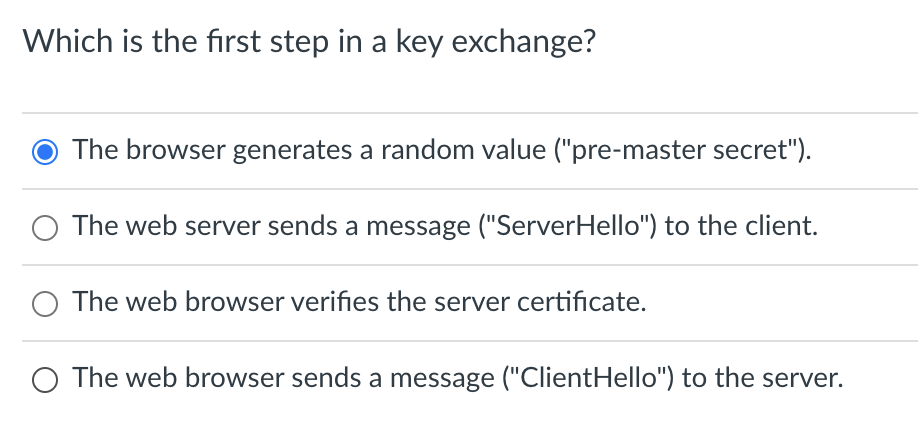
Which is the first step in a key exchange? The browser generates a random value ("pre-master secret"). O The web server sends a message ("ServerHello") to the client. The web browser verifies the server certificate. O The web browser sends a message ("ClientHello") to the server.
Q: It is a name assigned to data storage location. Answer: What keyboard shortcut is used to run a C-la...
A: 1. what is the name assigned to a data storage location. Answer: Primary storage (also known as main...
Q: his is what test developers usually do in order to save time and to use as less resources as possibl...
A: Answer 1) cross-validation because it is also used machine learning to test and train data. get ref...
Q: Using the below figure 1. The private enterprise's subtree below gives the object ID for these Objec...
A: The answer for the above gievn question is given below:
Q: c) In your development, you have 20 errors at the requirement stage, and it is amplified by a factor...
A: No. of errors at different stages are given here , and percentage rectification of the errors are gi...
Q: Computer Science
A: Relative Purchasing Power Parity (RPPP) is an expansion of the traditional purchasing power parity (...
Q: In C++: Define a function that reads input 5 integers from the user, stores them in a vector, and th...
A: Define a C++ function that reads input 5 integers from the user, stores them in a vector, and then r...
Q: Put the verb into the correct form: It takes me an hour to get to work in the morning. ?How long (it...
A: SOLUTION:
Q: C Programming Exercise 2: Write a program to input the values of two integers x,y and print the cube...
A: Write a C program to input the values of two integers x,y and print the cube of the absolute differe...
Q: FOR-LOOP dedicated to cursor management
A: Cursor FOR LOOP StatementThe cursor FOR LOOP statement implicitly declares its loop index as a recor...
Q: Represent the following decimal numbers in binary using 8-bit signed magnitude, one's complement, an...
A: Here in this question we have asked to convert +59 and -59 in sign magnitude,1s complement and 2s c...
Q: Put the verb into the correct form: The film wasn't very good. I it _(enjoy) .much
A: you question is about correct verb from
Q: What are the discrepancies with this database? The student administration database has the same ID ...
A: The above question is used below
Q: 9.1. Show that if G and H are consistent cuts of a distributed computation (E,-), then so are Gu H a...
A: Since G and H are consistent cuts of distributed computation. They are not related to each other or ...
Q: 1.)Which of the following identifier/variable name is considered as invalid? Select one: a. none of...
A: 1) rules for constructing variables Alphabets, numbers, and underscores can all be used in a varia...
Q: Put the verb into the correct form: (you / listen) to the radio? ''No, you can turn it off
A: The best suited answer for this is: Are you listening to the radio ? No, you can...
Q: HW 3 (due 2/15) draw the graph below with 2 self-intersections
A: Solution: If a feature intersect itself at a point and continue by crossing itself, it is consider...
Q: Which application layer protocol allows users on one network to reliably transfer files to and from ...
