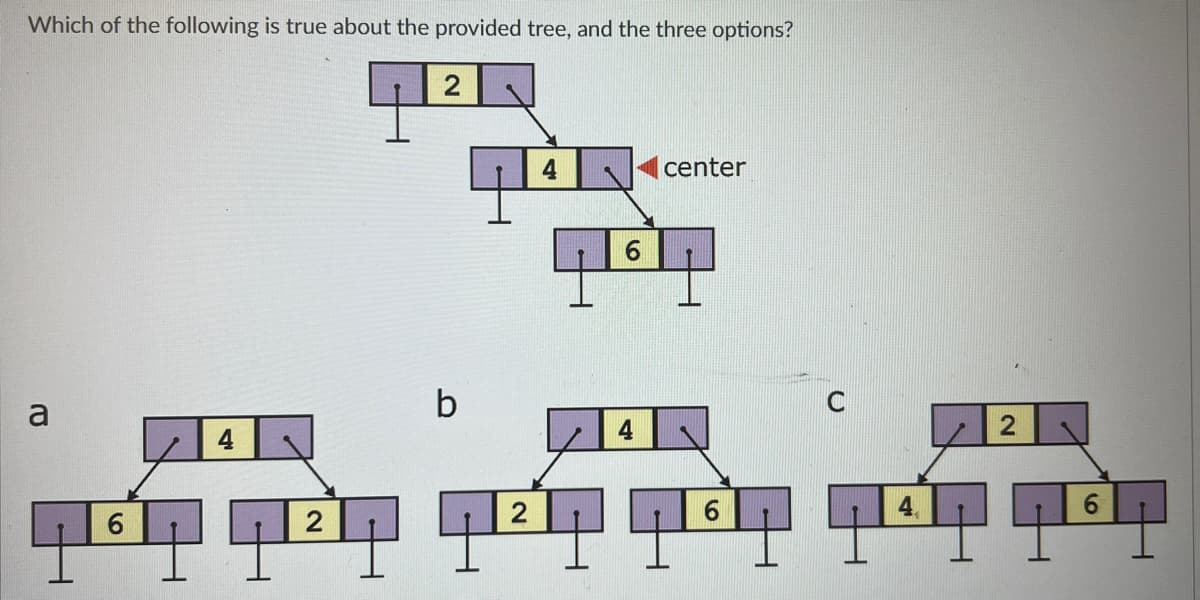
Which of the following is true about the provided tree, and the three options? T עם 6 4 2 7 2 b 2 6 center 6 4 2 6
Q: What is the balance factor of the node of this tree labeled with the red triangle?
A: ExplanationA balanced factor of a node in a tree is a measure of the relative balance of the…
Q: Risk management study. Identify assets, threats, vulnerabilities, risks, and mitigation. Category…
A: The very start of a risk organization psychoanalysis is to recognize the possessions. These items of…
Q: Determine the stack's effectiveness when allowed to function independently.
A: The Concept of a Stack in Data StructuresA stack is a linear data structure that follows a…
Q: What three characteristics must a successful network possess? Spend a few moments describing it in…
A: A successful network is an essential component in today's interconnected world. It enables the…
Q: Where does the United States' cybersecurity policy stand?
A: Understanding the current status of cybersecurity policy in the United States is crucial in…
Q: Why do HTTP, FTP, SMTP, and POP3 prioritise TCP over UDP?
A: HTTP (Hypertext Transfer Protocol), FTP (File Transfer Protocol), SMTP (Simple Mail Transfer…
Q: How important is RTN?
A: What is RTN: RTN can refer to different things depending on the context.It can stand for "Return to…
Q: Describe the most prevalent concerns regarding the security of cloud computing and how they could be…
A: There are various advantages of the cloud computing this includes the scalability , cost…
Q: Logic and Computation Just use one word to fill in the spaces. In your reply, please use commas. No…
A: Set of connections congestion is crucial in PC networking, remarkably in high-capacity networks such…
Q: Why use private network addresses? Can a private network datagram become accessible via the…
A: This question is getting some information about the explanations behind utilizing private network…
Q: 31. Consider the network shown below, and assume that each node initially knows the costs to each of…
A: Distance-Vector algorithm is iterative, asynchronous and distributed algorithm. The algorithm is…
Q: Help your friend set up a home computer network. This network connects all family PCs and mobile…
A: Setting up a home computer network is an essential task for connecting all the family's PCs and…
Q: If you want your network to be productive and effective, there are three conditions that must be…
A: In order to achieve productivity and effectiveness, a network must fulfill three crucial conditions.…
Q: Show that: ¬q 1) p→¬q 2) (p∧r)∨s 3) s→(t∨u) 4) ¬t∧¬u where ¬ is denied.
A: To show that ¬q holds based on the given statements, we need to derive it using logical deductions.…
Q: What causes DFDs to be unbalanced?
A: Data Flow Diagrams (DFDs) are graphical representations of how data flows within a system or…
Q: What purpose do protocols serve within network communication? Clarify the protocols that enable a…
A: Hello studentGreetingsThe communication between a web server and a web client is a fundamental…
Q: What separates computers and IT from non-computer media? Technology changes everyday. Consider…
A: Information Technology (IT) and computers contain reshaped our world radically. The ability to…
Q: Question 3 Draw a detailed activity Diagram in draw.io and screenshot it for me. ( **Please take…
A: An activity diagram is a type of behavioral diagram in UML (Unified Modeling Language) that visually…
Q: Which three criteria must a network satisfy in order to be considered successful and efficient?…
A: A computer network is a collection of devices, such as computers, servers, routers, switches, and…
Q: We lack the knowledge to make an informed evaluation of an operating system's inner workings.
A: Operating systems are very important computer system, bridge the gap flanked by user And the…
Q: There is a complete black box between us and how an OS function
A: The functioning of an operating system (OS) can indeed be perceived as a black box by many users.…
Q: array sorted in ascending order is rotated at some pivot unknown to you beforehand. (i.e.,…
A: Both the recursive and iterative solutions follow the same algorithms. Here's a step-by-step…
Q: airs of parentheses, write a function to generate all combinations of well-formed parentheses.…
A: The generate_parenthesis_v1 function takes an integer n as input and returns a list of strings…
Q: Which of these is NOT a valid reason to divide up a network? To a) restrict entry to broadcast…
A: Network division, also known as network segmentation, is a practice in computer networks to improve…
Q: Why is network segmentation bad? To restrict access to broadcast domains, decrease bandwidth usage,…
A: Network segmentation is not inherently wrong. Instead, it is a crucial strategy for network security…
Q: The challenge is to find ways to simplify complex programming languages. What method would you use…
A: To simplify complex programming languages, one approach to categorize the words is through lexical…
Q: Question 4 . In the Internet, file distribution can be performed using either a Peer-to-peer or…
A: In the given scenario, we are provided with certain parameters that define the characteristics of an…
Q: What differentiates BRISQUE and NIQE in the image processing field? Provide the formula and…
A: What differentiates BRISQUE and NIQE in the image processing field? Provide the formula and…
Q: Which of the six phases of DBLC does the data dictionary impact, and why?
A: The Database Development Life Cycle has become the guiding framework which the developers follow to…
Q: When the College opens, your email arrives on the BMCC web server. The BMCC web server will refuse…
A: The ARP protocol is used to identify the local computer receiving Internet data by mapping the IP…
Q: Discuss the type of interview that would be used in each of the following situations (in your answer…
A: Utilizing Interviews in ResearchInterviews serve as an important tool in data collection for…
Q: The challenge is to find ways to simplify complex programming languages. What method would you use…
A: Lexical analysis, often known as tokenization, is useful for categorizing and simplifying terms used…
Q: given input word, return the list of abbreviations. ex) word => ['word', 'wor1', 'wo1d', 'wo2',…
A: def generate_abbreviations(word): def backtrack(result, word, pos, count, cur): if pos ==…
Q: Design a nonrecursive implementation of a binary tree that maintains node data in a Vector, data. In…
A: The binary tree implementation uses a Vector called data to store the node values.The insert method…
Q: Disc prefetching is exactly what it sounds like: preloading data onto a disc. What are the benefits…
A: Recording prefetching, also known seeing that disk caching, is a development computer systems use to…
Q: Here are five main reasons why you should always update your software: How precisely do you
A: What is software: Software refers to a collection of programs, data, and instructions that enable…
Q: path refers to any sequence of nodes from some starting node to any node in the tree along the…
A: To find the length of the longest consecutive sequence path in a binary tree, we can use a…
Q: Uniprocessor systems require essential sections to safeguard shared memory from multiple processes.…
A: Because SMP systems share memory, programmed that process large amounts of data or move data between…
Q: What benefits does the deep web offer businesses that rely on IT systems?
