What would be the appropriate line of code to write the function f(x) = e* as an anonymous function? Oy= e^(-x) O z = @lx) exp(-x) Oy- @ly) e^(-x) t- exp(-x)
Q: Why are watchdog timers required in many embedded systems?
A: The above question that is watchdog timer s required in many embedded system is answered below
Q: Find se thu th table orm C-
A: Combinational logic circuit: In combinational logic circuit, the output is dependant at all times on...
Q: Discuss a concurrent processing issue in an operating system.
A: Introduction: Concurrent processing is a kind of processing in which numerous processors work togeth...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: Use a request for proposal to gather information on hardware and system software:- A request for pr...
Q: Is it easier for you to identify someone using their fingerprints, speech intonation, face features ...
A: Answer: Everyone can choose based on the perspectives but I beleive Retinal scanning is going to rul...
Q: What is a distributed denial of service attack, and how can a single individual carry one out?
A: Introduction: What is a distributed denial-of-service attack, and how can a single individual carry ...
Q: C Language: Answer the following 1. Write an appropriate array definition for each of the following...
A: To define the array we can do like Int array[5] This will define the array of size 5 and then we ca...
Q: Use a request for proposal to gather information on hardware and system software, and explain why it...
A: Answer: In a formal document called an RFP, a target information system's requirements are outlined ...
Q: Is common morality possible in cyber Security
A: Cyber security: The term cybersecurity explicitly conveys its main ethical goal, namely to create a ...
Q: Explain skin smoothing and body modification with examples (photoshop)
A: Skin Smoothing : Step 1: Make A Copy Of The Image Step 2: Select The Spot Healing Brush Step 3: Set ...
Q: Please provide an example of a computer-based system and a list of its characteristics. Provide at l...
A: Software, hardware, people, a database, documentation, and procedures are the components of computer...
Q: Write a C# programto convert currency from US$ to South African Rands. Declare the amount in US$ as ...
A: I give the code along with output and code screenshot
Q: What are the disadvantages of using the SSTF disc scheduling algorithm?
A: Here in this question we have asked that what are the disadvantage of SSTF disk scheduling algorithm...
Q: Convert the decimal number 11910 (base 10) to binary (base 2). Convert the decimal number 20810 (bas...
A: 1) To convert decimal number to binary number We can divide the given decimal number recursively by...
Q: Write a program in Python to get basic salary, house rent allowance and transportation allowance fro...
A: Answer: I have done code and also I have attached code and code screenshot as well as output
Q: Compare the advantage of doubly linked list over single linked list by giving a reason to perform th...
A: Advantages of doubly linked list over the single Linked list.
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: There are six types of topology. Bus topology Ring topology Mesh topology Star topology Tree top...
Q: What do you consider to be critical infrastructure?
A: Critical infrastructure: Critical infrastructure play a vital role in supporting modern society. It ...
Q: What are the two types of files, in general, that exist? In what ways do these two file formats diff...
A: A document can be characterized as an assortment of information or data. Notwithstanding, the PC dea...
Q: QUESTION 2 Given the following ARM assembly program, What will be the value stored in register R2 by...
A: Answer is 0 (Zero)
Q: Write a C++ program will ask the user to enter 5 numbers and then present with their sum.
A: Required:- Write a C++ program that will ask the user to enter 5 numbers and then present them with ...
Q: What role does cryptology play in information security? What would be the implications if cryptogra...
A: The role of cryptography in information security:- Cryptography is a data protection strategy used t...
Q: C Language Write a c function called REVERSE that takes an array name X as an input parameter and a...
A: Here is your code with an output.
Q: Man-in-the-middle (MITM) assaults are difficult to prevent. Give a detailed response.
A: Man in middle attack: Man in middle attacks are a common type of cybersecurity attack that allows ...
Q: 14. Convert the following decimal number to negative binary number, using 2's complement in 8 bits a...
A: a) Given number is in decimal form that is: 87 Binary form of 87 is: Division Quotient Remainde...
Q: Compare and contrast pivot tables to multidimensional analyses.
A: The answer is
Q: What was the impetus for the creation of the RISC architectural concept?
A: RISC stands for Reduced Instruction Set Computer. RISC is a CPU design plan based on simple orders ...
Q: MENTION R CODE Using OECD data produce a scatterplot of 'Environmental Policy Strigency Index' and '...
A:
Q: Examine different methods for gathering evidence from social media networks."
A: The solution to the given problem is below.
Q: What are the differences between IT security solutions used in a traditional on-premises data center...
A: Common data center IT solutions: 1> The data center contains negatives and backups made locally 2...
Q: Can there be a common morality, why or why not?
A: the answer is
Q: How can i check the type of signature of a method. (Assume that signature may be from the array or s...
A: In JAVA: Java method signatures are composed of a name, number, type, and order of parameters. When ...
Q: What are three options that could be used in a project based on the decision tree structure? What ap...
