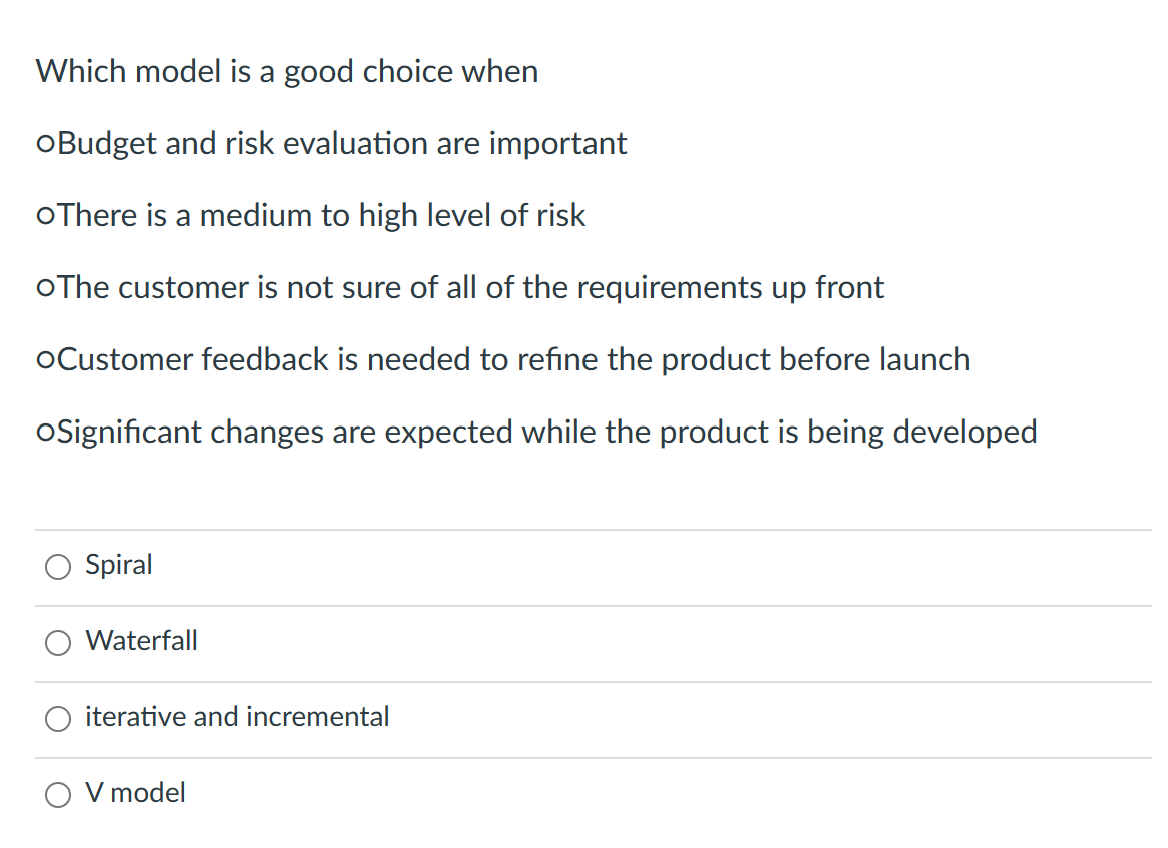
Which model is a good choice when oBudget and risk evaluation are important oThere is a medium to high level of risk oThe customer is not sure of all of the requirements up front oCustomer feedback is needed to refine the product before launch oSignificant changes are expected while the product is being developed Spiral Waterfall iterative and incremental O V model
Q: عبد الله المغلوث --
A: It seems that the speaker is making a general statement about the relationship between pressure and…
Q: You have been asked to create a program that takes 3 numbers from the user and finds their sum. For…
A: The software development life cycle and software development process are essential to creating…
Q: Please send me answer within 10 min!! I will rate you good for sure!! Please dont copy from internet…
A: This program generates 15 random demand values using the numpy library and fits a simple linear…
Q: Proposition Show that the marking algorithms LRU and FWF are.