A: Please find the correct answer and explanation in the following steps.
Q: Can we specify a variable filed width in a scanf() format string? A. Yes B. No
A: yes
Q: An array A [-10:10] has a base as 400 and its word size is 4 bytes, Calculate the addresses of the l...
A: Ans: Base address(B) = 400 LB= -10 W = 4 I = -3 Address of A[-3] = B + W * (I - LB) = 400 + 4 * (-3 ...
Q: What is a sign bit and where can you find one
A: Step 1 The answer is given in the below step.
Q: For stopped irreversible expansion of 1.0 mole of ideal monatomic gas in an adiabatic frictionless p...
A:
Q: rated values) text files? What is an easy com
A: CSV (comma-separated values) text files
Q: 1.In what year does the C-language was implemented? Select one: a. 1971 b. 1970 c. 1972 d. none of ...
A:
Q: 6. Given an random number generator rand5() that generates a uniform random integer in the range [1,...
A: By the given question we have rand5() function, which generates the random number between the 1 to 5...
Q: Describe what a data model is and why it's important in database design.
A: Answer :-
Q: Consider the Relation R4 = (A,C,B,D,E,F), with Functional Dependencies: A -> B, C -> D, E -> D. What...
A:
Q: Complete the sentences. Use a superlative (-est or most ..) + a preposition (of or in).lt's a very g...
A: the best room in
Q: 1- Given R0, RI, R2, and R3 followed by the indicated base; i- Convert each value into its correspon...
A:
Q: Suppose that a flaw in a certain computer chip installed in computers was discovered that could resu...
A: Suppose that a flaw in a certain computer chip installed in computers was discovered that could resu...
Q: ix) Define a function named arrayCount that takes an array and a number as the parameters and the fu...
A: Define a function named arrayCount in Python that takes an array and a number as the parameters and ...
Q: The C Preprocessor: The preprocessor provides facilities for including source code from other files ...
A: I will explain in detail about C preprocessor which is symbolized by using "#" : 1. The "#" preproce...
Q: _init__(self, items: list) -> None: self._first = None for item in items: self.append(ite
A: “ArrayList” is a part of the collection framework and is present in “java.util” package. It provides...
Q: Put the verb into the correct form: Where (Maria / come) from? Is she ?Spanish
A: Come is the correct verb
Q: Create a flowchart that will increase the value of the number by 5 if its greater than 10 and displa...
A: Flowchart is a type of design that represent the steps, procedure or workflow of programming logic. ...
Q: Suppose we are given an array of numbers A[0], A[2], . . . , A[n - 1]. You may assume that n is a mu...
A: The answer is given below:-
Q: Why do you think gadgets in a networked environment might need to be uniquely identified?
A: For the most part, software and user data files are saved on a central computer, known as a file ser...
Q: In Python Language do the following: The Springfork Amateur Golf Club has a tournament every weeken...
A: Python Language do the following:The Springfork Amateur Golf Club has a tournament every weekend. Th...
Q: Please write C++ functions, class and methods to answer the following questions. 1. Define a new C+...
A: Part(a) Explanation: Create a class named Exam. Declare its data members as student_id and score. I...
Q: Write a MIPS assembly program that can draw a rectangle pattern onto the console output based on a g...
A: Task : Given the height, width, border and fill character. Create the rectangle plot.
Q: Why is it advantageous that, in a system with cooperative multithreading, two threads communicate w...
A: Answer: The ability to run many pieces of a programme simultaneously is made possible by multithread...
Q: A city is planning for a road widening. They want to begin at Session Road, go down each street only...
A: Given: A city is planning for a road widening. They want to begin at Session Road, go down each stre...
Q: Create a function print_double_spaced(cs) that takes a C string as an argument and prints the charac...
A: Answer :
Q: Make a list of six different access technologies. Each one should be classified as either residentia...
A: Introduction: Six ways to get in: It's a modem: 56kbps is the maximum transfer rate. Fiber-coaxial h...
Q: Explore and Expand: Using the link/QR code reader/scanner provided, study the Basic Formula guides (...
A: “Since you have asked multiple questions, we will solve the first question for you. If you...
