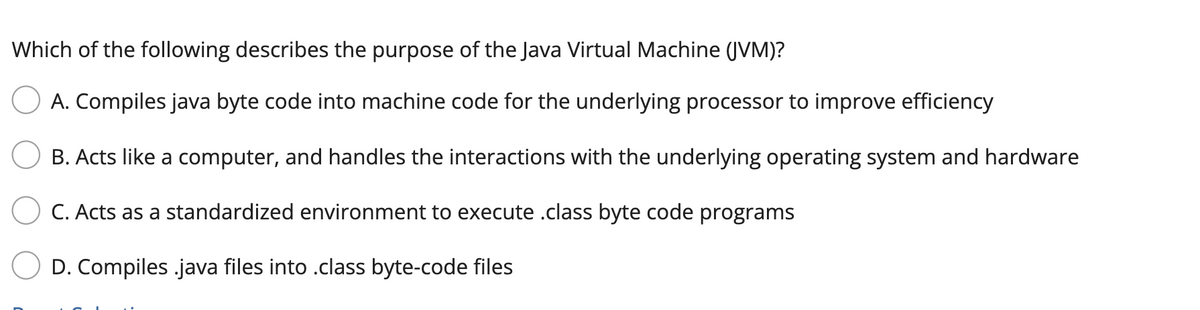
Which of the following describes the purpose of the Java Virtual Machine (JVM)? A. Compiles java byte code into machine code for the underlying processor to improve efficiency B. Acts like a computer, and handles the interactions with the underlying operating system and hardware C. Acts as a standardized environment to execute .class byte code programs D. Compiles.java files into .class byte-code files
Q: Consider the following 4-message protocol: A → S: (B, {(A, K1)}KpbS) S → B: A B → S: (A, {(B,…
A: A protocol is a set of rules or guidelines that dictate the behavior of entities in a communication…
Q: 3.2.2: Read and format integers. Jump to level 1 First, read in an input value for variable…
A: The C++ code is given below with output screenshot
Q: What are some ways that you may protect yourself from falling prey to a phishing scam? To begin,…
A: When someone sends a false communication that looks to be from a reliable source, it is known as a…
Q: Does the word "intrusion prevention system" have a definition?
A: Intrusion means entering into the network or computer system without any access for any malicious…
Q: Throughout this problem, consider the following setting: rng('default') % Set the random number…
A: For this question, I am using MATLAB Code to Plot the graph.
Q: Does the machine shut down in two stages when a customer repeatedly inserts the incorrect ATM pin…
A: No the machine will not shutdown if you enter a Incorrect pin for 2 or more time.
Q: The internet, in addition to internal and external intranet and extranet networks, plays an…
A: Contemporary business: In today's ever-changing world, it is essential for businesses to stay ahead…
Q: Which element is used to create a multiline text entry? A text (B) textarea c) submit (D) radio…
A: The textarea <textarea> is an HTML element used to create a multi-line text input control. It…
Q: Who was the first known user of an abacus, and when did this begin to take place?
A: Abacus is a calculating device used by sliding counters along rods or grooves, used to perform…
Q: Determine all truth value assignments, if any, for the primitive statements p,q,r,s,t that make the…
A: To determine the assignment of truth values for the primitive statements that make the compound…
Q: To what extent is networking essential to the development of IT?
A: Introduction: Even if you are not actively seeking for job, it may still help you improve…
Q: The following diagram shows the process_state and other_resources fields of 4 processes in the PCB…
A: (1) Process O requests resource 2: Process O moves from the running state to the blocked state and…
Q: Why does the installation of networking technologies provide more or less danger to enterprises…
A: Answer:- Networking is often thought to entail increased risk for information technology-using…
Q: rite and execute C program to simulate C-Look.
A: Here is The C Program to Simulate C-LOOK Disk Scheduling Algorithm With Comments for Better…
Q: At least four (4) of the best practices for internet security should be addressed, along with an…
A: Introduction : Internet security is the process of protecting and preserving data or information…
Q: Construct a truth table for the following compound statement, where p,q, and r denote primitive…
A: truth table for [(p⇒q)∧(q⇒r)]⇒(p⇒r) is :
Q: Consider a two-link network where Host A is connected to the router by Mbps link with 10 ms…
A: Given data: Packet size=1500 bytes Transmission rate = 15Mbps Propogation delay = 10 ms To…
Q: When it comes to multithreading, many computer operating systems (Linux, Windows, Mac, Android,…
A: Operating System:- An operating system is a software program that manages the hardware and software…
Q: Provide a brief description and examples of each of the following methods of clustering:…
A: Partitioning methods: Partitioning methods divide a dataset into a pre-specified number of clusters…
Q: So, how many different kinds of computers are there, exactly?
