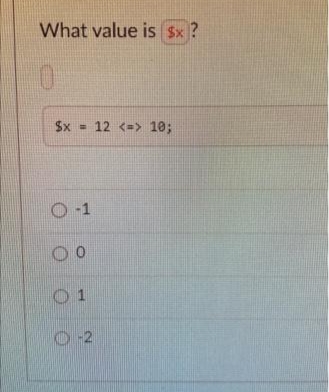
What value is Sx ? Sx - 12 <=> 10; O-2
Q: Computer science Explain the prefix, infix,and postfix notation.
A: Introduction: Computer science explain the prefix, infix, and postfix notation.
Q: Who do you need to work with to achieve these objectives in software design? What are some of the…
A: Introduction: Software design goals:…
Q: Why should edge triggers be used in shift registers?
A: Introduction: Registers are made from flip flops. They are used for storing data and work as memory…
Q: Which of the possible answers is logically equivalent to the expression below? (((C)) U ((C))) U (B\…
A:
Q: When it comes to tracking this data, why is Access better than Excel?
A: Introduction: MS Access stores data in tables that resemble worksheet or spreadsheet tables, but…
Q: The term "dynamic memory" refers to a sort of memory that evolves over time.
A: Introduction: To change or edit several types of data in your phone's memory. Also known as Shared…
Q: How would you develop a solid thesis statement if you were writing an essay?
A: Introduction: The thesis statement in a research paper or essay is a statement that explains why you…
Q: To which value would the following expression reduce if the values of P, Q, R, and S were True,…
A: In Step 2 , I have provided solution with brief explanation----------------
Q: What are the many types of relationships in a DBMS?
A: Imtrouction: Relationships in DBMS depict an association between the tables.
Q: How are user threads converted to kernel threads in Windows 7? Is communication one-on-one,…
A: So, first a user must know thread and types of thread and thread models in Win 7. A thread is a…
Q: What are the key steps in the C++ compilation process?
A: Introduction: A compiler is a unique software that analyses statements written in a certain…
Q: eXtreme Programming should be explained.
A: Introduction: Extreme programming is a technique for creating agile software. It is a software…
Q: When the computer is used optimally, with multiple applications running, the CPU consumption is…
A: Introduction: Multitasking is accomplished through time slicing, or allowing separate apps to…
Q: Demonstrate how object-oriented analysis may be used to help in the development of an information…
A: Analysis: Object-oriented analysis is critical for the development of information systems since it…
Q: Assume a database system is never unavailable. Is the recovery manager required in this system? Why
A: Database A database is a logically organized collection of data that is stored and accessed on a…
Q: Discuss the complications that data redundancy might pose.
A: Introduction: When numerous copies of the same data are stored in multiple locations at the same…
Q: Code Example 4-4 def multiply(num1, num2): product = num1 * num2 result = add(product,…
A: As i have read guidelines i can provide answer of only 3 part of questions if multiple questions…
Q: Discuss how to distinguish between the network core and the network edge in terms of network design…
A: Introduction: The difference between a network core and a network edge:
Q: What is the underlying cause of scope creep in information system design projects?
A: Introduction: Scope creep (also known as requirement creep) in project management refers to changes…
Q: (A 0.1
A: Here, we are given a NFA and we are asked the equivalent DFA for it and also we have to write the…
Q: Knowledge of social networking and the principles that underpin it To begin, let us define…
A: Social Networking: Modern social networking sites provide the bare essentials of communication.…
Q: What is information blockage in the context of health IT?
A: Introduction: In general, information blocking is a practise by a certified health IT developer,…
Q: What are the differences between polymorphic and generic functions in Machine Learning and…
A: Introduction: Polymorphism is a technique that allows an operator (or a member function name) to…
Q: Comparing and contrasting the following modelling and simulation techniques: a. Agent-Based…
A: Answer: a. Agent-Based Simulation: an agent based simulation model is a set of interfacing objects…
Q: What is the distinction between computer architecture and computer organisation? Give specific…
A: Intro The architecture of computer systems is concerned with the method in which hardware components…
Q: How does class DataInputStream help in socket programming?
