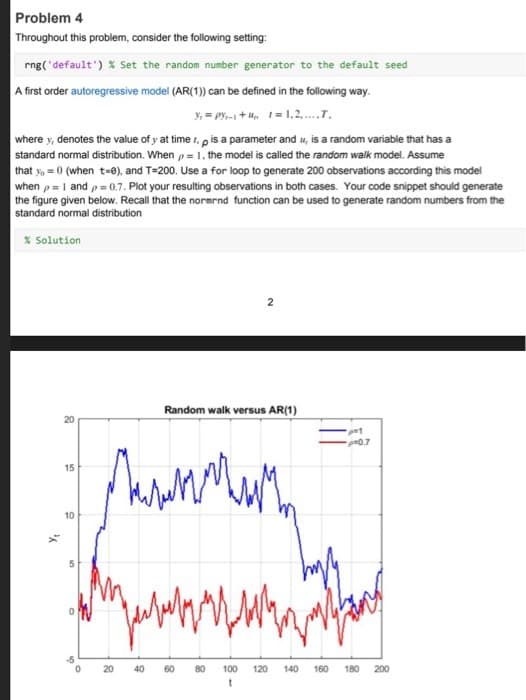
Throughout this problem, consider the following setting: rng('default') % Set the random number generator to the default s A first order autoregressive model (AR(1)) can be defined in the following way. 3₁=PY₁-1+₁=1,2,....T.
Q: Digital Logic Design Assignment Q1. Obtain the simplified Boolean expressions for output F and G in…
A: The above question is solved in step 2 :-
Q: Code a descriptor that has a range of B9DC78H-D3BEF2H. The segment follows the highest priority.…
A: Java is a high-level, class-based, object-oriented programming language that is used to develop…
Q: 1. Which element does not support the autofocus attribute? (A) B) 2. What defines a group of…
A: As per Bartleby's rules we can answer only 3 MCQ questions at a time I request you to post other…
Q: What are the three ways in which TCP stands apart from UDP?
A: Introduction: A network conversation that allows programs to exchange data is defined by the…
Q: Objectives Java refresher (including file I/O) Use recursion Description For this project, you get…
A: Note: As per the guideline I can only provide the solution of the 1 question in case of multiple…
Q: Give the initial state, goal test, successor function, and cost function to transform the following…
A: Problem formulation defines the scope of the problem, formulating one or more specific questions…
Q: This program prompts a person for income and expense amounts, then calculates their net monthly…
A: Introduction Java class: Class is a blueprint or template used to create objects in Java. It defines…
Q: 2. Consider the following function that counts the number of words in a string: void words (char…
A: The algorithm of the code is given below:- 1. Prompt the user to enter a string of up to 100…
Q: Write a shell script to display arguments to script. Enter any three input arguments to script and…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: Can you please separate 2 and 3. As this quite confusing which explanation is for 2nd part and which…
A: In this question we have to explain each point differently according to the solution. Hope this…
Q: that takes the her ear linked list as an Complete the following hasCycle fur input and as output to…
A: The source code of the python program def hasCycle(head): mp = set() while head is not…
Q: Use a vector to read 10 integer numbers, each of which is between 1 and 50. Begin with an empty…
A: This code is a C++ program that reads 10 integer numbers from the user and stores only the unique…
Q: A multiprocessor with eight processors has 20 attached tape drives. There is a large number of jobs…
A: The solution is given in the below step
Q: Proposition Prove that LRU and FWF are marking algorithm.
A: Marking algorithm is an algorithm which doesn't removes a marked page from the cache. LRU stands for…
Q: Given a matrix of size N x M where N is the number of rows and M is the number of columns, write an…
A: One possible solution to this problem is to use a modified version of Dijkstra's algorithm, a…
Q: What roles does the MAC sublayer have?
A: Introduction : The Media Access Control (MAC) sublayer is a sublayer of the Data Link Layer of the…
Q: Write a Python graphics program, using graphics.py from Chapter 4 of our textbook, to draws the…
A: Introduction Graphics.py is a Python graphics library that provides easy access to both low-level…
Q: What is the type of verbs 1) He will be (having) dinner at my parents’ house tomorrow. A(Action)…
A: Your answer is given below.
