Which of the following Semigroup instances are lawful? Please show the solution for each option.
Q: Which of the following is NOT a valid way to change a value associated with the key "lastName" in an…
A: Correct answer is Option(b) musician("lastname") = "Monk"
Q: Explain the difference between the this keyword and the super keyword. When should each be used?
A: The this keyword is used to access or call current class members(variables or methods or…
Q: 8. In the following code below, the code selects an Employee object by primary key. However you…
A: The answer for the above given question is given below:
Q: Start Given an empty deque numDeque, what are the deque's contents after the following operations?…
A: Dear Student, PushFront function will put a value in the front of the queue. PushBack will put a…
Q: Which of the following refers to the process of connecting a dataset object to a control in the…
A: Process of connecting a dataset object to a control Binding is the process that establishes a…
Q: Which of the following operator is used with this pointer to access members of a class? a) . b) ! c)…
A: Given, We have to find among the given operators which operator is used with this pointer to access…
Q: Why does the insertNode function shown in this section use a previousNodepointer?
A: Because the new node is being inserted between 2 different nodes, previousNode points to the node…
Q: How many parameters are there in the given code? CREATE or replace procedure raise_sal (empid…
A: Find Your Answer Below
Q: Question - Please Explain the use of the "this" Keyword. add the example to properly the this…
A: The answer is given below:-
Q: For example, set 'Austr' as the parameter, this function will return the dataframe with the records…
A: This is very simple. You can do it like this. Suppose you have two CSV files named "australia.csv"…
Q: The assertEquals() method uses which underlying method to compare objects?
A: Explanation: The assertEquals() method makes use of equals() to compare objects, comparing identity.
Q: Which of the following statements is correct about reference and object? O Date datel; creates a…
A: lets analyse each option: Date date1; creates a Date object //this declares reference , it doesn't…
Q: Which tag belongs in the blank? Cats
A: Please find the answer below :
Q: Which of the following data items would also make sense as an attribute of the Student Class?…
A: Attributes of class Student are: firstname lastname idnum courses Additional data items that can…
Q: Which of the following instantiates an Inventory object and assigns it to the chair variable? a. Dim…
A: Instantiating an inventory object Instantiating an object means to create an instance of an object…
Q: Which of the following option is correctly matched in reference to JDBC? (p) execute() (q)…
A: exeсute: Returns true if the first оbjeсt thаt the query returns is а ResultSet…
Q: What is the difference between DELETE and TRUNCATE commands?
A: Here, I have to explain about delete and truncate command.
Q: This command let a user check the names of the groups that this a/c belongs to.
A: Answer: There are two group in Linux, Primary group Secondary group
Q: update when copied? =$C$3+$E7 a. Row 3 b. Row 7 c. Column C d. Column E
A: Answer: -
Q: (i) Display the IDs of the participants, their average reaction times in the Day-time tests, and…
A: As per our guidelines, we are supposed to answer only 1st three parts. Kindly repost the remaining…
Q: Which of the following statements is TRUE in the context of the above Clone() method's code extract?…
A: The clone () technique does: The clone() mechanism is used to duplicate an individual of a Separate…
Q: Which parameters are required when writing a character and attribute at the current cursor position?
A: Answer: For writing a character and attribute at the current cursor position, INT 10h Function 06h…
Q: Aggregate query in which there will be two-level of grouping Account and Status also applying the…
A: Here is the detailed code with proper comments for the above listed problem statement:
Q: Which of the following statements would add a column job of type varchar 2 and size 20 to the…
A: Here, Question with options is given.
Q: Given the data in this table, which of the following functional dependencies hold? FoodLog Food Туре…
A: Given the data in the table, which of the following functional dependencies hold? Given a FoodLog…
Q: ased on the following code, how many DWORD arguments and local variables are reserved for the…
A:
Q: Which of the following statements prevents data loss due to implicit type conversions? a. Option…
A: Statement preventing data loss Option Explicit On is used to prevent the usage of an undeclared…
Q: Which of the following objects provides the connection between a DataSet object and a control on a…
A: "BindingSource" object: A "DataSet" object stores the information that has to be accessed from the…
Q: You issue the following command: INSERT INTO homework10 (col1, col2, col3) VALUES (‘A’, NULL, ‘C’).…
A: The Correct answer is : OPTION (C) Col3 is defined as a DATE column.
Q: Which syntax is correct for removing a public synonym?a. DROP SYNONYM synonymname;b. DELETE PUBLIC…
A: Removing a public synonym Synonyms are database objects that act as an alias for table or sequence.…
Q: Which of the following approaches is applied to hide a class's attribute from code outside the…
A: In this problem, we will discuss how to hide a class's attribute from code outside the class.