A: Syntax of DataInputStream: public class DataInputStream extends FilterInputStream implements…
Q: What are daemon processes, and why are they important? As an example, provide four instances.
A: Introduction Processes with distinct process identifiers are formed throughout the execution of a…
Q: Consider the following five examples of graph theory's use in artificial intelligence.
A: Introduction: Graph theory has been used in artificial intelligence in the following ways:
Q: Show Steps Please 22. Using the CRC polynomial 1101, compute the CRC code word for the information…
A: Introduction Modulo 2 division: Modulo 2 division is similar to the arithmetic division. Here, the…
Q: Which of the following was the first functional language?
A: Introduction: Functional languages are essentially languages in which activities are carried out…
Q: Is it feasible to modify any other variables in order to keep the page size constant? Assess their…
A: Introduction Value permanently: A variable is a piece of memory in a computer that may retain a…
Q: For practical encryption that involves secret message transmission from Alice to Bob, why is the…
A: Introduction: Asymmetric encryption is also known as public-key encryption, however, it is based on…
Q: Explain the fundamentals of Linux's process scheduling mechanism
A: Introduction: The fundamental process scheduling technique in Linux
Q: Compile a list of at least 10 of the most prevalent network failures.
A: Network Failure One of the largest risks is network failure, which has a direct impact on service…
Q: Explain in detail one client-side programming language and one server-side programming language.
A: introduction: User interface/display and any other processing on the client computer, such as…
Q: A decision table simplifies the process of connecting circumstances to actions. explain?
A: Intro - linking conditions with actions in decision table - decision table are made up of columns…
Q: How does rhetoric integrate into computer science?
A: Rhetoric has two functions in the public understanding of science: it is both a theory capable of…
Q: Which operation shifts each bit in an operand to the left by copying the highest bit into both the…
A: When an operand is moved to the left in this instruction: All bits in the given register or operand…
Q: Question 7 Assume we are using the simple model for floating-point representation as given in this…
A: Below is the answer to above question. I hope this will be helpful for you..
Q: Why is a computer's system time a good source of random seed values?
A: Intro Random seed When a computer generates a random number series, a random seed determines the…
Q: What is the meaning of a dangling pointer?
A: Introduction: Dangling pointer occurs at the time of item destruction when the item is removed or…
Q: The ______ language consists of just two digits: 0 and 1. a) decimal b) binary c)…
A: Intro The ______ language consists of just two digits: 0 and 1. a) decimal b) binary c)…
Q: Demonstrate the importance of object-oriented analysis while developing an information system.
A: Given: Object-oriented programming and visual modelling manage stakeholder communication and product…
Q: What would happen if the RET command was omitted from a procedure?
A: Please refer below for your reference: Basically , the ret instruction transfers control to the…
Q: What is the distinction between a mainframe operating system and a laptop operating system? How may…
A: Introduction: What is the distinction between a mainframe operating system and a laptop operating…
Q: What is it about information system architecture that causes scope creep to occur so frequently?
A: The project scope, in basic words, refers to all of the work that is necessary to accomplish a…
Q: Which architectural pattern is optimal for systems in which one component generates data and another…
A: Architectural pattern: The principle that defines the software organization schema for these…
Q: t is quicker since the compiled language does not require computer processing. Use a language that…
A: Introduction: The following are some of the benefits of utilizing a compiled language versus an…
Q: Which architectural pattern is the most appropriate for systems in which one component creates data…
A: Introduction An engineering design is a general, reusable answer for a regularly happening issue in…
Q: What's the Distinction Between Triggers and Rules?
