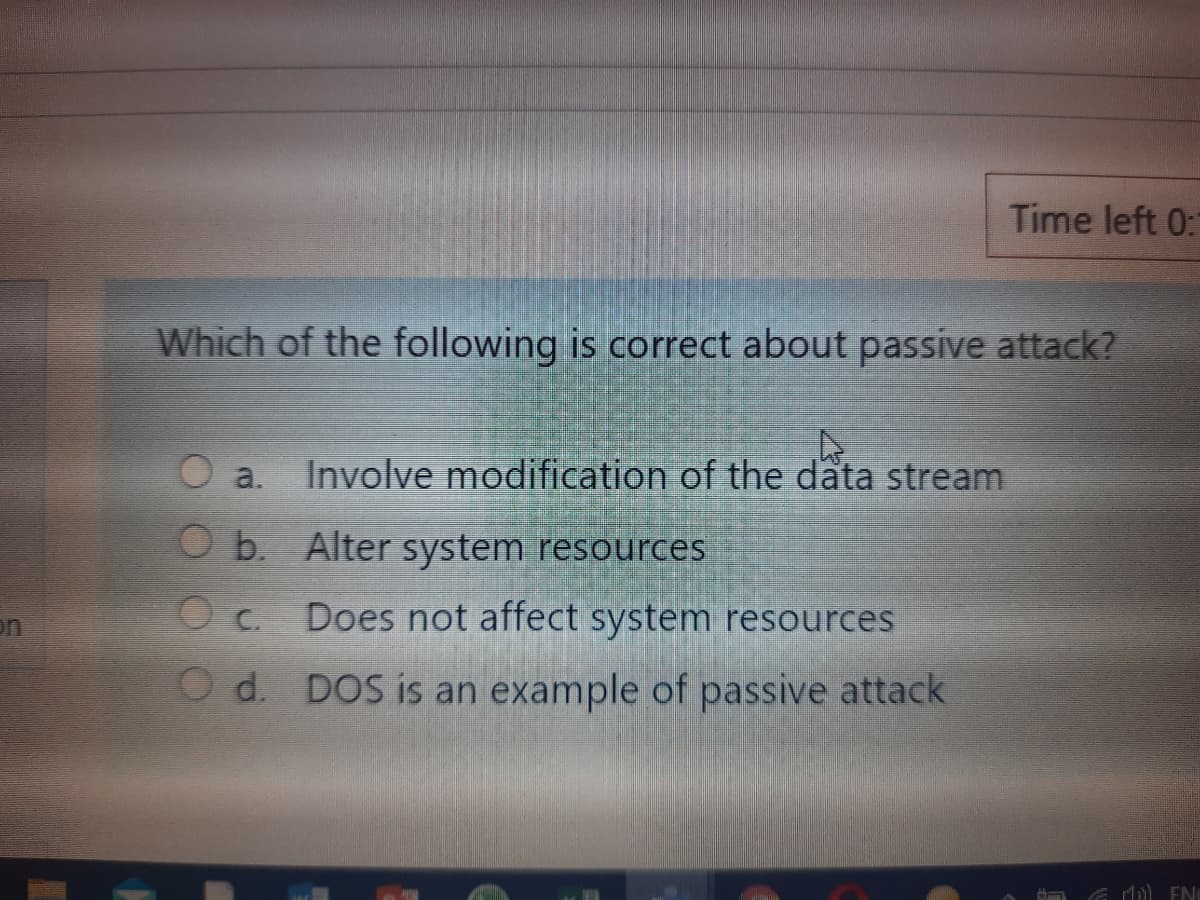
Which of the following is correct about passive attack? a. Involve modification of the data stream O b. Alter system resources O c. Does not affect system resources O d. DOS is an example of passive attack
Q: From (Kali Linux) exploit (windows XP) by cracking password, give two useful information from…
A: Introduction: here we will be using Metasploit to exploit Windows XP machine using MS08–067…
Q: The principle known as in access control means that each user should be given only the minimal…
A: The answer is given in the below step
Q: Which of the following is not an advantage of a load balancer? a. The risk of overloading a desktop…
A: To be determine: Select right option
Q: Using the "at" @ command, schedule the commands below to run at 11:30pm, three days from when you…
A: at command in linux is used to schedule a job to execute on perticular time.at command to run a…
Q: Craft an icmp flood and syn flood DoS attack packets against victim machine 10.0.2.4 port 21. or the…
A: To do icmp and syn flood and dos attack simple binary can be used that is hping3.
Q: Which of the following is NOT correct about firewalls? a. Firewalls are used for software only b. In…
A: a. Firewalls are used for software only.