Q: 2. Team Class a. Variables i. ii. iii. iv. V. b. Methods i. ii. iii. iv. vi. Trainer -> String Gym…
A: Program Approach: 1- First, create a class name as Pokemaon. 2- Inside the Pokemaon class, define…
Q: Using Ackermann’s Function to check how slowly a program can run, Implement the algorithm. Assume…
A: Ackermann's Function is a recursive mathematical algorithm that can be used to calculate the value…
Q: Case Study 1: The following fragment of code in Figure 1 show the function to calculating the total…
A: Given program contains a function calcPrice which takes four input parameters that are Quantities of…
Q: How Do I Make Use of a Liquid Crystal Display (LCD), and What Is It?
A: Computer graphics: Computer graphics is the creation of digital images using computers. This…
Q: Of the following, the most significant difference between many console applications and GUI…
A: Console applications are text-based, meaning they use the command line interface to receive and…
Q: 5-letter words" are formed using the letters A, B, C, D, E, F, G. How many such words are possible…
A: (a) The number of possible ways for 5 letter word when no condition is imposed is obtained as…
Q: Provide an explanation for three circumstances in which a surrogate key should be constructed in…
A: Indicators that point to the existence of a surrogate key There are three circumstances that…
Q: What instances of organizations employing databases in your information systems can you think of?
A: A database is a grouping of connected data. For any organisation, it is crucial. Businesses may…
Q: MINTERMS AND MAXTERMS ( BOOLEAN ALGEBRA AND LOGIC GATES) Convert Y = ABCD + A′BC + B′C′ into a sum…
A: The above question is solved in step 2 :-
Q: Prove the associative law An (BNC) = (ANB) nc by membership table
A: SETS:- A set is an unorganized grouping of unique pieces. Any mathematical operation can use sets to…
Q: Do you think it's important for an IT worker to understand binary? Can you think of five other…
A: Introduction: Programming gives the computer instructions. Tasks are instructed. Programmers use the…
Q: At least four (4) of the best practices for internet security should be addressed, along with an…
A: Introduction : Internet security is the process of protecting and preserving data or information…
Q: What is system design and explain
A: Software development: Software development is the process of creating, designing, and programming…
Q: fast please 1.In no more than 50 words, give two specific reasons why recursive functions are…
A: Introduction Recuresive Function: Code for recursive functions regularly uses loop configurations,…
Q: Explaining the need of using firewalls is an important step in maintaining the confidentiality of a…
A: Firewall is a network security device which is used monitor and filters the network traffic whether…
Q: explain how to do it aswell. For this assignment, write a Python script to allow users to enter the…
A: Algo: 1. Taking a variable employee_name and asking the user to enter the employee name input() is…
Q: Output each floating-point value with two digits after the decimal point, which can be achieved as…
A: Algorithm of the code: 1. Ask the user for the current price of the house2. Store input as…
Q: a) Based on the following specifications, construct the HTML code to generate the form design as…
A: Answer Step1:we have create a form to order the cake Step2: Then create the cake and their option…
Q: Harry Birthdays Add a Birthday All Birthdays Please do provide the HTML and CSS codes separately…
A: The algorithm of the code:- 1. Start the program 2. Set up the CSS styles for the header,…
Q: Identify and provide a description of each of the computer's components.
