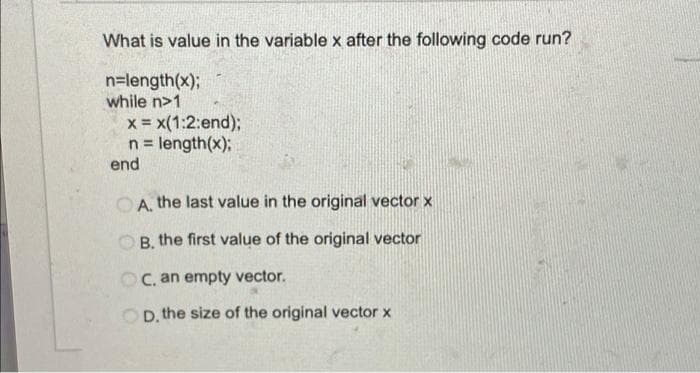
What is value in the variable x after the following code run? n=length(x); while n>1 x = x(1:2:end); n = length(x); end OA, the last value in the original vector x OB, the first value of the original vector OC, an empty vector. D. the size of the original vector x
Q: What are the key hardware and software components required for computer graphics?
A: Computer graphics hardware and software Computer graphics hardware comprises a computer with memory…
Q: What kind of fairness assumption should be used in an algorithm to accomplish mutual exclusion?…
A: MUTUAL EXCLUSION :prevents race circumstances. IT is the requirement that a process can't enter its…
Q: What do you think about today's wireless networks in developing countries? LANs and physical…
A: The term "wireless network" refers to a computer network that establishes connections between nodes…
Q: 1. Use Do while loop to help the users to calculate shape Area 2. In each iteration: a. Ask the user…
A: I have provided JAVA CODE along with CODE SCREENSHOT and OUTPUT…
Q: What type of relationship in the conceptual model is converted to an entity in the logical database…
A: Conceptual ERD models the business objects that should exist in a system and the relationships…
Q: The workings of RAID 5 Is there a situation in which RAID 5 would be more appropriate than the other…
A: Given: RAID is a storage virtualization system that integrates many physical disc drive components…
Q: What data-sharing problems do you envision big data posing in healthcare?
A: Beginning: The data sharing problems of big data in healthcare have been requested. Data is the…
Q: Compare and contrast the notion of abstraction using examples from the area of computer science.…
A: Our task: The issue addresses the significance of abstraction in software engineering and the…
Q: What is the purpose of XML schema?
A: A document known as an XML schema definition (XSD) is a blueprint that lays out the guidelines and…
Q: What are the two different kinds of services that the Internet offers to the apps that it hosts?…
A: The two types of services that the Internet gives to its users are: The Internet gives its…
Q: Task 03: Read the concept of Binomial coefficient given in chapter-6. Write a method that takes two…
A: Please refer below for your reference: Language used is C++: Formula used for C(n,k) is n!…
Q: What are the three different kinds of information systems?
A: Define: There are several kinds of information systems available. However, the following are the…
Q: Please be aware that the following is a sampling of what is expected of you as a student. The…
A: Introduction: When the functionality of a software is tested without understanding how it was…
Q: debate based on your knowledge of the importance of software quality assurance in software…
A: Software development is the most common way of considering, determining, planning, programming,…
Q: Wireless networks have a less bandwidth capacity than conventional networks.
A: Introduction: Wireless networks and Wired networks 1) A network is a collection of two or more…
Q: Write a program in Matlab to test odd or even numbers forn values
A: Find the required code in matlab given as below and output :
Q: sed are you in the principles of firewall adminis
A: Introduction: Below well-versed are you in the principles of firewall administration
Q: a description of what a flip-flop circuit does and how it may be utilized Whether the circuit is a…
A: A flip-flop is a two-state electrical circuit used for storing binary data. By modifying the inputs,…
Q: Write a program that reads a sequence of input values and displays a bar chart of the values, using…
A: Since no programming language is mentioned, I am using c++ Code: #include <iostream>using…
Q: Set the keyPress event.
A: When a key is pressed inside a control, the KeyPress event is triggered (i.e. the regime has been…
Q: .Create your own menu and display it using javaFX.
A: As per the question statement, we need to create JavaFX program and create menu.
Q: What are the numerous software testing techniques used in software engineering and why do they…
A: GIVEN: To describe the many software testing methodologies used in software engineering, as well as…
Q: Differentiate virtual reality technology and augmented technology from one another
A: answer is
Q: een computer programm
A: Solution - In the given question, we have to Distinguish between computer programming and…
Q: What happens if the cloud computing revolution has an influence on collaboration?