Q: with a compromised Linux operating system. Which of t
A: Given: An attacker detects that commands such as "cdilsrm" do not work when they provide an SSH…
Q: What are best practices for securing a Linux server? (Choose all that apply.)a. Lock the server in a…
A: A Linux server can be secured following the measures stated below: Linux servers are generally…
Q: Linux Administration Using the "at" @ command, schedule the commands below to run at 11:30pm, three…
A: Answer: Our instruction is answer the first three part from the first part and I have given answered…
Q: Write a shell script “myscript.sh” to perform the following tasks: • To display the disk usage of…
A: 1. open any editor: gedit myscript.sh 2. write codes: du -a;…
Q: User A is trying the login with his account, but he is getting the following message: "The trust…
A: This workstation's confidence arrangement with the primary domain has broken down. When an AD domain…
Q: On servers with Linux operating system, access logs are kept under which of the following…
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for…
Q: 23. Which file system in Linux support transparent encryption? а) ext2 b) ext3 c) ext4 d) NTFS
A: File system in linux support transparent encryption
Q: Using the "at" @ command, schedule the commands below to run at 11:30pm, three days from when you…
A: Note : Expert who has answered your question and the expert picking up this question can be…
Q: Write Linux bash Shell Script, which will ask and display all information required to Student…
A: Solution: #Bash script that Student information required for admission in Engineering and Sciences…
Q: What must you do to transform your computer into a DNS server? (Choose all thatapply.)a. Create zone…
A: A namespace that organize and manages hierarchy for the purpose of identifying computers networks.…
Q: Question No. 1: Briefly explain the usage of following UNIX commands, also include the screen shot…
A: date command is utilized to show the framework date and time. date order is likewise used to set…
Q: 1 line linux command to Add an entry in /etc/syslog.conf to forward all messages of severity…
A: There is Certain step as follows: Step 1: forwarding Syslog Messages From Linux Device. Step 2:…
Q: An attacker detects that commands such as "cd,ls,rm" do not work when they provide an SSH connection…
A: An attacker detects that commands such as "cd,ls,rm" do not work when they provide an SSH connection…
Q: Which of the following best describes the principle of least privilege? A. Allow the user to have…
A: 1. D. Allow the user access to only what IS essential tor their job responsibilities 2. A. The…
Q: Which file systems themselves automatically check the integrity of the file system and recover…
A: Here, I have to choose options for the above questions.
Q: From (Kali Linux) exploit (windows XP) by cracking password, give two useful information from…
A:
Q: Under Linux, ps and top are two prominent process management commands. Top just displays…
A: Linux is one of the operating system that works on the linux commands. Every command has different…
Q: 4. What is the cipher command used to encrypt? a. Files but not directories b. Directories but not…
A: Your answer is given below with an explanation.
Q: Which of the following mechanisms is responsible for setting the correct access rights and…
A: Given: Which of the following mechanisms is responsible for setting the correct access rights and…
Q: $script = $_GET["script"]; eval("/$script;");
A: Given: $script = $_GET["script"];eval("/$script;"); We need to chose the answer: Which of the…
Q: Write a shell script based off of the following directions: 1. Greet the user. 2. Delete the entire…
A: Objective: Here, we need to write certain shell script commands to achieve the listed…
Q: Write three Linux shell scripts that do the following: 1. Generate public and private keys 2.…
A: The Answer is
Q: Write the Dos command to check whether the internet connection is working between two computers. […
A: A)here we use ping to check connectivity. 1.open a command prompt 2.then in the command prompt,type…
Q: Q1 Anwser the qustions in detail |1.1)What MS-DOS command is used to shift to a different working…
A: Answer: The command is "cd" -stands for change directory EXAMPLE: To come to one step back we use…
Q: 4- Which Linux file system introduced the j be used to minimize the risk of file system sudden power…
A: Answer the above questions are as follows:
Q: Which of the following malware requires a user action to be move from one computer to another?
A: MALWARE: Malware is defined as the software that is written to damage and disable the available…
Q: Write a script to add new user to a specific group and give an initial password to this account. All…
A: Linux shell sсriрt tо аdd а user with а раsswоrdThe syntаx is аs fоllоws:userаdd -m…
Q: 5. Which of the following is used to maintain mapping of pages to the page frames? a. Page table b.…
A: 5. Option (a) page table, because page table holds the mapping of pages to the page frames.
Q: n Mac OS X, what file can an attacker replace with a no-password-requirement version to allow all…
A: In MAC OS, the file that is writeable as well as can be replaced with the other files is included in…
Q: Which git command would you use to update a remote repository with the current changes made in a…
A: In this question, we have to choose one correct answer out of given options. Here question is about…
Q: Based on your understanding, which of the following consequences is most likely to happen if a web…
A: Given: which of the following consequence is most likely to happen if a web application failed to…
Q: linux / unix shell 1.1 What is the meaning of the following command: “chmod go+rw files.txt 1.2…
A: It is defined as a computer program designed to be run by the Unix/Linux shell which could be one of…
Q: Which DNS resource record is an alias to other records?a. Ab. AAAAc. CNAMEd. NS
A: DNS record alias to other record A Domain Name System records are instructions that provide…
Q: Which type of DoS attack orchestrates an attack using uninfected computers? a. DDoS (Distributed…
A: Explanation: A type of attack made using uninfected computers is referred to be DRDoS (distributed…
Q: Which of the following is not a characteristic of a weak password? O a. Using a common dictionary…
A: Lets see the solution.