A: Decision Trees: A large part of the danger control method entails searching into the destiny, lookin...
Q: Filter programmes such as sed and awk are often used to format data in pipelines. Is this a true or ...
A: Explaination As the name suggest filter programs . We already know what is filtering right ? Filter...
Q: 1. Ceate e program uing rkedhet L acceph Snodes telemerti ond 2 Acceprs on indexwhere the nece shoui...
A: In Java, we have list.add(index, element) method which adds the element in the list at index positi...
Q: - 9. Use string methods to extract the website domain from an email, e.g., from the string "tomas.be...
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining ques...
Q: What does the first compound notation mean?
A: Introduction: MicrocontrollerMicroprocessor8085. Signed integers may be represented in computers in...
Q: David is used to doing programming in Python and since the print() function in Python by default pri...
A: in PHP, \r\n can be used to print newline.
Q: Design in JFLAP a simulator of a finite deterministic automaton that (only) recognizes Even length b...
A: Solution: To designing the finite automata for the even length binary number , We know to that the b...
Q: Map the car sale ER schema into a relation schema. Specify all primary keys (underline) and foreign ...
A:
Q: In PLC through using the SCL language inside the TIA PORTAL, write the codes to create FESTO MPS Dis...
A: main.kt package de.itemis.mps.gradle.modelcheck import com.fasterxml.jackson.dataformat.xml.XmlMap...
Q: What does the term "reduced" imply in the context of a computer with a restricted instruction set?
A: A Simplified Set of Instructions Computer is a form of microprocessor architecture that makes use of...
Q: Write an appropriate array definition for each of the following problem situations: a. Define a one-...
A: The first will be an integer array and the next two will be character arrays The implementation of e...
Q: Given that both cache memory and random access memory (F unclear why cache memory is required becaus...
A: given - Given that both cache memory and random access memory (RAM) are transistor-based, it'sunclea...
Q: malyze Relationships Having more or less decided on our core objects, we now want to analyze the rel...
A: Answer : Yes, Objects can be inherit from the other objects. Whenever, any objects is inherit from ...
Q: A filesystem must be utilised by all partitions on a hard disc drive once it has been formatted. Is ...
A: a file system must be utilised by all partition on a hard disc once it has been formatted true or f...
Q: Why isn't virtual memory utilised more often in embedded systems?
A: Virtual Memory is an approach to overseeing memory which is a new pattern of the innovation utilized...
Q: A list of five common network topologies should be included. Which one do you think is the most trus...
A: Introduction: The arrangement of a network's connections and nodes, or its topology, is referred to ...
Q: 2. Translate below math expressions into Python expressions: a. (3 + 4)/5: b. n(n-1). 2 c. 4m2?: d. ...
A: code:- print((3+4)/2) Output:-
Q: The number of dr specified by the c disks? What are disks in terms ofe during rebuild? ehi
A: given - The number of drives that are clustered together in a single RAID 5 array can bespecified by...
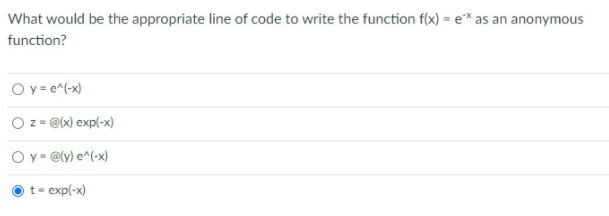
What would be the appropriate line of code to write the function f(x) = e-x as an anonymous function?
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- You are a product manager and currently leading a team to develop a new product. Unfortunately, the latest version of your product fails the quality check. Since each version is developed based on the previous version, all the versions after a bad version are also bad. Suppose you have n versions [1, 2, ..., n] and you want to find out the first bad one, which causes all the following ones to be bad. given is an API bool isBadVersion(version) which returns whether version is bad. Implement a function to find the first bad version. You should minimize the number of calls to the API. please write code in pythonWrite a function that when given a URL as a string, parses out just the domain name and returns it as a string. Examples:domain_name("http://github.com/SaadBenn") == "github" domain_name("http://www.zombie-bites.com") == "zombie-bites"domain_name("https://www.cnet.com") == "cnet"Note: The idea is not to use any built-in libraries such as re (regular expression) or urlparse except .split() built-in function""" # Non pythonic waydef domain_name_1(url): #grab only the non http(s) part full_domain_name = url.split('//')[-1] #grab the actual one depending on the len of the list actual_domain = full_domain_name.split('.') # case when www is in the url if (len(actual_domain) > 2): return actual_domain[1] # case when www is not in the url return actual_domain[0] # pythonic one linerdef domain_name_2(url):I am having a hard time understanding the output of this program with shadow and deep binding. Can someone explain it more in detail? I posted the answers below x : integer – – globalprocedure set x(n : integer)x := nprocedure print x()write integer(x)procedure foo(S, P : function; n : integer)x : integer := 5if n in {1, 3}set x(n)elseS(n)174 Chapter 3 Names, Scopes, and Bindingsif n in {1, 2}print x()elsePset x(0); foo(set x, print x, 1); print x()set x(0); foo(set x, print x, 2); print x()set x(0); foo(set x, print x, 3); print x()set x(0); foo(set x, print x, 4); print x() Here are the answers to the questions. The program prints = 10 20 30 40 with shallow binding The program prints = 10 52 00 44 with deep binding,
