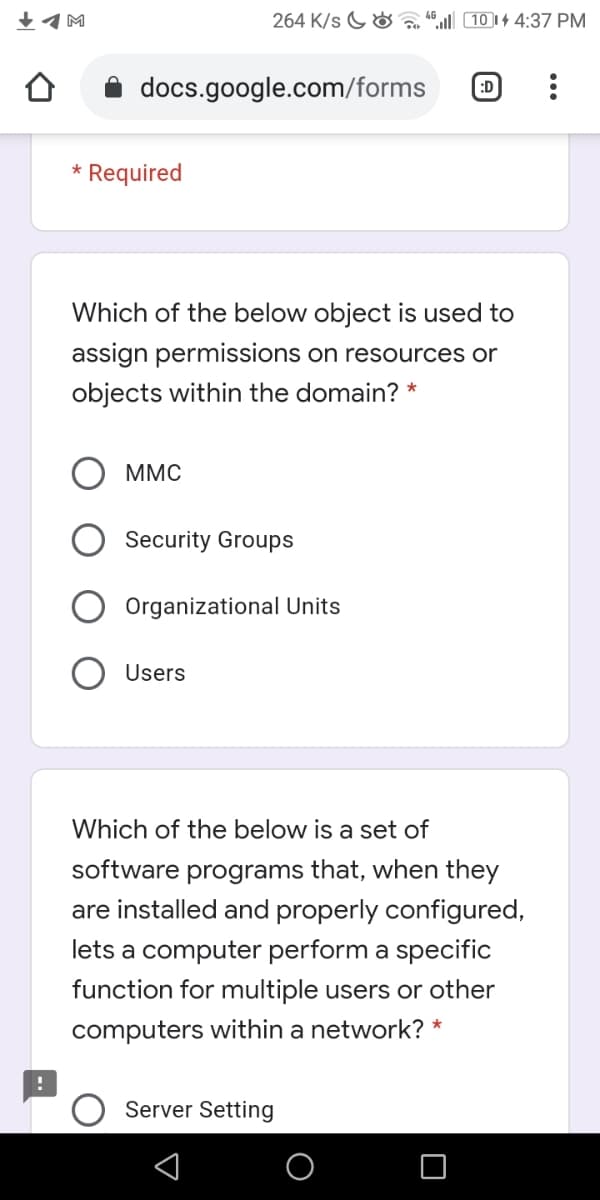
Which of the below object is used to assign permissions on resources or objects within the domain? * MMC Security Groups Organizational Units Users оОО О
Q: A company requires users to scan their fingerprint to access an application. The developers of the…
A: Introduction of Multifactor Authentication: It requires two or more verification factors to access…
Q: Which of the following is not found on the status pop-up?a. Accessibilityb. Network connectionc.…
A: Ans-: option(c)-Shelf
Q: JONS lo zisunabeD ort sueas o basmnoo on 1. What is the purpose of a digital certificate? a. To…
A: 1. In Question 1 Option,, (d) is correct An digital signature, otherwise called a public key…
Q: If a domain user is prohibited from accessing the control panel, where can the user to view the…
A: If a domain user is prohibited from accessing the control panel, where can the user to view the…
Q: New rules 1. Add two new rules to the local.rules file in the /etc/snort/rules directory. 2. Create…
A: Given: Please do this is in SEEDUbuntu and provide screen shots! Only 2 rules(NOT 4) for alert need…
Q: users user_id action date start 1-1-20 1 cancel 1-2-20 1-3-20 publish 1-4-20 1-5-20 start start…
A: Task set : Create table users with three attributes: user_id, action, date Fill the data in the…
Q: 5) _______________ After an ACL is creatred , a unique number is specified for the ACL. Answer:…
A: Note: I would provide answer for first question only. If you want answers for other questions,…
Q: Which of the following is created on the AD FS server that acts as the claims provider in an AD FS…
A: Federation trust: can be created to bypass requests for secondary credentials so that organizations…
Q: Type the name of the default authorized user password file used in Apache Web Server
A: Please follow the steps below:
Q: Which authentication method requires the computer to be joined to either a domain or Azure AD? a.…
A: Pass-through Authentication in Azure Active Directory (Azure AD) allows your users to sign in to…
Q: Q. Create an interface as shown below. Name Yuvan Gender Male Female Password Date of Bi... 12 / 12/…
A: import javafx.application.Application;import javafx.event.ActionEvent;import…
Q: CUSTOMER UI Pending Errands Active Errands Create new Errand Errand Descristion Address: Usemame…
A: 1.Download and install the free NetBeans IDE for your application at Netbeans.org (Link to…
Q: Which of the following commands can be used to change a password for a user account? (refer to the…
A: To change a password for a user account, “ALTER USER” command is used. The example for “ALTER USER”…
Q: Which of the following tabs in the properties window of a user account can be used to add the user…
A: Adding user account to a group means within a group of user one more user have access rights which…
Q: Which shortcut command is used to open a new document? O a. Control N O b. Alt N O c. Alt O Od.…
A: Answer is option A
Q: Create the Following OU and 3 Users based on the given below: (Provide the required Screenshots…
A: Accounts OU Each unit that joins Active Directory will have an Accounts OU. Using this OU is…
Q: Q12- Choose the correct values for the sequence numbers A,B,C and the Acknowledgment number D shown…
A: Answer: I have given answer in the brief explanation
Q: PLEASE HELP ME ASAP IN WEB PROGRAMMING QUESTION Set up a client session in server.js file using…
A: client-sessions is connect middleware that implements sessions in encrypted tamper-free cookies. For…
Q: Which security zone is relevant only if the computer is joined to a domain?
A: Computational domain is the simplified and easy form of the domain in physical form, which is…
Q: What two keys do you need to configure the AWS CLI? Choose two. a) Public Key b) Private Key c)…
A: While configuring the AWS CLI, we need to have both access key and secrte key. Access key is…
Q: Which of the following can be used to change the role that’s currently enabled for a user?a. SET…
A: SET ROLE: The “SET ROLE” statement is used to enable and disable roles for the user current session.…
Q: Which is the first step in a key exchange? The browser generates a random value ("pre-master…
A: Answer:
Q: Type the following command and press Enter, to add a user to the system. Type msfadmin for the…
A: Adding users in Linux. Explanation: Sudo useradd screenshot. screenshot of the new user. As you…
Q: A 5-character username for a website login must consist of a letter, three non-zero digits, and…
A: 5 character of username includes Letter, Non-zero digit, Non-zero digit, Non-zero digit, Letter…
Q: Powershell command only! Requirements: Create a new OU “Students” Create 5 new users in…
A:
Q: Which of following is default key size if keysize option is not used while creating the key using…
A: In this answer I will be discussing about the default key size if keysize option is not used while…
Q: Oluseyi receives a link to a free download of a premium application in his email. He clicks the link…
A: - We need to highlight the option which shows the changed MD5 value of the file. - The first…
Q: Q) Which of the following functional component of AAA records what users do and what they access? O…
A: The correct option is Accounting.
Q: Which of the following can be requested by Account Aggregator to the customer O a. Passwords…
A: Which of the following can be requested by Account Aggregator to the customer Passwords PINS…
Q: Observe the image below and choose the best corresponding option. Screen SysRq Lock Insert Home…
A: A keyboard is for putting information including letters, words and numbers into your computer. Press…
Q: 22. Which command can access the user home directory?
A: The home directory can be accessed and returned in a variety of ways. cd, pwd, pwd, mkdir, ls, and…
Q: Once you have created your domain in Windows Server 2012 0r 2016 or 2019, you will want to create…
A: OUs are Active Directory (AD) containers that hold other AD objects. They have three main functions:…
Q: is a tool that helps the attacker to find information about a domain.
A: Explanation: There is an open source security tools which help in auditing systems running which…
Q: Which of the following options can be used to define a default group while creating a new user…
A: Group is used to refer to a set of user accounts on Linux that can have some special permissions.…
Q: You can review the outcome of GitHub Script execution on the Actions tab of the GitHub portal.…
A: - We need to talk about Github actions. - The statement says that we can review the outcome of…
Q: Which of the following can be provided to an AAA system for the identification phase? A. Username В.…
A: Introduction AAA server is a server which provides Authentication, Authorization and Accounting…
Q: certificate
A: public-key infrastructure certificate
Q: Which of the following is not included in a ScreenTip for command? a. Link to a help topic on the…
A: ScreenTip:ScreenTip is a User Interface feature.It is a small popup window appears while the mouse…
Q: ism
A: a. Web applications should implement authentication mechanisms to protect confidential data. b. Web…
Q: What command is equivalent to the man –k keyword command?a. find keywordb. man keywordc. apropos…
A: "Apropos" keyword: Linux comes with many commands and makes it difficult for any user to remember…
Q: The new web administrator’s account (webadmin1) has been set up and a password provided to the user.…
A: command to force the user to change the password upon first login: You can set empty/null password…
Q: Which of the below users group is considered as the weakest group where its members has the minimum…
A: Domain GuestsThis group has no rights or permissions in the domain. It is not added to the local…
Q: Which of the below command is used to check the logged on users on a Server * O quser O net user O…
A: Which of the below command is used to check the logged on users on a Server ? a.) quser b.) net…
Q: Which authentication method requires the computer to be joined to either a domain or Azure AD?
A: Azure AD is a component of Office 365 which helps in managing identities and can be defined as a…
Q: Which of the following statemént is a valid example of an endorsement policy? OutOf('Org1.member',…
A: Endorsement policies are used to instruct a peer on how to decide whether a transaction is properly…
Q: Which one of the following is defined as the ability to ensure that data is accurate and unchanged?…
A: The data availability, Integrity, confidentiality, Authenticity all these are the important…
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Computer Science [ { "firstName": "Abdo ", "lastName": "Saleh", "email": "ab@iii.com", "password": "123455" }, { "firstName": "Ahmed ", "lastName": "Khaled", "email": "ak@iiicom", "password": "33242" } ] I have these users when I create a new I want it add under theses users in json file using KotlinQuestion 14 papa .1. In this problem, you should write a short bash script. The script should list all files that end in .o from the /lib directory on a UNIX system, only if the file name (not including the extension) begins and ends with a vowel. 2. Write a bash command to print out a text representation of all of the pop assembly instructions from an ELF file named runme. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineBash Shell Script Programming Assignment Question 1. Create a shell script file called q1.sh Write a script that would accept the two strings from the console and would display a message stating whether the accepted strings are equal to each other. Question 2. Create a shell script file called q2.sh Write a bash script that takes a list of files in the current directory and copies them as into a sub-directory named mycopies. Question 3. Create a shell script file called q3.sh Write a Bash script that takes the side of a cube as a command line argument and displays the volume of the cube. Question 4. Create a shell script file called q4.sh Write a Bash script that prompts you for a user name and displays the corresponding user’s id number (UID), group id number (GID), and his/her home directory. Note: this information can be found in the /etc/passwd file. Question 5. Create a shell script file called q4.sh Write a bash script that will edit the PATH environment variable…
- Review the following program that extracts the email server domain name. >>> data = 'From stephen.marquard@uct.ac.za Sat Jan 5 09:14:16 2008 ' >>> atpos = data.find('@') >>> print(atpos) 21 >>> sppos = data.find(' ',atpos) >>> print(sppos) 31 >>> host = data[atpos+1 : sppos] >>> print(host) 1. Adapt the program to extract the user name (stephen.marquard) and Copy+Paste the code in the answer2. Run the adapted program and include a full window screenshot with system time and date in the answer.Suppose you want to back up a huge file (e.g., a 10-GB AVI file) to aCD-R. You can achieve it by splitting the file into smaller pieces and backing upthese pieces separately. Write a utility program that splits a large file into smallerones using the following command:java Exercise17_10 SourceFile numberOfPiecesThe command creates the files SourceFile.1, SourceFile.2, . . . , SourceFile.n,where n is numberOfPieces and the output files are about the same size.Simple SHELL (.sh) script Write a SHELL script (minExF.sh) that takes a csv file ("Comma Separated Values", a text file that can be manipulated by Excel) as an argument containing the grades of the mid-term (called intra) exams with the passing thresholds and calculates the minimum grades that must be obtained in the Final exam by adding them as a column to the initial information in the output file. Note: To manipulate large integers and real numbers use the Unix command bc . Here is an example of how to use of this command to add two non-integer numbers stored in the variables VAR1 and VAR2 : VAR1=5.5VAR2=3.14159RESULT='echo $VAR1+$VAR2 | bc'echo $RESULT The result displayed on the screen will be 8.64159. The first line contains titles (mid-terms, weight mid-term, weight final, treshold). The following lines contain information about the Intra (mid-term) exam scores, exam weights and weighting of the exams and the cut-off points for the two exams, Intra (mid-term) and Final.
- 1.)Why is this code not thread safe? 2) What issues could arise if it is not fixed? 3) How you would fix it using what you learned about synchronization? You must write lines of code or fix lines of code that already exist in the file for full credit. mport java.io.ObjectInputStream; import java.io.ObjectOutputStream; import java.io.Serializable; import java.net.ServerSocket; import java.net.Socket; import java.util.ArrayList; import java.util.function.Consumer; import javafx.application.Platform; import javafx.scene.control.ListView; public class Server{ int count = 1; ArrayList clients = new ArrayList(); TheServer server; private Consumer callback; Server(Consumer call){ callback = call; server = new TheServer(); server.start(); } public class TheServer extends Thread{ public void run() { try(ServerSocket mysocket = new ServerSocket(5555);){ System.out.println("Server is waiting for a client!"); while(true) { ClientThread c = new ClientThread(mysocket.accept(), count);…Computer Science in linux An important concept in computer security is the principle of least privilege. Each user must be able to access only the information and resources that are necessary for legitimate purposes and activities. With the “principle of least privilege” in mind, how would you configure your Unix/Linux system to designate a small set of users as printer admins? For example, users steve and bob will need to perform printer administration tasks. This includes running the lpadmin, cupsaccept, cupsreject, cupsenable, cupsdisable, cancel and lprm commands as root. How will you configure the system to allow these printer admins to do their jobs without having any other kind of root user access? Provide the relevant config file entries. (Absolute pathnames required for commands)Question 1 Using Powershell .ps1 A System creates a new user file for a new user every time a new user is registered. A System administrator runs the powershell script named new_user.ps1 and input command line parameters as follows (This is just an example): .\new_user.ps1 "John Doe" "12/19/1981" "Houston TX" "04/15/2019" This information is then stored in a file named John_Dow.usr in this format: Name: John Doe DOB: 12/19/1981 Location: Houston TX Date Joined: 04/15/2019 Full explainthe this question very fast solution sent me step by step Don't ignore any part all part work u Text typing work only not allow paper work
- • Exercise 1: Please create a script that print “Hello, your name.” • Exercise 2: Please create a directory call user_bin, and add it to PATH. Then mv script of Exercise 1 to user_bin. Then run it from your root directory.• Exercise 3: Add a new command call ‘l’ which will perform exact same as ‘ls -a’. • Exercise 4: Create a function call sortFile, which will sort all filenames of current directory.• Exercise 5: Please make your own page using shell script, print following as your page. <html><head><title>My System Information</title></head><body><h1>My System Information</h1></body></html> Exercise 6: Could you add one variable in the example, name the variable as greeting, which displays “Hello, my name is xxx xxx” in the body using variable greeting.• Exercise 7: Could you add one variable in the example, name the variable as FILE_LIST, which displays the filenames of current working directoryQuestion no 02: Write script/command to:- Question Script/Command 1 Let the System know that the following script is a bash script. 2 Make VAR an unchangeable and undeletable Variable. 3 Access 8th Argument passed to the script. 4 Print Process ID of the current script. 5 Sleep the system for 2 seconds 6 Print “I have $200” 7 Print all the elements of an array without using loops. 8 Print filename of the current script. 9 Print the exit status of the previous command 10 Print all environment variableLinux Homework Please show console output 1: Please create a script that prints “Hello, your name.” 2: Please create a directory call it yourname_bin, and add it to PATH. Then move the script “Hello, your name” to yourname_bin. Then run it from your root directory. 3: Add a new command called ‘a’ which will perform exact same as ‘ls -a’. 4: Create a function call it yournamesortFile, which will sort all filenames of current directory. 5: Please make your own page using shell script, print following as your page. <html> <head> <title> YourName System Information </title> </head> <body> <h1>YourNameSystem Information</h1> </body> </html> 6: Add one variable in the example, name the variable as greeting, which displays “Hello, my name is your name” in the body using variable greeting. 7: Add one…