A: Intruduction: a special online algorithm family for the paging problem called marking algorithms.…
Q: Perform the following subtractions using the 2s complement method: 1. - 11 10 0 1 10+ No Carry →…
A: Requirement: Perform the given subtraction using the 2's complement method. Steps for subtraction…
Q: F(L) = {0¹¹ a0¹ |a € A, n >0} Consider the condition that A is the language over {0, 1}. Using the…
A: Given language is, F(L)= {0na0n | a∈ A, n>=0} In this language, set of input alphabets are {0, a}
Q: Write a program which prompts the user to input 10 float numbers and store them into array. Find the…
A: I have provided C CODE along with CODE SCREENSHOT and OUTPUT…
Q: I need the python code for this system of differential equations. I have the octave code. In 1995,…
A: According to the question, We have to write python code for the following equation:
Q: Draw a flowchart for a program to convert meters to inches. The program takes input of length in…
A: Draw a flowchart for a program to convert meters to inches. The program takes input of length in…
Q: (d) L3 = {w| w doesn't contain 010} * (e) L3= {w| every even position of w is a 0}
A: (d) Definition of DFA recognizing L3 = {w| w doesn't contain 010}: A DFA is a 5-tuple (Q, Σ, δ, q0,…
Q: What is hibernate in Java
A: Introduction : Java is a well-known computer language that Sun Microsystems developed in 1995. A…
Q: The command pattern and strategy patterns are widely used patterns for encapsulating a behavior or…
A: The Command and Strategy patterns can be used to encapsulate behaviors or algorithms, but each…
Q: How do you change the default behavior of the print function that causes it to add a new line after…
A: Write how to change the default behavior of the print function that causes it to add a new line…
Q: Question 15 ( In the sprint planning meeting the product owner and sprint team negotiate which items…
A: A sprint planning meeting is when that of the team (including the Scrum Master, Scrum Product…
Q: Make a C / C++, Java, or Python program with two processes (or threads, whichever is easier for you…
A: The solution is given below
Q: Good access control policies require what two properties? Group of answer choices A smart user clear…
A: Access control policies: Access control policies are rules and regulations that are put in place to…
Q: What are the benefits of learning software methodologies for developers individually?
A: Software: Software is a set of instructions, programs, and data that is stored electronically on a…
Q: Draw a flowchart for a program to convert meters to inches. The program takes input of length in…
A: flowchart:- A flowchart is a graphical representation of a process that shows the steps that need to…
Q: Describe the halting condition for the recursive binary search and the reason why stopping…
A: A binary search algorithm is divide and conquer search algorithm which has logarithmic time…
Q: E. The relationship amb indicates that a and b are equivalent. The relationship asb indicates that a…
A: mod of any number gives the remainder of the number. for instance: 5mod2 = 1 since the remainder…
Q: can you explain the thought process behind the code?
A: The given Python program is as follows: import timeimport random def original_quicksort(input_list):…
Q: 3. This program is for extra credit. Write a MARIE program that takes you name as input and outputs…
A: The solution is given below
Q: Write a method to produce a new list with the real frequency of each name given two lists, one of…
A: ALGORITHM: 1. Define a function with the name "find_real_frequency" that takes "names" and…
Q: a, d and, f Fast pls i will give u like for sure solve this question correctly in 5 min
A: - We need to talk about the order of growth in functions a, d, f.
Q: The PatternAwareLetterFreqGuesser is an improvement over the naive approach, but it can still be…
A: Python code: from collections import Counterfrom string import ascii_lowercase class…
Q: Make a flowchart using Flowgorithm based off of this psuedocode (you might have to add items like…
A: Modified the given psuedo code, so that variables and declarations are included: Declare SetAlarm as…
Q: ogram in big-O notati
A: Given Code: Analyze the time complexity of this program in big-O notation, assuming the size…
Q: ng : Attach ouput screen shot of whole code and required. Else dislike sure. DinThe following table…
A: I have written the HTML code below as mentioned in the question:
Q: Given a matrix of size N x M where N is the number of rows and M is the number of columns, write an…
A: One possible solution to this problem is to use a modified version of Dijkstra's algorithm, a…
Q: he Ministry of Vybsie_Culcha intends to implement a grant for singers in order to offset…
A: The Ministry of Vybsie_Culcha intends to implement a grant for singers in order to offset…
Q: First, read in an input value for variable valCount. Then, read valCount integers from input and…
A: Algorithm of the code: 1. Start 2. Prompt the user to enter the number of values they wish to input…
Q: Mention two (2) Unary operators in Java and give two (2) sample expressions.
