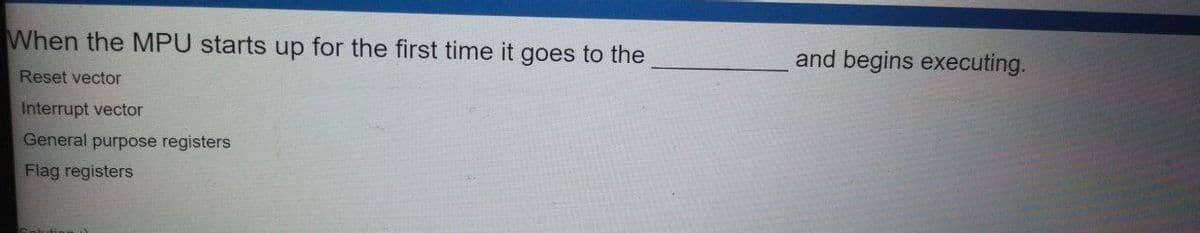
When the MPU starts up for the first time it goes to the and begins executing. Reset vector Interrupt vector General purpose registers Flag registers
Q: A- System.out.print(Math.floor(5.7));
A: 1) We have a statement in question System.out.print(Math.floor(5.7)); 2) To understand this statem...
Q: What's the use of big-O notation? Relate to the Java data struct.
A: By using this Big-O notation we can measure an algorithm's efficiency.
Q: The netstat command (available on Linux and Windows) displays a computer's active network connection...
A: The netstat command (available on Linux and Windows) displays a computer's active network connection...
Q: Why do the size and format of physical addresses differ depending on the network?
A: Introduction: A physical address (also known as a real address or a binary address) is a memory addr...
Q: ite a C program to find words in a word search. User types the word and the program confirms which r...
A: Lets see the solution.
Q: Which kind of parallelism (data or control) is optimal for SIMD? What kind of parallelism does MIMD ...
A: Introduction: Program-level parallelism is decentralizing a single program and running it on several...
Q: Write a program in Java for the below situation In a royal casino, there is a lottery at 14 number c...
A:
Q: Which kind of parallelism (data or control) is
A: given - Which kind of parallelism (data or control) is optimal for SIMD? What kind of parallelism do...
Q: 2. How information technolog 3. How information technolog 4. How information technolog
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN ...
Q: 149. Write a C# Sharp program to create a new list from a given list of integers removing those valu...
A: List is a data structure used to store the elements of both primitive and class type objects. The be...
Q: Write a JAVA program in which the user enters the initial velocity u, time of travel t, and the acce...
A: As given, we need to write a Java program that takes initial velocity u, time of travel t and the ac...
Q: Carry out the Select algorithm on the following set, using k = 19 (return the element of rank 19). S...
A: So, basically the select algorithm is used to sort a given array or a list of integer elements . The...
Q: What impact does a data leak have on cloud security? What are some of the potential countermeasures?
A: Introduction: Data breaches can in many forms, including stolen information, ransomware, phishing, p...
Q: 31 fe a tee-ievel cache ryte he aces times of L d ia cches ei dchek cycles, gectirely. The i penalty...
A: Miss rate of L1 cache= 0.111 Miss rate of L2 cache= 0.055
Q: Write a python program to find the potentia energy using the total energy & kinetic energy. All the ...
A: The Python program is given below
Q: A GSM syatem uses 124 channels and each channel is divided into time slots. What is fhe maximum numb...
A: The given question is A GSM system uses 124 channels and each channel is divided into 8 time slots. ...
Q: Describe the function of each of the following types of keys: primary, alternate, secondary, and for...
A: A key in a database table is a column or group of columns that are used to define some property of t...
Q: Ada Lovelace did what?
A: Ada lovelace did what ?
Q: There are many different types of data in Big Data. For Big Data processing, a language other than S...
A: Big data is defined as data with higher variety, volume, and velocity. Big data is defined as enormo...
Q: This question is about the Hadamard code corresponding to the 16 × 16 Hadamard matrix created by Syl...
A: Here our number is 55536, after converting even numbers to zero and odd numbers to 1, our message wi...
Q: Which kind of parallelism (data or control) is optimal for SIMD? What kind of parallelism does MIMD ...
A: Introduction: Program-level parallelism is decentralizing a single program and running it on several...
Q: For this reason, Access is a better tool to use than Excel to keep track of this kind of information...
A: Answer: When it comes to keeping track of data, Ms. Access is much superior than Ms. Excel. MS Acce...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: We need to write a program in PHP programming language to convert the temperature from Degree Celciu...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: Given: To write a php program to convert the temperature in Fahrenheit from the degree celcius.
Q: (Lecture 2] The rísk equation is: R = Tx Vx C, where, Ris the estimated risk, Tis the probability fo...
A: A simple emphasis on the planning stage isn't enough to deal with security issues properly. The vari...
Q: 11. Solve the given logic circuit and find the Boolean expression for the output variable Y. A B
A: Solve the given logic circuit and find the Boolean expression for the output variable Y.