A: There are 5 different kinds of computers , based on classification they have answered in step2.
Q: What role does Moore's law play in the development of technologies such as grid computing, cluster…
A: 1) Moore's Law states that the number of transistors on a microchip doubles every two years. It…
Q: If num_difference is equal to -15, execute total_difference = -25. Else, execute total_difference =…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT…
Q: When it comes to wireless networks, what is the highest degree of encryption that may be used?
A: Answer is
Q: I'm curious as to the pros and cons of service-oriented computing technology.
A: Simply put, cloud computing is the provision of computing services such as servers, storage,…
Q: please answer with proper explanation and step by step solution. Question: (Python) Evaluate the…
A: Introduction The operator precedence is a set of rules that determine how operators are evaluated in…
Q: Web servers are attractive targets for attackers because it is so simple to access them. An in-depth…
A: Introduction: Website material is stored and delivered via web servers. Web servers, which are…
Q: Is there anything that can be done to extend the life of a dot matrix printer?
A: We need to be aware of the methods for extending the life of a dot matrix printer. We can prolong…
Q: Which of the following is a legal Form Text property value? a. none of these
A: Which of the following is a legal Form Text property value? a. none of these b. either of these…
Q: We look at how the internet has changed the way business is done today. In the current business…
A: Business paradigm: A business paradigm is a concept that describes the way businesses work, with a…
Q: Using the mov.w instruction we copy the 16-bit word 0xB612 to the address 0x1C20. You do not need to…
A: Microprocessor:- A microprocessor is composed of several components, including an arithmetic logic…
Q: Create a mask to read the 9th LSB of a 16 bit binary number. int a = rand()%; unsigned int mask mask…
A: NOTE: The hint for Question 7 is missing. Given, int a=rand()%; unsigned int mask=_______;…
Q: I am planning to install a data cable between two office labs that are 80 meters apart. Can you…
A: Introduction : Copper twisted pair cable is a type of cabling that consists of two insulated copper…
Q: Numerous parts make up a computer.
A: Numerous parts that make up a computer and which makes it work faster ar given below.
Q: The MSP430X family (X stands for eXtended) can handle a larger amount of memory since it has a…
A: The MSP430X family of processors is a group of microcontrollers manufactured by Texas Instruments.…
Q: Write and execute C program to simulate Segmentation
A: Algorithm: Resultant algorithm to simulate segmentation is: Start Declare and initialise the…
Q: As a direct consequence of this, web servers are a common target for cybercriminals. Discuss in…
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Walk me through the steps involved in the construction of a Physical database.
A: A physical database is a collection of data that is stored in a specific structure on a computer's…
Q: How can a company take use of the Internet to create a virtual corporation or become a more nimble…
A: Information technology: Information technology (IT) is the practice of storing, retrieving,…
Q: What instances of organizations employing databases in your information systems can you think of?
A: A database is a grouping of connected data. For any organisation, it is crucial. Businesses may…
Q: Knowing how to use and recognize a computer's parts is an essential skill.
A: A computer is a programmable electrical device that receives unprocessed data as input and uses a…
Q: Total latency is equal to a summation of network delay contributors such as frame transmission time,…
A: Introduction: A packet of data's latency is the amount of time it actually takes for it to travel…
Q: Among these three features, which one sets TCP apart from UDP?
A: Introduction: TCP differs from UDP in these three areas: Explanation: TCP (Transmission Control…
Q: Are there any downsides to using the web for international business?
A: Internet improves global business: Internet business has several advantages. By making it more…
Q: A Costume shop requests a Computer application that advertizes Costume rentals. This week's Costume…
A: To create the costume rental application in Visual Basic, follow these steps: Open Visual Studio…
Q: It is essential to have a clear understanding of the difference between a vulnerability screening…
A: Vulnerability Scanning: Vulnerability scanning identifies known vulnerabilities in the system or…
Q: in python
A: We need to solve the given problem in python.
Q: In Python, write a code to create a choropleth map showing the unemployment rate within a selected…
A: Dataset in Python which usually refers to the one it is mostly used for manipulation of Gifs and…
Q: What kind of link is created between the different functional units by ERP?