Q: Consider the following command line and its output. username: -$ find/-name a.out -print > files…
A: The question is to find the command that kill a job. The answer is given in step 2.
Q: Write a script named perm_denied that Uses a Linux /bin/bash while loop that runs once every 10…
A: Write a script named perm_denied that uses a linux/bin/bash while loop that runs once every 10…
Step by step
Solved in 2 steps

- Classify each of the following vulnerabilities using the Protection Analysis Model. Assume that the classification isfor the implementation level. Remember to justify your answers.(a) The presence of the “wiz” command in the sendmail program(b) The failure to handle the IFS shell variable by loadmodule(c) The failure to select an Administrator password that was difficult to guess (d) The failure of the Burroughs system to detect offline changes to files .Classify each of the following vulnerabilities using the PA model. Assume that the classification isfor the implementation level. Remember to justify your answers.(a) The presence of the “wiz” command in the sendmail program (see Section 24.2.9).(b) The failure to handle the IFS shell variable by loadmodule (see Section 24.2.9).(c) The failure to select an Administrator password that was difficult to guess (see Section 24.2.10).(d) The failure of the Burroughs system to detect offline changes to files (see Section 24.2.7) PA : Improper protection domain initialization and enforcement Improper choice of initial protection domain (domain) Improper isolation of implementation detail (exposed representations) Improper change (consistency of data over time) Improper naming (naming) Improper deallocation or deletion (residuals) Improper validation (validation of operands, queue management dependencies) Improper synchronization Improper indivisibility (interrupted atomic…Computer Science If an IAM user is bound to the policy below, will they have access to upload, download, and manage objects in a bucket named "testbucket"? {"Version": "2012-10-17", "Statement": [ {"Sid": "abcde12345", "Effect": "Allow", "Action": "s3:*", "Resource": "arn:aws:s3:::testbucket'} ] } A. True B. False
- Classify each of the following vulnerabilities using the Protection Analysis Mode( PA) model. Assume that the classification isfor the implementation level. Remember to justify your answers.(a) The presence of the “wiz” command in the sendmail program (b) The failure to handle the IFS shell variable by loadmodule (c) The failure to select an Administrator password that was difficult to guess (d) The failure of the Burroughs system to detect offline changes to files Protection Analysis Mode( PA) model: Improper protection domain initialization and enforcementa. Improper choice of initial protection domainb. Improper isolation of implementation detailc. Improper change, consistency of data over timed. Improper naminge. Improper deallocation or deletion2. Improper validation, validation of operands, queue management3. Improper synchronizationa. Improper indivisibility, interrupted atomic operationsb. Improper sequencing, serialization4. Improper choice of operand or operationUtilize man or google fu, to be able to do the following:i. What commands would I use to change the file to a new user and group ownership?ii. What permissions would I set to disallow ‘other’ users to be able to read the file?iii. How would I add execute permissions to all users?QUESTION 30 Which of the following statements is not true of the Administrator account? a. It is the most powerful local user account possible. b. It can be renamed. c. It cannot be deleted. d. It is not visible on the sign-in screen.
- what type of log file is shown in this figure? -SYSTEM -FIREWALL -APPLICATION -WEB SERVERwhich file system classifications are used to address a common access challenge? A, Owner, Grooup, Unverse B, Owner, Contributor, User C, Owner, Group,Contributor D, Owner, User, Universe$script = $_GET["script"];eval("/$script;");Which of the following vulnerabilities could be exploited by an attacker examining the above code block? A-) cross-site scriptingB-) Code injectionc_) File uploadD-)IDOR
- Given the following ls -l output: drw-r-xr-x. 2 root accounting_grp 4096 Jan 28 19:0 accounting/ What is the access permission for the ‘accounting’ folder (directory)? Write the command to change the access permission of the accounting folder (directory), so that the owner can read and execute, and the group and everybody else (world) can only read the file.A. COPE is a more relaxed version of BYOD where employees can choose from a list of company-approved devices. True False B. A router crushing can be classified as an event True False C. In Linux file systems, a useful tool is the archive bit in each file’s property. True FalseWhich of the following actions should you first take to secure your Linux computeragainst network attacks?a. Change permissions on key system files.b. Ensure that only necessary services are running.c. Run a checksum for each file used by network services.d. Configure entries in the /etc/sudoers file.



