Consider the following graph. Apply Prims algorithm to find MST. Show each and every significant…
A:
Q: The program below reads two integers n and m from the user. As a function of n and m, give a formula…
A: Here is the explanation regarding the problem:
Q: Question 4: A heap has 1000 elements placed as we have discussed in an array with indeces going from…
A: In an array of n elements where indices begin from 1, the formula for the index of the first…
Q: Write a C program to read two floating point numbers L and M from the console. Find and display the…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: 16. With reference to Hierarchical Clustering, explain the issue of connectivity constraints.
A: Solution for given, With reference to hierarchical clustering, Explain the issue of connectivity…
Q: What are the differences between ext2, ext3 and ext4 filesystem?
A: What are the differences between ext2, ext3 and ext4 filesystem ?
Q: What is the value in string st1[] of the below code []="SultanateOf";char st2 0 snippet? char st1…
A: Below I have provided the solution to the given question.
Q: What is the value of result when the following code executes? int result = 0; for(int i=1; i <= 5;…
A: Here is the value of the result when we execute the following code. See below steps.
Q: Explain various ways of coding an algorithm with the help of an examp
A: Answers:- Various ways of coding:- Data compression (source coding):- The Data compression in which…
Q: lease answer all parts of the question 2. For the given plaintext:…
A: SOLUTION- An step by step solution of each part is given in the particular manner as- Plain text-…
Q: How would the numbers be illustrated in the array order of a max heap, with the given numbers?
A: Solution: Building max heap from an array: Root is at index 0 in array. Left child of i-th node…
Q: Given a circular linked list, implement an algorithm that returns the node at the beginning of the…
A: Circular Linked list : In a circular linked list, the first element points to the last element,…
Q: Q2: Write a Verilog description for the simplified form of the following function, using Dataflow…
A: Below I have provided the solution to the given question.
Q: Algorithm for VerifyNash Inputs: Finite-state deterministic joint policy π, specifications φj for…
A: Algorithm for VerifyNashInputs: Finite-state deterministic joint policy π, specifications φj for all…
Q: three (3) central organizational factors to consider when planning a new system
A: Organization: A organization means a group of people work together in a organized way. Organization…
Q: 1. Discuss the types of data analytics used in business. 2. Explain the benefits of data analytics…
A: From descriptive statistics to more intricate predictive analytics and machine learning algorithms,…
Q: Q.6 State of Algorithm disadvantages of Naïve Bayes.
A: Naive Bayes: It is a machine learning algorithm for solving a classification problems. It is based…
Q: In an IPv4 packet, the value of HLEN is (1010)2 and the value of the full-length field is (005A)16.…
A: IPv4 The fourth iteration of the protocol for directing Internet traffic as well as other…
Q: 3. Write a Java program that declares and initializes two integers (assign values of your choice to…
A:
Q: Write shorts notes on: Gaussian naive Bayes
A:
Q: Searches for any number within the sorted list using Binary search. Searches for any number that is…
A: 1st method in java code:- class Main { public static int binarySearch(int a[], int l, int y, int x)…
Q: DIDNT WORK
A: You also have to change the dimension according to the scatter plot. >> ax1 = plt.subplot2grid…
Q: Your application will demonstrate the ability to retrieve 10 numbers from a user and determine the…
A: Program Approach:- Step 1: Declare class with the name of ArrayProgram. Step 2: In main method…
Q: Data compression, in general, and Huffman encoding as a method, can be used in multiple areas:…
A: a) The challenges of Image processing are The problem of how one store and transmits a digital…
Q: Algorithm ASSOCIATED LEGENDRE SOLVE Given positive squarefree integers B,C such that the equation…
A: given data: Algorithm ASSOCIATED LEGENDRE SOLVEGiven positive squarefree integers B,C such that the…
Q: Part 1: String class • Read a String (the first line of input) from scan. . Print the string. •…
A: The JAVA Code is given below with code and output screenshot Happy to help you ?
Q: Explain Data formats for supervised learning problem with example.