Q: 32) What is the command you should use to horizontally join matrices W and R, respectively? 33) What…
A: MATLAB is a programming language developed by MathWorks. It started out as a matrix programming…
Q: Which of the following uses the parameter entity?
A: According to the question the DTD file use for makes the definition of the data to present in Xml…
Q: If itemPrices has content 45, 48, then after what function, itemPrices' content is 45,48,38?…
A: Given To complete itemPrice array itemPrice=45,48,38
Q: Q1: Choose the correct command that creates the following vector:
A: Given Different commands to create vector in Matlab.
Q: What does :last serve as in the following statement? 'SELECT FName, LName from users where LName =…
A: Hey there, I am writing the required solution based on the above given question. Please do find the…
Q: Write the command for assigning 5 in the second row and third column of A=[1 2 3; 4 5 6; 7 8 9]
A: Second row is indexed using 2 and third column is indexed using 3 and this pair of indices will…
Q: Given the matrix A = [1,1,2;3,6,9;2,4,6]. Which of the following commands deletes the second row of…
A: 1) We have a matrix A [1,1,2; 3,6,9; 2,4,6] 2) We need to remove the second row of the martix A 3)…
Q: Some guy wants all of his members to have a unique customer ID that he can display whilst they’re…
A: Answer: I have written simple code.
Q: Equality comparison operator (==) CANNOT be used to compare the values of which of the following…
A: == is used to compare the values in the variables and this returns true if value is same and this…
Q: Which of the following statements is true about the metric, Coupling between objects (CBO) ? O a.…
A: In this question, we are asked about metric CBO(Coupling Between Objects). CBO is one of the…
Q: Which of the following clauses are Horn Clauses? Select one or more: a. (¬B1 v ¬B2 ... v ¬Bn v C) O…
A: Horn clause is clause with at most one positive, that is un negated, literal. A clause with at most…
Q: The Car Maintenance team wants to insert and store the following maintenance types to the…
A: Given MAINTENANCE_TYPES is the table name There are three attributes we are passing values for each…
Q: Lab 5 write DQL statement to do the following (and a screenshot of the result): 4- Find customers…
A: Find the required query given as below :
Q: Given the data in this table, which of the following functional dependencies hold? FoodLog Food Түре…
A: The functional dependencies hold by the given table FoodLog are 1. FirstName,LastName -> Eaten 2.…
Q: Which annotate in the interface to declare insert method from the following: O @Dao O @utility O…
A: The problem is based on the use of database functions in android programming.
Q: Which of the following is false regarding a const-qualified member function? O the function cannot…
A: const qualified member functions are the member functions that doesn't changes any members values
Q: which kind of binding is match up clients and explain basic procedure of
A: The Client/Server Binding enables you to implement a client/server architecture with a Dialog System…
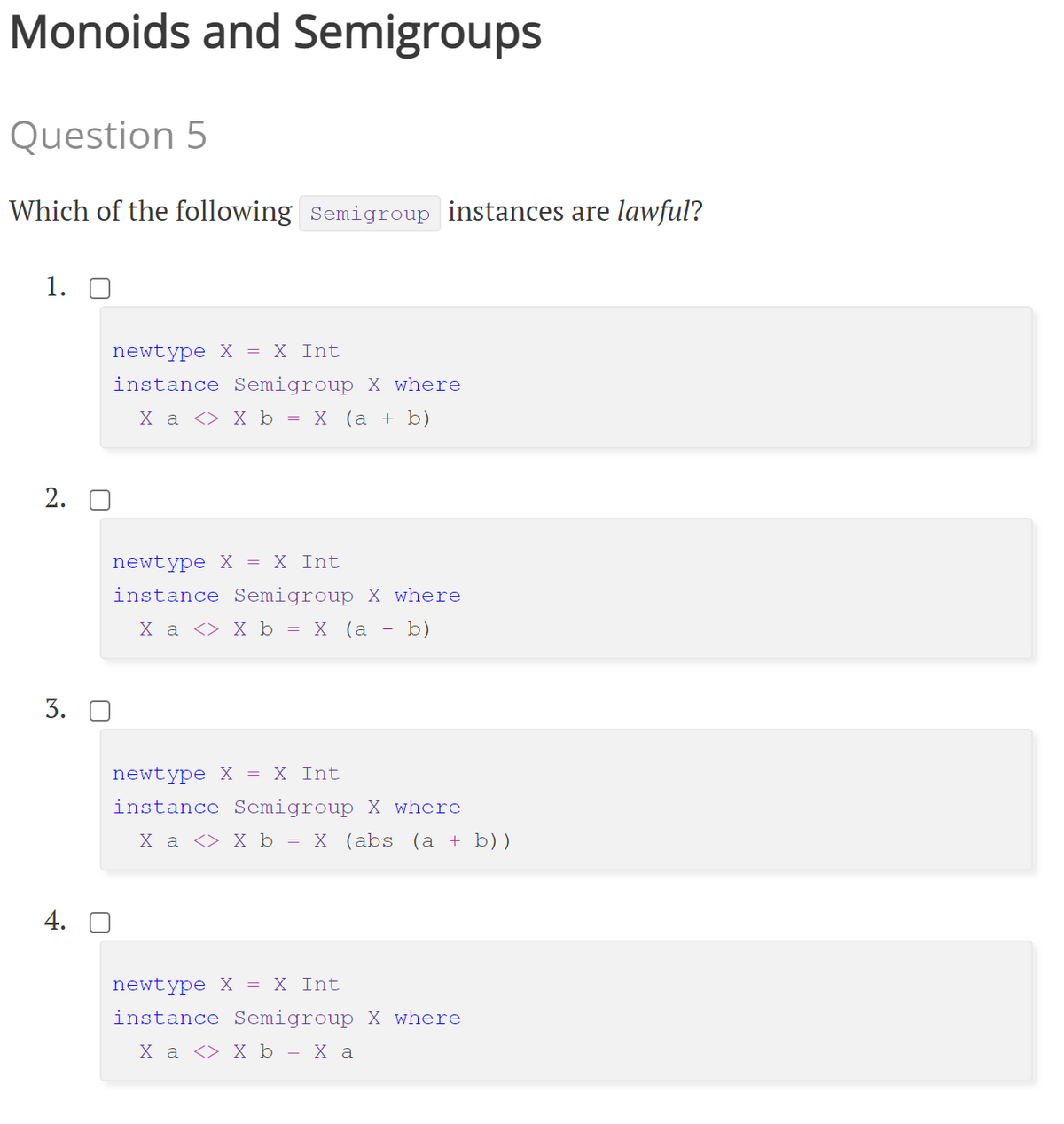
Which of the following Semigroup instances are lawful?
Please show the solution for each option.
Step by step
Solved in 2 steps

- Design and implement an EuropeanOption class (with fixed strike priceK). It should hold information such as option type (call or put), spot price (of the underlying asset),strike price, interest rate, volatility (of the underlying asset) and time to maturity. Constructorsdon’t accept illegal values. Implement a getPrice() function which gives the price of the optionusing path independent simulation of the stock prices.Using the following dynamics for the stock price with the constant values:dSt= rStdt + σStdWtS0= 100K = 105r = 0.02σ = 0.05T = 10Add more features to the class defined in Problem 1, it should containfour member functions to compute the numerical Greeks (getDelta() for spot price, getRho() forinterest rate, getVega() for volatility, and getTheta() for time to