A: Unary operators are a type of operator that operate on one operand. In Java, unary operators are…
Q: Prove that, for any sets A and B, it is true that AU(ANB) = A. Hint. You must do lhs ≤ rhs and rhs…
A: Given that, A∪(A∩B)=A In this expression, the sets are A, B.
Q: C++
A: I have provided C++ CODE along with CODE SCREENSHOT and OUTPUT…
Q: 3. Construct an adjacency matrix for the graph shown in Figure: ( please write it in copy paste…
A: In graph theory, an adjacency matrix is describing the finite graph structure. It is the 2D matrix…
Q: Print and write code for sure if incorrect downvote sure I am creating a html web page and I need…
A: Here is an HTML code for a simple web page with two tabs, "Fish" and "Dogs": Code: <!DOCTYPE…
Q: 1. C language requires objects to be declared before they can be used. Which lines show objects…
A: “Since you have posted multiple questions, we will provide the solution only to the first five…
Q: Question 17 Aa .What happens when the following command lines are executed? a = ones(2,3); b =…
A: Question 17 Aa Given, The code snippet: a = ones(2,3); b = zeros(2,1); c = (3:4)'; [r,s,t] =…
Q: Write a program in C++ that allows the user to enter the last names of five candidates in a local…
A: Algorithm: START Create five c-strings to store the names of the candidates Create five integer…
Q: Total latency is equal to a summation of network delay contributors such as frame transmission time,…
A: Introduction: A packet of data's latency is the amount of time it actually takes for it to travel…
Q: Write a complete program for finding a longest common substring:
A: Brute Force implementation for the above problem in R programming. # Function to find the length of…
Q: 1.Have you ever identified a potential problem and proactively implemented a software solution? 2..…
A: A healthcare organization has issues with managing patient data and appointment scheduling. To…
Q: The query's nodes are defined by code. The query graph defines a specific collection of nodes and…
A: The query graph defines a specific network of nodes and their associated properties. In this…
Q: Hello ,Hope You all are Good. The Question is Related to Amazon Web services ( AWS). It's My First…
A: The answer is given in the below step
Q: Question: The Caesar cipher is a type of substitution cipher in which each alphabet in the plaintext…
A: Algorithm : 1. Start2. Declare variables for storing the key and message3. Ask the user to enter the…
Q: Backtrack Search Using First in Orbit Algorithm 1 Input: a group G with a basis B=[I, 2..... k] and…
A: The backtrack search using First in Orbit Algorithm 1 is a procedure for finding a strong generating…
Q: Write a shell script to display arguments to script. Enter any three input arguments to script and…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: You are going to implement a program that creates an unsorted list by using a linked list…
A: You are going to implement a program that creates an unsorted list by using a linked list…
Q: Based on the following specifications, construct the HTML code to generate the form design as shown…
A: please find the html code below
Q: . Multicore CPUs facilitate multithreading. What ismultithreading?
A: Cpu allows multi tasking means two or more persons working on the same program is known as multi…
Please refer to the following step for the complete solution to the problem above.
Step by step
Solved in 2 steps

- Your team represents the ERP Design and Development Project for a XYZ hospital. Your company's senior management has requested that you prepare a risk management plan that identifies potential risks and identifies risk management strategies. From the course content and readings, you know that the overall purpose of risk planning is to anticipate possible risk events and be ready to take appropriate action when risk events occur, to eliminate or reduce negative impacts on the project. Following features must be addressed in your risk management strategy:• Realistic Assumptions based on the scenario• Risk identification (Risk item checklist)• Risk projection (developing a risk table and Assessing risk impact)• Risk Mitigation and Monitoring planSelect one HIM function (e.g., coding, release of information, chart completion, transcription, filing/chart retrieval, document imaging, etc.). For this function, identify and describe one risk associated with this function. Elaborate on how each risk management principle could be applied to your identified risk: Risk assessment Risk mitigation Risk transference Risk avoidance Risk acceptance Describe your chosen risk in a sentence or two. Then provide one substantial and descriptive paragraph for each principle.Use the online version of OWASP Risk Rating. Make up a scenario or use one from a recent news story. Take a particular threat and walk through the risk rating calculator. Explain your scenario, the final score, and what you learned on one page. You will have to use your imagination to fill in the unknown data. Be creative.