A: Supervised Learning:- The method of supervised learning involves giving the machine learning model…
Q: each of the following relations that are not in third normal form, write a relational schema that…
A: Given: Each of the following relations that are not in third normal form, write a relational schema…
Q: Algorithm for ECCS
A: Solution- Algorithm for ECCS method in the Voice Telephone Network with its design- Introduction-:…
Q: Please do it with Python. #Problem 1 #Chip Brownie made a mistake and allowed any value to be…
A: Here is the python code of the above problem. See below steps.
Q: List the types of information you need to store and state how long you think you will need them for.…
A: Answer: We need to write list of the information store and how can be accessible so we will see in…
Q: Explain the role of machine learning algorithms in Natural Language processing.
A: The answer to the question is given below:
Q: et's say that you are given a network address block as 192.168.16.0/24, and are asked to divide it…
A: The answer is
Q: 1 2 3 4 567 8 9 10 50 11 30 10 234 12 13 14 15 678 a 50 30 10 9 50 30 10 2 5 3 253 253 USING CELL…
A: A cell reference refers to a cell or a range of cells on a worksheet and can be used in a formula so…
Q: b) Write down a non-trivial loop-invariant that holds at the line marked "invariant here!" in the…
A: The invariant is that at the start of each iteration of the loop, answer is the smallest value seen…
Q: 1) On the command line, you can redirect stdout and stderr, but not stdin. True False 2) System…
A: Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: SHOW FORMULAS IN EXCEL
A: Given: Highlight FormulasIf you don’t want to see the actual formulas, but want to know which cells…
Q: Exercise 1-Printing Characters of Odd ASCII Codes Recursively Exercise Objectives ✓ Calling…
A: Below I have provided a program for the given question. Also, I have attached a screenshot of the…
Q: program makes a system call, explain how the mode bit changes to Supervisor mode. b) When we want…
A: SummaryThe unrestricted mode is referred to as manager mode or kernel mode, and the restrained one…
Q: What is block cipher? Explain counter mode block cipher.
A:
Q: simple machine learning (ML) modul
A: Introduction Machine learning is a type of learning structure that provides certain algorithms for…
Q: this loop using a single line of vectorized code.
A: Given :- In the above given question, a code fragment is mention in the above given question Need…
Q: De Morgan's laws commonly apply to text searching using Boolean operators AND, OR, and NOT. Consider…
A: De morgan's law The intersection of two sets' complements is the complement of a union of two sets,…
Q: The first two bytes of a 2M x 16 main memory have the following hex values: 1. Byte 0 is FE 2. Byte…
A: In this instance, a word in the main memory has a length of 2 bytes or 16 bits. The value in the…
Q: The input file salesin. txt contains a series of lines with three numbers on each line. Each line…
A: Solution:
Step by step
Solved in 2 steps

- Write out a truth table (including all four cases) for the following expressions. Here, p,q and r represent simple statements that can be true or false. a) ~p . q . ~rWhat is the value of the postfix expression 6 3 2 4 + - *: A. Something between -15 and -100 B. Something between -5 and -15 C. Something between 5 and -5 D. Something between 5 and 15 E. Something between 15 and 100Write the inverse of the following statement: “If it is winter, then it is snowing.” ____________________________________________________________________
- This is test prep, I know the right answer is E, what I don’t understand is why the else statement overrides the first if statementShow the value of x after each of the following statements is performed:a) x = fabs(7.5);b) x = floor(7.5);c) x = fabs(0.0);d) x = ceil(0.0);e) x = fabs(-6.4);f) x = ceil(-6.4);g) x = ceil(-fabs(-8 + floor(-5.5)));you are missing the zero,running and stopped boolean expression. Please check the above solution.
- Convert the following code into descriptive code, and verify using White Box Testing. a = 2 b = 10 c = a * b for( i = a, i < b, i = i+a) result = a + i if ( result % 2 == 0) print (“Even”) else print (“Odd”) end-if end-for **************************************** I want a solution like this photoIn which cases you can transform an else-if statements to switch? Provide an example.Some one please explain what is "where z′ is the value of z after the statement is executed" given in the question. CAN SOME ONE PLEASE SOLVE THIS QUESTION CORRECTLY WITH PROPER EXPLANATION OF WHICH CONDITION TO CONSIDER.

