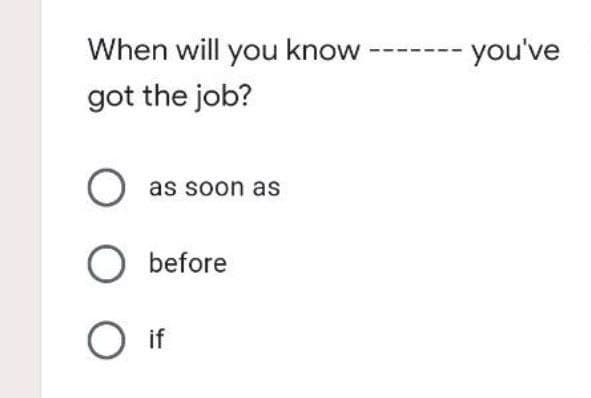
When will you know got the job? you've
Q: Is having a working understanding of computers useful? What are some of the good consequences of…
A: Computer technology is the use and study of computers, networks, languages, and storage spaces to…
Q: What type of long-term repercussions does a data breach have for the cloud's security, and how…
A: The loss of client trust is the most important long-term effect of a data breach: Customers entrust…
Q: When it comes to modeling software systems, what factors should be taken into consideration?
A: Introduction Software systems are the systems that are used for the intercommunication components…
Q: What are the benefits of learning Boolean expressions and gate logic?
A: The following are some of the advantages of studying Boolean expressions: - Understanding and using…
Q: What precisely is a poison package attack, and what does it mean? Please describe two examples of…
A: Introduction: ARP Poisoning also referred to as ARP Spoofing, is a kind of Internet assault on a LAN…
Q: B. Suppose the left hand switch is a subnet with the last byte as the host address. Write the subnet…
A: (B) Given that the left-hand, switch subnet has the last byte as the host address. Hence, Host ID =…
Q: Fig 1 Change Pictures Select Picture to Display Sunset Display a photo of water lilies. Winter Scene…
A: Code:
Q: What exactly is multifactor authentication and why is it useful? What role does it play in the…
A: The question has been answered in step2
Q: How long two years. If I I in the bank? For has you worked have you worked had you worked * -‒‒‒‒‒‒…
A: 1) First stament is How long ______ you worked in the bank ? For two years . Let's understand what…
Q: There is an extensive discussion on DNS records, authoritative and root servers, iterated and…
A: Introduction: Domain Name Servers (DNSs) are the devices that map the hostname to the IP addresses…
Q: Create a list of all of the various types of DNS records that are currently in use. It is important…
A: Given: Explain the various types of DNS records and offer examples. Is it possible for a company's…
Q: For this challenge, you will write a program that prompts a user to answer whether or not they are…
A: Find the required code in python given as below and sample output :
Q: What are the best estimates of the worst-case running times of the following operations in big-O…
A:
Q: The concepts described up to this point are the fundamental elements of a high-level programming…
A: Answer to the given question: Most contemporary programming is completed utilizing high-level…
Q: Write a python3 function sqr( n ) that returns the square of its numeric parameter n.
A: According to the information given. we have to write python3 function sqr( n )that returns the…
Q: Is it possible to write out the steps involved in the object-oriented programming analysis and…
A: The above question is answered in step 2 :-
Q: How does the DNS system make use of iterated and non-iterated requests, authoritative servers and…
A: The Answer is in given below steps
Q: How do the rows in a table in a database organize the data that is stored in them?
A: A database is an organized collection of data for easy access and control. You can organize data…
Q: the flow of information
A: It is the bearing where information streams between two communication gadgets that is characterized…
Q: Despite the fact that sudo is the command of choice, root may be accessed by anybody on certain…
A: SUDO:- sudo (Super User DO) order in Linux is by and large utilized as a prefix of some order that…
Q: Is it feasible to differentiate between the various kinds of authentication with regard to the level…
A: Distinguished: To be differentiated is to value someone. Outstanding people are often older,…
Q: computer science - Explain the function of any three to four value stream measurement parameters.
A: Introduction: Various Value Stream Measurement parameters are:
Q: What are the benefits of an operating system architecture based on a layered design approach? Is it…
A: Introduction: Semantics is a branch of linguistics concerned with the understanding and meaning of…
Q: Give one example for each of the addressing modes.
