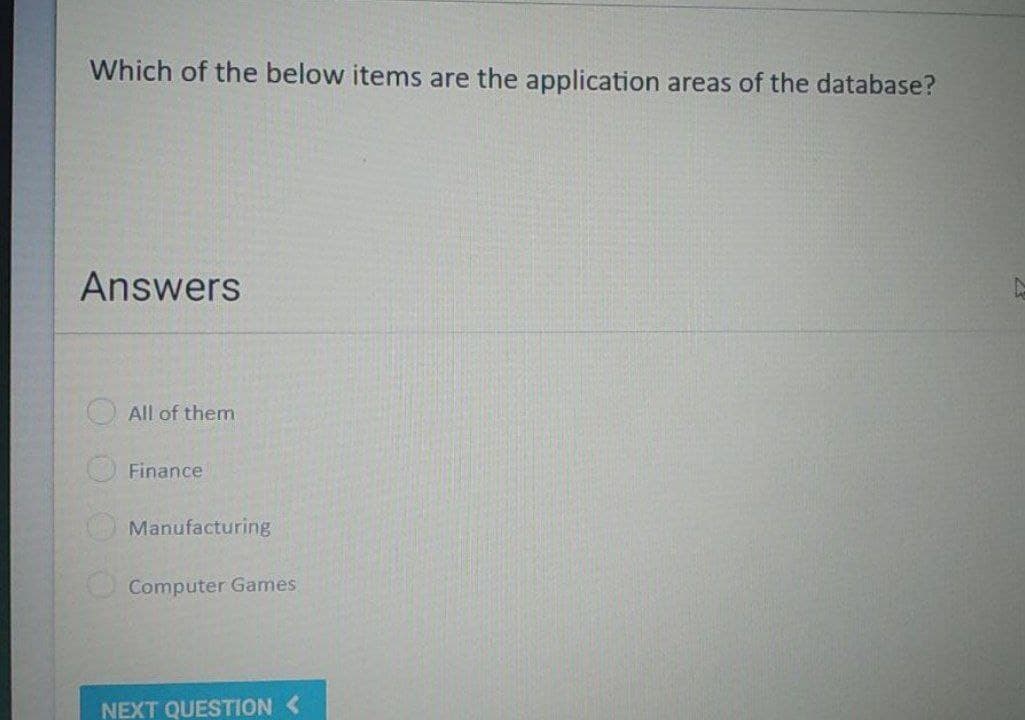
Which of the below items are the application areas of the database? Answers All of them Finance Manufacturing Computer Games 00
Q: History of information systems should be discussed, focusing on the key players and events that…
A: Discuss the history of information systems(IT), focusing on the key figures and events that paved…
Q: The fundamental goal of businesses that make computers is to fulfill the requirements of customers…
A: Launch: It is vital to develop a system that is of a good quality and has adequate processing power…
Q: s that, i
A: A programming language is any set of rules that converts strings, or graphical program components on…
Q: Explain why the internet is the most advanced kind of information and communications technology. Do…
A: Start: To begin, the internet is the most powerful tool that has been made accessible in the…
Q: Why is it that many consider the internet to be one of the most remarkable examples of information…
A: Introduction ICT is an acronym for - "information and communications technology," and it refers to…
Q: When it comes to storing data on the cloud, what are the many uses, business models, advantages, and…
A: Start: The storing and access of data and computer resources through the Internet is referred to as…
Q: You should put some thought into taking a class in a computer programming language during the next…
A: Answer: Languages for ProgrammingA programming language is a form of computer language that…
Q: Would you be interested in expanding your knowledge not only of the cloud and other vital topics,…
A: Instagram, Facebook, and Tumblr: Instagram, Facebook, and Tumblr are just a few examples of social…
Q: nges that information systems face using tech
A: Introduction: Below Investigate the challenges that information systems face using technology and…
Q: Access and Authentication in Information Security
A: Introduction of Access and Authentication in Information Security.