A: An information system (IS) which refers to the one it is a formal, sociotechnical, organizational…
Q: Given a system with 2 memory channels and 4 DRAM DIMMs (2 DIMMs per channel), each DIMM has: • 1…
A: Addressing in physical and virtual memory spaces refers to the mechanism by which a computer's…
Q: IP, Subnet Mask, Subnet Information? field value Host IP subnet mask Subnet bitcount Subnet count…
A: Given:IP address= 172.33.2.34Subnet mask= 255.255.255.252
Q: Give a brief summary of the OS's functions and how they are accomplished.
A: An operating system (OS) is a software that serves as the foundation for computer systems, providing…
Q: Given a string, find the first non-repeating character in it and return it's index. If it doesn't…
A: Step1: start traversing string from starting index to endstep2 : then check whether the char at…
Q: IP, Subnet Mask, Subnet Information? field value Host IP subnet mask Subnet bitcount Subnet count…
A: The provided information includes an IP address, subnet mask, and subnet details.
Q: Write a code using C# for the following images.
A: Define the Building class with properties representing the details of a building: Type, RoomCount,…
Q: Assist a buddy with home networking. All home gadgets must be networked. List networking hardware.…
A: To create a home network that connects all the gadgets, it will need several networking hardware…
Q: Explain in detail why my computer's startup time is so sluggish. Your assistance is greatly valued.
A: Given that, the computer's startup time is so sluggish. That means the computer is taking so much…
Q: Which layer-2 exploit blocks genuine clients from acquiring IPv4 addresses? Attacks using DHCP…
A: Different layer-2 vulnerabilities can be used in the field of network security to interfere with…
Q: What causes DFDs to be unbalanced?
A: Data Flow Diagrams (DFDs) are graphical representations that illustrate the flow of data within a…
Q: What is python
A: Python is a popular high-level programming language that is widely used for its simplicity,…
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

- Which of the following statements are correct for the tree below? (Select all that applies.) look at the picture sent Group of answer choices The number of internal nodes is 3 and the number of external nodes is 4. The depth of the node 5 is 3. The height of the tree is 3.Which of the following is the postorder traversal of the tree below? A. 200, 175, 150, 90, 50, 20 B. 20, 50, 90, 150, 175, 200Which of the following is an inorder traversal of the tree below? A. 20, 50, 90, 150, 175, 200 B. 200, 175, 150, 90, 50, 20
- Which of the following changes the contents of the strWord variable from “trees” to “tree”?a. strWord = strWord.Trim(4)b. strWord = strWord.Trim(5) c. strWord = strWord.Remove(4)d. strWord = strWord.Remove(5, 1)Which of the following is an AVL tree?Which statement is correct of suffix tree with a string of length n?a) The tree has n leaves.b) The tree has n rootsc) Height of Tree is nd) Depth of tree is n
- Which of the following statement is false? In a parse tree, the label of each leaf node is terminal In a parse tree, the labels of all nodes except leaf nodes are nonterminal In a parse tree, the root of the tree is called the start symbol of the derivation None of the mentionedThese are keys and corresponding priority. which of those choices will cause AVL rotations after inserting into the Tree below?Which of the following statements are correct for the expression trees? (Select all that applies.) a. An expression tree is a binary tree. b. The root and internal nodes are operators. c. Each leaf is an operand. d. Subtrees are sub-expressions, with the root being an operator. 2. The height of a binary tree is the maximum number of edges in any root to leaf path. The maximum number of nodes in a binary tree of height h is: a. (2^h)-1 b. (2^(h+1))-1 c. 2*(h+1)-1 3. Which of the following statements are correct? (Select all that applies.) a. The maximum number of internal and external nodes in a proper binary tree with n nodes are (n-1)/2 and (n+1)/2, respectively. b. The maximum number of nodes at level k (k = 0,1,2,...) of a proper binary tree: 2^k c. Depth of a node refers to the number of ancestors. d. Height of a tree refers to the the maximum of the depths of its leaf positions.
- Which of the following node definitions are FALSE? Select one: a.Leaf nodes are also known as external nodes b.Internal node is a node with at least one child c.Leaf nodes have no parent d.Root node is a node with no parent e.Leaf nodes have no childrenWhich of the following is true of a decision tree? Group of answer choices Each non-leaf node is labelled with a class Each leaf node is labelled with a class Each root node is labelled with a class Each node is labelled with a class.Which of the following algorithms are useful for processing queries on trees? A. Centroid Decomposition. B. Heavy Light Decomposition. C. Both (A) and (B). D. Neither (A) nor (B).