A: In this question we have to understand the influence and benefits of collaboration in the cloud…
Q: depiction of illumination In the Phong model, what is the difference between ambient, diffuse, and…
A: As Bryan Pawlowski made sense of, ambient light is (in the exemplary lighting model) just a steady…
Q: What are some practical uses of Automata Theory?
A: Here, we must determine the applications of Automata Theory.
Q: What are a program's three main focuses?
A: A program's three major activities are: input: The term "input" refers to the gathering of raw data…
Q: geographically, it is feasible to utilize a local area
A: Local Area Network (LAN) is confined to a small geographical area, usually to a relatively small…
Q: What are some of the most efficient ways to keep a firewall in good working order? Explain.
A: A firewall is a network security device that prevents unauthorized access to servers. There are two…
Q: What factors led to the development of the three-level database design in the first place?
A: What prompted the development of the three-tier database architecture? Architecture on three levels:…
Q: What exactly is a Binary Search Tree?
A: Binary Search Tree: The Binary Search Tree is only an additional twisted binary tree in which the…
Q: As a foundational concept of operating system security, how does the distinction between kernel mode…
A: Important Facts to Know There are 2 modes of operation in an operating system: user mode and kernel…
Q: Why polling should not be utilized but instead interrupt should be used in development.
A: Introduction: Why should interrupt be used instead of polling in development? In i/o mode, polling…
Q: Is it possible for you to explain the metrics used in the software development process? Isn't it…
A: Development of software: These are the metrics that are used to assess the different phases of…
Q: Defintion of roundoff mistake
A: The difference between a number's determined approximation and its exact mathematical value is known…
Q: Explain the following: 1. Database management system concurrency 2. DBMS Backup and Recovery
A: Database management system concurrency In the database management system concurrency is the ability…
Q: comment on ISO-9000-3 Software Quality Process
A: ISO-9000-3 is a Standard to the development, supply, and maintenance of software. It is the Quality…
Q: What is the most critical part of switching from a serial to a batch processing system?
A: What is the most critical part of switching from a serial to a batch processing system?
Q: metrics are used in the software development process
A: Software metrics: It is a measure of software characteristics. Software characteristics are…
Q: Describe some of the most common computer applications for the minimal spanning tree problem?
A: Given: What are some of the most important uses that computers have found for the minimal spanning…
Q: In software engineering, there are several data kinds. Discuss the differences between simple and…
A: The field of software engineering makes use of a wide variety of data formats. Here, we'll talk…
Q: what end are firewalls put in place?
A: here in the question ask for at what end we can put firewall?
Q: where can we use the character code? and give me an exaple
A: Character code are also known by the name of character set, charset, character encoding. A character…
Q: What is a Runtime Error?
A: A runtime error occurs when a program is syntactically correct but contains an issue that is only…
Q: Explain briefly how you can use asymmetric key encryption to secure the integrity of outgoing data.…
A: Intro Asymmetric cryptography is a kind of cryptography, where the users are allowed in…
Q: If we change the implementation of any layer in the TCP / IP model then the implementation of other…
A: The answer is
Q: Draw class diagram using Rational rose software in payroll system
A: Step 1: Rational rose is a object oriented UML (unified modelinglanguage) design software design…
Q: Explain why read-only memory (ROM) is needed and what function it plays in the design of a computer…
A: The answer is given below.
Q: What does technical analysis aim to achieve? Explain how and why technicians utilize it, as well as…
A: Technical analysis: Technical analysis examines and forecasts future stock prices using data such as…
Please don't privide direct answer explain me
Step by step
Solved in 4 steps with 1 images

- Modify from the code below, add an additional input from the use input to get how many random integers to create. Use a vector<int> instead of an int array to store the random integers. Function prototypes: void showValues(const vector<int>&); void fillVector(vector<int>&, int, int); int maximum(const vector<int>&); int minimum(const vector<int>&); double average(const vector<int>&); bool searchValue(const vector<int>&, int); Code: #include <iostream>#include <iomanip>#include <cstdlib>#include <ctime>using namespace std; // Function prototypevoid showValues(const int[], int); void fillArray(int[], int, int, int); int maximum(const int[], int); int minimum(const int[], int); double average(const int[], int); int main(){const int ARRAY_SIZE = 10;int numbers[ARRAY_SIZE];srand(time(0));int low = 0, high = 1;cout << "**This program will generate 10 random integers between [low] and…We can dynamically resize vectors so that they may grow and shrink. While this is very convenient, it is inefficient. It is best to know the number of elements that you need for your vector when you create it. However, you might come across a situation someday where you do not know the number of elements in advance and need to implement a dynamic vector. Rewrite the following program so that the user can enter any number of purchases, instead of just 10 purchases. Output the total of all purchases. Hint: us do while loop with your vector.. #include <vector> #include <iostream> using namespace std; int main() { vector<double> purchases(10); for (int i = 0; i < 10; i++) { cout << "Enter a purchase amount"; cin >> purchases[i]; } return (0); }Write a program that first gets a list of integers from input and puts them into a vector. The input begins with an integer indicating the number of integers that follow. Then, get the last value from the input, which indicates a filtering threshold. Output all integers less than or equal to that last threshold value separated by a comma and space. Ex: If the input is: 5 50 60 140 200 75 100 the output is: 50, 60, 75 The 5 indicates that there are five integers in the list, namely 50, 60, 140, 200, and 75. The 100 indicates that the program should output all integers less than or equal to 100, so the program outputs 50, 60, and 75. Such functionality is common on sites like Amazon, where a user can filter results.