- You have been tasked to measure the likelihood of different identified risksusing the FAIR approach. Based on your experience, you have chosen to focuson the Loss Event Frequency (LEF) factor.Defend your decision by discussing the four fundamental factors related to LEF.Hello I need help with this discussion for my Risk Management class. Risk assessment is an inexact science. One of the key factors in evaluating risk and developing a risk mitigation strategy is the tolerance for risk, which can be inexact as well. Read the following ARTICLE (Links to an external site.) and discuss the following questions: 1. What are some of the key factors in determining risk tolerance as it relates to information security? 2. How do you determine IS risk tolerance within an organization? 3. Based on your experience, do you consider your organization (current or prior) to be risk tolerant or risk averse when it comes to information security?For your client, a regional distribution center for an auto parts manufacturer, please explain the differences between a qualitative and quantitative approach to risk assessment. Be sure to discuss, why a schema is important and how it will be defined and used in the assessment you are discussing.
- Effective metrics are the most obvious technique to ensure policy compliance. Metrics can be used to demonstrate how well compliance is performing. You have a measure on how many people have read, acknowledged, and accepted a policy if you create a rule to determine if it has been read, acknowledged, and accepted by signature. The number of employees who have accessed the system would be a statistic if the policy is based on system access. Please respond to the following question(s): Exactly what sort metrics related to knowledge testing following cybersecurity would be useful? The metrics could be collected right after training or at regular intervals over a period of months.a) Tim is an accountant working in a listed company A. He has secretly adjusted the profit and lossstatement so that the company appears to be doing well in business. Investors started to question thecompany’s actual performance. The internal auditors eventually found out that Tim is the one whomanipulated the fraud.(i) Suggest and briefly describe ONE (1) potential action that Company A could initiate a lawsuitagainst the fraud.(ii) Analyze FOUR (4) possible perspectives that could explain the details of action proposed inQuestion 2 a) (i) above. Your answers could base on the point of view of the company’s businessperformance, the perspective of investors or the board of directors and so on.b) The case of Daubert v. Merrell Dow Pharmaceuticals establishes an important precedent in the USjudicial system.(i) Discuss the significance of the case on producing scientific knowledge in court.(ii) Propose any possible steps where the forensics investigators could take in view of the…A recommended approach is that the people assigned to implement a risk management program should begin by studying the models presented earlier in this chapter and identifying what each offers to the envisioned process. Once the organization understands what each risk management model offers, it can adapt one that is a good fit for the specific needs at hand. Which risk control strategy would you consider the most effective and why? When should the strategy be used and why should it not be used for all risks?
- Which of the following are stages of risk-based analysis Select one: a. Risk identification, analysis and classification, decompisition and reduction assessment are not the complete stages b. Risk identification, analysis and classification, decompisition and reduction assessment c. Risk decompisition and reduction assessment d. Risk identification, analysis and classificationFor the scenario below, analyze it by completing the following two phases. There are several examples of how to analyze a scenario in the text book starting on page 474. Brainstorming phase List all the people and organizations affected. (They are the stakeholders.) List risks, issues, problems, and consequences. List benefits and identify who gets each benefit. In cases where there is not a simple yes or no decision, but rather one has to choose some action, list possible actions. Analysis phase Identify responsibilities of the decision maker. (Consider responsibilities of both general ethics and professional ethics.) Identify rights of stakeholders. (It might be helpful to clarify whether they are negative or positive rights, in the sense of Section 1.4.2.) Consider the impact of each potential action on the stakeholders. Analyze consequences, risks, benefits, harms, and costs for each action considered. Find sections of the SE Code or the ACM Code that apply. Consider the…Asset valuation is the process of determining the fair market value of an asset, which is one of the first priorities of risk management. The asset value can be determined from the asset replacement value (how much does it cost to replace it) or what the asset provides to the organization (how much dollar value does the organization get from having the asset). The value can also be determined using a combination of both values. Are personnel assets (employees, vendors, etc) or data assets (business information, databases, financial records, etc) more difficult to quantify? Why?



