Which of the following statement refers to the main difference between the operation of inbound and outbound ALCS? O On a network interface, more than one inbound ACL can be configured but only one outbound ACL can be configured. OInbound ACLS are processed before the packets are routed while outbound ACLS are processed after the routing is completed. Inbound ACLS can be used in both routers and switches but outbound ACLS can be used only on routers. In contrast to outbound ALCS, inbound ACLS can be used to filter packets with multiple criteria.
Which of the following statement refers to the main difference between the operation of inbound and outbound ALCS? O On a network interface, more than one inbound ACL can be configured but only one outbound ACL can be configured. OInbound ACLS are processed before the packets are routed while outbound ACLS are processed after the routing is completed. Inbound ACLS can be used in both routers and switches but outbound ACLS can be used only on routers. In contrast to outbound ALCS, inbound ACLS can be used to filter packets with multiple criteria.
A+ Guide To It Technical Support
10th Edition
ISBN:9780357108291
Author:ANDREWS, Jean.
Publisher:ANDREWS, Jean.
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 13TC: Which two of the following hosts on a corporate intranet are on the same subnet?...
Related questions
Question
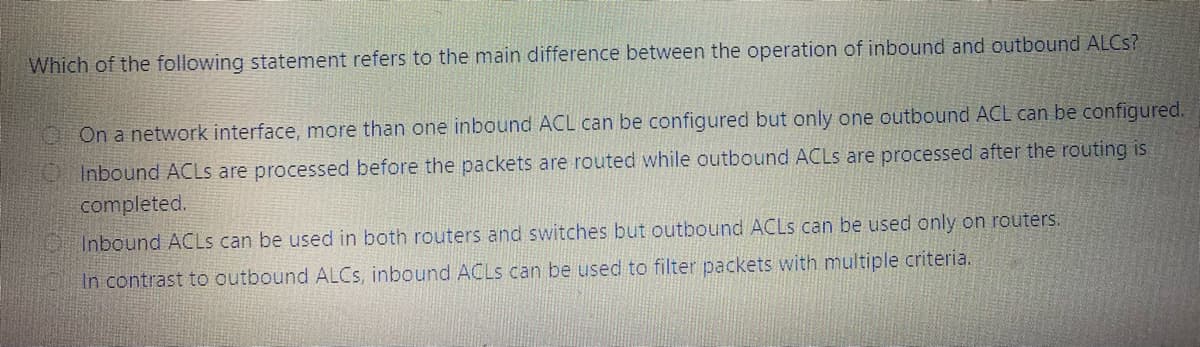
Transcribed Image Text:Which of the following statement refers to the main difference between the operation of inbound and outbound ALCS?
OOn a network interface, more than one inbound ACL can be configured but only one outbound ACL can be configured.
OInbound ACLS are processed before the packets are routed while outbound ACLS are processed after the routing is
completed.
Inbound ACLS can be used in both routers and switches but outbound ACLS can be used only on routers.
In contrast to outbound ALCS, inbound ACLS can be used to filter packets with multiple criteria.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,

A+ Guide To It Technical Support
Computer Science
ISBN:
9780357108291
Author:
ANDREWS, Jean.
Publisher:
Cengage,