A: The following are the major components of a computer system: Central Processing Unit (CPU): The…
Q: 1 English to Propositional Logic Convert the following English sentences into propositional logic.…
A: Propositional logic is a branch of mathematical logic that deals with propositions, which are…
Q: What are three signs that a surrogate key should be generated for the primary key of a relation…
A: A surrogate key is one that serves no practical or operational purpose. It's "artificial" and made…
Q: can you please convert this python code into java? Python code is as shown below: # recursive…
A: The source code of the java program public class Main{public static boolean row_puzzle_rec(int…
Q: nt does a website rely on what you say are its basic
A: We know The extent to which a website relies on its basic features can vary greatly. Some websites,…
Q: Write a program that converts Celsius temperatures to Fahrenheit # temperatures. The formula is as…
A: 1) Since programming language is not specified I have written program in python 1) Below is program…
Q: Affirm the significance of the term, the concept, or the analysis in either the process of attacking…
A: Introduction : A digital attack is an attack on a computer system, network, or individual computer…
Q: Write an assembly language program that corresponds to the following C program: int num; int main ()…
A: Answer: Here is an example of an x86 assembly language program that corresponds to the given C…
Q: Could you provide me some examples of companies that make use of databases in your IT…
A: The term "DBMS" (Database Management Systems) refers to a group of information and management…
Q: Which one of the following commands generates an array of equally spaced elements? x = 0,0.1,10 x =…
A: Introduction Array: An array is just a group of similar information items maintained in successive…
Q: Imagine a histogram (bar graph). Design d hold if someone poured water across the t 1. 0, 6, 0, 0,…
A: SummaryWhat is a histogram? A histogram is a graphical representation of data points organized into…
Q: Let's say you have bought a new 16GB pen drive. When you plug it into the computer, you notice that…
A: The reason for the difference in memory size of a pen drive can be attributed to several factors.…
Q: In what way does an IDS function?
A: The answer is given in the below step
Step by step
Solved in 3 steps with 1 images

- We are given the following: D = set of all students at your school M(s) = “s is a math major” C(s) = “s is a computer science student” E(s) = “s is an engineering student” Use quantifiers, variables, and the predicates M(s), C(s), and E(s) to express the statement of “Some computer science students are also math majors”onsider the challenge of determining whether a witness questioned by a law enforcement agency is telling the truth. An innovative questioning system pegs two individuals against each other. A reliable witness can determine whether the other individual is telling the truth. However, an unreliable witness's testimony is questionable, below is a confusion matrix of all the possible outcomes from a given scenarios, This pairwise approach could then be applied to a larger pool of witnesses. Answer the following: Assume a pool of K witnesses, in which the reliable ones are eager to help solve a case, and the unreliable ones are equally eager to hide the truth. Prove that if more than half of the witnesses are unreliable, the approach outlined above cannot help identifying the reliable witnesses.NOTE: WRITE IN C# Write a distributed probability random number generator using one of the probability sampling methods (like rejection sampling). Explain the codes and the sampling implementation in detail. Example: İnputs : (3, 0.4) (5, 0.5) Output: Generated random number is 3, it has %40 probability Generated random number is 5, it has %50 probability NOTE: WRITE IN C# NOTE: MAKE A GENERIC SOLUTION THAT APPLIES FOR ANY GIVEN NUMBER AND PROBABILITY. NOT JUST BASED ON THIS EXAMPLE !!!
- In R-Studio Problem 2. Find a large set of integers (with at least 10000 observations) representing a sample drawn from real life (i.e., do not generate the numbers using some random number generator). First, explain what the integers correspond to in real life. Then, investigate the distribution of the integers, and also the first and last digits of the integers in this sample (For example, if the data has [34 65], plot the distribution of these numbers and also distribution of [3,6] and [4 ,5] separately). Does any of these digits follow a uniform distribution? Is this expected? If one of them does not follow a uniform distribution, what distribution does it follow? Can you explain why? [You can analyze the image age dataset provided by IMDB Wiki, which contains the ages of actors and actresses whose photos are present in the IMDB database. The data contains 459868 age values in years, ranging from 1 to 99 years.]In Python, write a function that produces plots of statistical power versus sample size for simple linear regression. The function should be of the form LinRegPower(N,B,A,sd,nrep), where N is a vector/list of sample sizes, B is the true slope, A is the true intercept, sd is the true standard deviation of the residuals, and nrep is the number of simulation replicates. The function should conduct simulations and then produce a plot of statistical power versus the sample sizes in N for the hypothesis test of whether the slope is different than zero. B and A can be vectors/lists of equal length. In this case, the plot should have separate lines for each pair of A and B values (A[1] with B[1], A[2] with B[2], etc). The function should produce an informative error message if A and B are not the same length. It should also give an informative error message if N only has a single value. Demonstrate your function with some sample plots. Find some cases where power varies from close to zero to…This problem exercises the basic concepts of game playing, using tic-tac-toe (noughtsand crosses) as an example. We define Xn as the number of rows, columns, or diagonals with exactly n X’s and no O’s. Similarly, On is the number of rows, columns, or diagonals with just n O’s. The utility function assigns +1 to any position with X3 = 1 and −1 to any position with O3 = 1. All other terminal positions have utility 0. For nonterminal positions, we use a linear evaluation function defined as Eval (s) = 3X2(s)+X1(s)−(3O2(s)+O1(s))."Mark on your tree the evaluations of all the positions at depth 2."