Q: (25 min) The following table shows the foreign exchange rates for a few currencies. Foreign Currency...
A: Step 1 : Start Step 2 : Print the Currency Exchange Rate Table. Step 3 : Take user input of the Curr...
Q: Paragraph Completion: Switzerland is only a small country but has rich natural endowments, especiall...
A: ANS:- Option 4:- In the alps the weather is generally cool even in the summer
Q: testability tip and provide an overview of the compiler.
A: Testability refers to the ability to run an experiment to test a hypothesis or theory. ... Testabili...
Q: Put in alan or the. It's not easy to get job at the moment
A: Answer is a
Q: neurons will increase in value, at the same rate. neurons will increase in value, but at different r...
A: Option 2 is correct.
Q: Computer Science Question
A: PLease post a question properly'
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Which of the following are contained in a public-key infrastructure certificate? Check all that apply. (a)Group of answer choices (b)Owner's secret key (c)Owner's public key (d)Owner's name (e)A signature from the owner (f)Issuer's secret key (g)Issuer's public key (h)Issuer's name (i)A signature from the issuerWrite a PHP script that could be used to connect to MYSQL database named gctudb running on a web server with IP address "192.168.10.100". Assume the user name is nuksoft and the password is makadcode. Remember to close your connection explicitly.What is the output of the following command? Get-DnsServerTrustAnchor –name secure.practicelabs.com –computername PLABDC01 Updates the trust points created earlier on the PLABDC01 Creates a new trust point on the PLABDC01 Refreshes the trust point on all DNS servers Creates a new trust point on all DNS servers from PLABDC01
- 5, For the first mode of Message Authentication code (MAC), which description is NOT correct? The key used in this mode is for message encryption. This mode cannot protect message confidentiality. The receiver is able to detect malicious message modification by checking the MAC. The attacker who does not know the key cannot calculate the MAC.Which one of the following statements is NOT correct about HTTP cookies? a. A cookies is a piece of code that has the potential to compromise the security of an Internet user b. A cookie gains entry to the user’s work area through an HTTP header c. A cookie has an expiry date and time d. Cookies can be used to track the browsing pattern of a user at a particular siteWhat type of authentication method is displayed in this picture? Multi-Factor Authentication Biometric Authentication Token-based authentication Single Sign-on 2.Wendy is examining the logs of a web server that was compromised by a remote attacker. She notices that right before the attack, the logs show a series of segmentation fault errors. Other logs indicate that the attacker sent very long input strings to the web server that had malicious commands at the end of the string. What type of attack most likely took place? SQL Injection Cross-site request forgery Cross-Site scripting Buffer Overflow 3.Jessica is combatting a security incident where a specific piece of malware is continually infecting systems on her network. She would like to use application control technology to block this file. What type of application control should she use? Greylisting Bluelisting Whitelisting Blacklisting
- Which of the following parameters are required for the certificate template that will be used for issuing of IKEv2-based VPN server certificate? (choose two). Validity period must be more than two years. Private key must be exportable. Private key must be non-exportable. Must support server authentication.You are configuring a group of VPN servers and want to automate the enrolment of computer certificates to the mentioned server devices. For a certificate to allow auto-enrolment, what will you do first? Create a base certificate revocation lists (CRL) on the CA server. Enable certificate archiving on a computer certificate. Create a customized certificate template. Enable a digital signature on a computer certificate. Create a delta certificate revocation lists (CRL) on the CA server.When does a proxy send an acknowledgement to a response and when does it simply forward the response without sending an acknowledgement?
- Consider the following simple authentication dialogue: C → AS: IDc II Pc II IDv AS → C: Ticket C → V: IDc II Ticket; Ticket = E(Kv, [IDc II ADc II IDv]) Where: C = client AS = authentication server V = server IDc = identifier of user on C IDv = identifier of V Pc = password of user on C ADc = network address of C Kv = secret encryption key shared by AS and V ***Explain the process of this protocol.write a telegram bot code, which will provide Chegg answers including enhanced content. The bot will run on student account cookiesWhich key is used by the sender to have a simple digital signature for message (m) that is wanted to be send ?.\ A sender’s public key B receiver’s private key C receiver’s public key D sender’s private key