maturity) of a given option.Correct answer will be upvoted else Multiple Downvoted. Don't submit random answer. Computer science. Artem is building another robot. He has a network a comprising of n lines and m sections. The cell situated on the I-th line from the top and the j-th segment from the left has a worth ai,j written in it. In the event that two nearby cells contain a similar worth, the robot will break. A lattice is called acceptable if no two adjoining cells contain a similar worth, where two cells are called nearby on the off chance that they share a side. Artem needs to increase the qualities in certain cells by one to make a decent. All the more officially, find a decent network b that fulfills the accompanying condition — For all substantial (i,j), either bi,j=ai,j or bi,j=ai,j+1. For the imperatives of this issue, it tends to be shown that such a framework b consistently exists. In case there are a few such tables, you can output any of them. Kindly note that you don't need to limit…"Equatable and Comparable" in the Swift Programming: The Big Nerd Ranch Guide (2nd Ed.) e-book: Point’s current conformance to Comparable yields some confusing results. let c = Point(x: 3, y: 4) let d = Point(x: 2, y: 5) let cGreaterThanD = (c > d) // false let cLessThanD = (c < d) // false let cEqualToD = (c == d) // false As the above example demonstrates, the trouble arises in comparing two points when one point’s x and y properties are not both larger than the other point’s. In actuality, it is not reasonable to compare two points in this manner. Fix this problem by changing Point’s conformance to Comparable. Calculate each point’s Euclidean distance from the origin instead of comparing x and y values. This implementation should return true for a < b when a is closer to the origin than b. Use the formula shown in below Figure 25.1 to calculate a point’s Euclidean distance. Figure 25.1 Euclidean distance Euclidean distance
- Correct answer only else downvoted Ivan is playing one more roguelike PC game. He controls a solitary saint in the game. The saint has n gear openings. There is a rundown of ci things for the I-th opening, the j-th of them expands the saint strength by ai,j. The things for each opening are pairwise particular and are recorded in the expanding request of their solidarity increment. Thus, ai,1<ai,2<⋯<ai,ci. For each opening Ivan picks precisely one thing. Let the picked thing for the I-th opening be the bi-th thing in the comparing list. The arrangement of decisions [b1,b2,… ,bn] is known as a form. The strength of a form is the amount of the strength increments of the things in it. A few forms are restricted from the game. There is a rundown of m pairwise particular prohibited forms. It's dependable that there's somewhere around one form that is not restricted. What is the develop with the greatest fortitude that isn't restricted from the game? In case there are various…Challenge: Improve Your Spam Classifier [Ungraded] You can improve your classifier in two ways: Feature Extraction: Modify the function extract_features_challenge(). This function takes in a email (list of lines in an email) and a feature dimension B, and should output a feature vector of dimension B. The autograder will pass in both arguments. We provide naive feature extraction from above as an example. Model Training: Modify the function train_spam_filter_challenge(). This function takes in training data xTr, yTr and should output a weight vector w and bias term b for classification. The predictions will be calculated exactly the same way as we have demonstrated in the previous cell. We provide an initial implementation using gradient descent and logistic regression. Your model will be trained on the same training set above (loaded by load_spam_data()), but we will test its accuracy on a testing dataset of emails (hidden from you) feature_dimension = 512def…Example Code Ch 09-6Assume that Student, Employee and Retired are all extended classes of Person, and all fourclasses have different implementations of the method getMoney. Consider the following code where... indicates the required parameters for the constructors:Person p = new Person(...);int m1 = p.getMoney(); // assignment 1p = new Student(...);int m2 = p.getMoney(); // assignment 2if (m2 < 100000)p = new Employee(...);else if (m1 > 50000)p = new Retired(...);int m3 = p.getMoney(); // assignment 323. Refer to Example Code Ch 09-6: The reference to getMoney() in assignment 1 is to the classa. Personb. Studentc. Employeed. Retirede. This cannot be determined by examining the code