Q: a python program for the following pattern using while loop [code & output screenshots are…
A:
Q: The Internet of Things was first developed as a means of connecting various devices; however, what…
A: Launch: The term "Internet of Things" (IoT) refers to physical objects (or groups of such objects)…
Q: Explain why the cost-performance ratio of information technology is projected to improve by a factor…
A: Encryption: In economics and engineering, price–performance ratio refers to a product's performance…
Q: What are some of the current applications that people are discovering for the internet of things in…
A: Introduction The Internet of things (IoT) portrays actual items (or gatherings of such articles)…
Q: What exactly does it imply when people talk about "computer programming"? What kinds of things need…
A: The above question is solved in step 2 :-
Q: What exactly does the term "interdependence" signify in connection to system ideas, and how does it…
A: Interdependence: Interdependence is a feature of the international system. Regardless of the…
Q: Consider three intensive processe requires 10,20 and 30 units of tim times 0,2 and 6 respectively.…
A: Introduction: Scheduling algorithms efficiently and effectively schedule processes on the processor.…
Q: How exactly may CPU Scheduling help to make a difference in the overall performance of an operating…
A: The central processing unit (CPU) is the component of a computer that processes instructions. The…
Q: Assess the effectiveness of the different security measures in addressing the various security…
A: Answer:
Q: Could you please explain the four P's of good software project management and provide some relevant…
A: The four P's are essential for successful software project management: People Product \spruces…
Q: Is it feasible for cloud computing to resolve all of the issues that an organization has with its…
A: Cloud computing: Cloud computing refers to the sharing of computing resources rather than the use of…
Q: If the marks obtained by a student in five different subjects are input through the keyboard, find…
A: #include<stdio.h>int main(){ float sub1,sub2,sub3,sub4,sub5; float total,…
Q: Question 4a: Construct a DFA which accepts all strings over A = {a, b, c, d, e, f, g} which have…
A: L = {aa, ab, ba, bb} Number of states: n+2 Where n is |w|=n def checkStateA(n): if(len(n)==1):…
Q: Take a look at these five moral considerations for computer systems.
A: The five moral aspects of information systems are as follows: 1. Informational rights and…
Q: How does logic apply to the process of computer programming? What kinds of things need to be taken…
A: Introduction: A programming language is a set of rules for converting text to machine code or…
Q: 1-Write a C++ program ,where you define a structure called student which contains the following…
A: The code implementation is given in the below steps. The algorithm: The structure student is…
Q: The Cost Benefit Analysis, often known as CBA, is a method of doing an economic evaluation that…
A: Given: A cost benefit analysis, often known as a CBA, is a method of economic evaluation and…
Q: Do you believe that the actual production of the program itself is the most crucial stage of the…
A: Software development : The process through which programmers create computer programmes is known as…
Q: O(N) is the order of growth execution time of the remove operation when using the…
A: This is correct O(N) is the correct answer
Q: Where did the idea for the internet of things come from, and what are some of its applications?
A: Encryption: The Internet of Items (IoT) is a network of physical things that are combined with…
Q: array1]-(1, 2, 3, 4, 5); array2]- (3, 5, 2, 10, 16, 1, 10, 15); Write a code to display the…
A: Given :
Q: Choose any data sets you want. Perform descriptive
A: Data sets: -Demographic data -Economic data -Cities -States -Zip codes Description: This…
Q: Write a MATLAB program to enter string in lowercase and converting it to uppercase
A: newStr = upper(str) All lowercase characters in str are converted to uppercase characters, while all…
Q: We have a circuit that counts from 1 to 14. This circuit output (1,2,4,6,7) will light up red, when…
A: int pin1=11; int pin2=10; int pin3=9; int pin4=8; int timr=1000; int i=0; void setup() {…
Q: Explain why the programs that are designed specifically for a client are not the only kind of…
A: Professional software must adhere to particular industry standards to ensure being used and…
Q: Computer Science write a complete C++ code for Cricket tournament scheduling aspect of the…
A: Please find the answer below :
Q: What are the challenges that come with having a software product line that has a scope that is not…
A: Software product: Software product-line engineering is a proven way to build vast portfolios of…
Q: Need to use Ocaml. Not Javascript and python.
A: Answer is given below-
Q: Is there a special use for authentication? Which authentication techniques have the most benefits…
A: Let's see the solution in the next steps
Q: Is it feasible to include cloud computing into the workings of an organization without significantly…
A: Introduction: Cloud computing is a kind of computing that uses . It is a service paradigm that…
Q: In regard to one of the eight principles described in the ACM/IEEE Code of Ethics, could you please…
A: In light of the ACM/IEEE code of ethics, what does the term "product" refer to? Product is intended…
Q: Talk about the many different versions of Microsoft Windows that are available, as well as the…
A: Given: Microsoft Disk Operating System (MS-DOS) (1981) Microsoft designed MS-DOS for IBM-compatible…
Q: Explain the importance of "cybersecurity" and what it entails.
A: Cyber-security is a security mechanism that secures computers, servers, mobile devices, electronic…
Q: In a town, the percentage of men is 52. The percentage of total literacy is 48. If total percentage…
A:
Q: If the marks obtained by a student in five different subjects are input through the keyboard, find…
A: Code in step 2
Q: What is preemptive scheduling? Compare this to Cooperative scheduling.
A:
Q: What are the most recent advances in the technological capabilities of information technology,…
A: Given: Infrastructure refers to the facilities and services that a corporation need. Electricity,…
Q: Which of the following is most likely to be dropped when a line comes to a conclusion? Why was it…
A: Given: The aorta, a huge and thick-walled artery, is the initial portion of the systemic…
Q: Please discuss the many different types of design models that we make use of at this stage of the…
A: Software development: Software development include the creation, design, implementation, and…
Q: What characteristics of other academic fields are analogous to computer science, and what sets it…
A: Launch: Computer science is the study of computers and algorithmic processes, including their…
Step by step
Solved in 2 steps

- I WANT THIS PROGRAM IN JAVA LANGUAGE OOP KINDLY USE GUI eShop Create/View/Edit ProfileAdmin account for notifications/viewable informationview itemscontact seller (chatbox)add to cartview cartcheckoutmake paymentsview purchase historyview product viewing historyreminder to checkoutGroup Members Click for more optionsI want to make REST API using Android studio (java language) which can connect with Neo4j database. I want to implement MATCH cypher query in textbox and wants its json response as output (want to generate RestfulAPI). If someone give a solution with explanation it will be great help for me to understand things easily. I will be very thankful to you.Please do not give solution in image format thanku Giveexplanation short point to point and short code for each topic!!!! what is laravel? What is migration in laravel? What is validation in laravel? what is controller in laravel? what view in laravel? commands in laravel? directory structure? MCV?
- Which data source provides audibility for event investigation as well as documentation.A. Object storageB. Block storageC. Database logsD. Database rowsquestion Create a test case for a web application that enables clients to access material seamlessly from local storage. Test Case ID:Test Case Description:Test Steps:Test Data:Expected Results:Actual Results:Pass/ Fail:Which of the following is NOT one of the places where due diligence might actually happen? A. Virtual data room B. In a public place with a lot of fanfare C. Offsite team room D. On sit
- Which of the following is not a part of the standard office suite?A) Word ProcessorB) DatabaseC) Image EditorD) File Manager. Which of the following statements is correct? a. On an Excel workbook, the active worksheet can be identified by a solid border around the worksheet. b. For example, $B6 is a relative reference where the column is relative and the row is absolute. c. All the answers are correct. d. A worksheet of Excel allows several related workbooks to be contained in one file for easy access. e. In a mixed reference only the column or row remains constant, not both.Which component of the web consists of pages that can reach out to the strongly connected component (SCC) by following the links, but they are not reachable from the SCC. a. a) In-component b. Out-component c. In-between-component d. Within-component Which of the following is not part of a standard SQL statement? a. Importable programming libraries b. Predicate c. Expressions d. Clauses
- Which of the following are common interfaces for integrating SaaS applications? Question 8 options: a.CORBA stub b.REST API c.Java RMI a) and b) b) and c)Any change to Windows or an installed application results in a change to this special database. a. Microsoft SQL Server b. Microsoft Excel c. ntuser.dat d. Registry e. DefaultSuppose that we have access to the world database, on the server something.com with username "Jim123" and password is K@$t0r1@.We need to create in any programming language, an application that will be connected to the above database and will perform the following actions.The user, that is you, will choose from an appropriate menu like the one shown in the picture.1. Connect to the system of the database.2. Display of data3. Data entry4. Update data5. Start transaction6. Exit the System.In the meantime you will have created appropriate triggers that will inform appropriate table for the actions that have been taken. The names of the triggers will be formed with the name that you as a user have followed from thetrN with N (1,2,3,...), example jsinatkas_tr4. Also in the transaction process you will make sure to lock, if needed the the table or tables in which you are going to enter or update data them. This lock will last as long as it is necessary to complete your action. This will be…