A: Addressing modes are only the various manners by which the area of an operand can be indicated in a…
Q: It is possible that UDP and IP both have the same amount of unreliability. Is there a rationale for…
A: Given: In terms of the UDP/IP debate, each have different levels of unreliability. Because its…
Q: Describe the components of an organization’s hardware and software infrastructure and highlight…
A: I will explain it with details,
Q: ibe the flow of information that occurs between the different parts of a web ap
A: Introduction: Below the describe flow of information that occurs between the different parts of a…
Q: A database system has taken the role of the traditional file processing system. Utilizing this fresh…
A: Introduction: A database(DBMS) is a logically organized collection of structured data, usually kept…
Q: Given the recent data breaches that have been publicized, is it possible that cloud security might…
A: Definition: Is it possible that a data breach might have a major impact on cloud security? What are…
Q: Do you believe there is a difference between the computer that is being used by the user and the…
A: 1) WHAT IS A Client Server Network?A client server network includes multiple clients or workstations…
Q: What are the drawbacks of using UAC functionality within Windows 10/8/7? Should standard user…
A: The above question is answered in step 2 :-
Q: There are 3 algorithms to solve the same problem. Let n = problem size. Suppose that their runtime…
A:
Q: Design a FORTRAN program segment to do the following: a) Find the sum of vectors A and B, and store…
A:
Q: Can you walk me through the process of designing a physical database?
A: A physical database is a method of transforming a data model into the physical data structure of a…
Q: Despite the fact that sudo is the preferred way of accessing the root account on certain Linux…
A: Sudo is the preferred way of accessing the root account on certain Linux systems but why ?? Main…
Q: computer science - Choose any two infrastructure-centric indicators that are used to assess IT…
A: Introduction: IT metrics are quantitative measurements that help IT leaders run the business of IT…
Q: Define social engineering. Provide a detailed example of how an attacker might execute a social…
A: Information technology and Network society is based in the communication technologies and the…
Q: Describe how the arithmetic operators really function.
A: Arithmetic Operator is used to performing mathematical operations such as addition, subtraction,…
Q: How does a vulnerability scan evaluate the current level of security?
A: A vulnerability scanner is an application that identifies and creates an inventory of all the…
Q: What is encryption
A: To secure the data while data transfer is big task. So many attackers try to hack the data what we…
Q: Following diagram is the confusion matrix for multi classification. Find the precision and recall.…
A: Given that confusion matrix. We need to find the precision and recall. See below steps.
Q: Which of the following is not a technique to avoid a collision? a) Make the hash function appear…
A: The hash random function, chaining method, and uniform hashing are used to avoid collisions. With…
Q: What, if anything, can we learn about our obligations as security practitioners on a national and…
A: Introduction: International security, often known as global security, refers to the measures taken…
Q: Explain the line coding approach and describe the encoding process (Digital Data to Digital Signal).
A: Encoding technique: Encoding is the way of converting the data into specified format and all this…
Q: Explain Network database system, a database management system based on the notion of ownership.
A: Introduction: The network database system is an ownership-based database management system.
Q: The use of selection structures is very important in programming, yet these structures cannot…
A: Let's look at the answer. The terms "frontend" and "backend" are used most often in web development.…
Q: Is it feasible to distinguish between different methods of authentication in terms of security?
A: Intro Distinguished: Being distinct implies appreciating someone. It is not unusual for exceptional…
Q: Using a certain form of processing, is it feasible to avoid wasting computing cycles while…
A: Introduction This article was written to address the topic of write-blocking, which is a prevalent…
Q: Object-oriented and procedural programming languages each have their own unique set of strengths and…
A: Object oriented programming Object oriented programming mainly works with the object(that represents…
Q: Write a C program for a match-stick game between the computer and a user. Your program should ensure…
A:
Step by step
Solved in 2 steps with 2 images

- posting so so so many times dont dont dont answer iwthout sure sure strict report to quality team dont waste my quesstionnn dont answerrrr!!!!dont dotn dont answer without 100% knwoledge else sure sure strict warning want full fledged answer very strictly sayingdont dont dont answer if not 100% sure else sure sure compliannt very strict warning
- dont dont dont post unncesssary answer sure strict warning posting soo soooo many times dont waste my question very very very seriously sayinggggposting so so so sosososo man y timesss dont test my patience and dont dare to answer dont dont waste my question multiple dislikes for sure dont dare to answerIt's not the same thing to "save" us as it is to "rescue" us.