- Define an integer vector and ask the user to give you values for the vector. because you used a vector, so you don't need to know the size. user should be able to enter a number until he wants(you can use while loop for termination. for example if the user enters any negative number, but until he enters a positive number, your program should read and push it inside of the vector). thenGiven two arrays A and B of equal size N, the task is to find a vector containing only those elements which belong to exactly one array - either A or B - but not both. That is, if some element x appears in both A and B it should not be included in the output vector. Complete the implementation of "getVector(vector<ll>A, vector<ll>B, int N)" function. Example: Input: 1 3 5 7 1 3 2 4 6 7 8 Output: 3 5 1 3 2 4 6 8 The driver codes are attached in the images below. DO NOT CHANGE THE PROVIDED DRIVER CODES AT ALL, LEAVE THEM EXACTLY THE SAME. ONLY ADD CODE TO THE "getVector(vector<ll>A, vector<ll>B, int N)" FUNCTIONWrite a function that accepts a number, N, and a vector of numbers, V. The function will return two vectors which will make up any pairs of numbers in the vector that add together to be N. Do this with nested loops so the the inner loop will search the vector for the number N-V(n) == V(m). n and m are indices in the vector of numbers. Example A = [1,2,3,4,5,6, 7] Google(5, A) Return [1,2,3,4] and [4,3,2,1] being the pairs that sum to 5. Notice that each pair appears twice. Try to write code that does not do this.
- Assume you have a non-empty vector vec in your Matlab workspace. Will the following command: >> length(vec(vec == max(vec))) count all elements in vec with values equal to the maximum value in vector vec? Yes NoWhich shows valid accesses for an array a and vector v, each with 10 elements? In other words, this question is asking what is the proper syntax for accessing the array and vector. a. array: a[7] vector: v.at(5) b. array: a.at(5) vector: v[9] c. array: a.at(5) vector: v[5] d. array: a[1] vector v.at[4] Coding is in C++.Modify the existing vector's contents, by erasing the element at index 1 (initially 200), then inserting 100 and 102 in the shown locations. Use Vector ADT's erase() and insert() only, and remember that the first argument of those functions is special, involving an iterator and not just an integer. Sample output of below program with input 33 200 10: #include <iostream>#include <vector>using namespace std; void PrintVectors(vector<int> numsList) {unsigned int i; for (i = 0; i < numsList.size(); ++i) {cout << numsList.at(i) << " ";}cout << endl;} int main() {vector<int> numsList;int userInput;int i; for (i = 0; i < 3; ++i) {cin >> userInput;numsList.push_back(userInput);} /* Your solution goes here */ PrintVectors(numsList); return 0;} Please help me with this problem using c++.
- 6) While there is a built-in pop_back() method for vectors, there is no built-in pop_front method. Suppose a program needs a pop_front() method that will remove the first element from the vector. For example if the original vector is [1, 2, 3, 4, 5], then after passing in this vector to pop_front() the new resulting vector will be [2, 3, 4, 5]. Which of the options below is the correct implementation of pop_front()? Group of answer choices D-) void pop_front(vector<int> &v){ for(int i=0; i<(v.size()-1); i++)v[i+1] = v[i]; v.pop_back(); } C-) void pop_front(vector<int> &v){ for(int i=0; i<(v.size()-1); i++)v[i] = v[i+1]; v.pop_back(); } B-) void pop_front(vector<int> &v){ for(int i=0; i<v.size(); i++)v[i+1] = v[i]; v.pop_back(); } A-) void pop_front(vector<int> &v){ for(int i=0; i<v.size(); i++)v[i] = v[i+1]; v.pop_back(); } 7) Suppose a program has the following vector: [99, 23, 55, 71, 87, 64, 35, 42] The goal is to…is there another way without using vector?Write code for determining the index of a value in an OrderedVector. Be aware that if the value is not in the Vector, the routine returns the ideal location to insert the value. This may be a location that is outside the Vector(use java)