A: Introduction: What Is the Difference Between Triggers and Rules is the query, and the answer is in…
Please explain to me
Step by step
Solved in 2 steps

- You need to choose a password for computer account. The rule is that the password must consist of two lowercase letter (a to z) followed by one capital letter (A to Z) followed by four digits (0, 1, …, 9). For example, the following is a valid password:Find the total number of possible passwords.Saira owns a small business and she frequently makes transactions. Sometimes she makes payments and other times payments are credited in her account. One of her customer Tania purchased a product and credited payment while another payment by Saira was in progress. Now the sequence of transaction is as follows:1. Tania’s account read amount in saira’s account2. Saira’s account read amount in saira’s account3. Tania added Rs. 500/- in original amount (that was lets suppose Rs. 60,000/ 4. Saira’s account subtracted Rs. 2000/- that she debited in someone else’s account form the original amount (that was Rs. 60,000) 5. Tania’s account committed the transaction 6. Saira’s account committed the transaction Draw the above-mentioned sequence in form of a table and see if there is a problem. What this problem is called and how can we avoid such kind of problem? Propose some solutions (at least two) and then explain which one is better and why?With a single parameter: It represents the price of one (1) item ordered. Add 12% tax andreturn the total due.• With two (2) parameters: These represent the price of an item and the quantity ordered.Multiply the two (2) values, add 12% tax, and return the total due.• With three (3) parameters: These represent the price of an item, the quantity ordered, andthe discount amount. Multiply the quantity and price, deduct the discount amount, add 12%tax, and return the total due.
- Write a statement that assigns numCoins with numNickels + numDimes. Ex: 5 nickels and 6 dimes results in 11 coins?What is the opposite of greater than?Customers who belong to an online retailer’s Free Ship club receive free shipping on all of their purchases. Customers who do not belong to the club must make a minimum purchase of $50 to receive free shipping. If subcondition1 is strClubMember = "Y" and subcondition2 is dblPurchase >= 50, which logical operator should you use to combine both subconditions: AndAlso or OrElse?
- Which of the following statements declares the dblMAX_PAY named constant and initializes it to 11.25? a. Con dblMAX_PAY As Double = 11.25 b. Const dblMAX_PAY As Double = 11.25 c. Constant dblMAX_PAY As Double = 11.25d. none of the abovethis is the information that has to be hard-coded: # hard-coded calls jim = User(first_name='Jim', last_name='Bob', user_id=1000, last_login='June 12, 1998', password='password123') jim.describe_user() jim.greet_user() joe = User('Joe', 'Bob', 1001, 'July 4, 2001', 'babygirl') joe.greet_user() joe.describe_user()CHALLENGE ACTIVITY 1.10.1: Sphere volume. Given sphereRadius and piVal, compute the volume of a sphere and assign sphereVolume with the result. Use (4.0 / 3.0) to perform floating-point division, instead of (4 / 3) which performs integer division.Volume of sphere = (4.0 / 3.0) π r3 (Hint: r3 can be computed using *)
- Write a statement to print the data members of InventoryTag. End with newline. Ex: if itemID is 314 and quantityRemaining is 500, print:Inventory ID: 314, Qty: 500 #include <iostream>using namespace std; struct InventoryTag { int itemID; int quantityRemaining;}; int main() { InventoryTag redSweater; cin >> redSweater.itemID; cin >> redSweater.quantityRemaining; /* Your solution goes here */ return 0;}Richard employs Interior Decorating company that wants to use your services to help create an invoicegenerating system. The Decorators submit an invoice weekly. They charge $20 per hour worked. Theyalso charge tax 10%. Richard likes to see an invoice that displays all the information – number of hours,the charge per hour, the total BEFORE tax and the total AFTER tax. Since this is an invoice, we also needto display the name of the company (Decorating Xperts) at the top of the invoice. Display all of theinformation on the screen.Using Pseudocode, develop an algorithm for this problem.Consider the following code. num = NOT_Assigned alist = [2, 0, 1, 5, 3, 4] val = 0 for i in range(0, num): val = alist[alist[val]] print(val) What should be the smallest value assigned to num such that the number 3 is printed from the last statement print(val)? Question 9 options: 5 1 3 Not possible 0 2