- Question 2. Use composition approach to simulate the following distributionP = 0.3p1 + 0.7p2,where p1 follows a geometric distribution with mean 2 and p2 follows a Bernoulli distributionwith mean 0.1. Write Python code with n = 10^6. Use the random seed 0. Compute thesimulated mean. # use Spyder1(a). For an M/M/1 queuing system, write your own function in R to compute andoutput the:1. long-run probability po,p1,…,pn of there being 0,..,n people in the system.2. the values L, Lq, W, Wq, and Wse. The function should return elements with the names probs (vector of po,…,pn), L, Lq, W,Wq, and Wse (does not have to be in this order) The function should take as inputs, lambda (arrival rate), mu (service rate), and n (thenumber of people to compute probabilities for 0,…,n) Note: you are to code the computations for the above on your own, so none of the functionsin the queueing package are to be used. 1(b). Using your function from 1(a), find the values (b)-(f) in the Queuing Theory(M_M_1).SUCCESSIVE-OVER-RELAXATION Method TROUBLESHOOTING: Fix the errors in the code below and run the script with your modified code function [x,numIter,omega] = gaussSeidel(func,x,maxIter,epsilon) % Solves Ax = b by Gauss-Seidel method with relaxation. % USAGE: [x,numIter,omega] = gaussSeidel(func,x,maxIter,epsilon) % INPUT: % func = handle of function that returns improved x using % x = starting solution vector % maxIter = allowable number of iterations (default is 500) % epsilon = error tolerance (default is 1.0e-9) % OUTPUT: % x = solution vector % numIter = number of iterations carried out % omega = computed relaxation factor if nargin < 4; epsilon = 1.0e-9; end if nargin < 3; maxIter = 500; end k = 10; p = 1; omega = 1; for numIter = 1:maxIter xOld = x; x = feval(func,x,omega); dx = sqrt(dot(x - xOld,x - xOld)); if dx < epsilon; return; end if numIter == k; dx1 = dx; end if numIter == k + p omega = 2/(1 + sqrt(1 - (dx/dx1)ˆ(1/p))); end end error(’Too many iterations’)
- Simulated annealing is an extension of hill climbing, which uses randomness to avoid getting stuck in local maxima and plateaux. a) As defined in your textbook, simulated annealing returns the current state when the end of the annealing schedule is reached and if the annealing schedule is slow enough. Given that we know the value (measure of goodness) of each state we visit, is there anything smarter we could do? (b) Simulated annealing requires a very small amount of memory, just enough to store two states: the current state and the proposed next state. Suppose we had enough memory to hold two million states. Propose a modification to simulated annealing that makes productive use of the additional memory. In particular, suggest something that will likely perform better than just running simulated annealing a million times consecutively with random restarts. [Note: There are multiple correct answers here.] (c) Gradient ascent search is prone to local optima just like hill climbing.…Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. coordinating, we can observe the number of times some white string meets some dark string. We process the number of sets of distinctively shaded strings that cross rather than the number of convergence focuses, so one convergence point might be counted on numerous occasions if various sets of strings meet at a similar point. In case c is a legitimate shading, let f(c) mean the base number of such convergences out of all conceivable matchings. circle above is portrayed by the shading bwbbbwww. In the wake of coordinating with the spools as displayed, there is one convergence between contrastingly shaded strings. It tends to be demonstrated that it is the base conceivable, so f(bwbbbwww)=1. You are given a string s addressing an incomplete shading, with dark, white, and uncolored spools. A shading c is called s-reachable if you can accomplish it by allocating tones to the uncolored…Please implement Multinomial Logistic Regression on the following data. Please continue from the given code:

