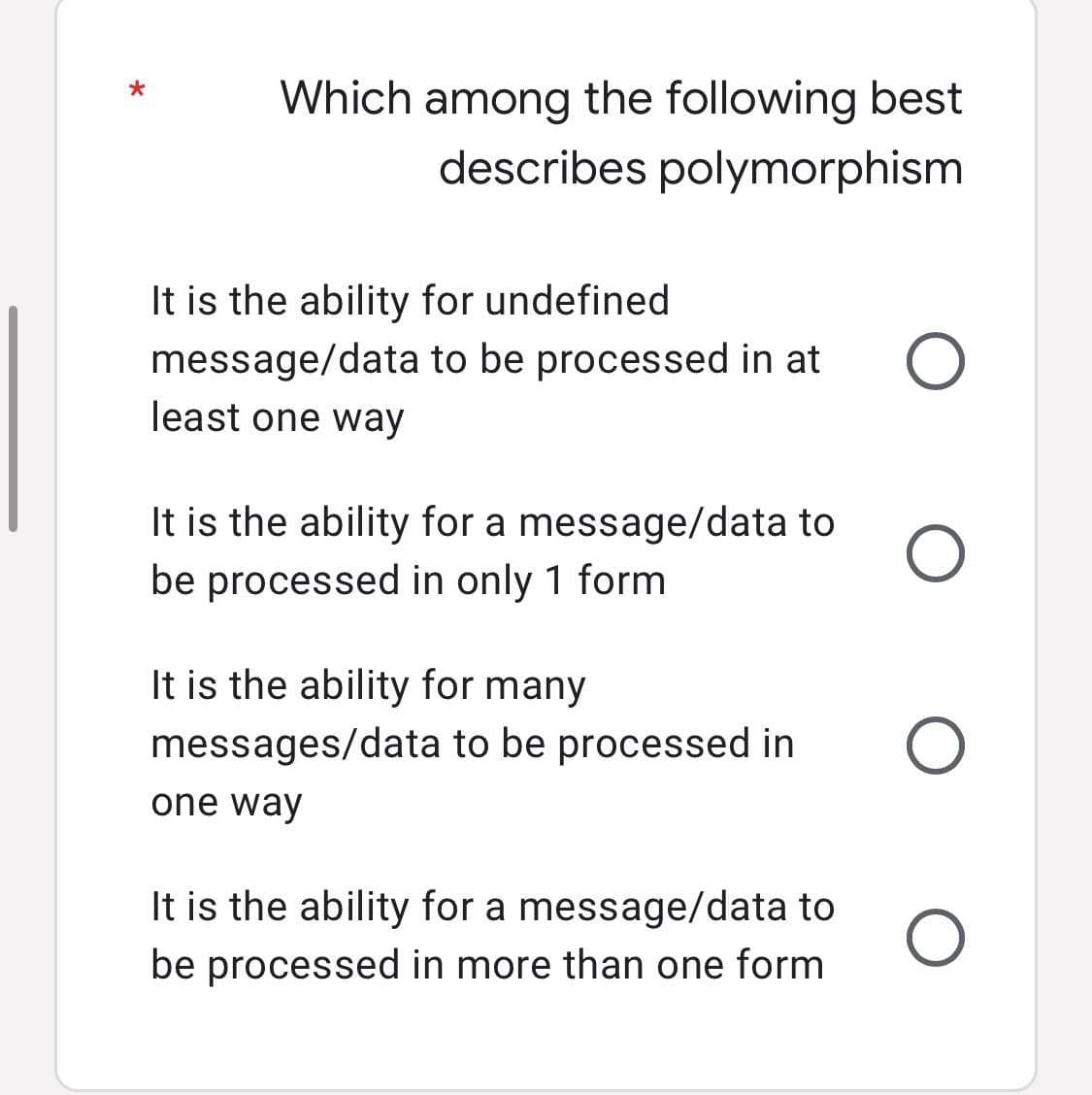
Which among the following best describes polymorphism
Q: Before going into specific examples, provide a general overview of real-time operating systems.…
A: Keeping up with events as they happen in real time: In circumstances in which a large number of…
Q: Write a C++ program that prints the following figure using for loop ✰✰ *** **** *** **
A: Algorithm: The algorithm to print given pattern is: Start Initialise the variables i, j, n Read the…
Q: Q4/ Convert the following algebraic expressions into expressions in Mat lab: 1) z=e-10t - cos(0-a) +…
A: Hello student Greetings Hope you are doing great As per our policy guidelines, in case of multipart…
Q: 1. Write a program in C to find the number of times a given word 'the' appears in the given string.…
A: A string is a sequence of characters terminated with a null character \0.
Q: B-Write C++ program, to read 7°5 2D-array, then find the summation of the array elements, finally…
A: #include <iostream> using namespace std; // Get the size m and n #define M 7 #define N 5…
Q: Is it feasible for a MAC address to be shared by two different network interfaces? Is there a reason…
A: Introduction: When a computer connects to a network, whether it be public or private, this is known…
Q: Joe's lived in that flat since 2012 a year O two years O ages a long time O Robert usually goes to…
A: The Answer is given below step.
Q: When it comes to data backup and recovery, what are some of the most significant considerations?
A: Given: During the process of backing up and recovering data, careful preparation is carried out to…
Q: ?Describe the processing of 00111 by using IDs
A:
Q: Discuss the benefits and drawbacks of performing regular software updates.briefly.
A: Introduction: Updating programmes and software is supposed to help you a lot because it brings new…
Q: their work, they. __home had finished / had gone O finished / had gone O None of other options O…
A: Here is the solution:
Q: 3-5. Summation: Given nums resw 5, complete the code below to compute for the sum of 5 numbers…
A: Find the required answer with explanation given as below :
Q: Guice is a popular dependency injection library in the Java programming language. However, there are…
A: Introduction: Dependency Injection handles difficulties like how an application or class can be…
Q: The following instruction is in valid form (legal form) SHR AX,BX Select one: True False
A: Given question are true or false based question.
Q: NotAnonCo has developed a machine learning application to determine the identity of users who post…
A: Here we have given a brief idea regarding the questions asked. You can find the solution in step 2.
Q: * .Root vertex in a derivation tree must be labeled by the start symbol True False O
A: you asked multiple questions about True or false. but as per Bartleby's guideline, I can only answer…
Q: In what ways are layer 2 and 3 switches different? If you were to buy a switch, which one would you…
A: MAC Address: Each device on a network is identified only by its Media Access Control address (MAC…
Q: 1. The following (Name, Race, Stats) are the information needed for character creation in a RPG…
A: //code in java package game;import java.util.*; abstract class Name{ abstract String pname();…
Q: When a web client requests access to protected server resources, apply native authentication and…
A: Start: Layering network protocols and services simplifies networking protocols by breaking them down…
Q: There must be a reason for interruptions, but what is it? What is the difference between a trap and…
A: Interrupts: Interrupts are signals provided by I/O devices to the CPU, instructing the CPU to halt…
Q: degrees ve). Assume yo A inage should keep od at a tem ature have a non-empty list of integer and/or…
A: logic:- define an empty lst, empty=[] iterate for each element in temperatures list. if i<0…
Q: Is it feasible to have the same MAC address on two distinct devices? Whether or whether this will…
A: MAC address : Media Access Control (MAC) addresses are hardware identifiers that uniquely identify…
Q: What's the difference between computer architecture and management?
A: Computer Architecture is concerned with the interconnection of hardware components to construct a…
Q: When a web client requests access to protected server resources, apply native authentication and…
A: Launch: Layering network protocols and services simplifies them by separating them into smaller,…
Q: For systems in which one component creates data, which architectural pattern is best?
A: Architectural pattern: An architectural pattern is a fundamental principle that specifies the…
Q: What is the effect that the access method of the memory component has on a machine? How does…
A: Answer:
Q: What does the term "operating system" refer to? What are the two primary functions of the operating…
A: Answer:
Q: 1. Select one of the listed protocols. • Routing Information Protocol • Open Shortest Path First •…
A: 1. select one protocol RIP 2 . create and demonstrate selected protocol using Huawei eNSP
Q: What impact do the methods for handling interrupts have on the performance of the machine?
A: Interrupt is the signal which is emitted by the software or hardware when the process or the event…
Q: You developed an interactive solution for computerising registration and administration at the…
A: Introduction: The use of technology tools in general curricular areas to assist students to apply…
Q: ation D are router R. received by 200 bytes S.C.
A:
Q: her for everything she have thanked / has done O thanked / had done O None of other options O had…
A: The given questions are fill in the blank type questions.
Q: Compare two alternative topological types and provide an example of when one would be more efficient…
A: A topology is the physical or logical structure of devices that shares information.
Q: What Are the Stages of an Instruction Cycle?
A: Introduction: Every instruction cycle, the computer goes through the following phases: Fetch: The…
Q: Differences between Harvard and von Neumann architectures may be summarized as follows:
A: Generally, any micro-controller is an arrangement of its CPU components, specifically RAM and ROM.…
Q: In what ways are layer 2 and 3 switches different? If you were to buy a switch, which one would you…
A: What is the difference between layer 2 and layer three switches? Which switch would you choose, and…
Q: Using your own words, walk us through how each of these activities may be accomplished on a computer…
A: System Programming and Application Programming: The major distinction between application…
Q: VM live migration is suitable for which of the following scenarios ? load balancing among datacenter…
A: Answer the above question are as follows
Q: 6. What is the name of the device that transforms computer output to a format suitable for…
A: Introduction: Data sent over a phone line will be encoded and then decoded at the receiving end.
Q: Multi-tape machines simulate Standard Machines by use The language accepted by a TM are called The…
A: 1) The first question is not written in correct grammar format. Let me give some possible stuffs…
Q: What kind of files can't be opened (with fopen txt O bin O overloading O None of the above O
A: The solution to the given question is: NONE OF THE ABOVE
Q: Hi! Could you help me? I think something is wrong with my code but I couldn't figure out what. Also,…
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful.…
Q: Consider the following code. How many times is the function rec_func_2() called in total? options: 0…
A: #lets trace the given code to find out how many times rec_fun2() called in total: def rec_func_2(n):…
Q: When it comes to computers, what's the difference between architecture and organization precisely?
A: The question is to define the difference between architecture and organisation.
Q: We can overload only virtual ?functions
A: The answer along with the explanation is given below.
Q: {a=b+c; X=X*X; y=a+x; } is a compound statement. Select one: O True O False
A: Here is the solution:
Q: Convert infix notation to postfix notation: X+ (B+D-(D-E*F)-G)/H^Y
A: Algorithm to convert infix to postfix expression In this case, We use the stacks to convert infix to…
Q: Can you name and describe in detail at least five of the most common drawbacks associated with cloud…
A: Cloud computing eliminates the need for enterprises to have their own data centers by reducing the…
Q: computer science - What four e-commerce support technologies would you describe?
A: Introduction: Four supporting technologies are required for e-commerce:
Q: hat is a demilitarized zone (DMZ), and why is it necessary?
A: Explanations :What is DMZ : The acronym DMZ stands for 'demilitarize zone.' This refers to a network…
Step by step
Solved in 2 steps

- Exercise A: In this exercise, you are asking the user to set a alpha numeric password for any website. Put some conditions. Password must be 8 characters long. There must be at-least one uppercase letter There must be at least one number. Then show the user, you have set the correct password or not. Exercise B: This exercise is the extension of the above Exercise. In this exercise we are not checking all the criteria of having a good password. Here ask the user to enter his/her password twice. If both matches, thanks the customer otherwise loop your code until user enters both passwords same.5. Create a scalar-valued function named fnUnpaidInvoiceID that returns the InvoiceID of the earliest invoice with an unpaid balance. Test the function in the following SELECT statement: SELECT VendorName, InvoiceNumber, InvoiceDueDate, InvoiceTotal - CreditTotal - PaymentTotal AS Balance FROM Vendors JOIN Invoices ON Vendors.VendorID = Invoices.VendorID WHERE InvoiceID = dbo.fnUnpaidInvoiceID();Which of the following identifier forms is most readable? Support yourdecision.SumOfSalessum_of_salesSUMOFSALES