A: 1. A Database Management system (or DBMS). 2. It is essentially nothing more than a computer-based…
Q: The hardware is the physical components of a computer
A: Hardware comprises of tangible things that we can touch and feel, as opposed to software, which we…
Q: Given a set of jobs {J1, ... , Jn}, each job Ji = has a required processing time ti and a weight…
A: A common approach to solve this problem is to use a greedy algorithm. The idea is to sort the jobs…
Please refer to the following step for the complete solution to the problem above.
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- Containers are very similar to which of the following? Operating Systems Infrastructure as Code Virtual Machines Networks1) Which of the following acts as a bridge of communication between the user wants and the software? a. Registry Program b. Keyboard c. Booting of Computer d. BIOS 2) Which of the following best explains why developing native applications is a bit cost intensive or costly a. Native application are costly to developed since they need to written using web based application and the unfamiliarity of most programmers using this software adds to development cost b.Native application are costly because they are entirely dependent on internet connection hence developers must make sure that it can always have a good internet connection in order to function c. Native application are costly to developed since it needs to be continuously updated and maintained through the website d. Native application are costly to developed since it requires that the application must be suited only to the specific operating system in order to maximize its device…Which of the following is NOT an example of a user interface?the a. command prompt b. operating system c. visual interface d. concurrently b and c
- Create a java project that present the Android intents to switch between Activity classes and pass data. Create two java files for two activities. First Activity: Enter your full name (Evasn) and phone number (123456). Then, click “Ok” to go to the Second Activity. Second Activity: Display Welcoming message with your name (Evasn). Write the java codes for each activity. Take screenshot for outputs. HINT: Include the screenshot of your App, after you run the app, as a part of your answer.Please help me with this using java. If possible please complete third step along with 1) and 2) 1) Create a login/sign up page with a place to type up username and password or to create a username and password(Refer to first image) 2) then create a game menu with two clickable buttons play game and instructions. And include a image ( Refer to Second image) 3) Connect the play button from the game menu to the actual game. So once the user clicks play game it start my trivia game. because my Java trivia code is too long please go to YouTube and search up bro code java trivia game and the code should be in the comments section then connect them together. The program starts if with the login/sign up page. Once user has entered or create username and password l. It then goes to the game menuI am getting this error message: Caused by: java.io.IOException: CreateProcess error=206, The filename or extension is too long.It is coming up during build. Happens when the build process gets to "compileGwt". I have updated my Intellij settings, JDK location, .gradle location is all in C drive. My build and run using: Intellij IDEA. JAVA_HOME is mapped to the C drive as well. The programme is a Java programme. I need help on how to clear this error. Clean has not helped either
- please help dont copy from google I need a sample of code of the below scenario in Java with Spring Boot framework: Create a sign-in and sign-up page for an online book store. Data that need to be stored from the user are: username and password If the user inputs the wrong credential system, display an error. Please use JSPs. and JSTL dependenciesPython. ● For this task, categorise which type of NLP application applies for each ofthe following use-cases:(Use the categories we have discussed on this bootcamp so far)a. A model that allocates which mail folder an email should be sent to(work, friends, promotions, important), like Gmail’s inbox tabs.b. A model that helps decide what grade to award to an essay question.This can be used by a university professor who grades a lot of classesor essay competitions.c. A model that provides assistive technology for doctors to providetheir diagnosis. Remember, doctors ask questions, so the model willuse the patients’ answers to provide probable diagnosis for thedoctor to weigh and make decisions.Create an "Office Supplies Inventory System" using Java Netbeans with the following features: - Login Page as Admin user - Add, View, Update, and Delete features of office supplies information (supply name, description, color, type, etc.). - Records the employee's info every time he/she wants to get an office supplies. (Example: You have 5 rims of bond paper and 1 box of black pen. Juan Dela Cruz wants to get 1 rim of bond paper and 3 pcs of black pen. The Admin User of the system will record his/her full name and the office supplies he/she was requesting. After that process, the 1 rim of bond paper and 3 pcs of the black pen will automatically be deducted from your inventory. - Generating of Report
- السؤال which of the following programs has the role of loading operating system into memory? الاجابات Microsoft word Mozilla bootstrap no one of previousWhich of the following is an example of an Application Programming Interface? a. APIs for operating systems b. All alternatives are accurate c. APIs for websites d. APIs for applicationsTranscribed Image Text Joshua, a systems administrator, is configuring new Windows 10 laptops. He is creating new local users on each laptop. He realizes that two users have the same name, Miguel. He uses the name Miguel for one user. Which of the following is a valid user name that he can create for the second user? a) Miguel? b) Mig c) Miguel d) Miguel2 e) All the above will work!