- write a python code named get_total_cases() takes the a 2D-list (similar to database) and an integer x from this set {0, 1, 2} as input parameters. Here, 0 represents Case_Reported_Date, 1 represents Age_Group and 2 represents Client_Gender (these are the fields on the header row, the integer value represents the index of each of these fields on that row). This function computes the total number of reported cases for each instance of x in the text file, and it stores this information in a dictionary in this form {an_instance_of_x : total_case}. Finally, it returns the dictionary and the total number of all reported cases saved in this dictionary. (Suppose we want to know the total number of cases reported on each date, so use x = 0.) >>> result, total_cases = get_total_cases(database, 0) >>> display_dict(result) 2021-05-19: 8 2021-05-20: 2 2021-05-21: 1 2021-05-22: 1 >>> print(total_cases)Write a program that first gets a list of six integers from input. The first five values are the integer list. The last value is the upper threshold. Then output all integers less than or equal to the threshold value. Ex: If the input is 50 60 140 200 75 100, the output is: 50 60 75 For coding simplicity, follow every output value by a space, including the last one. Such functionality is common on sites like Amazon, where a user can filter results. Your program should define and use a function: Function outputIntsLessThanOrEqualToThreshold(integer array(?) userVals, integer upperThreshold) returns nothingPHP Write a matchIPAddress function Write a function matchIPAddress($str) that takes a string representing an IP address as a parameter. The function should return true if the IP address is valid, and false if it is not. An IP address consists of a series of 4 numbers on the range 0-255 separated by dots (e.g. 192.168.0.1). Use regular expressions with capture groups and some additional validation in your solution (e.g. preg_match).]
- Write a program in C/C++ that reads N number of nonnegative decimal numbers from a user and creates a hash table to store the numbers. The output of the program displays the order of the numbers in the hash table. The program then prompts the user to enter a target value. The program searches the target value to the hash table, and displays the search outcome. For simplicity, let’s assume that N = 6 and the size of the hash table is 10. Use this hash function in your code h(k) = 2k+3 where k is the key value. Use linear probe method for collision resolution. Example test run Test Run 1: Enter 6 elements: 3 2 9 6 11 13 Hash table order: 13 9 - - - 6 11 2 - 3 Enter the target: 1111 is located at index: 6 Test Run 2: Enter 6 elements: 3 2 9 6 11 13 Hash table order: 13 9 - - - 6 11 2 - 3 Enter the target: 1515 is not in the tableWrite a function that converts encoded HTML into actual HTML. The function will take a string of text, and then a hashmap, mapping html tags to a list of tuples, where each tuple represents the first and last index of the string that the tags need to encompassINT_MIN = -32767 def cut_rod(price): """ Returns the best obtainable price for a rod of length n and price[] as prices of different pieces """ n = len(price) val = [0]*(n+1) # Build the table val[] in bottom up manner and return # the last entry from the table for i in range(1, n+1): max_val = INT_MIN for j in range(i): max_val = max(max_val, price[j] + val[i-j-1]) val[i] = max_val return val[n] # Driver program to test above functionsarr = [1, 5, 8, 9, 10, 17, 17, 20].
- Write a function encrypt that receives a message with a string or character vector and returns the message that is encrypted. This function returns the message concealed in the input string that is the first letter of each word in the string (or char vector) and returns a string that contains the first letter of each word in the input string. >> string = ‘This is the third question of final exam’; >> m = encrypt(string) m = ‘Tittqofe’Write a C++ program using Windows API to RemoveDirectory – For Removing the Directory BOOL RemoveDirectory(LPCSTR lpPathName); Return Type – Boolean (TRUE or FALSE). LPCSTR – Long Pointer to constant String. lpPathName – Directory Path Which one you want to delete. If this function Fails then its return FALSE or ZERO. Also We can print the Error Information with the help of GetLastError() function. RemoveDirectory Function Link.In Python, The function concatAltChars takes a string parameter s and a boolean parameter even; the function concatenates together either the even-position characters of s or the odd-position characters of s, depending on whether even is True, or False, respectively. The accumulated string is returned. For example, the even-indexed characters of "HANOVER" are at indexes 0, 2, 4, and 6: H N V R. So, concatAltChars("HANOVER", True) returns the string result "HNVR". But concatAltChars("HANOVER", False) returns the string result "AOE". For example: Test Result s = "goldfinches" print(concatAltChars(s, True)) glfnhs s = "A" print(concatAltChars(s, True)) A s = "A" print(concatAltChars(s, False))