- In this question, don't change code just following the instructions #!/usr/bin/env python """ An example python script to illustrate how a projection might be simulated, and lead to an example GROUP BY ( using dictionaries to group and aggregate ) """ import sys, os, time import csv from datetime import datetime from optparse import OptionParser class SQLProjectionExample: def __init__(self): """ The SQLProjectionExample constructor includes the logic for arg handling. In effect, we assume this class will be run on the command line with a main. """ self._opt_defaults = {} self._opt_parser = OptionParser() self._opt_parser.add_option( '--table', '-t', action = 'store', dest = 'table', help = 'Table' ) self._opt_parser.add_option( '--columns', '-c', action = 'append', dest = 'columns', metavar = 'col', help = 'column' ) self._opt_defaults['test'] = False (self._opts, self._args) = self._opt_parser.parse_args() def show(self): """ Simple standard utility function for illustrating argument…I am having an issue creating this function with a trigger using postgreSQL (plpgsql). Could someone please help me solve this? Thank you! CREATE OR REPLACE FUNCTION Moreno_03_bankTriggerFunction()RETURNS TRIGGERLANGUAGE PLPGSQLAS$$BEGINCREATE TRIGGER Moreno_03_bankTriggerAFTER DELETE ON accountFOR EACH ROWWHERE depositor.account_number = account.account_numberEXECUTE PROCEDURE Moreno_15_bankTriggerFunction();END;$$ Database Schema: branch ( branch_name, branch_city, assets ) customer ( ID, customer_name, customer_street, customer_city ) loan ( loan_number, branch_name, amount ) borrower ( ID, loan_number ) account ( account_number, branch_name, balance ) depositor ( ID, account_number )C++ Exercise A: In this exercise, you are asking the user to set a alpha numeric password for any website. Put some conditions. Password must be 8 characters long. There must be at-least one uppercase letter There must be at least one number. Then show the user, you have set the correct password or not. Exercise B: This exercise is the extension of the above Exercise. In this exercise we are not checking all the criteria of having a good password. Here ask the user to enter his/her password twice. If both matches, thanks the customer otherwise loop your code until user enters both passwords same.
- Retrieve information from this webpage "https://www.chewy.com/b/dry-food-294", Dry Dog Food. The information you need is 1) the brand and the name of the products, 2) the price for auto ship, and 3) the regular price. For Q1 and Q2, you may need the function trimws() or gsub() to remove unwanted characters. Can i have the code you use pleaseOracle language 1-Display the JOB_ID and the position of the character S in the JOB_ID on jobs table as thefollowing:Search of the character S in the JOB_TITLE ResultS not found in the name Not FoundS in the last character of the name Last CharacterThe name contains the character S Contains SS in the first character of the name First Character 3. Display the employee’s name whose salary is within a range that is specified by theuser input as follows:Assume an Oracle database administrator has connected to a pluggable database. What will be the statements the DBA use to create a password verification function emp_pass_verify to enforce a password to conform to all the following rules:• contains at least 8 characters• contains at least one letter, at least one digit, and at least one specialcharacter (that is not a letter or a digit)• starts with an upper-case letter• does not contain the username as a substring
- Please create a Java Function called "ConnectToDbase" that will connect to the database. Assume that the middleware API is named "JDBCConnect". The details of the "JDBCConnect" function are below. // Returns true if successful, false if not successful boolean JDBCConnect(hostname, username, pass, database); // This is the Function you will call. You will code a Java function called "ConnectToDbase" that will call JDBCConnect. Assume that it returns a boolean value (true if successful, false if unsuccessful) Assume that it will have parameters for the values it will need to connect (e.g. hostname, ...) Print out an Error statement if you cannot connect.This is my question and assignemnt. Any and all help would be great! Create a PHP file named User.php. Create a class User with two attributes: $username (containing username) and $roles (containing a string array of roles such as admin or customer). Create a constructor that accepts a string username. Assign the username to the username attribute. Code example: $this->username = $username; Assign the role of 'admin' to the roles attribute. Code example: $this->roles = array('admin'); Create a function to retrieving user roles. Name it getRoles() that returns the $roles object. Do a test Create a new User and insert a username. Code example: $user = new User('groot'); Retrieve the roles from the user and print_r the content. Code example: $roles = $user->getRoles() and print_r($roles);You have been tasked to design a COVID-19 screening application for your campus. The guards ateach gate will screen the students and enter their details on the application. The capabilities andfeatures of the application should include a choice between the following functions:1. A screening survey which will allow guards to record the students’ screening data.2. Searching for a student’s details and status. Q.2.2 By means of pseudocode, demonstrate how overloaded methods can be usedin the COVID-19 application you are designing. (in pseudocode form)