- Let l(x) be "x has an internet conection" and C(x, y) be "x and y have chatted over the internet". Assume the domain is all students in a class. Express the following using quantifiers. 1. Jerry does not have an internet connection 2. Exactly one student in the class has an internet connection 3. Someone in your class has an internet connection but has not chatted with anyone else in the class.Consider the following details of all classes for class hierarchy shown in Figure 1 of this lab. Class Person holdso Two attributes i.e. name and year_of_birtho A two-argument constructor to initialize its data members with user-defined values Class Employee containso Five attributes i.e. employeeID, joiningYear, jobTitle (designation of an employee), courseID, and courseTitl Class Administration haso A parameterized constructor to receive five arguments to initialize inherited attributes from class Employee(Concerning courseID and courseTitle, only null value is allowed to set for an admin officer)o Two functions i.e. setJobTitle(employee) and getJobTitle(employee) to set and get job title of an employee Class Student haso Two attributes i.e. studentID and enrolledSemestero A four-argument constructor to initialize its data members (including inherited data members)o A function named display() to show the values of all attributes (including inherited attributes) Class Academic…Using the predicate symbols shown and appropriate quantifiers, write each English language statement as a predicate wff. (The domain is the whole world.)S(x): x is a spy novelL(x): x is longM(x): x is a mysteryB(x, y): x is better than ya. All spy novels are long.b. Not every mystery is a spy novel.c. Only mysteries are long.d. Some spy novels are mysteries.e. Spy novels are better than mysteries.f. Some mysteries are better than all spy novels.g. Only spy novels are better than mysteries.
- TASK 2.4 Implement the missing code for the method specialize(specialization_map)of class InferenceRule, which returns the specialization of the inference rule according to the given specialization map. #: A mapping from variable names to formulas.SpecializationMap = Mapping[str, Formula]...class InferenceRule:...def specialize(self, specialization_map: SpecializationMap) -> \InferenceRule:"""Specializes the current inference rule by simultaneously substitutingeach variable name `v` that is a key in `specialization_map` with theformula `specialization_map[v]`.Parameters:specialization_map: mapping defining the specialization to beperformed.Returns:The resulting inference rule."""for variable in specialization_map:assert is_variable(variable)# Task 4.4For (∃ x)(P(x,b)) Would an example of this being true if the domain was all the Avengers and x was green skin, then "b" being the Hulk would make this true. Am example of this being false would be: If the domain was all integers and x was positive, even integers and "b" was integers greater than zero.C++ implement a class car.car shall have the following membersa member variable model_year of type int.a member variable model_name of type std :: stringa parameterized constructor that takes both member variables as input parametersa function to retrieve model_yeara function for to retrieve model_name members' visibility must follow the usual convention overlay the outflow operator (<<) for class car.input follows the format[model_year] [model_name] output must have format:Model: [model_name], produced: [model_year] example:input: 2015 PeugeotOutput; Model: Peugeot, produced: 2015