Q: Create a python program that the user will input 3 positive integers (A,B & C) where A & B represent...
A: read three numbers A,B and C iterate from A to B Pass each number in summation function to get t...
Q: (our task is to make a point calculator which takes a point in the 1st quadrant and then finds its p...
A: Logic:- read first quadrant points x and y if x>0 and y>0 Read quadrant location(1,2,3,4) ...
Q: How can i convert the temperature in Fahrenheit from the degree celsius which is entered by user in ...
A: We need to write php script to change temperature from Fahrenheit to celcius.
Q: a Website that give you coordinates of current location in the alert Design prompt when you click a ...
A: Required:- Design a Website that gives you coordinates of the current location in the alert prompt w...
Q: Write one line of code ONLY. With slicing, print to be in the string, all in lower case, using the v...
A:
Q: he physical layer is concerned with the transmission of bits across a physical media. Clarify?
A: Introduction: The physical layer is concerned with the transmission of bits across physical media. C...
Q: Consider a poorly built web application for an online shopping site that saves the price of each ite...
A: Introduction: A website's web page (or webpage) is a hypertext document presented to a user through ...
Q: Which kind of parallelism (data or control) is
A: given -Which kind of parallelism (data or control) is optimal for SIMD? What kind of parallelism doe...
Q: How do I adjust the minimum and maximum under Bounds in excel graphing. Also, under units the major ...
A: adjust the minimum and maximum under Bounds in excel graphing. Also, under units the major and min...
Q: def create_scrabble (user_input): tile_dict = { 'A': 1, 'B': 3, 'C': 3, 'D': 2, 'E': 1, 'F': 4, ...
A: Looks like there is no error in code may be you should try other compiler : Here I tried to run in J...
Q: Assume that a relation is kept in a B+-tree file structure. Assume secondary indices keep track of r...
A: Introduction: Indexing is a data structure that improves database efficiency by minimizing the numbe...
Q: what strategies can you use to distinguish fake information on social media?
A: False or misleading material masquerading as authentic news is referred to as fake news. Deliberatel...
Q: Chinese Wall model: consider following COls and CDs: Bank COl class: Chase Bank, US Bank, Citi Bank ...
A: China's Wall: A model These CDs and COIs should be taken into account: Conflicted banks include Chas...
Q: A GSM system uses 124 channels and each channel is divided into 8 time slots. What is he maim bandwi...
A: The answer is
Q: What is Standard Error, and what does it mean?
A: Standard Error is the approximate standard deviation of a statistical sample population. The smaller...
Q: Use ggplot2 to create a scatterplot to observe how winter game "Alpine Skiing" medalists' age change...
A: PresentationThe 'cutting edge Olympics' involves every one of the Games from Athens 1986 to Rio 2016...
Q: What steps should a corporation take to deter workers from violating company policies or committing ...
A: Introduction: A code of ethics is another term for a code of conduct. A code of conduct is a collect...
Q: or WriteChar, describe what it does
A: White Char ( WhiteSpace Character ) : Computer programming consists of 250 chaacters mapped fom asc...
Q: where are 2 place you can search for app that work with quickbook online
A: Here we have given two apps name that work with quickbook online. you can find them in step 2.
Q: How are truly distributed systems modeled?
A: Distributed system model are as follows - Architectural Models Interaction Models Fault Models Arc...
Q: QUESTION 1 Write a complete program that consists of the main function that will call 4 user-defined...
A: logic:- To repeat users calculation, use while(1) loop and in one of choice put break. Use two fun...
Q: The instruction LH is a/an- R-format instruction I-format instruction J-format instruction Save O O
A: LH: It stands for Load Halfword. LH instruction has two operands. First operand is a general purpos...
Q: What level(s) of input/output manipulation can an assembly language programme perform?
A: What level(s) of input/output manipulation can an assembly language programme perform?
Q: our task is to make a point calculator which takes a point in the 1st quadrant and then finds its po...
A: The given problem needs a program to be written in Java where the user will enter the original point...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- When a value is read from a memory location, the value in that location is preserved;this process is said to be_____________This kind of memory is used to temporarily store information that is often accessed. A few of its features and instances are shown below:The following elements are always present in the random access memory (RAM) of an operating system:
- Computer Science In x86-32 Assembly language using extern functions fopen, fprint and flclose. Create a file with "hello" inside and copy it to another file.If a user requires information to be immediately available to the CPU, it should be stored in secondary storage.When creating instructions that access variables, why is it not a good idea to use numeric addresses?
- C Programming Language Task 1 - Create a file called data by running this command: head –c 10000 /dev/random > data Task 2 - Create a program that uses mmap to map data into memory, then creates a shared memory area and uses memcpy to copy the data from the mmap’ed memory into the shared memory area.Data must be turned into before it can be transferred.The size of the main memory location is called a _______________. a. Word. b. Set. c. Line. d. Block.



